Reconnaissance Tools
econnaissance tools for hacking are essential in the information-gathering phase of ethical hacking and penetration testing. In this section, you will explore powerful reconnaissance tools used to discover domains, subdomains, IP addresses, exposed services, and publicly available data. Tutorials cover tools like Nmap, Amass, Sublist3r, theHarvester, and Shodan with step-by-step setup and usage guides. Each article explains how security professionals map attack surfaces, automate recon workflows, and interpret scanning results safely. You will also learn how organizations defend against reconnaissance attempts and reduce information exposure. This category is ideal for bug bounty hunters, penetration testers, and cyber security students building their toolkit.
38 articles
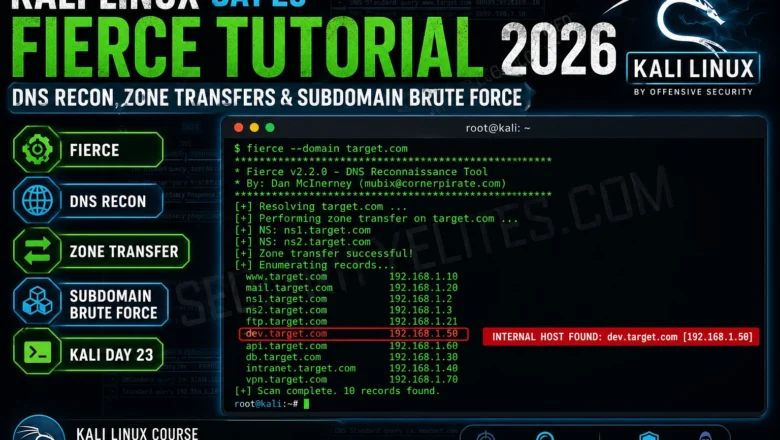
Kali Linux Day 23 — Fierce DNS Reconnaissance Tutorial 2026
Kali Linux Day 23: Fierce DNS reconnaissance tutorial — how to use Fierce for subdomain enumeration, DNS zone walking, and…
Shodan Tutorial Kali Linux 2026 — Search Engine for Hackers, Dork Queries & API Usage | Hacking Tools Day22
Shodan Tutorial in Kali Linux for 2026. Search exposed devices, run dork queries, use the API and build a recon…
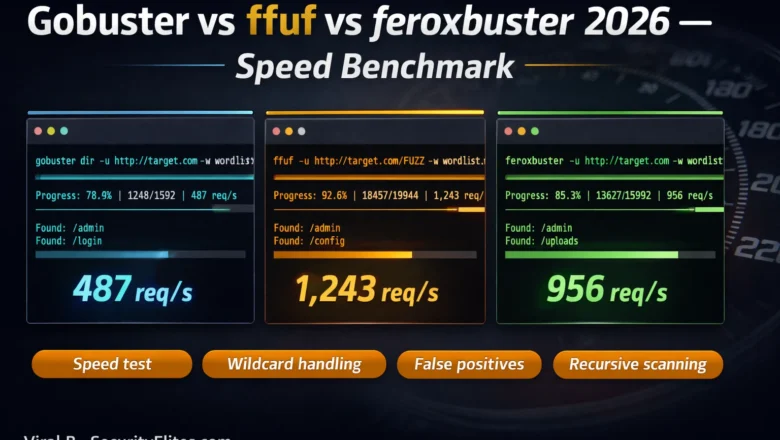
Gobuster vs ffuf vs feroxbuster — Speed & Accuracy Benchmark 2026
Gobuster vs ffuf vs feroxbuster 2026 — side-by-side speed and accuracy benchmark. Which directory fuzzer wins on speed, false positives,…
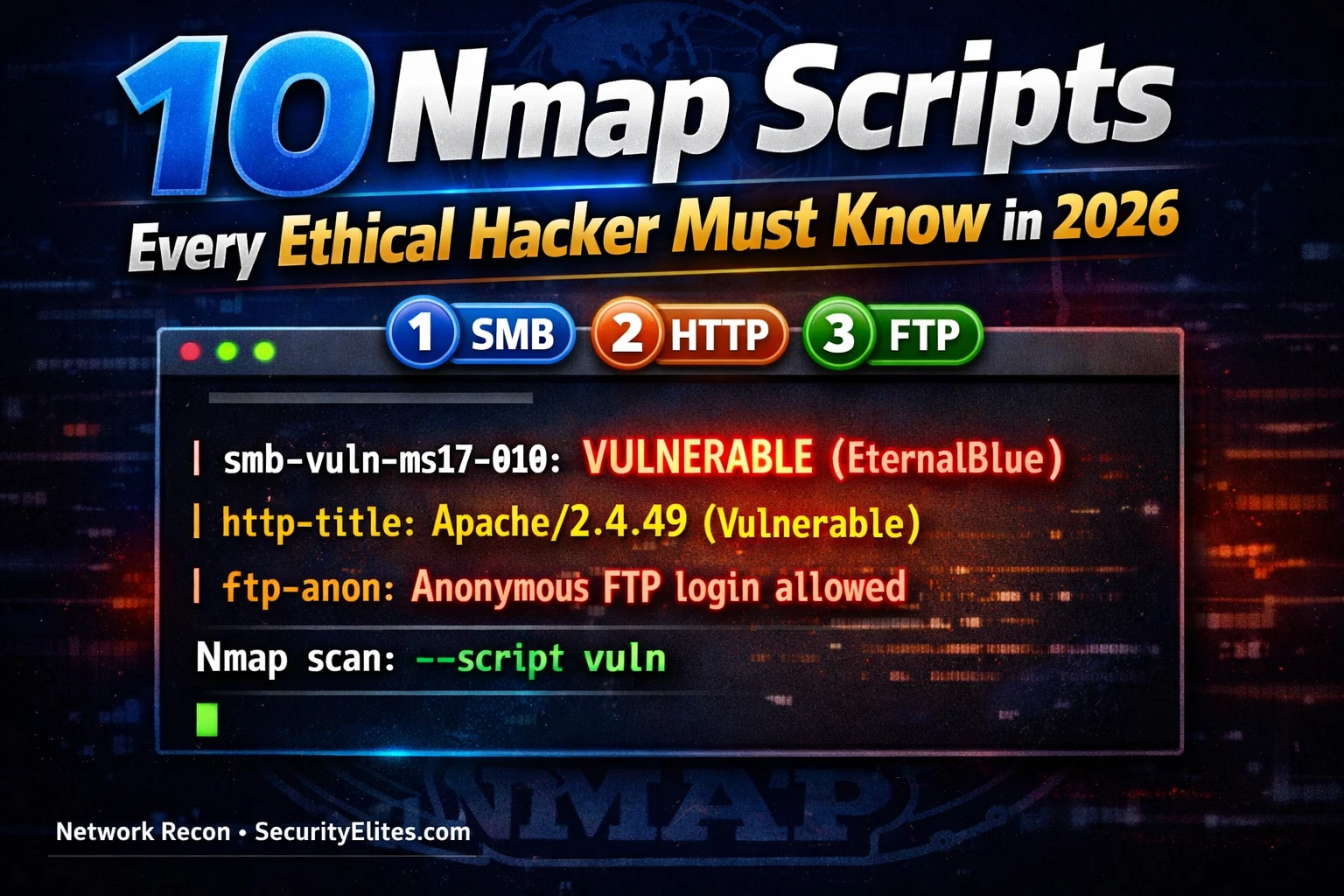
10 Nmap Scripts Every Ethical Hacker Must Know in 2026 (With Examples)
10 nmap scripts every ethical hacker must know in 2026 — NSE scripts for vuln scanning, SMB enumeration, HTTP discovery,…
How to Use Shodan 2026 — The Hacker’s Search Engine Complete Guide
How to use shodan 2026 — search internet-connected devices, find exposed services, use Shodan dorks for bug bounty recon and…
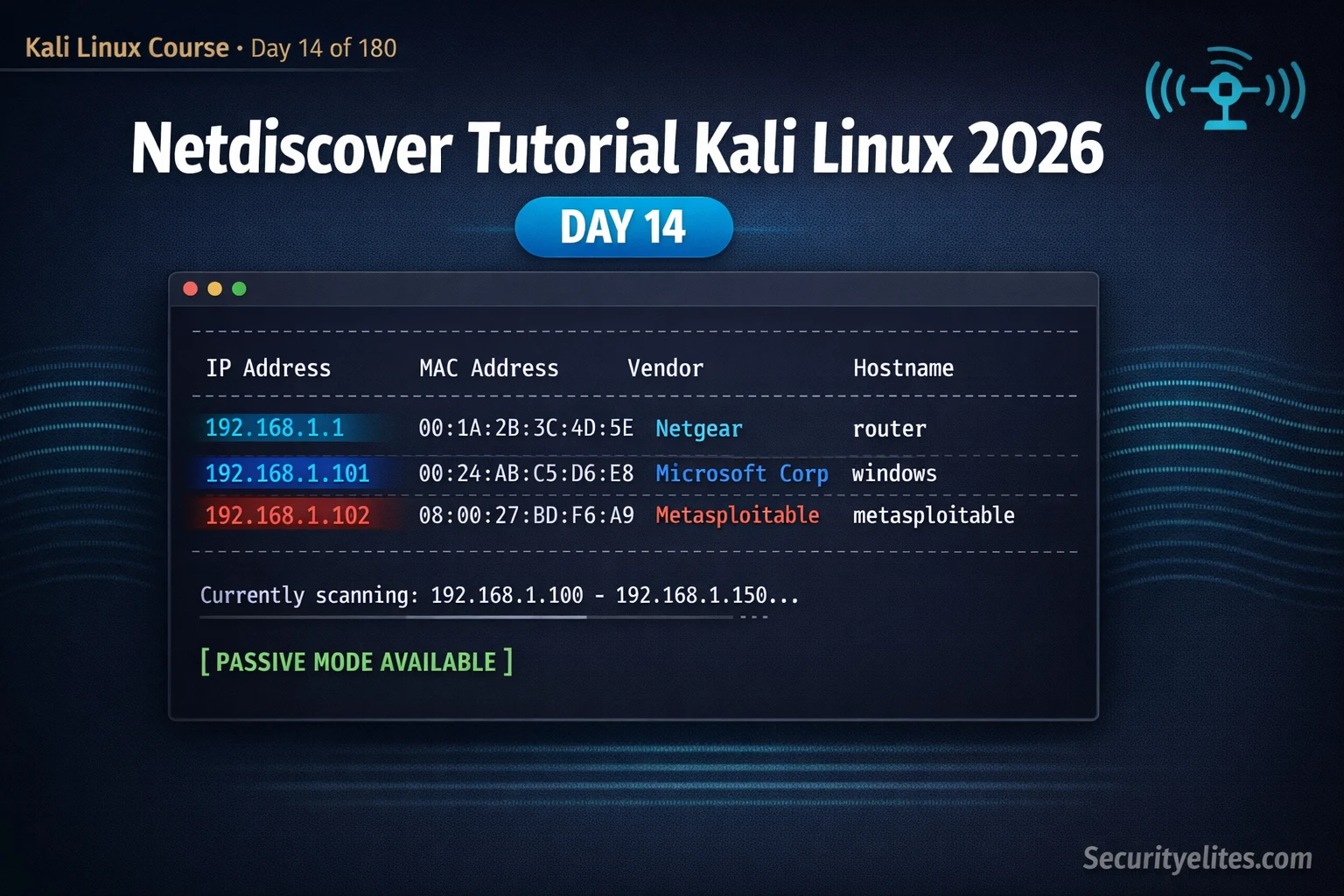
Kali Linux Day14: Netdiscover Tutorial Kali Linux 2026 — Instantly Discover Every Device on Your Network
Netdiscover tutorial kali linux 2026 — discover live hosts on local networks using ARP scanning, passive mode and IP range…
Kali Linux Commands Cheat Sheet 2026 — 150 Tools, 2955 Commands, One Click
Kali linux commands cheat sheet 2026 — 150 tools, 2955+ ready-to-use commands across 13 categories. Filter by tool, copy any…
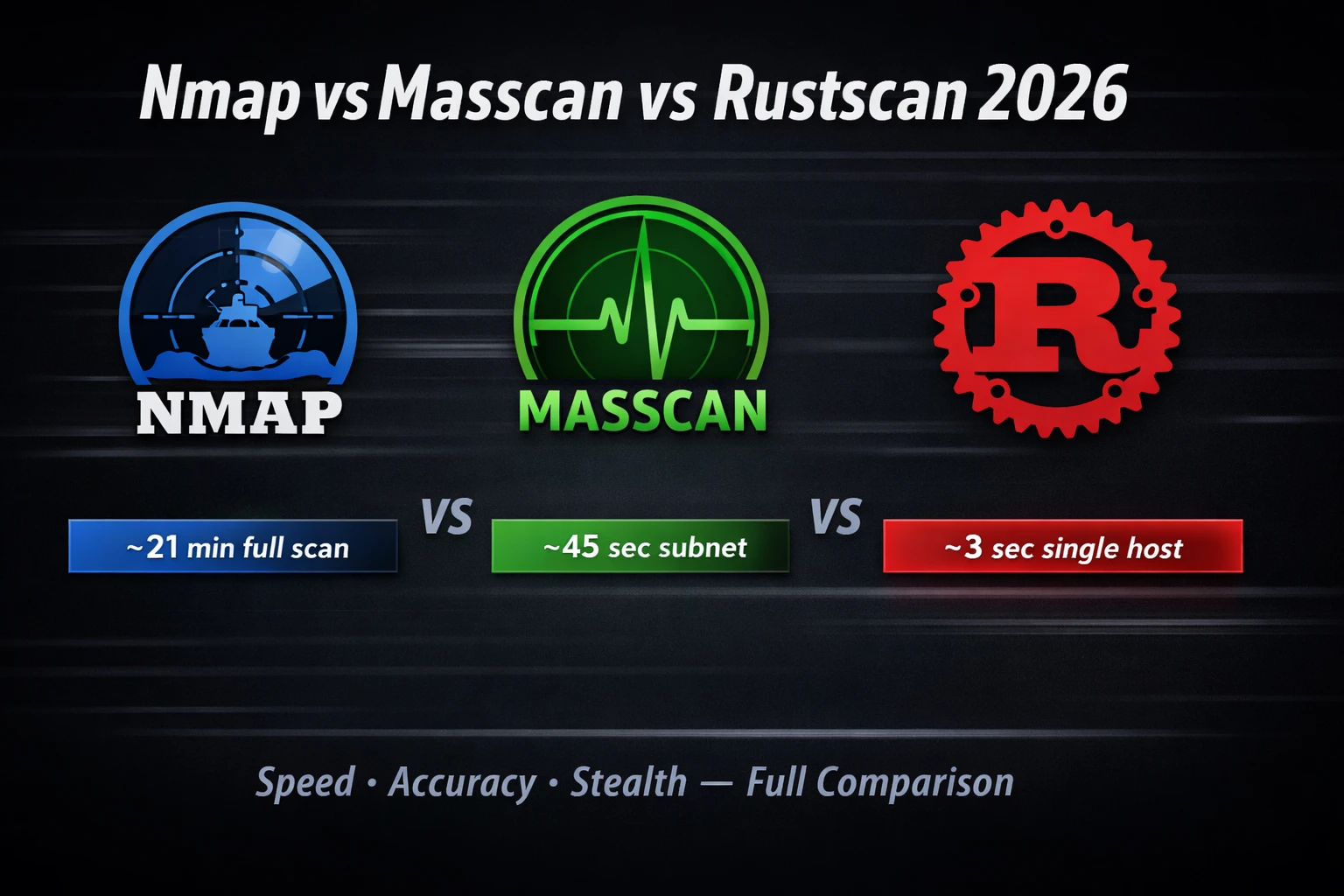
Nmap vs Masscan vs Rustscan 2026 — Which Port Scanner Is Fastest & Most Accurate?
Nmap vs masscan vs rustscan 2026 — speed benchmarks, accuracy tests, stealth comparison and which scanner to use for recon,…
10 Best Hacking Tools in 2026 — What Every Ethical Hacker Actually Uses
The 10 best hacking tools in 2026 ranked by real-world usage — Kali Linux, Burp Suite, Metasploit, Nmap, and more.…