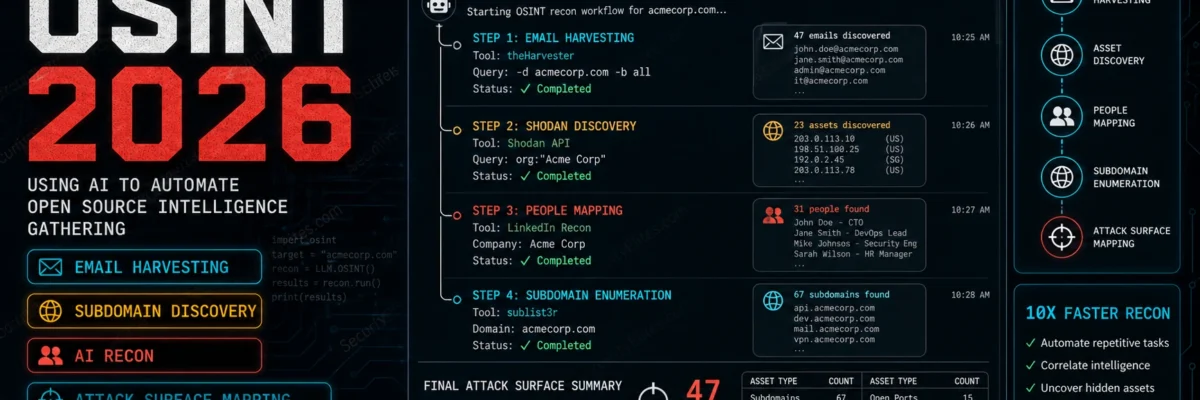
OSINT
Dive into open source intelligence techniques used to gather information from publicly available sources. Learn how to investigate emails, phone numbers, domains, usernames, and social media profiles using professional OSINT tools. This category covers intelligence gathering methods used in cyber investigations, penetration testing, and digital forensics while maintaining legal and ethical boundaries.
18 articles
Shodan Tutorial Kali Linux 2026 — Search Engine for Hackers, Dork Queries & API Usage | Hacking Tools Day22
Shodan Tutorial in Kali Linux for 2026. Search exposed devices, run dork queries, use the API and build a recon…
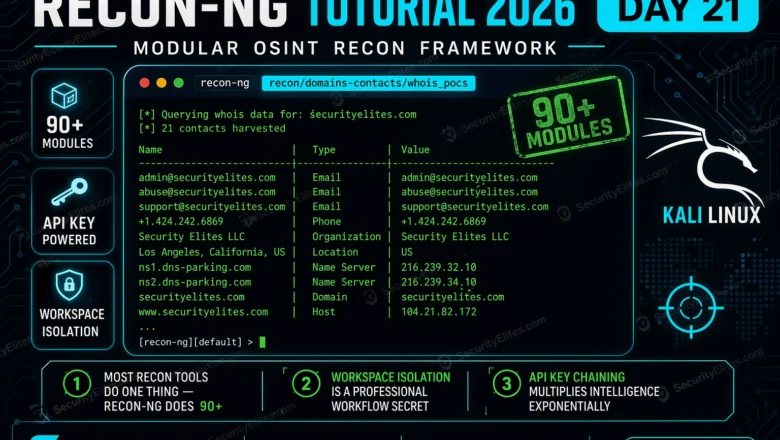
Recon-ng Tutorial 2026 — Modular OSINT Framework for Professional Reconnaissance | Tools Day21
Recon-ng tutorial 2026 — install, configure workspaces, run modules, harvest emails domains and contacts using the most powerful modular OSINT…
How to Use Shodan 2026 — The Hacker’s Search Engine Complete Guide
How to use shodan 2026 — search internet-connected devices, find exposed services, use Shodan dorks for bug bounty recon and…
Google Dorking for Hackers 2026 — 50 Dorks to Find Vulnerabilities and Exposed Data
Google dorking for hackers 2026 — 50 essential Google dorks to find exposed admin panels, config files, passwords, subdomains and…
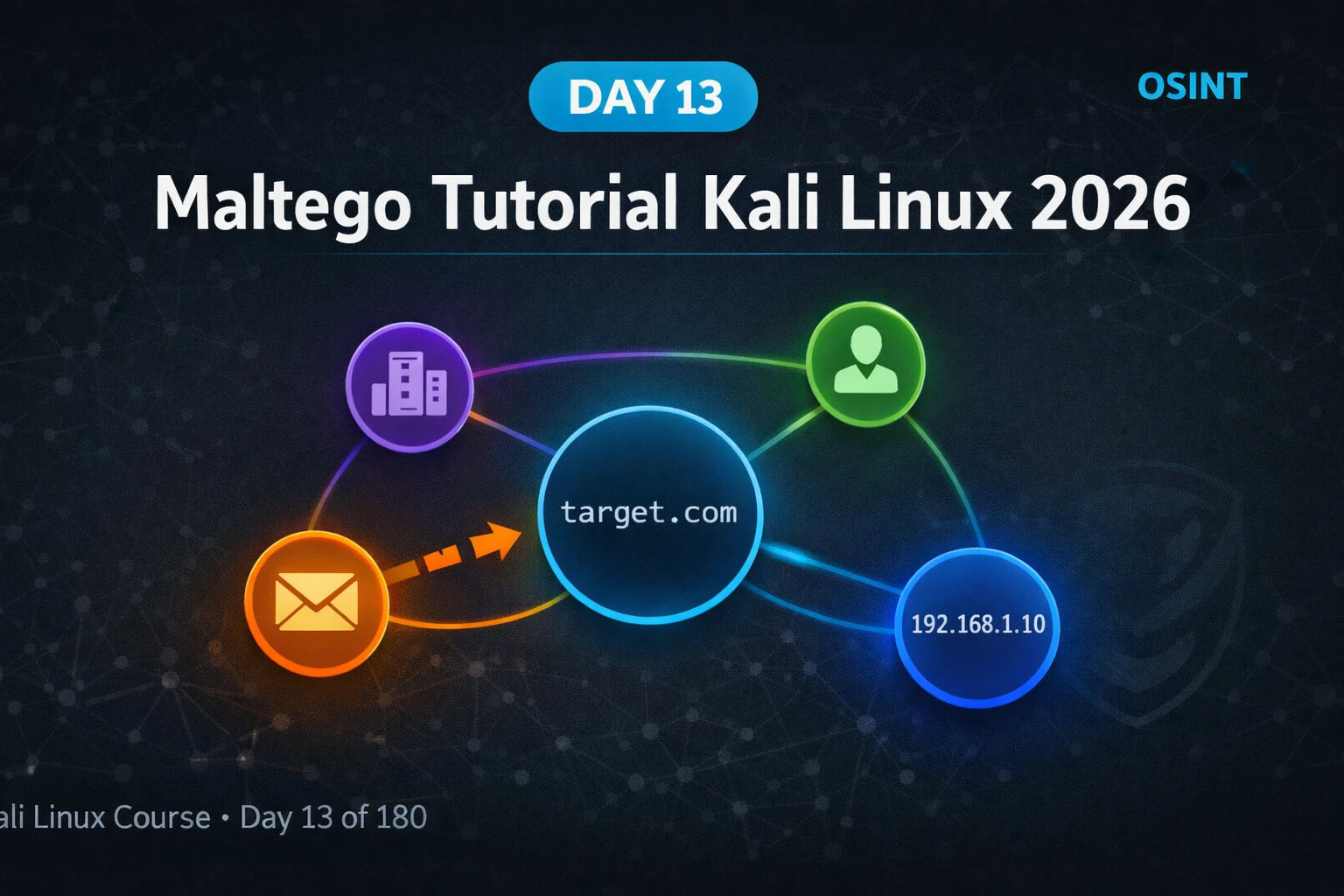
Kali Linux Day13: Maltego Tutorial Kali Linux 2026 — OSINT Link Analysis & Entity Mapping Guide
Maltego tutorial kali linux 2026 — install Community Edition, run transforms, map domains and emails, build entity graphs for OSINT…
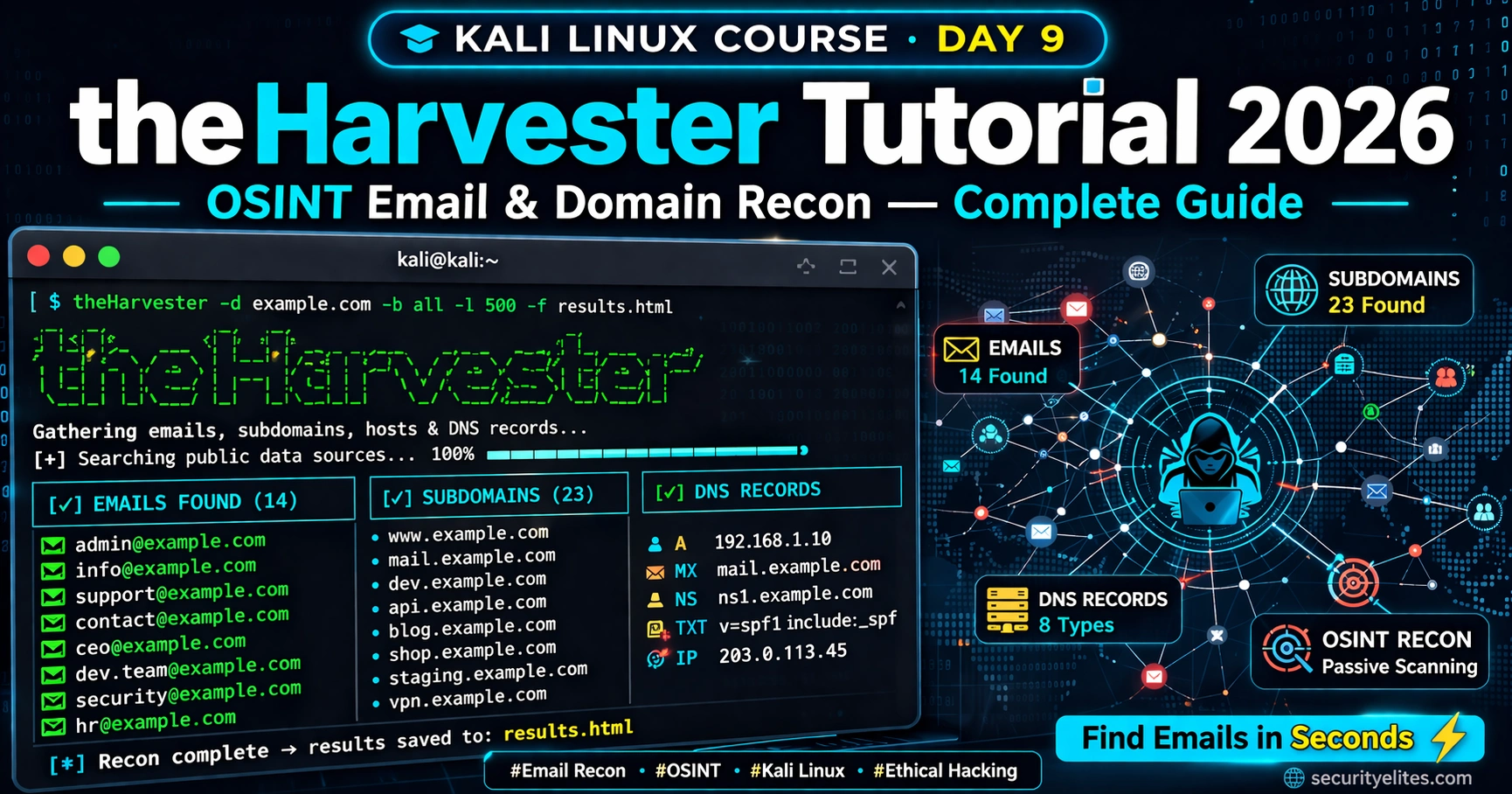
How Hackers Use theHarvester to Find Emails in Seconds (Most Don’t Know This)
Discover how hackers use theHarvester to harvest real employee emails from public sources in seconds — the OSINT technique most…
Kali Linux Day 9 : theHarvester Tutorial 2026 — OSINT Email & Domain Recon Complete Guide
Master theHarvester in Kali Linux 2026 — collect emails, subdomains & DNS records for OSINT recon. Complete Day 9 guide…
Prompt Injection Attack & LLM Hacking 2026 — How Hackers Attack AI Systems (Complete Guide)
Prompt injection attack is OWASP’s #1 AI vulnerability. Learn how hackers exploit LLMs through direct injection, indirect attacks, data exfiltration,…
AI-Powered Cyberattacks 2026 — How Hackers Are Using Artificial Intelligence to Attack You
AI powered cyberattacks are the #1 threat of 2026. Discover how hackers use agentic AI to automate phishing, vulnerability scanning,…