Bug Bounty Reconnaissance
Learn reconnaissance strategies specifically for bug bounty hunting, including asset discovery, automation tools, and target mapping techniques used by professional hunters.
19 articles
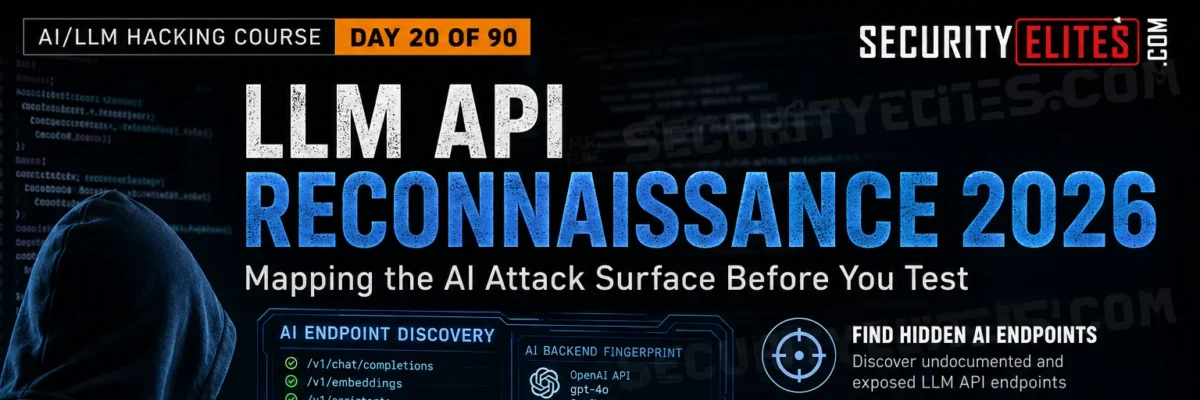
LLM-Powered OSINT 2026 — Using AI to Automate Open Source Intelligence Gathering
LLM-Powered OSINT 2026 — How security researchers use LLMs to automate OSINT in 2026. AI for email harvesting, subdomain synthesis,…
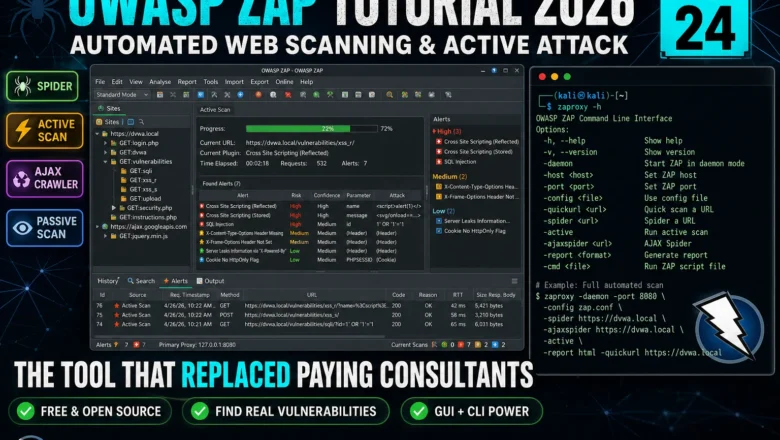
OWASP ZAP Tutorial 2026 — Automated Web Scanning, Spider & Active Attack | Kali Linux Tools Day24
Master OWASP ZAP in Kali Linux 2026. Spider, passive scan, active attack, AJAX crawl, and integrating ZAP into a professional…
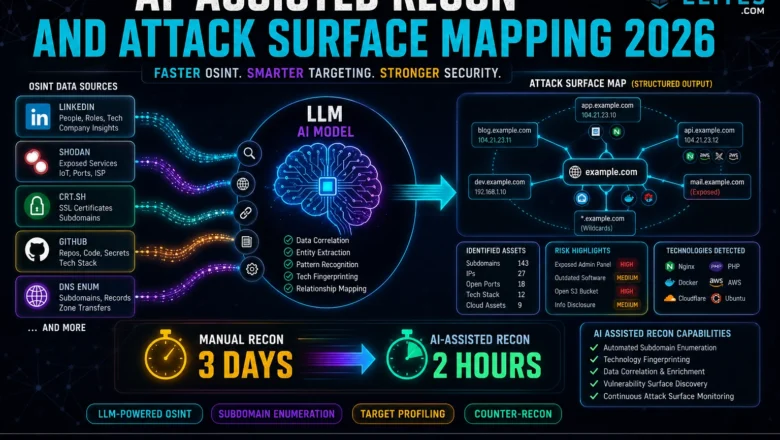
AI-Assisted Recon and Attack Surface Mapping 2026 — How hackers use LLMs to map attack surfaces faster
AI-Assisted Recon & Attack Surface Mapping - How hackers use LLMs to map attack surfaces faster in 2026. AI-assisted OSINT,…
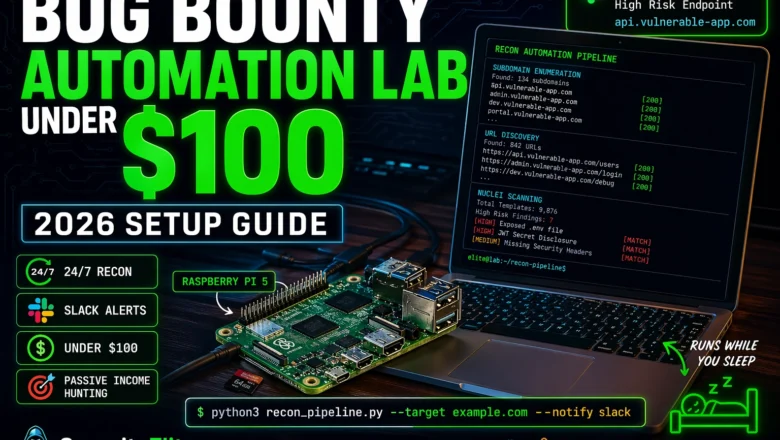
How to Build a Bug Bounty Automation Lab at Home for Under $100 (2026)
Build a complete bug bounty automation lab at home for under $100 in 2026 — hardware, tools, recon pipeline, subdomain…
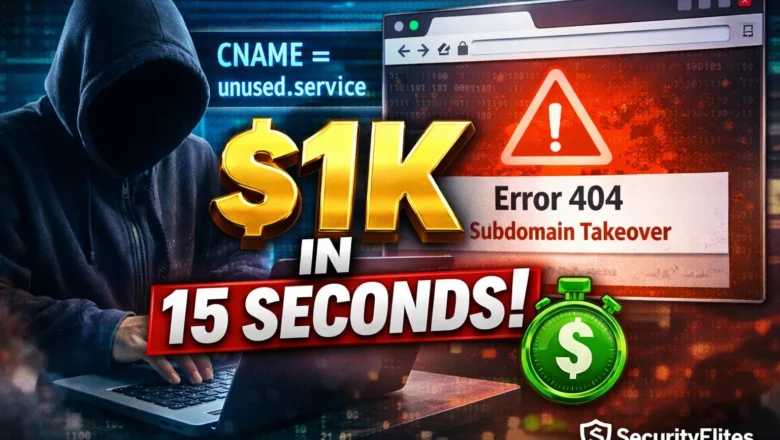
How Hackers Find Subdomain Takeovers — The 15-Second Check That Pays $1,000
Subdomain takeover guide 2026. The 3-command DNS check that finds dangling CNAME records, which cloud services allow takeover, how to…
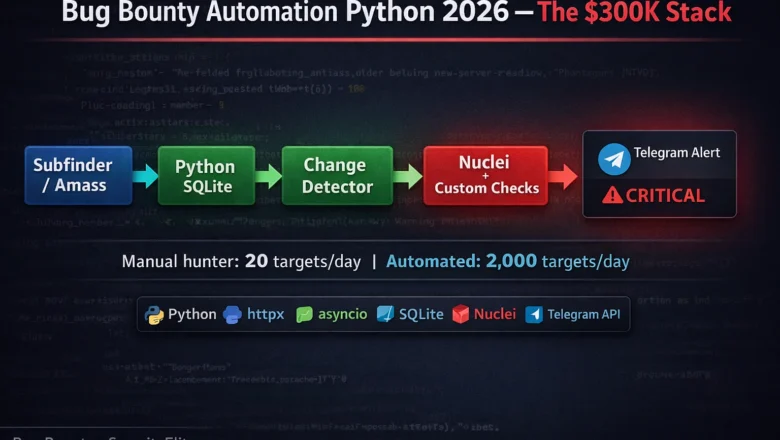
Bug Bounty Automation Python 2026 — The Exact Stack Top Hunters Use to Earn $300K/Year
Bug bounty automation Python 2026 — continuous recon, change detection, Nuclei integration, Telegram alerts. The exact 4-layer pipeline top hunters…
How to Use Shodan 2026 — The Hacker’s Search Engine Complete Guide
How to use shodan 2026 — search internet-connected devices, find exposed services, use Shodan dorks for bug bounty recon and…
Passive vs Active Reconnaissance — 90% of Beginners Do This Wrong (2026 Hacker Guide)
Master Passive vs Active Reconnaissance for ethical hacking and bug bounty. Learn passive recon (OSINT, WHOIS, certificate transparency) vs active…
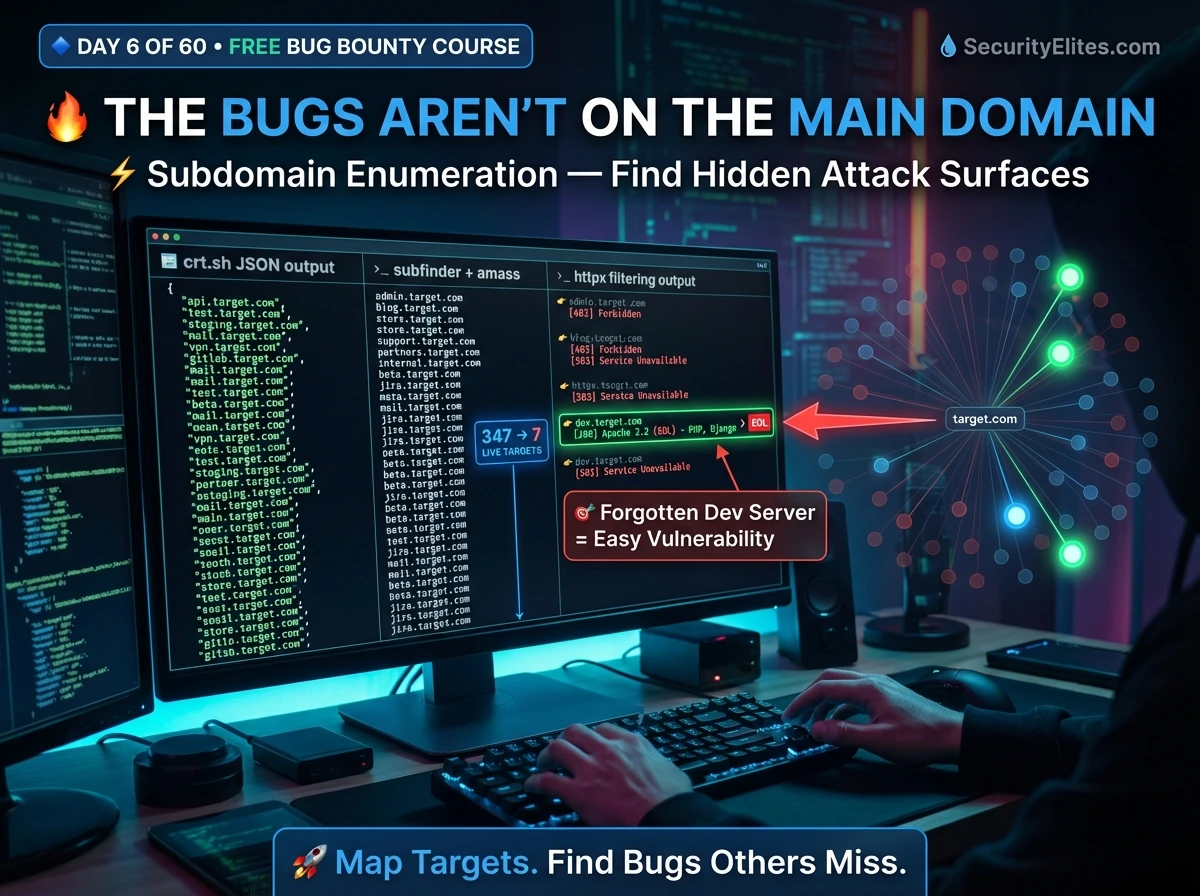
Bug Bounty Day 6: Subdomain Enumeration — Build Your Full Attack Surface Map (2026)
Master subdomain enumeration for bug bounty — Subfinder, Amass, crt.sh, httpx live filtering, ffuf directory fuzzing, and building a professional…