Bug Bounty Hunting
Start your bug bounty hunting journey with complete beginner-to-advanced tutorials on finding and reporting vulnerabilities. Learn reconnaissance techniques, subdomain enumeration, Google dorking, automation tools, and vulnerability validation methods used by top bug bounty hunters. This section also includes real bug bounty case studies, report writing tips, and platform guides like HackerOne and Bugcrowd to help you earn rewards by ethically reporting security flaws.
89 articles
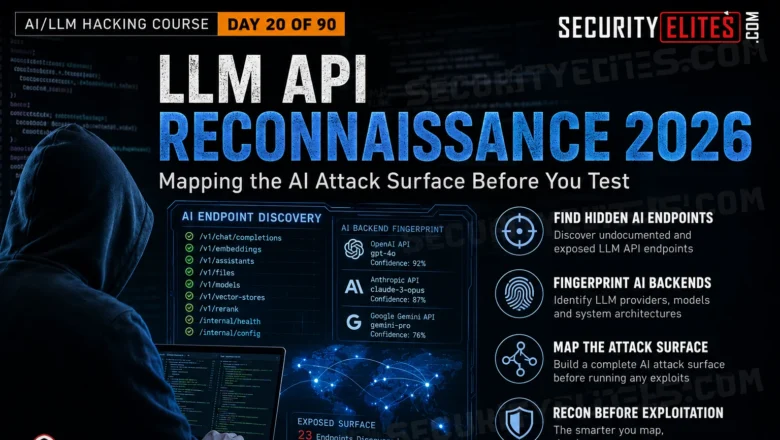
How to Perform LLM API Reconnaissance – Mapping the AI Attack Surface Before You Test | Day 20
Master LLM API reconnaissance in 2026. Find undocumented AI endpoints, map attack surfaces, fingerprint AI backends and build the test…
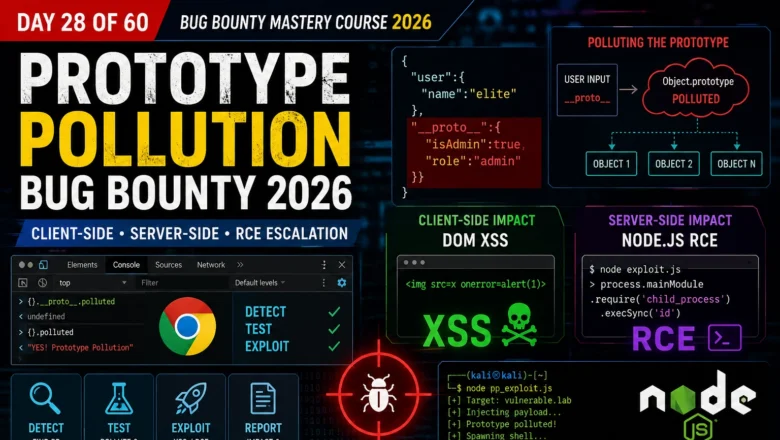
Prototype Pollution Bug Bounty — Client-Side, Server-Side & RCE Escalation | BB Day 28
Master prototype pollution for bug bounty 2026. Client-side DOM XSS chains, server-side Node.js RCE, detection with Chrome DevTools, and full…
LLM-Powered OSINT 2026 — Using AI to Automate Open Source Intelligence Gathering
LLM-Powered OSINT 2026 — How security researchers use LLMs to automate OSINT in 2026. AI for email harvesting, subdomain synthesis,…
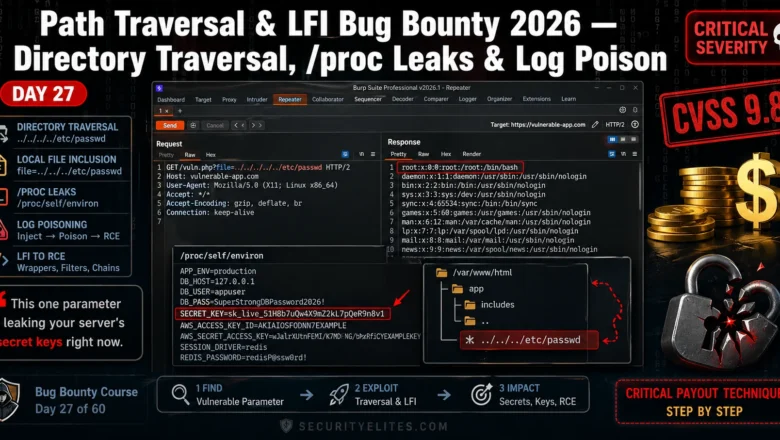
Path Traversal LFI Bug Bounty 2026 — Directory Traversal, proc Leaks & Log Poison | BB Day 27
Master path traversal LFI bug bounty in 2026. Directory traversal, /proc leaks, log poisoning — real techniques that earn Critical…
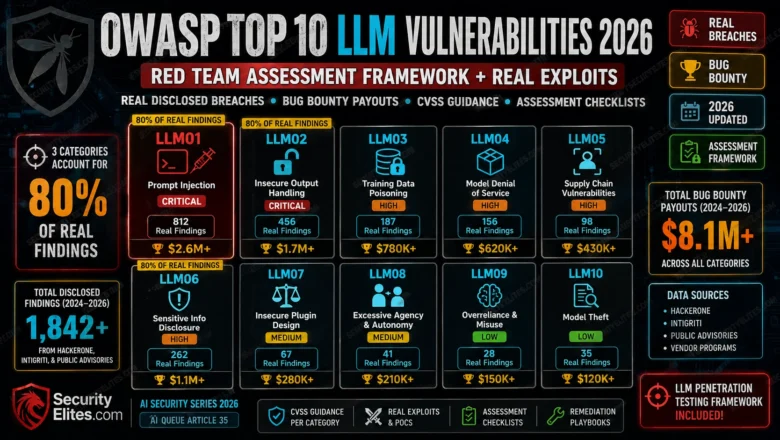
OWASP Top 10 LLM Vulnerabilities 2026 — Red Team Assessment Framework + Real Exploits
OWASP Top 10 LLM Vulnerabilities 2026 red team framework. Real disclosed breaches, bug bounty payouts, CVSS guidance, and assessment checklists…
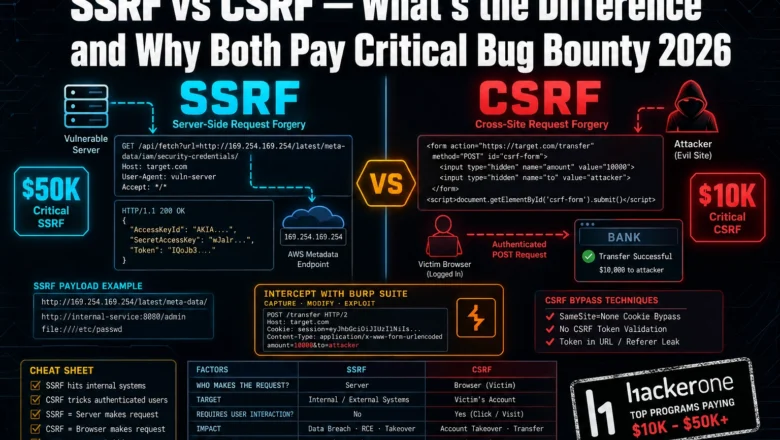
SSRF vs CSRF Bug Bounty 2026— What’s the Difference and Why Both Pay Critical
Most bug bounty hunters mix up SSRF and CSRF — and miss critical payouts because of it. Here's exactly how…
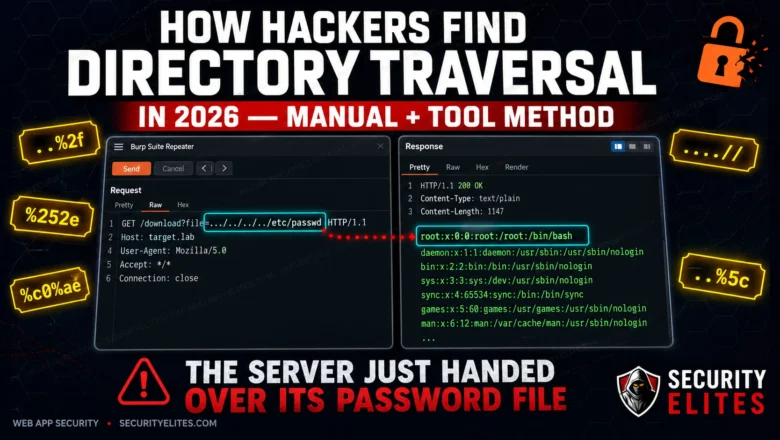
How Hackers Find Directory Traversal in 2026 — Manual + Tool Method
Directory traversal is still landing critical findings on HackerOne in 2026. Here's the exact manual and automated method hackers use…
SSTI Bug Bounty 2026 — Server-Side Template Injection to RCE on 5 Template Engines | BB Day 26
Server-Side Template Injection turns a misplaced expression into a shell. I'll walk you through detection, exploitation chains, and RCE payloads…
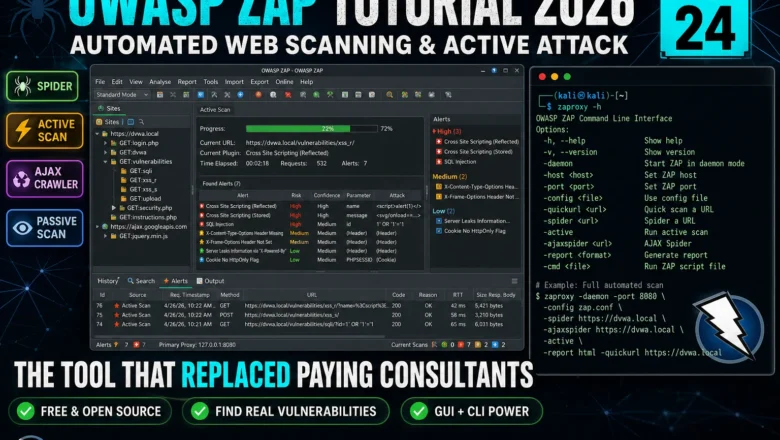
OWASP ZAP Tutorial 2026 — Automated Web Scanning, Spider & Active Attack | Kali Linux Tools Day24
Master OWASP ZAP in Kali Linux 2026. Spider, passive scan, active attack, AJAX crawl, and integrating ZAP into a professional…