Exploitation Tools
Exploitation tools for penetration testing help security professionals validate vulnerabilities in controlled environments. This category includes tutorials on frameworks like Metasploit, SQLmap, Hydra, and other exploitation utilities used to test system weaknesses. Learn how to configure payloads, execute exploits, establish reverse shells, and perform post-exploitation activities responsibly. Each guide emphasizes ethical usage and defensive measures to protect against exploit-based attacks. Real-world lab demonstrations help readers understand how vulnerabilities are exploited and how security teams mitigate risks.
16 articles
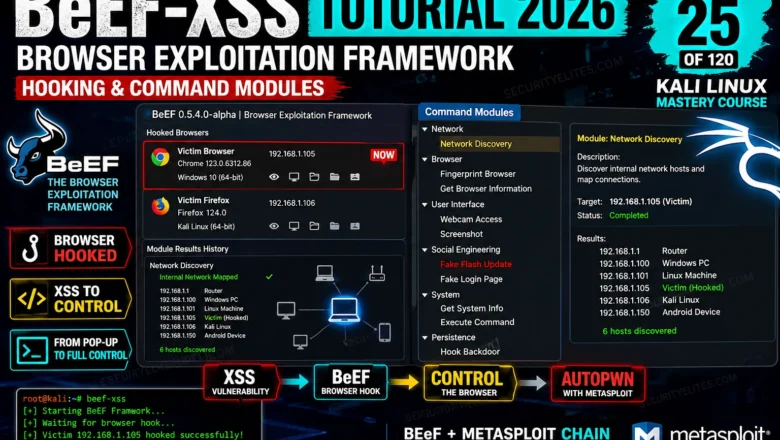
BeEF-XSS Tutorial 2026 — Browser Exploitation Framework, Hooking & Command Modules | Tools Day 25
BeEF-XSS Tutorial Kali Linux 2026. Hook browsers, run command modules, steal cookies, capture keystrokes, and understand browser exploitation in a…
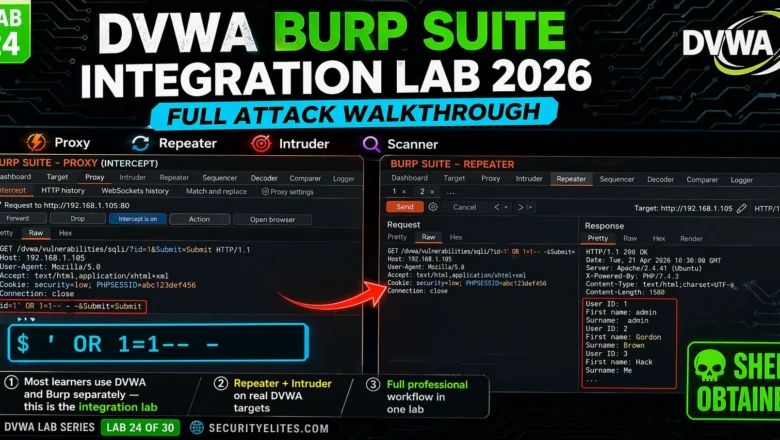
DVWA Burp Suite Integration Lab 2026 — Full Attack Walkthrough Using Burp Suite | Hacking Lab24
DVWA Burp Suite integration lab 2026 — configure Burp proxy, use Repeater, Intruder and Scanner to exploit every DVWA vulnerability…
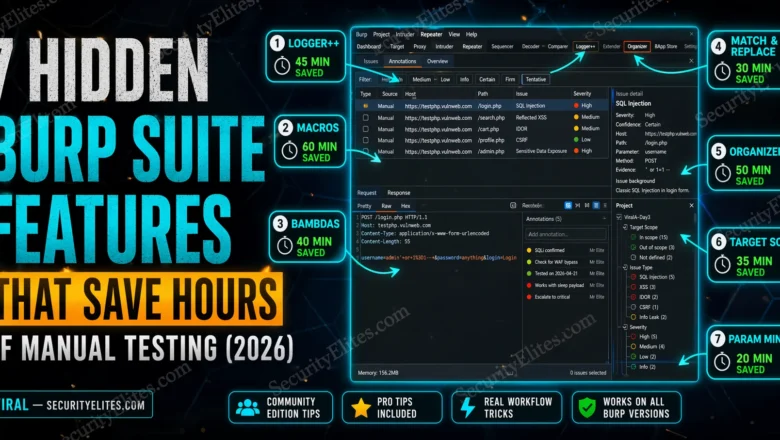
7 Hidden Burp Suite Features That Save Hours of Manual Testing (2026)
7 Burp Suite hidden features most ethical hackers miss in 2026 — macros, Logger++, Match & Replace, Bambdas, target scope…
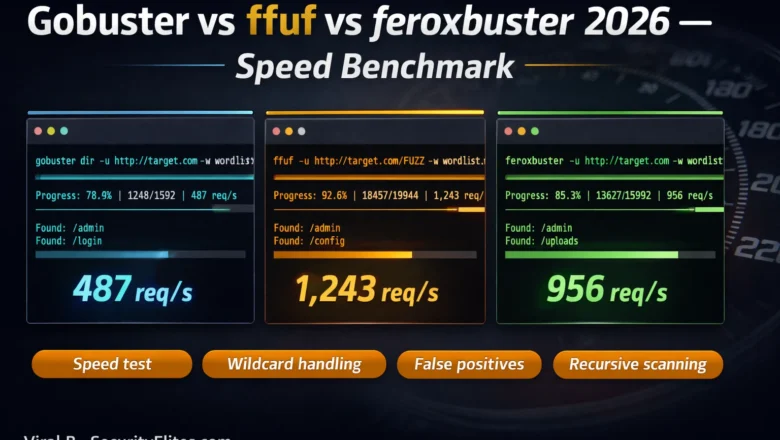
Gobuster vs ffuf vs feroxbuster — Speed & Accuracy Benchmark 2026
Gobuster vs ffuf vs feroxbuster 2026 — side-by-side speed and accuracy benchmark. Which directory fuzzer wins on speed, false positives,…
Meterpreter Commands Cheat Sheet 2026 — 50+ Commands With Real Examples
Complete Meterpreter commands cheat sheet 2026. Every essential Meterpreter command with real examples — system recon, file operations, privilege escalation,…
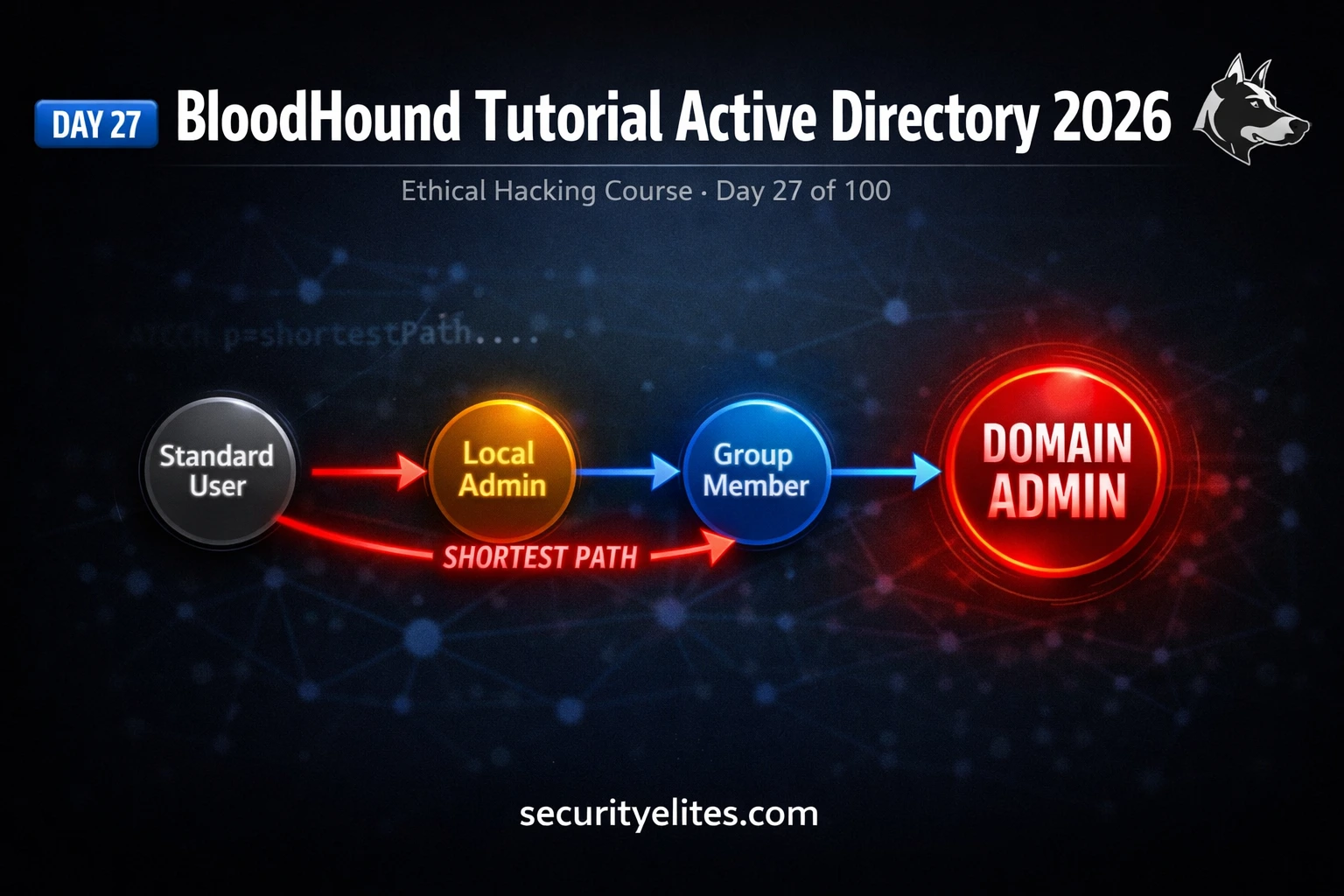
BloodHound Tutorial 2026 — Find the SHORTEST Path to Domain Admin in Minutes | Day 27
BloodHound tutorial active directory 2026 — install SharpHound, collect AD data, visualise attack paths and find the shortest route to…
Kali Linux Commands Cheat Sheet 2026 — 150 Tools, 2955 Commands, One Click
Kali linux commands cheat sheet 2026 — 150 tools, 2955+ ready-to-use commands across 13 categories. Filter by tool, copy any…
10 Best Hacking Tools in 2026 — What Every Ethical Hacker Actually Uses
The 10 best hacking tools in 2026 ranked by real-world usage — Kali Linux, Burp Suite, Metasploit, Nmap, and more.…
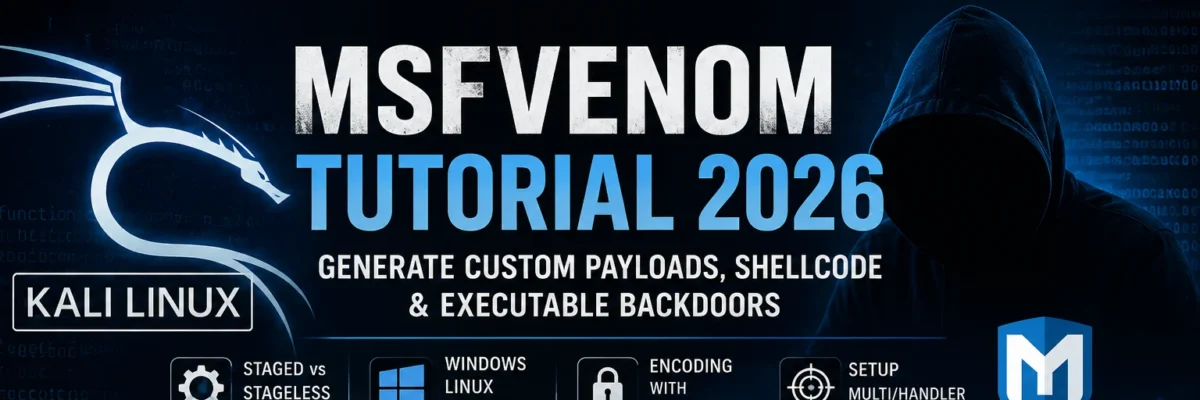
Kali Linux Day 10 : Metasploit Tutorial Kali Linux 2026 — msfconsole, Modules & First Exploit Complete Guide
Master Metasploit in Kali Linux 2026 — msfconsole commands, exploit modules, payloads & your first real shell. Day 10 complete…