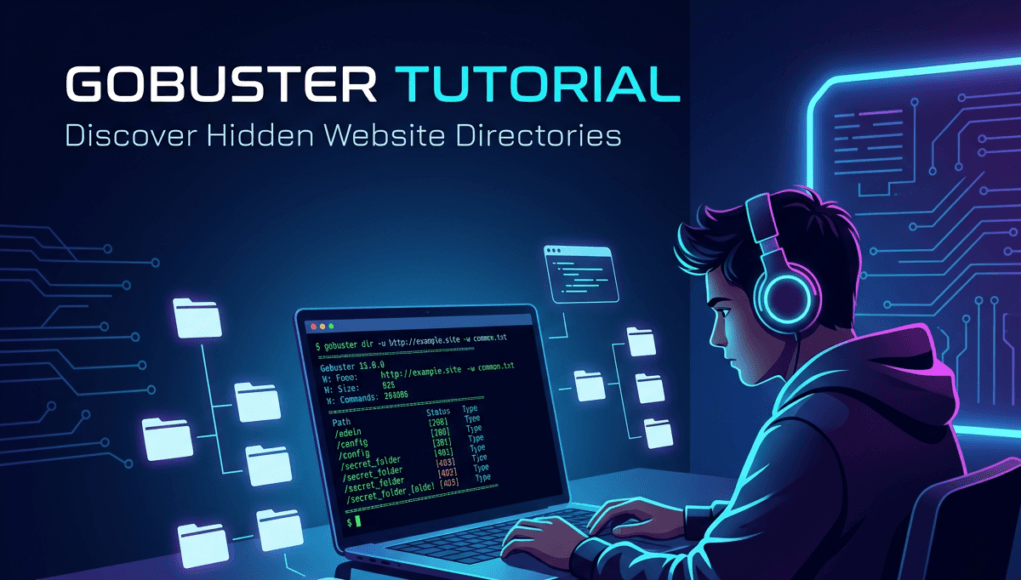
This Gobuster Tutorial teaches cybersecurity learners how to use the Gobuster tool to discover hidden directories, files, and subdomains on a web server using wordlist-based brute force techniques.
Gobuster is widely used in ethical hacking, penetration testing, bug bounty hunting, and web security assessments. It works by sending automated HTTP requests to a target website using thousands of possible directory names from a wordlist. When the server responds with valid status codes such as 200, 301, 302, or 403, Gobuster identifies that directory or file as existing on the server.
Hidden paths such as /admin, /backup, /dev, or /config are common discoveries during a Gobuster tutorial exercise. These resources often expose administrative dashboards, backup archives, or development environments that may contain vulnerabilities.
Because of its speed and efficiency, Gobuster has become one of the most trusted tools for web reconnaissance and attack surface discovery in modern cybersecurity testing.
Table of Contents
Gobuster Tutorial Overview
This Gobuster tutorial begins with understanding how web servers organize files and directories.
Most websites contain far more resources than what users see through navigation menus. Behind a normal website interface are multiple hidden directories used for administration, development, backups, APIs, and internal tools.
For example, a typical web server may contain directories such as:
/admin
/backup
/staging
/dev
/api
/config
/private
These directories often remain hidden because developers simply do not link them publicly.
However, hidden does not mean secure.
If the directory exists on the server, it can still respond to a request if someone guesses the correct URL.
This is where the technique explained in this Gobuster tutorial becomes extremely valuable.
Gobuster performs directory brute forcing, also known as content discovery. Gobuster is an open-source security tool maintained by the cybersecurity community. You can explore the official documentation on the Gobuster GitHub repository.
The tool takes a wordlist containing thousands of potential directory names and automatically generates requests such as:
https://example.com/admin
https://example.com/backup
https://example.com/dev
https://example.com/config
The server responds with an HTTP status code.
Important responses include:
200 OK
301 Redirect
302 Found
403 Forbidden
Each of these responses tells a security tester that the resource exists on the server.
This process allows cybersecurity professionals to map the hidden attack surface of a web application.
The concept is simple but extremely powerful.
Many serious vulnerabilities are not visible through the main website interface. Instead, they exist inside forgotten development areas or backup locations that were accidentally left accessible.
Examples discovered during real penetration tests include:
- exposed admin dashboards
- database backups
- staging servers
- configuration files
- development APIs
- file upload directories
This is why directory enumeration is considered a core reconnaissance technique in ethical hacking.
Note —
Think of a website like a large office building.
Visitors normally see the lobby and meeting rooms.
But there are also maintenance rooms, staff-only doors, storage areas, and server rooms hidden from public view.
This Gobuster tutorial essentially teaches you how to check every door in that building.
Eventually you find doors nobody expected an outsider to open.
How Attackers Use This Technique
This Gobuster tutorial does not only explain the tool. It also explains the mindset of attackers using it.
Professional attackers rarely begin with exploitation.
Instead, they spend significant time mapping the attack surface.
Directory enumeration is one of the most effective reconnaissance techniques used in both penetration testing and real-world cyber attacks.
Attackers usually follow a structured workflow.
First, they identify a target domain.
Example:
example.com
Next, they analyze the web technology stack.
Understanding the technology stack helps attackers predict possible directory structures.
For example:
A WordPress website commonly contains:
/wp-admin
/wp-content
/wp-login
A Laravel application may contain:
/storage
/vendor
/public
Understanding frameworks allows attackers to build better wordlists.
Next, attackers launch a directory brute force scan using tools such as Gobuster.
Wordlists typically contain between 10,000 and 100,000 directory names.
These lists are compiled from years of security research and real-world penetration testing.
Once the scan begins, attackers analyze server responses carefully.
Example results:
/admin (Status: 301)
/backup (Status: 200)
/uploads (Status: 403)
/api (Status: 200)
Each response gives attackers valuable information.
For example:
A 403 response means the directory exists but access is restricted.
That alone confirms the directory is real.
Attackers then manually investigate the discovered resources.
Common discoveries include:
- development environments
- outdated applications
- database exports
- configuration files
- API endpoints
Many bug bounty programs report critical vulnerabilities discovered purely through directory enumeration.
Common Beginner Mistakes
Students following this Gobuster tutorial often make several mistakes.
Mistake 1 — Using extremely small wordlists
Small wordlists drastically reduce discovery rates.
Mistake 2 — Ignoring HTTP response codes
Different response codes indicate different situations.
Mistake 3 — Scanning too aggressively
High-speed scans may trigger web application firewalls.
Mistake 4 — Not validating discovered directories manually
Automation identifies directories, but human investigation reveals vulnerabilities.
Professional testers combine automation with manual analysis.
SecurityElites Hands-On Lab Exercise – Step-by-Step Gobuster Tutorial Using Kali Linux
This section walks you through a practical Gobuster tutorial lab designed for cybersecurity beginners.
Only perform these exercises in legal practice environments.
Recommended practice targets include:
- DVWA
- OWASP Juice Shop
- Metasploitable
- intentionally vulnerable training websites
Never run scans against systems without permission.
Step 1 — Verify Gobuster Installation
Kali Linux includes Gobuster by default.
Verify installation with:
gobuster -h
If Gobuster is missing, install it using:
sudo apt install gobuster
The help menu shows supported scanning modes.
dir
dns
vhost
s3
In this Gobuster tutorial, we will focus on directory enumeration mode.
Step 2 — Locate Wordlists
Wordlists are the foundation of directory brute forcing.
Kali Linux stores default wordlists here:
/usr/share/wordlists/
A commonly used list:
/usr/share/wordlists/dirb/common.txt
For larger scans, security professionals often use SecLists.
/usr/share/seclists/
SecLists contains thousands of curated directory and file names used by developers worldwide.
Note —
Wordlists represent real developer behavior patterns.
They are built from years of security testing data.
Step 3 — Run Your First Gobuster Scan
Example command from this Gobuster tutorial:
gobuster dir -u http://target-site.com -w /usr/share/wordlists/dirb/common.txt
Parameter explanation:
dir = directory enumeration mode
-u = target URL
-w = wordlist
Gobuster will now begin sending automated requests.
Example output:
/admin (Status: 301)
/backup (Status: 200)
/images (Status: 301)
/uploads (Status: 403)
Each entry represents a discovered resource.
Step 4 — Analyzing the Results
Understanding scan results is a critical part of this Gobuster tutorial.
Example result:
/backup (Status: 200)
This indicates that the directory is accessible.
Attackers immediately investigate such directories.
Example:
/uploads (Status: 403)
Even though access is restricted, the directory exists.
Attackers may try alternative methods to bypass restrictions.
Step 5 — Discover Files Using Extensions
Many sensitive files use specific extensions.
Examples include:
.php
.txt
.zip
.bak
.sql
You can test file extensions with:
gobuster dir -u http://target-site.com -w common.txt -x php,txt,zip
This command attempts combinations like:
backup.zip
config.php
notes.txt
These files often contain sensitive information.
Step 6 — Increase Scan Speed
Gobuster supports multi-threading.
Example parameter:
-t 50
Example command:
gobuster dir -u http://target-site.com -w common.txt -t 50
Higher threads increase speed but may trigger defenses.
Professional penetration testers carefully balance speed and stealth.
Step 7 — Filter Response Codes
Filtering improves scan clarity.
Example:
gobuster dir -u http://target.com -w common.txt -s 200,301,302,403
This shows only meaningful results.
Step 8 — Save Scan Results
Always record scan results.
-o gobuster-results.txt
Example command:
gobuster dir -u http://target.com -w common.txt -o results.txt
Saved results help during later investigation.
Step 9 — Manual Investigation
The final step of any Gobuster tutorial lab is manual exploration.
Discovered directories might include:
/backup
/dev
/api
/staging
These areas may expose:
- configuration files
- database dumps
- developer notes
- API documentation
- debugging interfaces
This is where serious vulnerabilities are often discovered.
Automation finds the doors.
Human analysis finds the vulnerabilities.
How Organizations Prevent Directory Enumeration ?
Organizations must assume attackers will attempt directory brute forcing.
Several defensive strategies reduce exposure.
First, remove unnecessary directories.
Old development environments such as:
/backup
/dev
/staging
should never remain on production servers.
Second, enforce strong authentication controls.
Administrative interfaces must require login protection.
Third, deploy Web Application Firewalls.
WAF systems can detect automated scanning patterns such as thousands of sequential directory requests.
Fourth, implement rate limiting.
Rate limiting restricts the number of requests allowed from a single IP address.
Fifth, monitor server logs.
Security teams should watch for patterns like:
GET /admin
GET /backup
GET /test
GET /config
These patterns strongly indicate enumeration activity.
Finally, organizations should conduct regular penetration testing and security assessments to identify exposed directories before attackers do.
FAQs – Gobuster Tutorial
What is Gobuster used for?
Gobuster is a directory and subdomain brute force tool used in ethical hacking and penetration testing. It helps cybersecurity professionals discover hidden directories, files, and subdomains on web servers by sending automated requests using wordlists. These discoveries often reveal parts of a web application that are not publicly linked.
Is Gobuster better than Dirb?
Gobuster is often faster than Dirb because it is written in the Go programming language. Many penetration testers prefer Gobuster due to its speed and efficiency when scanning large wordlists. However, security professionals often use multiple tools such as Dirsearch and FFUF for comprehensive reconnaissance.
Can beginners learn Gobuster safely?
Yes. Beginners can practice Gobuster safely in controlled environments such as cybersecurity labs, intentionally vulnerable web applications, and training platforms. Practicing in legal environments allows students to understand directory enumeration without harming real systems.
What wordlists are best for Gobuster?
The most commonly used wordlists come from the SecLists project. Kali Linux also provides useful lists such as common.txt and directory-list-2.3-medium.txt. Choosing larger and well-curated wordlists significantly improves directory discovery results.
Can Gobuster discover subdomains?
Yes. Gobuster includes DNS enumeration mode that allows security testers to discover subdomains. Using a subdomain wordlist, Gobuster can identify hidden hosts such as admin.example.com or dev.example.com.
Conclusion – Key Takeaways
This Gobuster tutorial introduced one of the most powerful reconnaissance techniques used in ethical hacking and penetration testing.
Directory enumeration helps cybersecurity professionals identify hidden parts of web applications that may expose vulnerabilities.
During real security assessments, many critical issues originate from directories discovered using tools like Gobuster.
Hidden resources frequently expose administrative interfaces, configuration files, development environments, and backup archives.
For beginners entering cybersecurity, mastering reconnaissance tools like Gobuster is an essential skill.
After completing this Gobuster tutorial, the next skills you should practice include:
- web application reconnaissance
- subdomain enumeration
- vulnerability scanning
- HTTP response analysis
- manual penetration testing techniques
The most successful penetration testers are not just tool users.
They are investigators who explore systems carefully and discover weaknesses others overlook.
Continuous practice in cybersecurity labs will gradually transform beginners into skilled ethical hackers.