Web Application Security
Explore web application security vulnerabilities and learn how ethical hackers identify and exploit them. This category covers SQL injection, cross-site scripting (XSS), CSRF, file upload vulnerabilities, authentication bypass, API security flaws, and session management issues. You’ll find hands-on tutorials, payload examples, exploitation labs, and prevention techniques to secure web applications. Ideal for bug bounty hunters, penetration testers, and developers who want to build and test secure web platforms.
100 articles
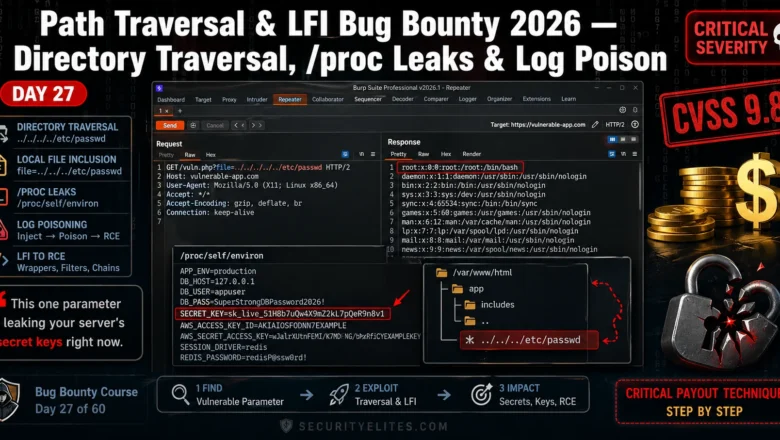
Path Traversal LFI Bug Bounty 2026 — Directory Traversal, proc Leaks & Log Poison | BB Day 27
Master path traversal LFI bug bounty in 2026. Directory traversal, /proc leaks, log poisoning — real techniques that earn Critical…
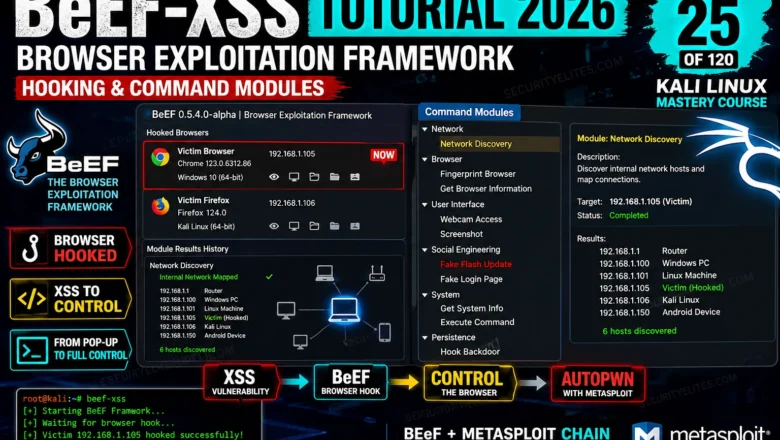
BeEF-XSS Tutorial 2026 — Browser Exploitation Framework, Hooking & Command Modules | Tools Day 25
BeEF-XSS Tutorial Kali Linux 2026. Hook browsers, run command modules, steal cookies, capture keystrokes, and understand browser exploitation in a…
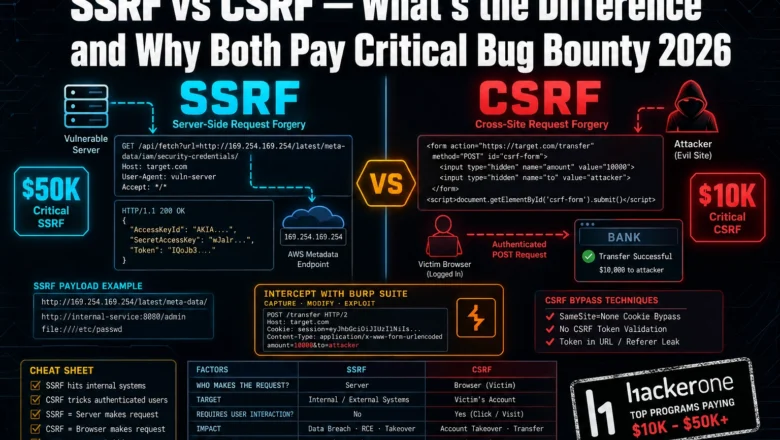
SSRF vs CSRF Bug Bounty 2026— What’s the Difference and Why Both Pay Critical
Most bug bounty hunters mix up SSRF and CSRF — and miss critical payouts because of it. Here's exactly how…
Command Injection Payloads That Bypass WAF in 2026 — Real Bypass List
Real WAF bypass via command injection payloads in 2026. I've tested every technique here — encoding tricks, wildcards, IFS abuse.…
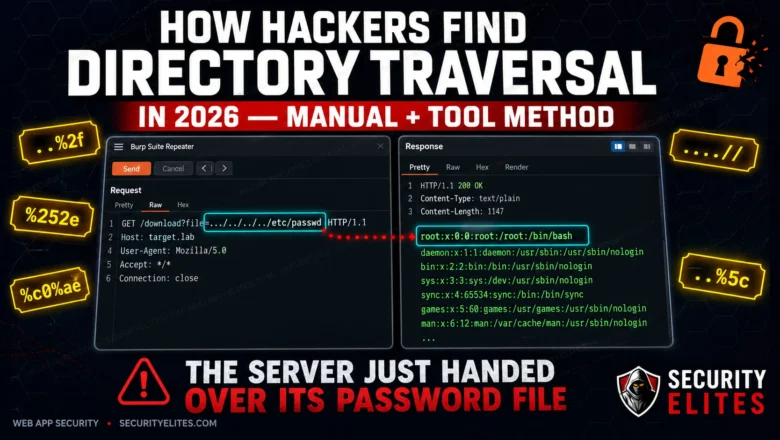
How Hackers Find Directory Traversal in 2026 — Manual + Tool Method
Directory traversal is still landing critical findings on HackerOne in 2026. Here's the exact manual and automated method hackers use…
SSTI Bug Bounty 2026 — Server-Side Template Injection to RCE on 5 Template Engines | BB Day 26
Server-Side Template Injection turns a misplaced expression into a shell. I'll walk you through detection, exploitation chains, and RCE payloads…
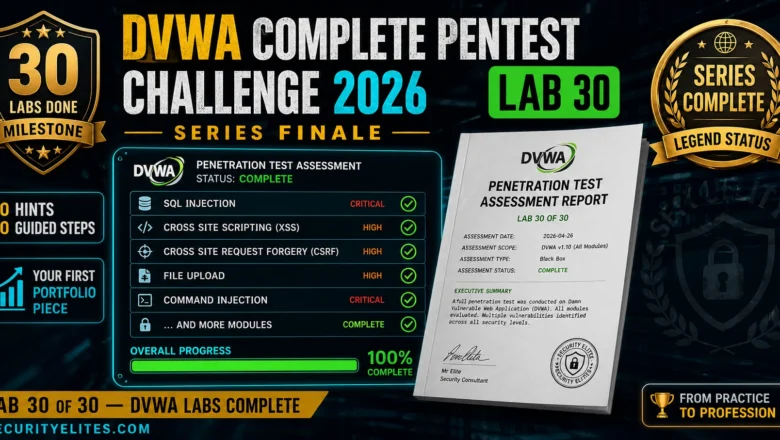
DVWA Complete Pentest Challenge 2026 — Full Assessment From Scratch, No Hints | Hacking Lab 30
The DVWA series finale — a complete unsupported pentest challenge across all modules. No hints, no steps, just methodology and…
SecurityElites Launched 47 Free Hacking Labs 2026 — No Signup, No VM, No Setup – Start Your Hacking Journey Now
SecurityElites Just launched 47 free hacking labs — no signup, no VM. AI hacking (17 labs), XSS, JWT, SSRF, SSRF,…
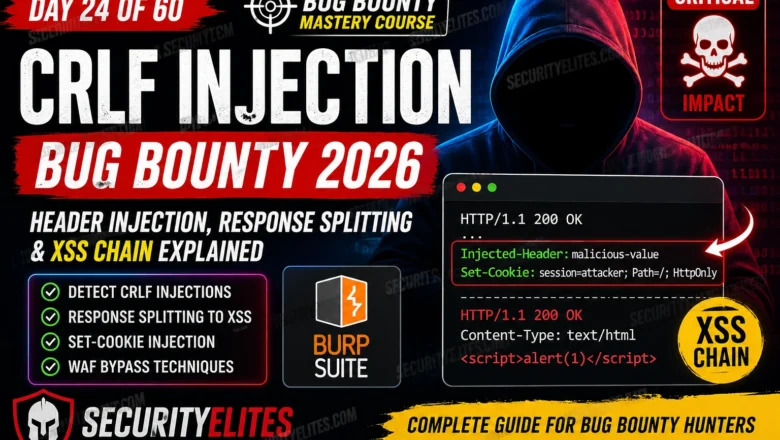
CRLF Injection Bug Bounty 2026 — Full Exploit Guide (XSS, Response Splitting) BB Day 24
Complete guide to CRLF injection bug bounty in 2026. Covers HTTP response splitting, Set-Cookie injection via CRLF, XSS chains through…