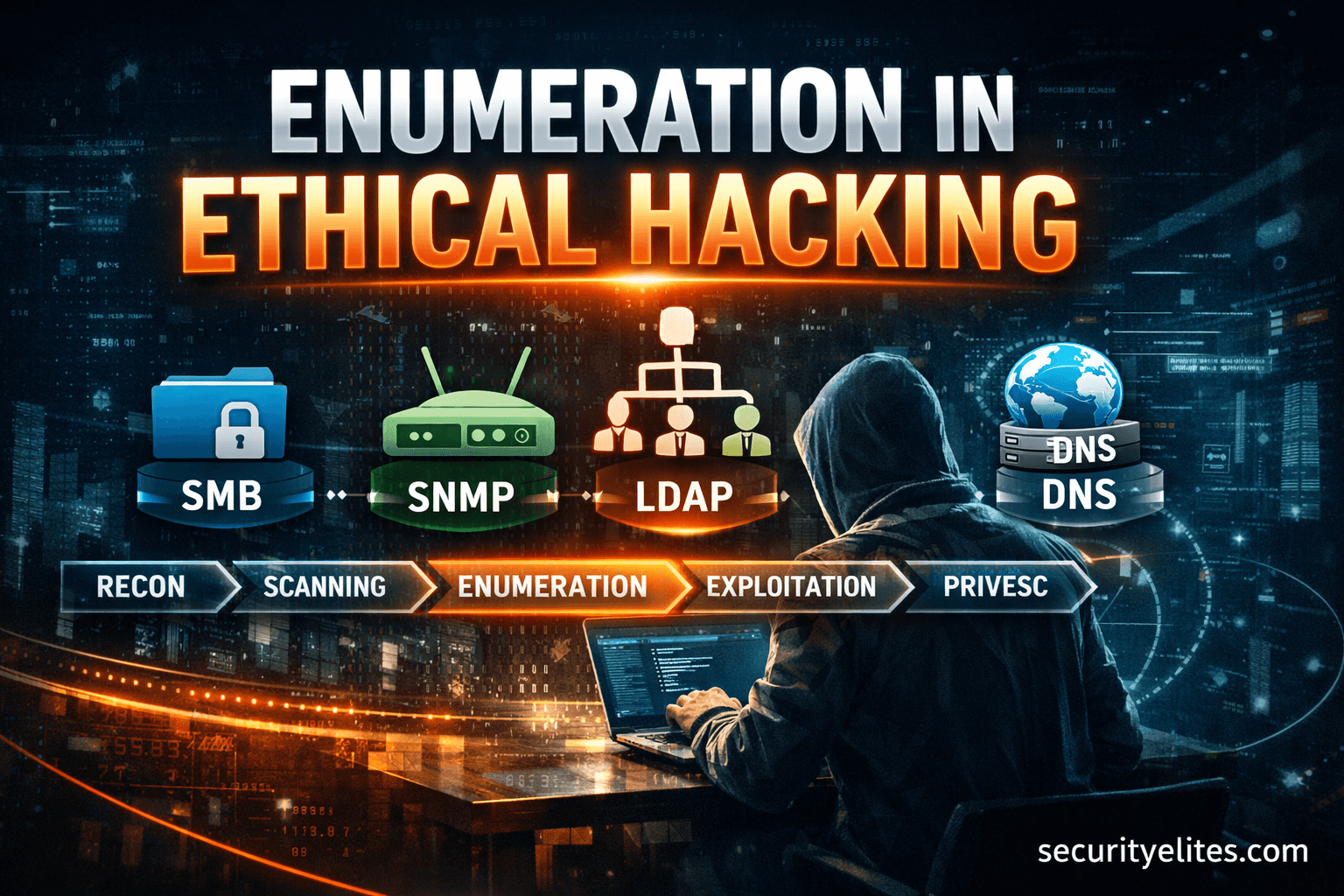
Enumeration
Enumeration is the process of extracting detailed system and user information after initial scanning. This sub-category teaches how to enumerate SMB shares, users, groups, DNS records, SNMP data, and LDAP services. You’ll learn practical enumeration techniques used in penetration testing to uncover hidden network resources and misconfigurations. Step-by-step labs demonstrate how attackers move from scanning to exploitation using gathered intelligence.
9 articles
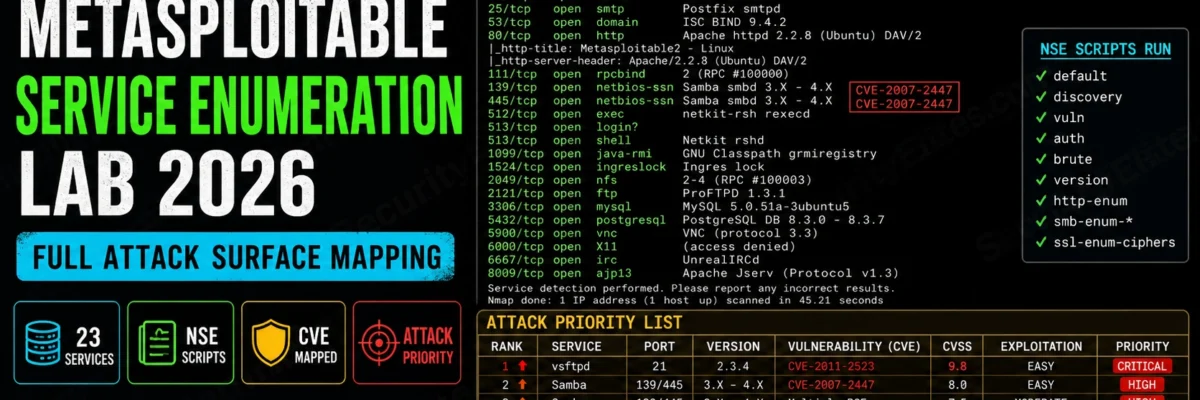
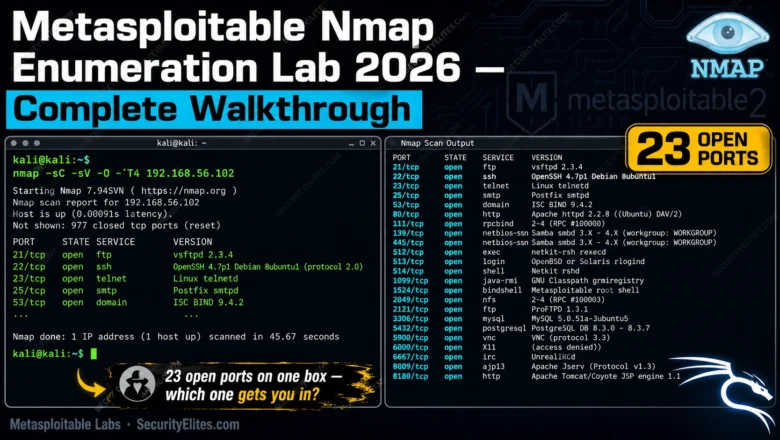
Metasploitable Nmap Enumeration Lab 2026 — Complete Walkthrough | Hacking Lab 32
Run your first real Nmap enumeration against Metasploitable in 2026. Full lab walkthrough — every scan, every flag, every result…
How Hackers Find Subdomain Takeovers — The 15-Second Check That Pays $1,000
Subdomain takeover guide 2026. The 3-command DNS check that finds dangling CNAME records, which cloud services allow takeover, how to…
Kali Linux Day15: Enum4linux Tutorial Kali Linux 2026 — SMB Enumeration, User Listing & Share Discovery
Enum4linux tutorial kali linux 2026 — enumerate Windows & Samba SMB targets for users, shares, password policies and OS information.…
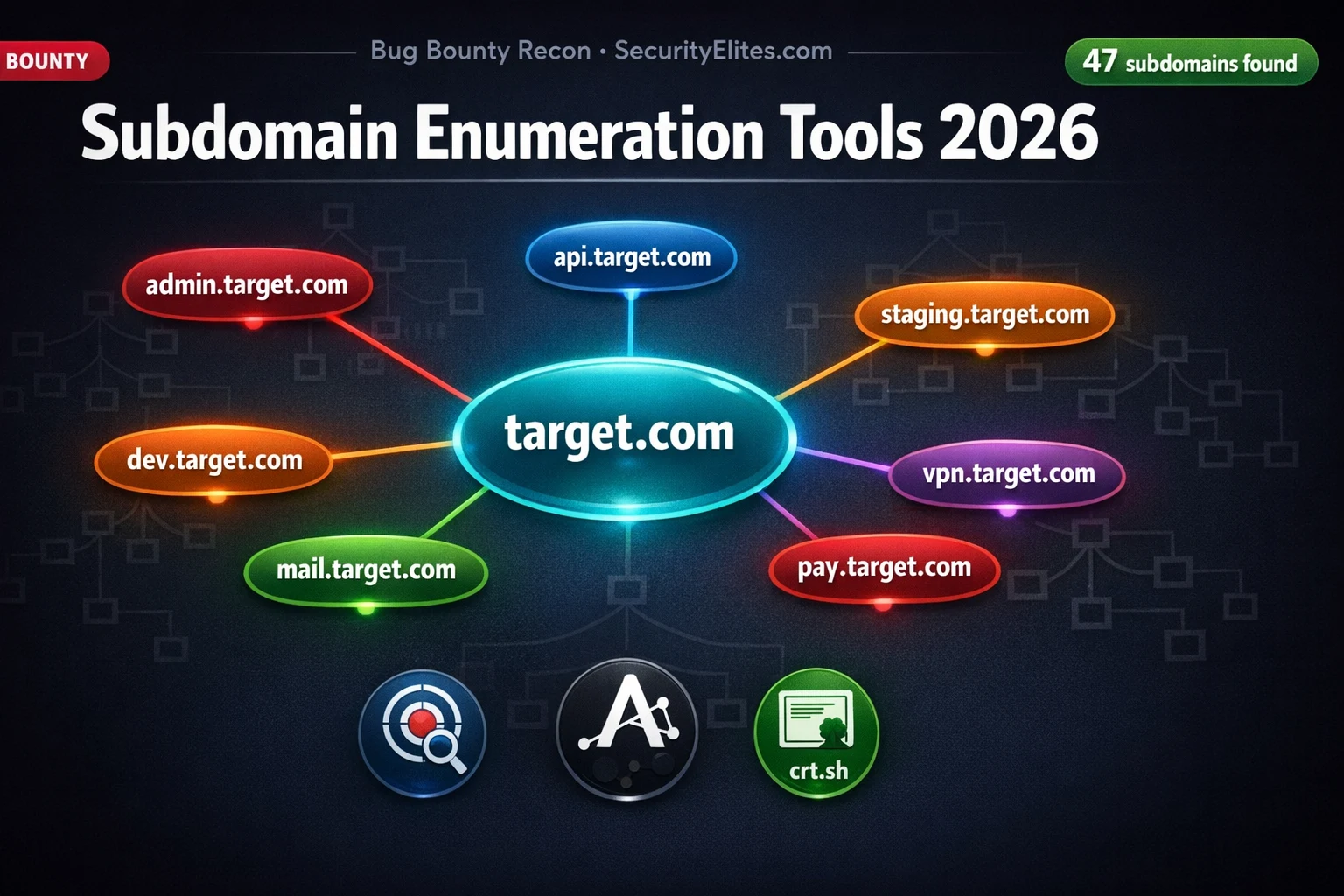
Subdomain Enumeration Tools 2026 — 7 Best Methods to Find Every Hidden Subdomain
Subdomain enumeration tools 2026 — best methods using Subfinder, Amass, Assetfinder, crt.sh and Google dorks to find every hidden subdomain…
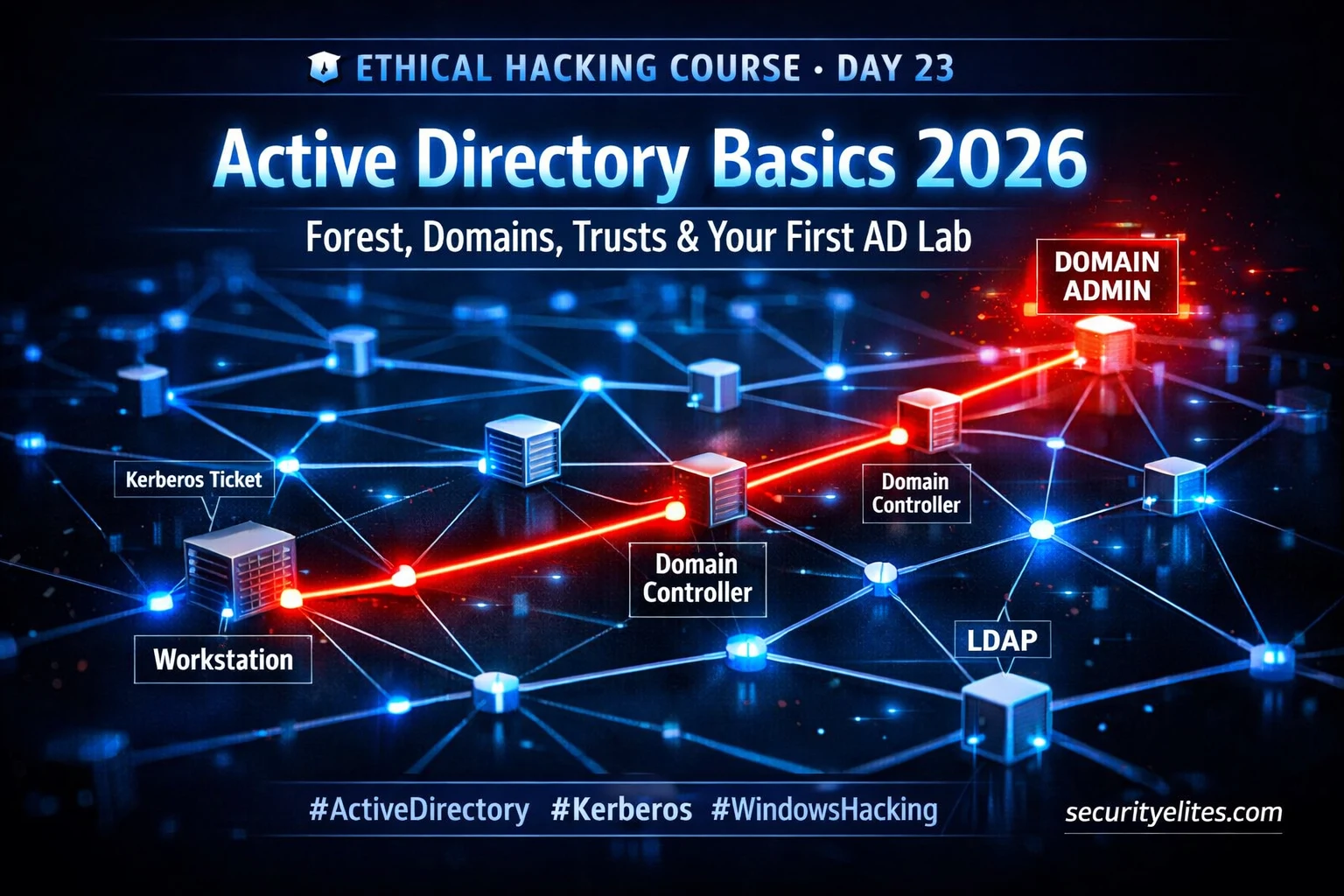
Day 23 : Active Directory Basics 2026 — Forest, Domains, Trusts & First AD Lab
Master active directory basics for ethical hacking 2026 — forests, domains, Kerberos, attack surface & free lab setup. Day 23…
Cloud Security Hacking 2026 — How Attackers Exploit AWS, Azure & GCP (Ethical Hacker’s Guide)
Cloud security hacking is the highest-demand offensive skill of 2026. Learn IAM misconfiguration exploitation, S3 bucket attacks, SSRF to cloud…
Network Scanning Tutorial Using Nmap Day 4 — Service & Version Enumeration
Network Scanning Tutorial Using Nmap Day 4 - Learn service and version enumeration using Nmap like professional penetration testers. Day…
Enumeration in Ethical Hacking – Full Practical Guide
Learn Enumeration in Ethical Hacking with this in-depth practical guide. Step-by-step techniques, real-world examples, tools, beginner mistakes, and pro tips…