File Upload Vulnerabilities
Understand insecure file upload flaws that allow attackers to upload malicious shells. This section demonstrates bypass techniques, file filtering weaknesses, and secure upload implementations.
8 articles
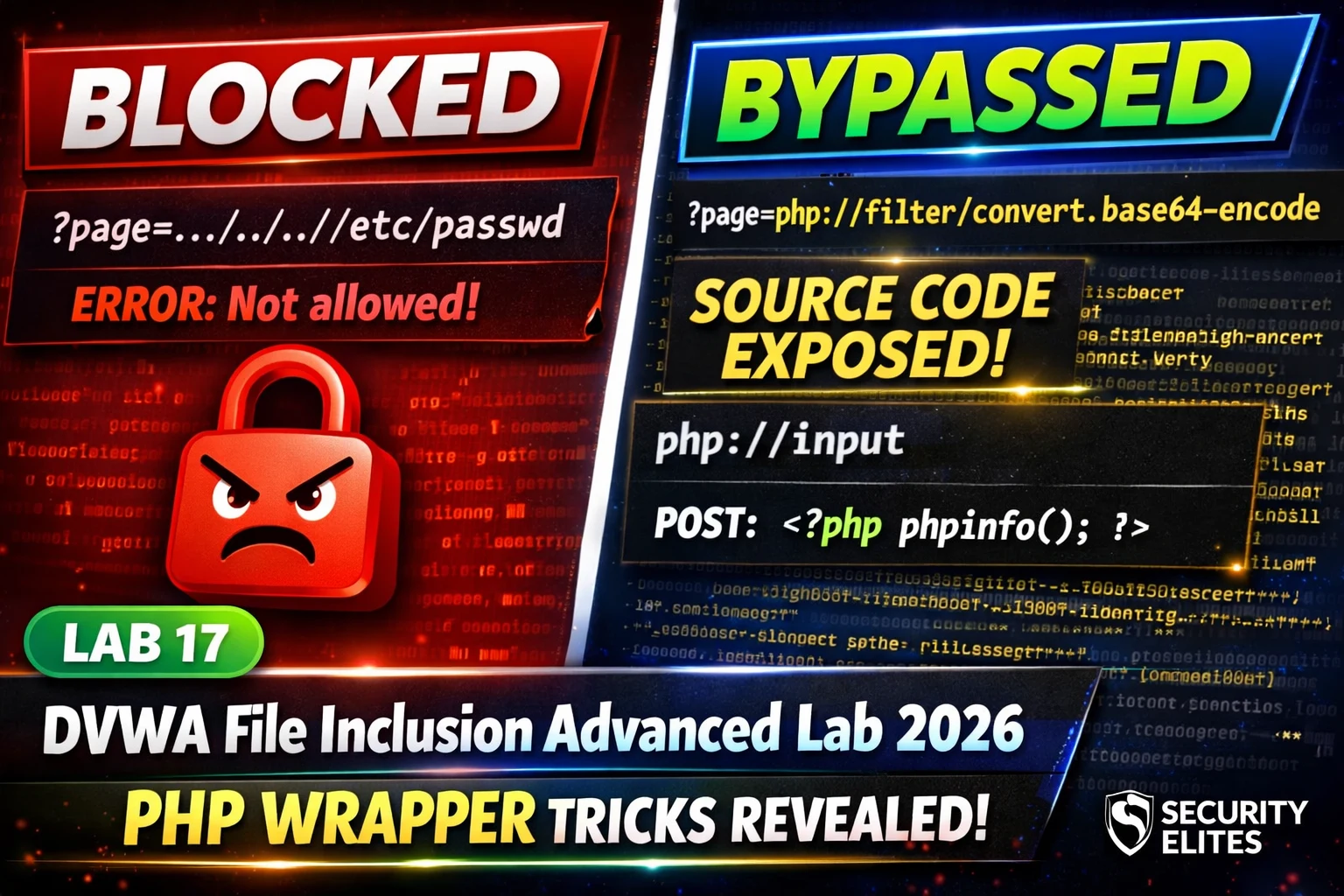
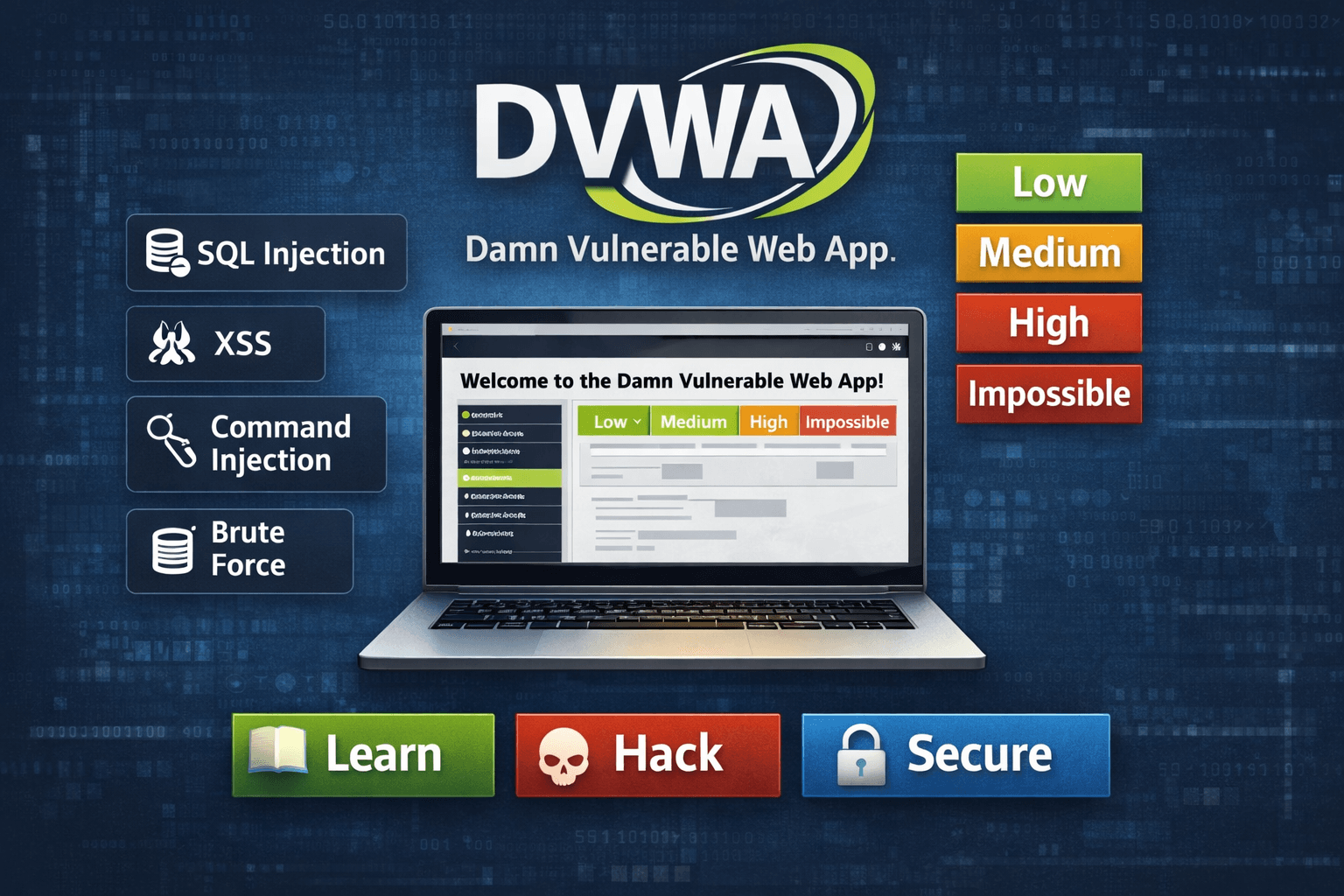
DVWA File Inclusion Advanced Lab 2026 — PHP Wrappers & Path Bypass Complete Walkthrough | Hacking Lab17
DVWA file inclusion advanced lab 2026 — bypass Medium and High security using php://filter, php://input, data:// wrappers and path restriction…
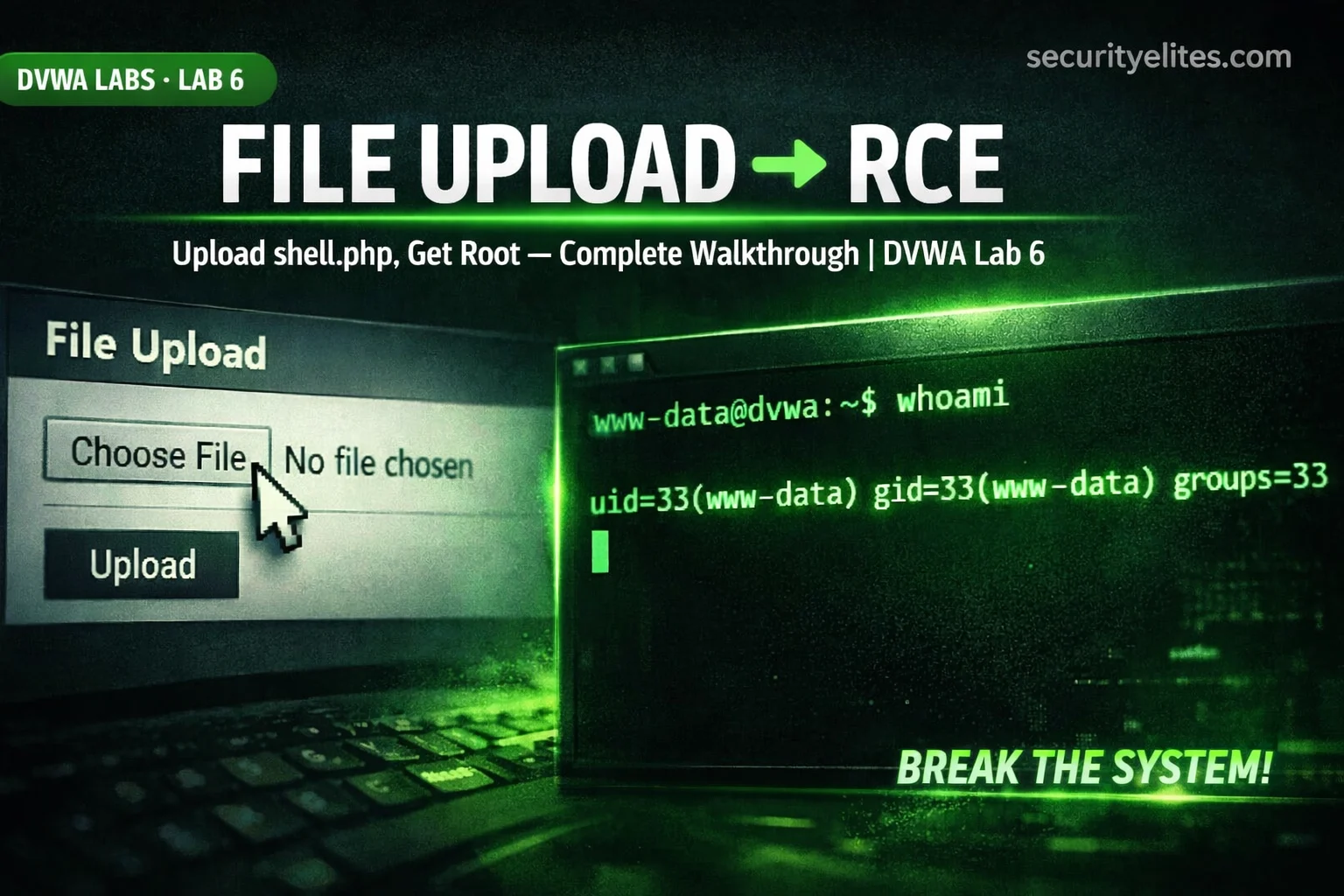
Lab 6: DVWA File Upload Lab 2026 — Ultimate Guide to Upload PHP Webshells & Get RCE Fast
Complete DVWA File Upload lab 2026 — upload PHP webshells, bypass MIME type checks, extension filtering, and achieve RCE at…
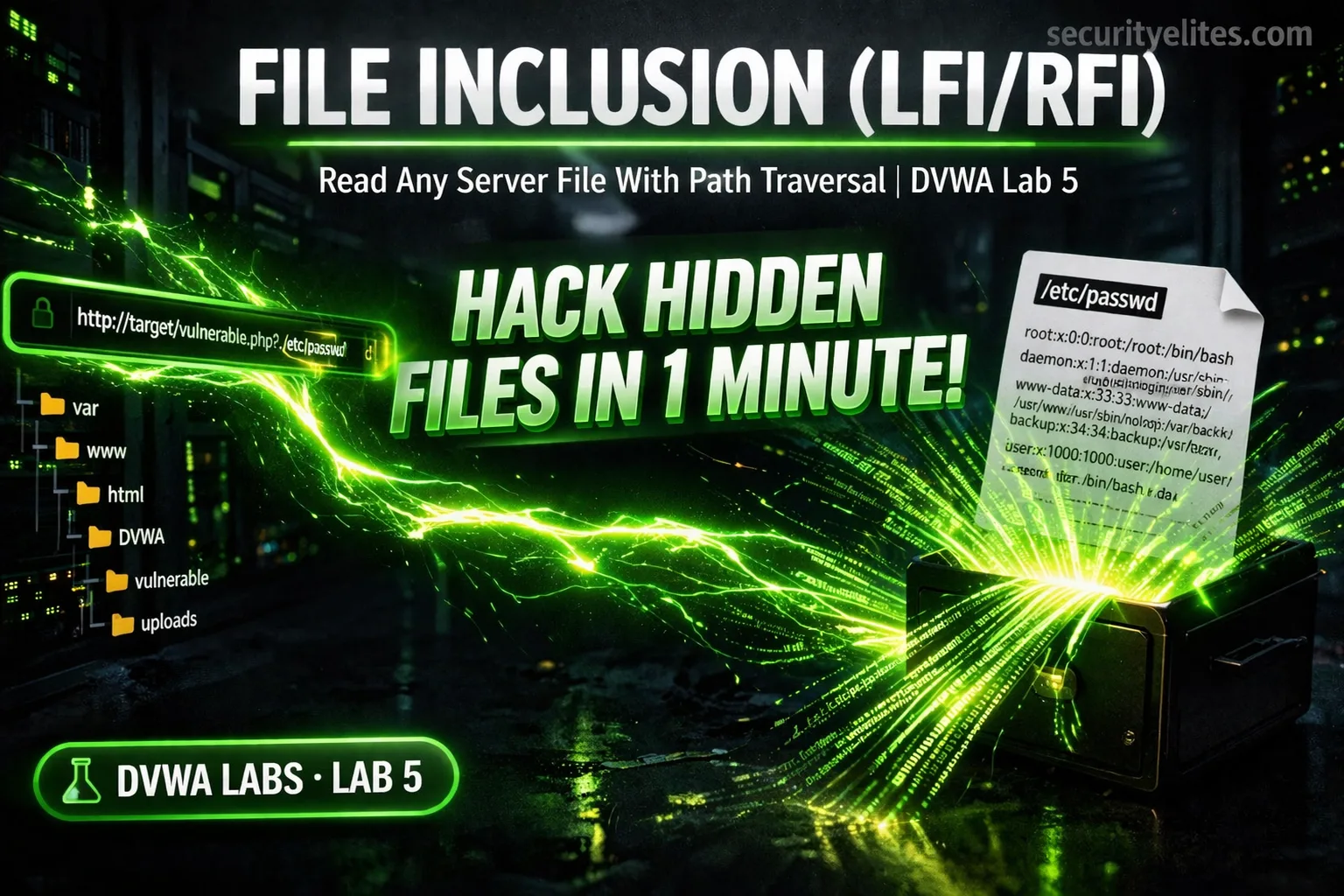
Lab 5: DVWA File Inclusion Lab 2026 — Hack Hidden Files in 1 Minute
Complete DVWA File Inclusion lab 2026 — exploit LFI to read /etc/passwd, path traversal, PHP wrappers, and RFI remote code…
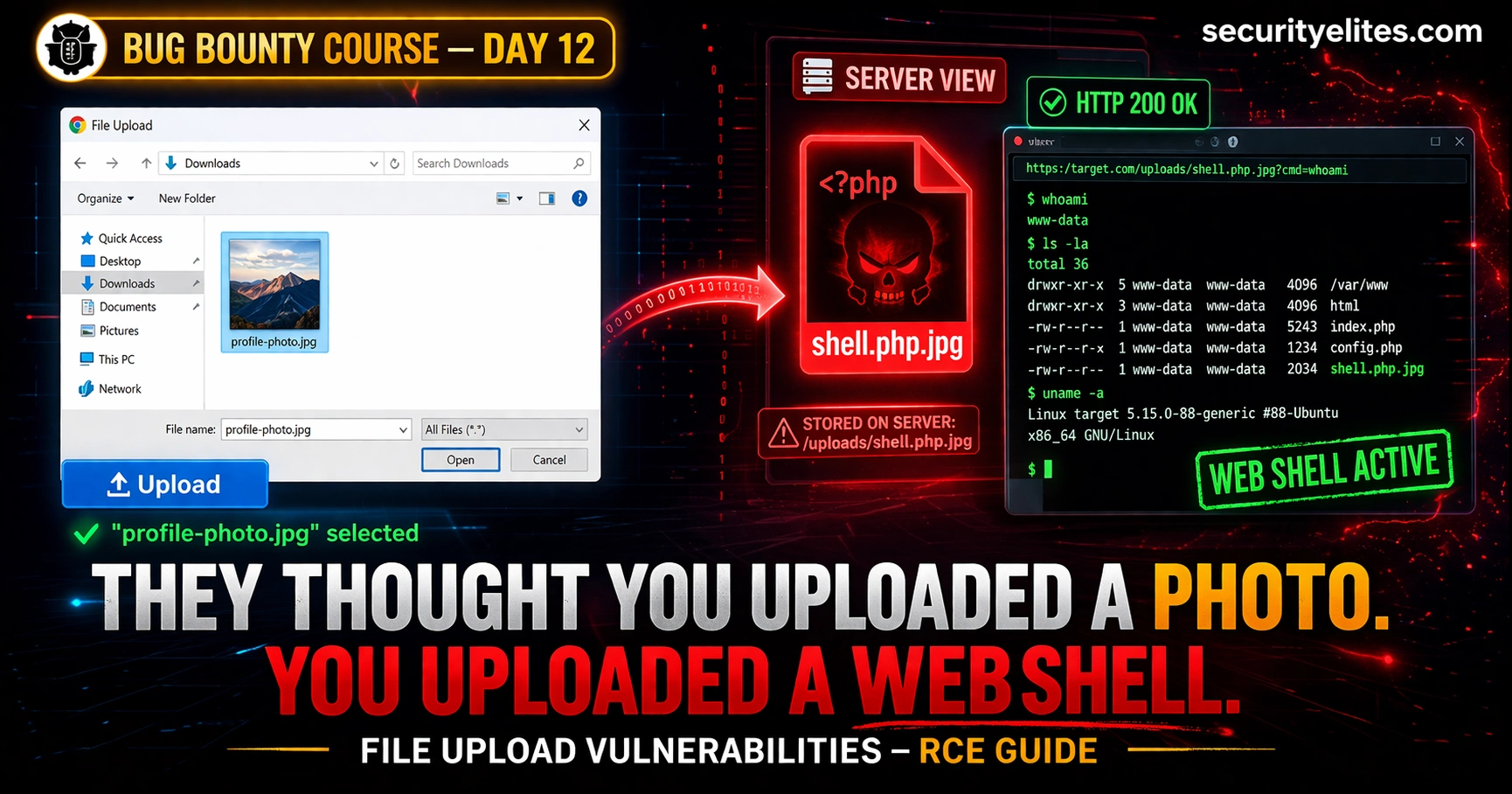
Day 12: File Upload Vulnerabilities — From Bypassing Filters to Remote Code Execution (Bug Bounty 2026)
File upload vulnerabilities bug bounty are among the highest-paying bugs in bounty programs. Day 12 covers every bypass technique—from MIME…
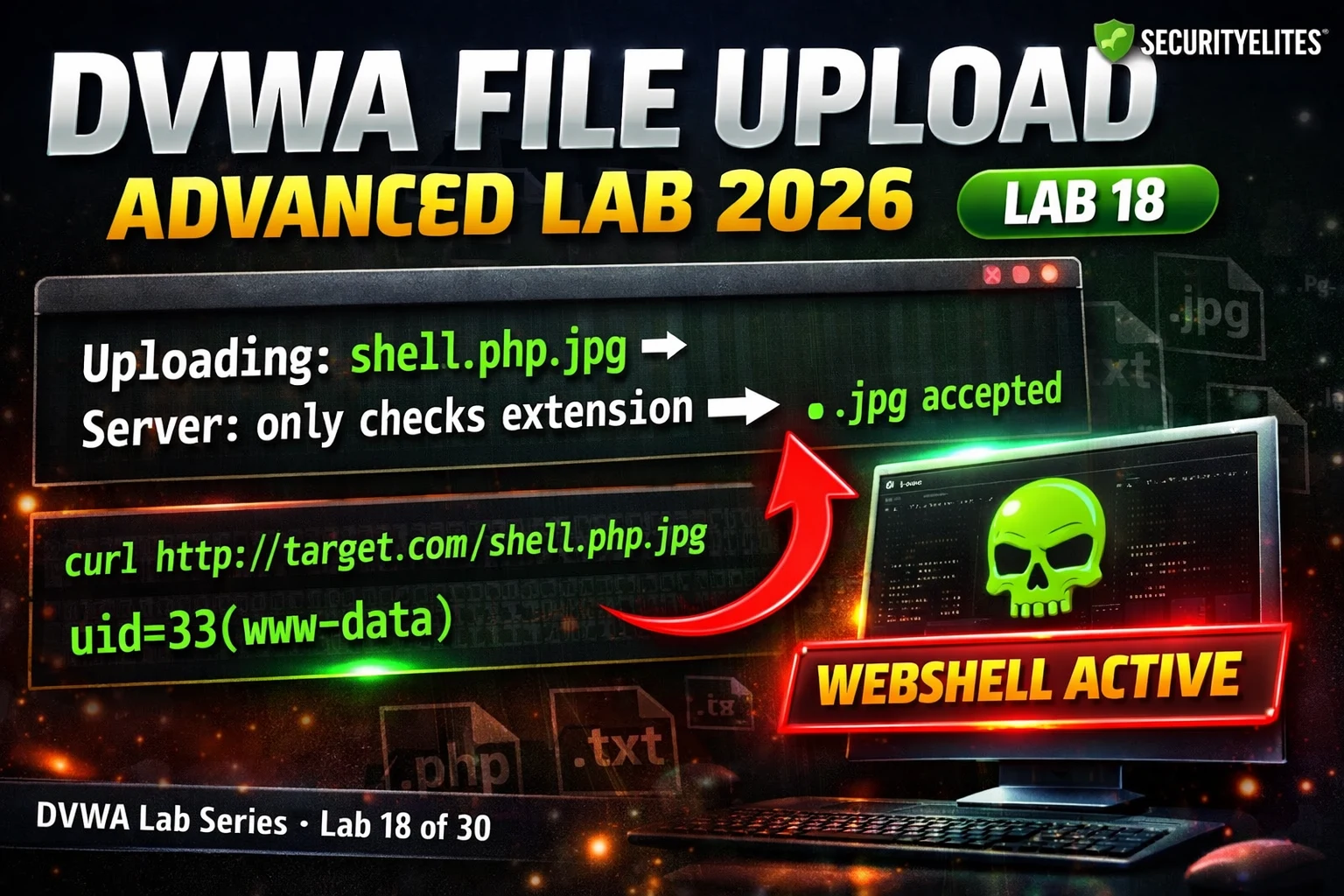
Day 18: File Upload Vulnerabilities — From Image Upload to Web Shell (2026)
Understand file upload vulnerabilities from first principles — how validation is bypassed, how web shells work, full DVWA demos at…
How Hackers Hack Websites in 2026: A Beginner-Friendly Step-by-Step Guide
Learn how hackers hack websites in 2026 with this beginner-friendly step-by-step guide. Discover reconnaissance, vulnerability scanning, SQL injection, XSS attacks,…
DVWA Web Hacking Tutorial Day 6: File Upload & Command Injection Exploitation
DVWA Web Hacking Tutorial Day 6 - Learn file upload attacks and command injection using DVWA. Achieve server-level exploitation with…