Cyber Security Courses & Training
This best cyber security courses online section helps learners choose the right training programs to build technical expertise. Tutorials include free and paid courses, certification training, lab platforms, and degree programs. You will find course comparisons, syllabus breakdowns, pricing insights, and career outcomes. Whether you prefer self-paced learning, bootcamps, or university programs, this category provides complete training guidance for cyber security learners.
51 articles
50 Cybersecurity Interview Questions 2026 — Real Questions + Model Answers
50 real cybersecurity interview questions with model answers for 2026. Covers analyst, SOC, pentester, and engineer roles — fundamentals to…
eJPT Certification 2026 — Is It Worth It, How Hard Is It, and Who Should Skip It
Honest 2026 review of the eJPT certification. Exam difficulty, employer value, cost, who should take it vs skip it, and…
SecurityElites Launched 47 Free Hacking Labs 2026 — No Signup, No VM, No Setup – Start Your Hacking Journey Now
SecurityElites Just launched 47 free hacking labs — no signup, no VM. AI hacking (17 labs), XSS, JWT, SSRF, SSRF,…
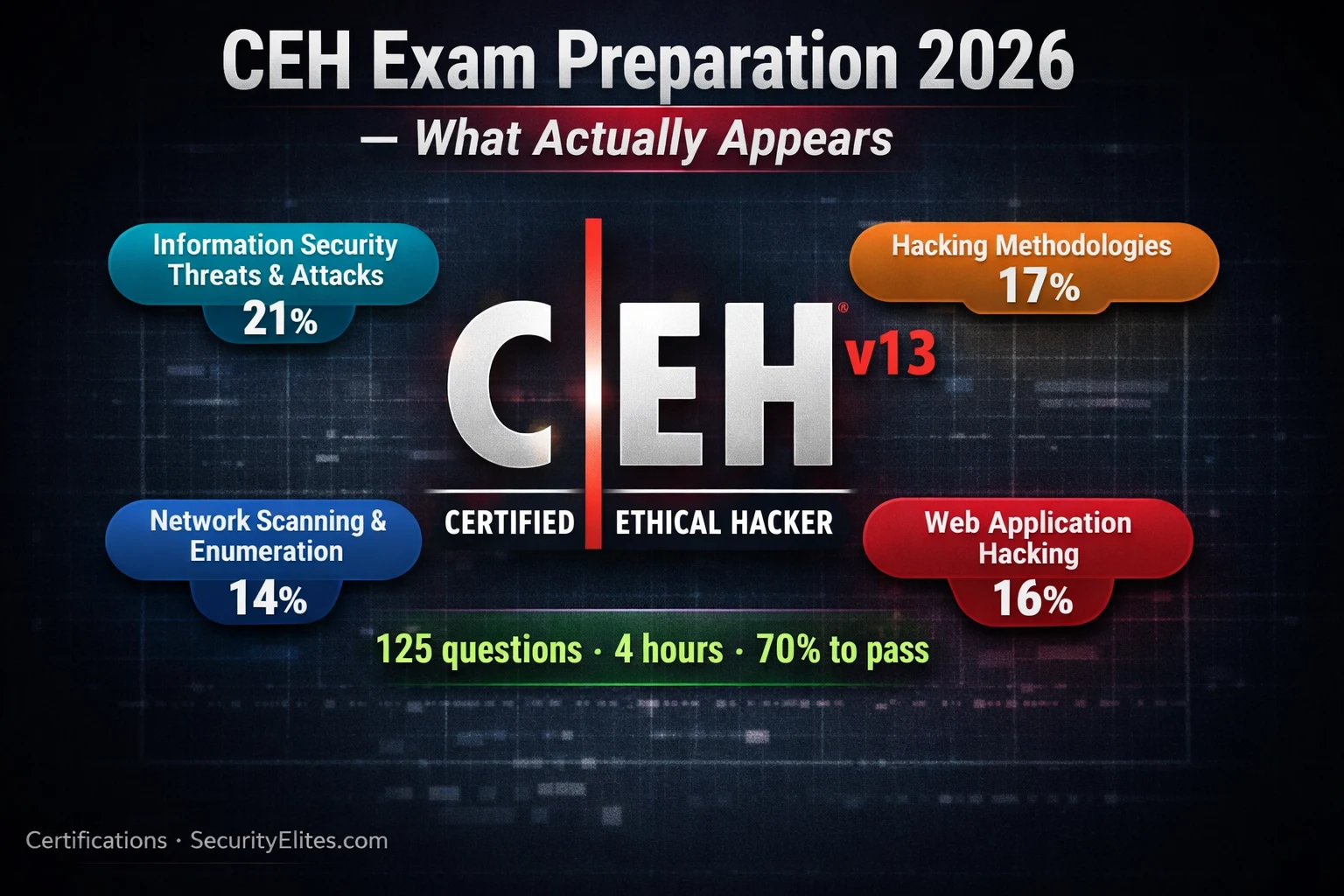
CEH Exam Preparation 2026 — What Actually Appears and How to Pass First Try
CEH exam preparation 2026 — what actually appears on the EC-Council CEH v13 exam, the best study resources, and how…
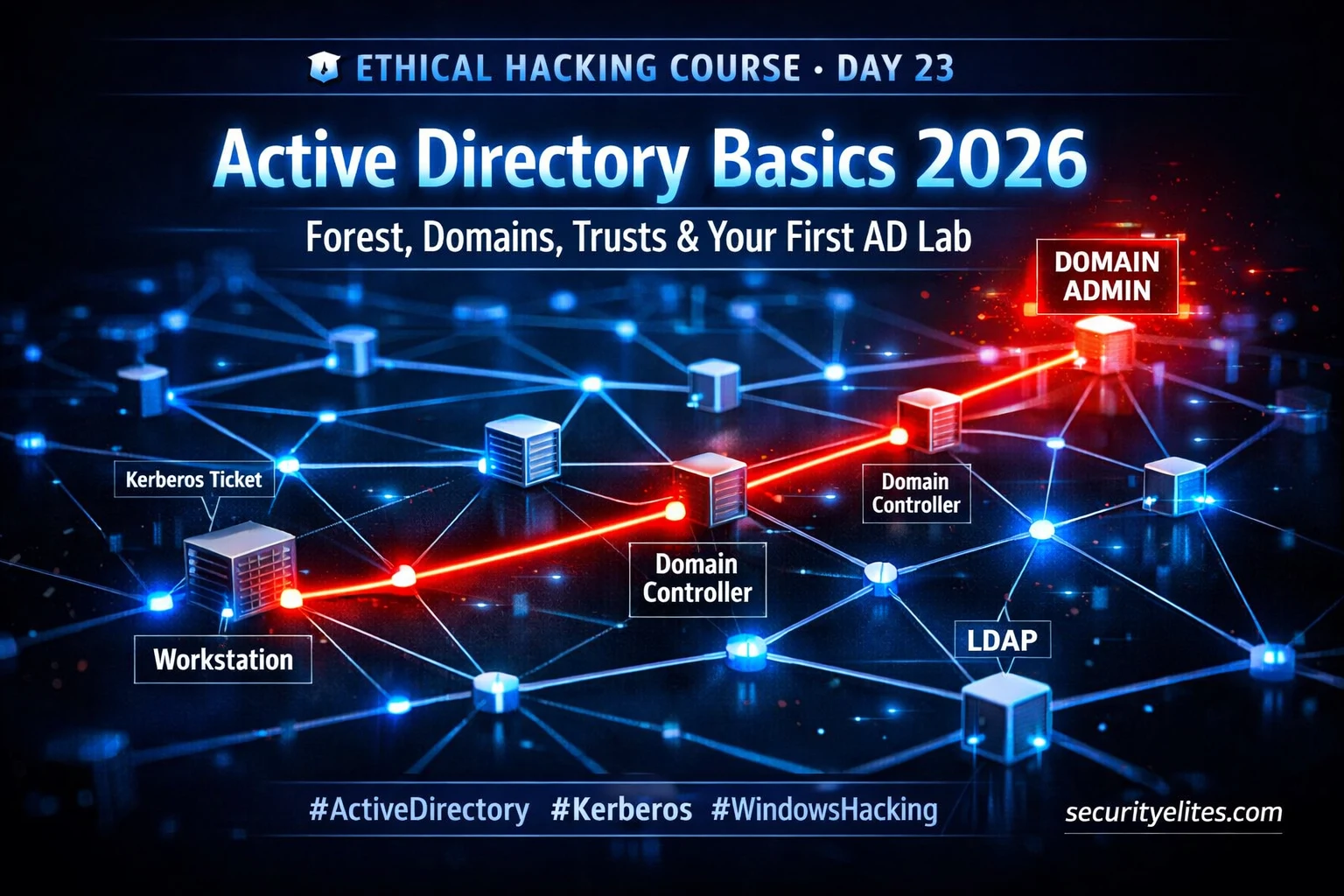
Day 23 : Active Directory Basics 2026 — Forest, Domains, Trusts & First AD Lab
Master active directory basics for ethical hacking 2026 — forests, domains, Kerberos, attack surface & free lab setup. Day 23…
Day 11: Open Redirect Bug Bounty Hunting 2026 — Find, Chain and Report the Vulnerability That Turns $200 Bugs Into $5,000 Findings
Day 11 of 60. Master open redirect bug bounty hunting with manual testing, bypass techniques, OAuth chaining for account takeover,…
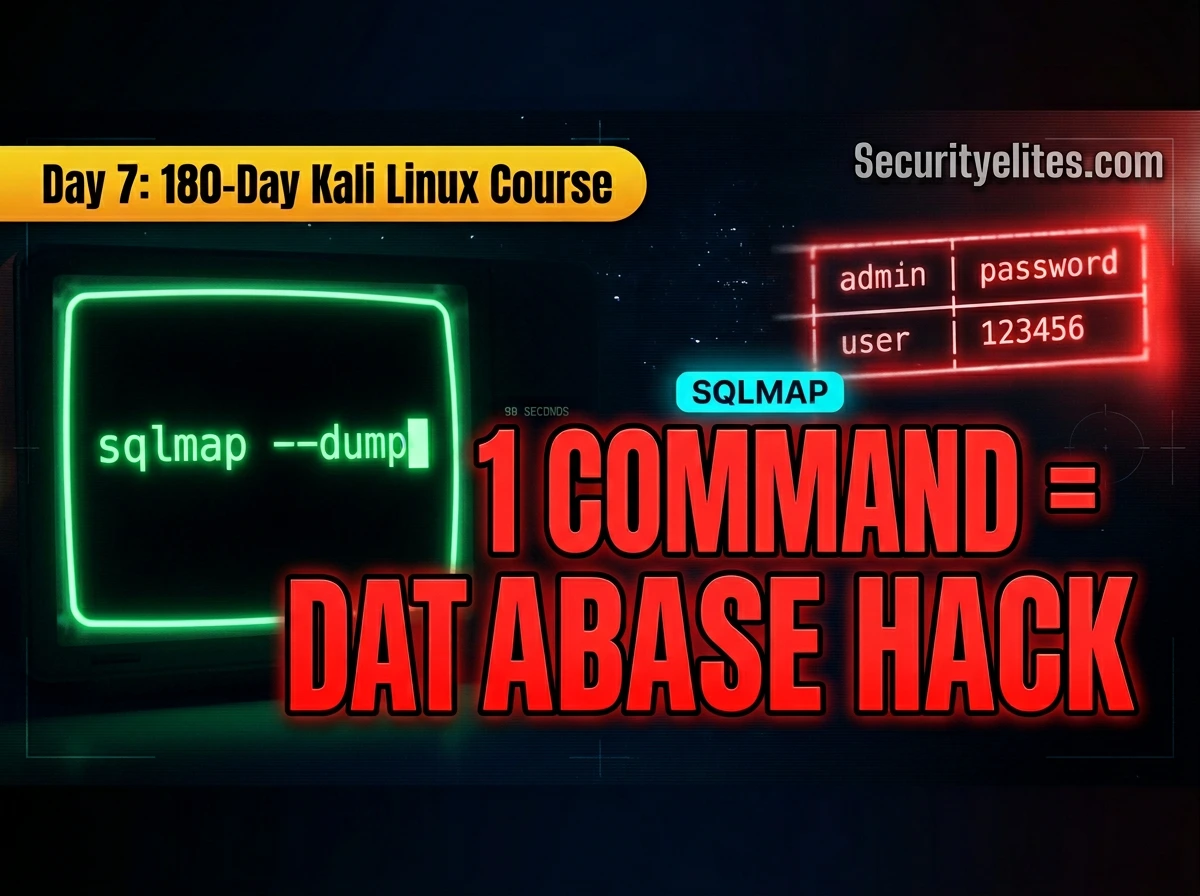
Kali Linux Day 7: SQLmap Tutorial (2026) — Automate SQL Injection Like a Pro 🔥
Complete SQLmap tutorial for Kali Linux — detect SQL injection, enumerate databases, extract tables, dump credentials, use Burp request files,…
Day 21: Metasploit Framework — From Module to Shell (Complete Beginner’s Guide 2026)
Day 21 of 100. Master the Metasploit Framework — msfconsole commands, auxiliary and exploit modules, Meterpreter, and a full Metasploitable…
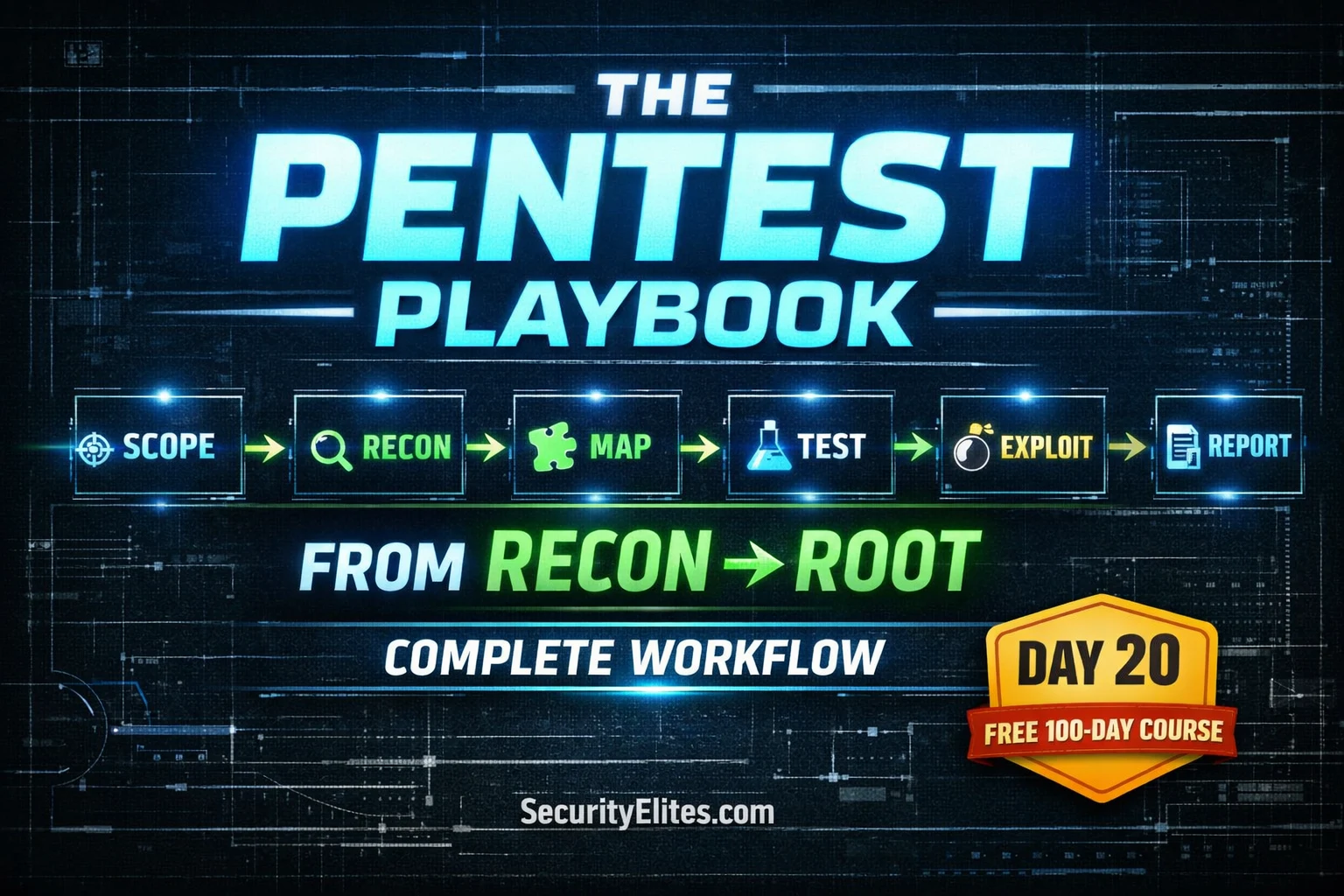
Day 20: Web Application Penetration Testing Methodology 2026 — Zero to Pro Hacker Workflow (Complete Guide)
Day 20 of 100. Master the complete web app pentesting methodology—scoping, reconnaissance, mapping, testing, exploitation, and reporting. A professional framework…