Footprinting & Reconnaissance
Footprinting and reconnaissance are the first and most critical phases of ethical hacking, where security professionals gather intelligence about a target before launching any attack simulation. This section covers passive and active reconnaissance techniques including domain analysis, WHOIS lookup, DNS enumeration, social media intelligence, and public data mining. You’ll learn how ethical hackers use reconnaissance tools to map attack surfaces, identify entry points, and collect valuable system information. Step-by-step tutorials, tool guides, and lab demonstrations will help you master information gathering legally and effectively.
37 articles
What Hackers Can Do With Your IP Address And What They Can’t 2026
What hackers can do with your IP address in 2026? The real risks, the myths, DDoS attacks, geolocation limits, and…
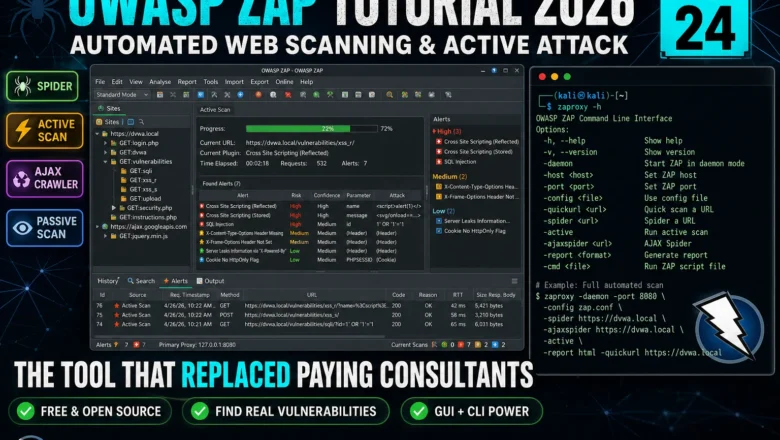
OWASP ZAP Tutorial 2026 — Automated Web Scanning, Spider & Active Attack | Kali Linux Tools Day24
Master OWASP ZAP in Kali Linux 2026. Spider, passive scan, active attack, AJAX crawl, and integrating ZAP into a professional…
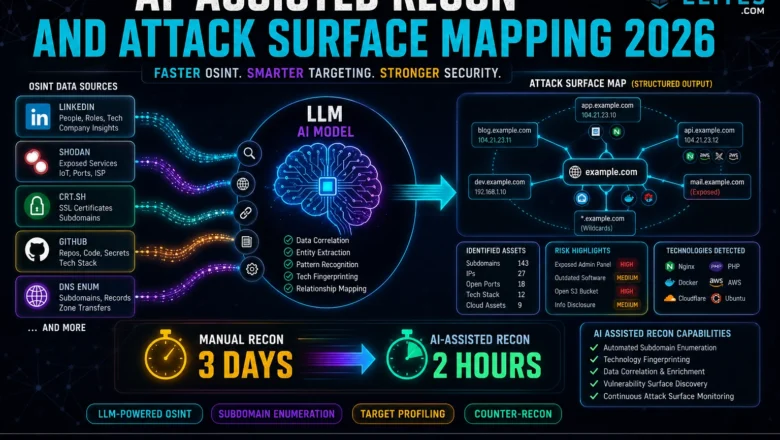
AI-Assisted Recon and Attack Surface Mapping 2026 — How hackers use LLMs to map attack surfaces faster
AI-Assisted Recon & Attack Surface Mapping - How hackers use LLMs to map attack surfaces faster in 2026. AI-assisted OSINT,…
How to Use Shodan 2026 — The Hacker’s Search Engine Complete Guide
How to use shodan 2026 — search internet-connected devices, find exposed services, use Shodan dorks for bug bounty recon and…
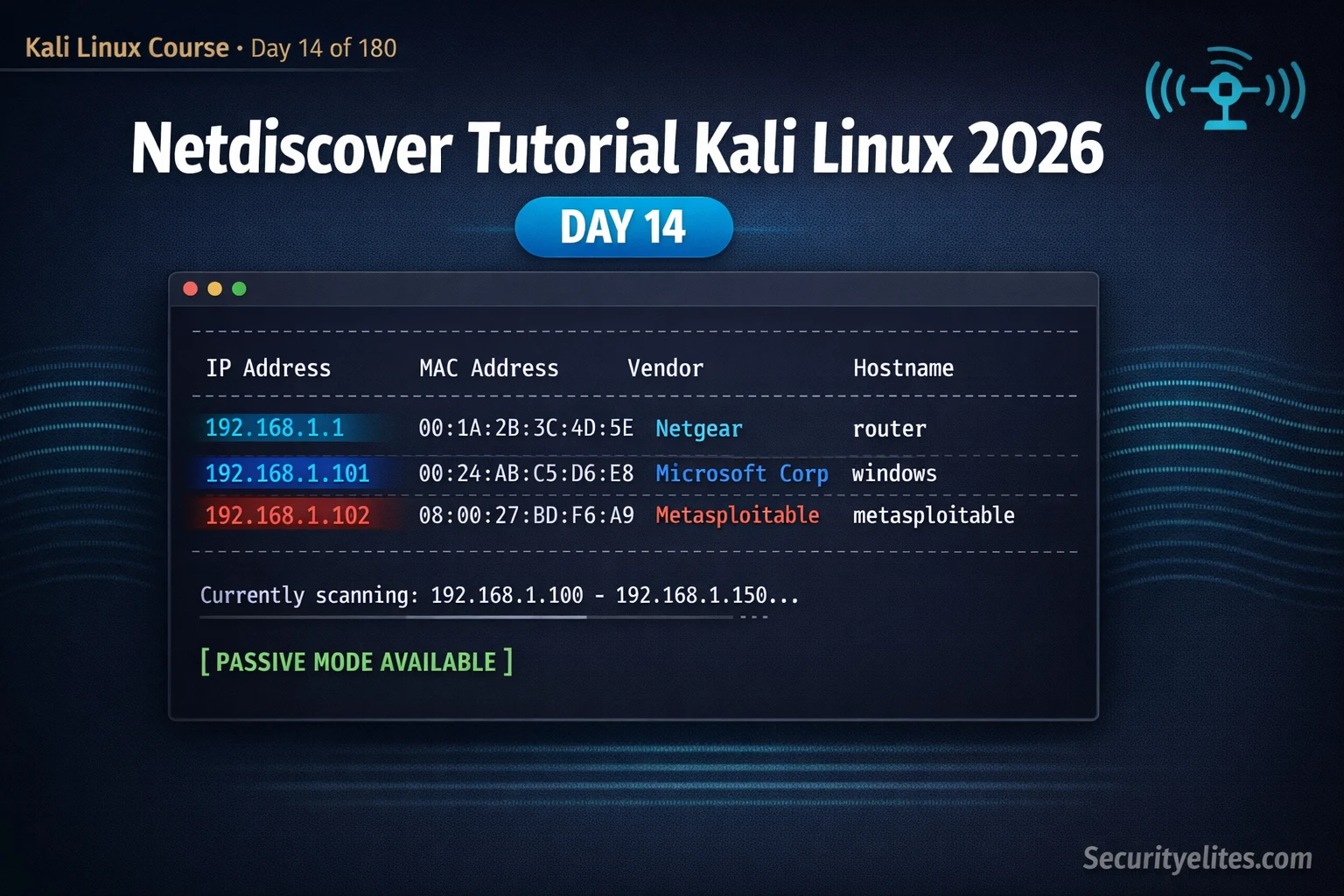
Kali Linux Day14: Netdiscover Tutorial Kali Linux 2026 — Instantly Discover Every Device on Your Network
Netdiscover tutorial kali linux 2026 — discover live hosts on local networks using ARP scanning, passive mode and IP range…
Google Dorking for Hackers 2026 — 50 Dorks to Find Vulnerabilities and Exposed Data
Google dorking for hackers 2026 — 50 essential Google dorks to find exposed admin panels, config files, passwords, subdomains and…
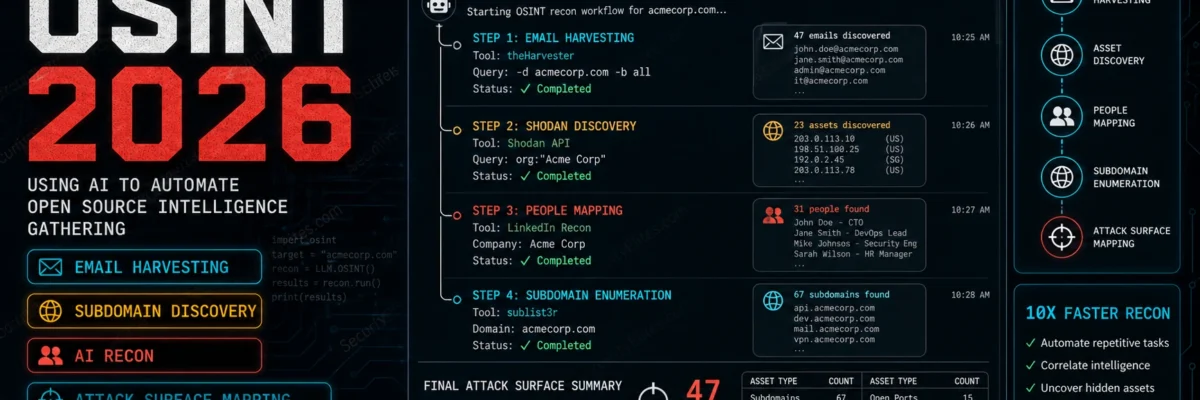
How Hackers Use theHarvester to Find Emails in Seconds (Most Don’t Know This)
Discover how hackers use theHarvester to harvest real employee emails from public sources in seconds — the OSINT technique most…
Passive vs Active Reconnaissance — 90% of Beginners Do This Wrong (2026 Hacker Guide)
Master Passive vs Active Reconnaissance for ethical hacking and bug bounty. Learn passive recon (OSINT, WHOIS, certificate transparency) vs active…
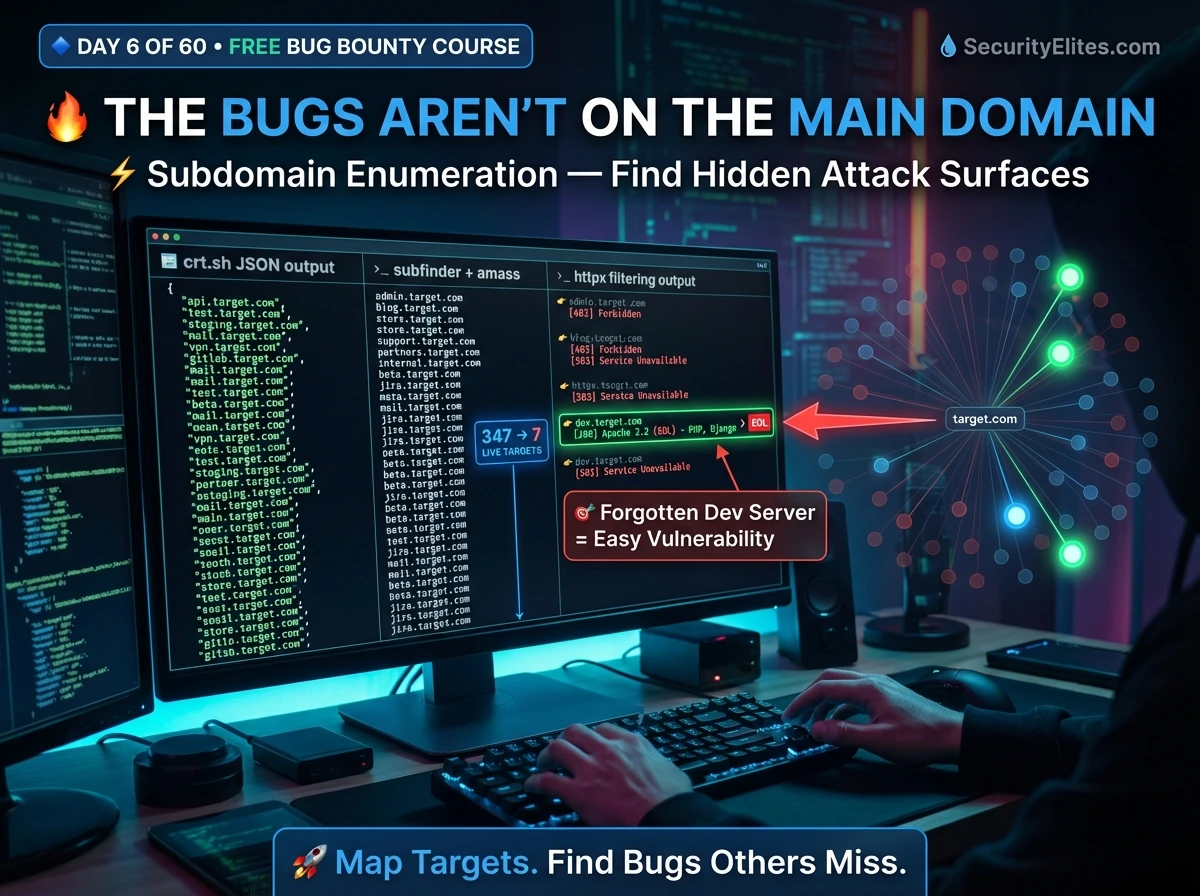
Bug Bounty Day 6: Subdomain Enumeration — Build Your Full Attack Surface Map (2026)
Master subdomain enumeration for bug bounty — Subfinder, Amass, crt.sh, httpx live filtering, ffuf directory fuzzing, and building a professional…