Password Cracking Tools
This password cracking tools tutorial section explains how security professionals audit password strength using controlled lab environments. Learn how tools like John the Ripper, Hydra, and Hashcat work in password auditing and brute-force simulations. Each tutorial focuses on understanding hashing mechanisms, attack techniques, and defense strategies such as strong password policies and multi-factor authentication. Practical labs help readers understand password security risks and mitigation techniques.
14 articles
Cracking Passwords using AI – How AI Makes Weak Passwords Even More Dangerous
Cracking Passwords using AI in 2026. How AI-powered tools crack passwords faster, PassGAN research, what makes a password AI-resistant, and…
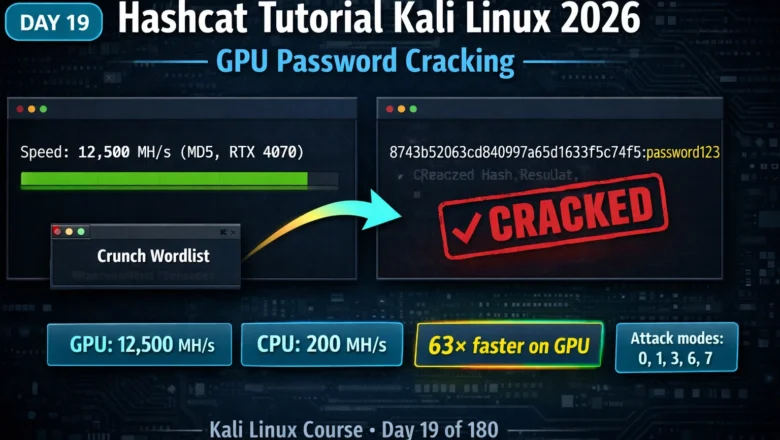
Kali Linux Day19: Hashcat Tutorial Kali Linux 2026 — GPU Password Cracking, Attack Modes & Benchmarking
Hashcat tutorial Kali Linux 2026 — master GPU password cracking with dictionary, mask, rule-based and combinator attack modes. Crack MD5,…
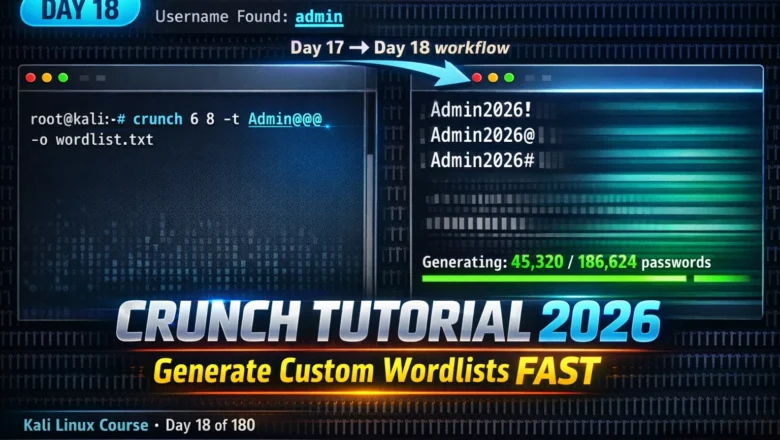
Kali Linux Day18: Crunch Tutorial Kali Linux 2026 — Generate Custom Wordlists for Targeted Password Attacks
Crunch tutorial kali linux 2026 — generate custom password wordlists using patterns, character sets and rules. Day 18 complete guide…
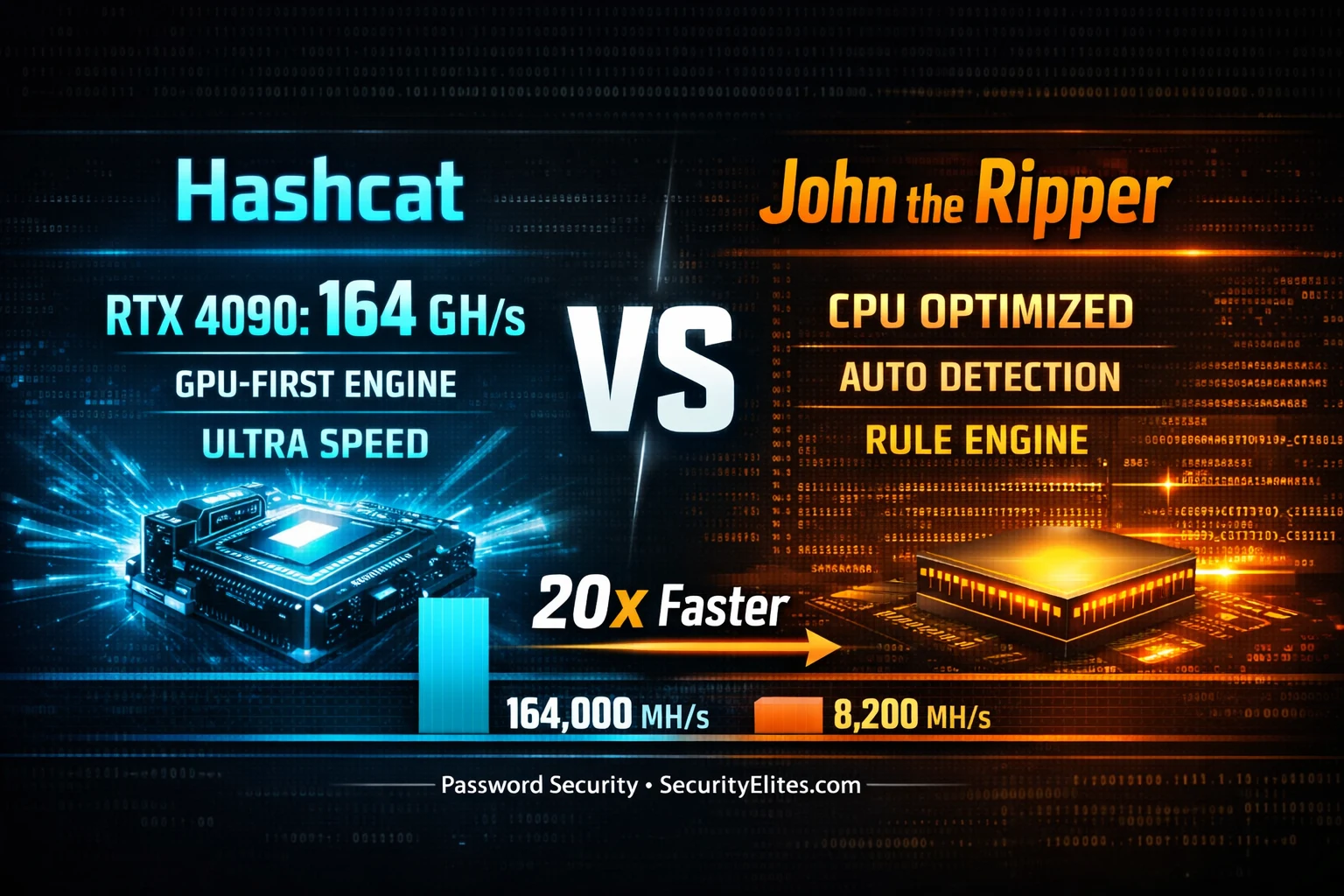
Hashcat vs John the Ripper 2026 — The 20x Speed Gap No One Talks About
Hashcat vs John the Ripper 2026 — real benchmark comparison on GPU vs CPU for MD5, NTLM, bcrypt and SHA256.…
Kali Linux Commands Cheat Sheet 2026 — 150 Tools, 2955 Commands, One Click
Kali linux commands cheat sheet 2026 — 150 tools, 2955+ ready-to-use commands across 13 categories. Filter by tool, copy any…
10 Best Hacking Tools in 2026 — What Every Ethical Hacker Actually Uses
The 10 best hacking tools in 2026 ranked by real-world usage — Kali Linux, Burp Suite, Metasploit, Nmap, and more.…
Kali Linux Day 11: Aircrack-ng Tutorial 2026 — Crack WiFi Passwords & Audit WPA2 Security
Aircrack-ng tutorial in Kali Linux 2026 — capture WPA2 handshakes, run dictionary attacks, audit wireless security. Day 11 complete guide…
Kali Linux Day 5: John the Ripper Tutorial — Crack Hashes, /etc/shadow, ZIP & PDF Passwords (Complete Guide 2026)
Complete John the Ripper tutorial for Kali Linux — identify hashes, crack /etc/shadow with unshadow, use wordlist mode, rule-based cracking,…
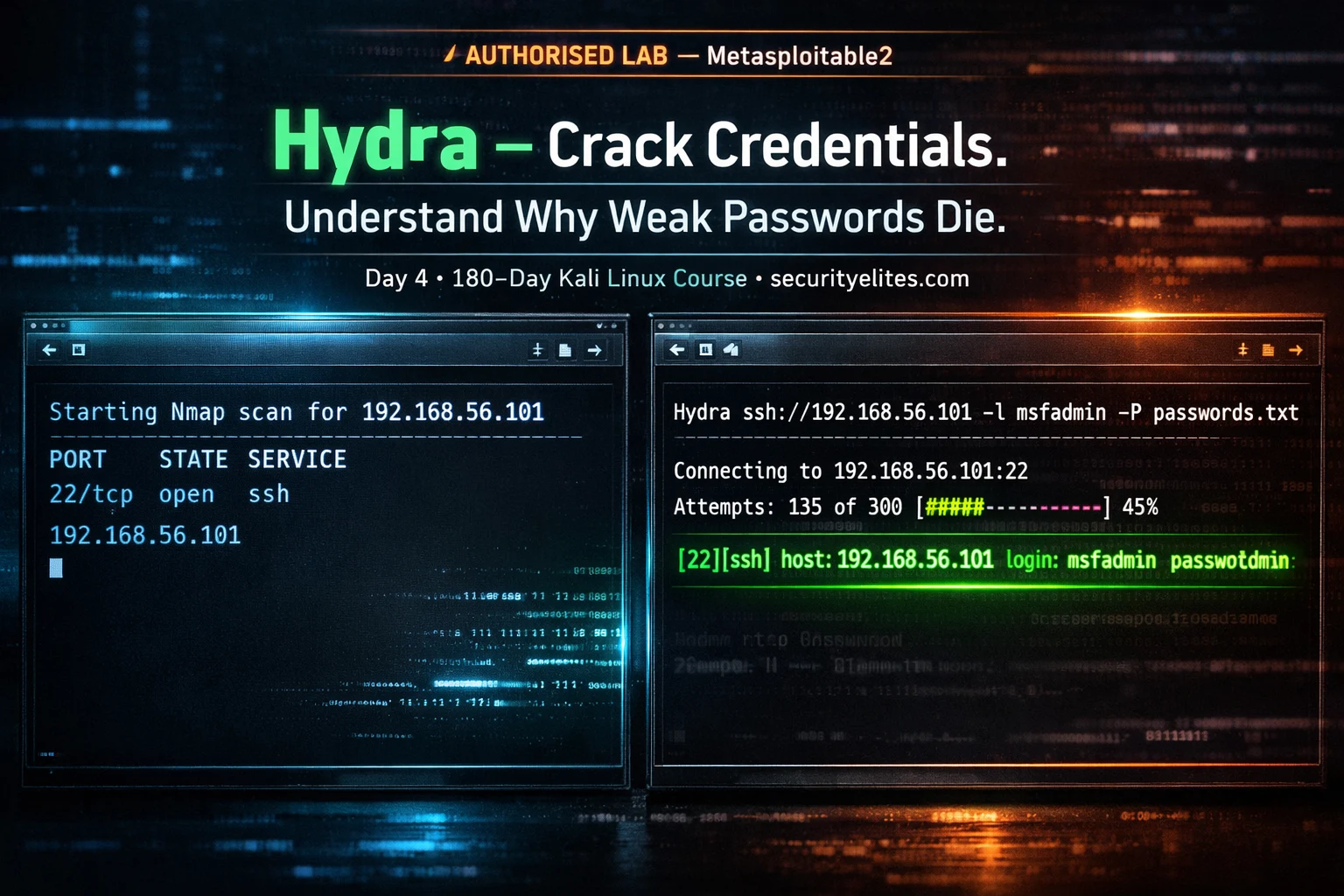
Kali Linux Day 4: Hydra Tutorial — Brute Force SSH, FTP, HTTP & 50+ Protocols (Complete Beginner Guide 2026)
Complete Hydra tutorial for Kali Linux — brute force SSH, FTP, HTTP login forms, RDP, MySQL, and 50+ protocols. Every…