Authentication Bypass
Explore broken authentication mechanisms, login bypass techniques, session flaws, and credential attacks. Learn how ethical hackers test identity systems and how developers can secure them.
22 articles
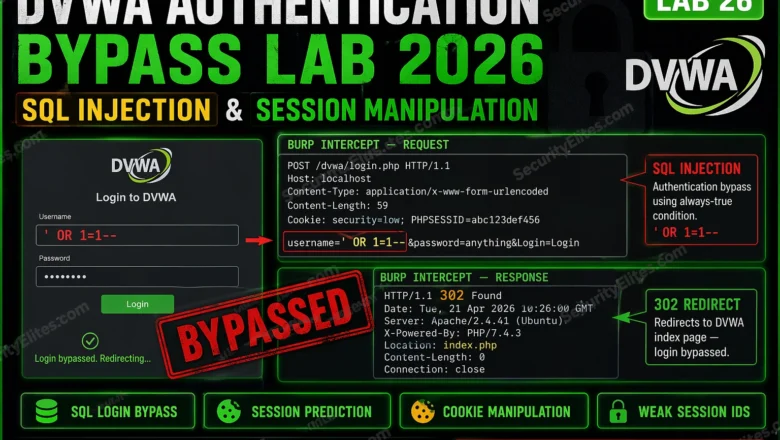
DVWA Authentication Bypass Lab 2026 — SQL Injection Login & Session Manipulation | Hacking Lab26
DVWA authentication bypass lab 2026 — bypass DVWA login with SQL injection, manipulate session cookies, exploit weak session IDs, and…
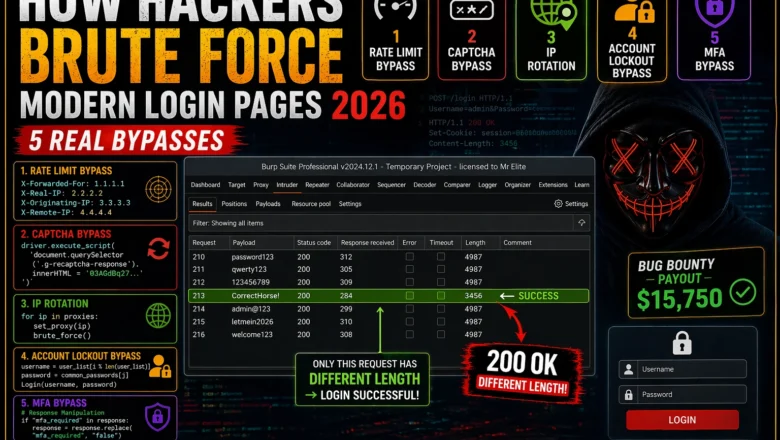
How Hackers Brute Force Modern Login Pages — 5 Real Bypasses (2026)
How hackers brute force modern login pages in 2026 — bypass rate limiting, CAPTCHA, account lockout, MFA, and IP rotation…
BB Day19: CSRF Bug Bounty 2026 — Find Cross-Site Request Forgery That Pays and Chain It to Account Takeover
CSRF bug bounty 2026 — find cross-site request forgery vulnerabilities, bypass SameSite cookies, chain CSRF to account takeover, and write…
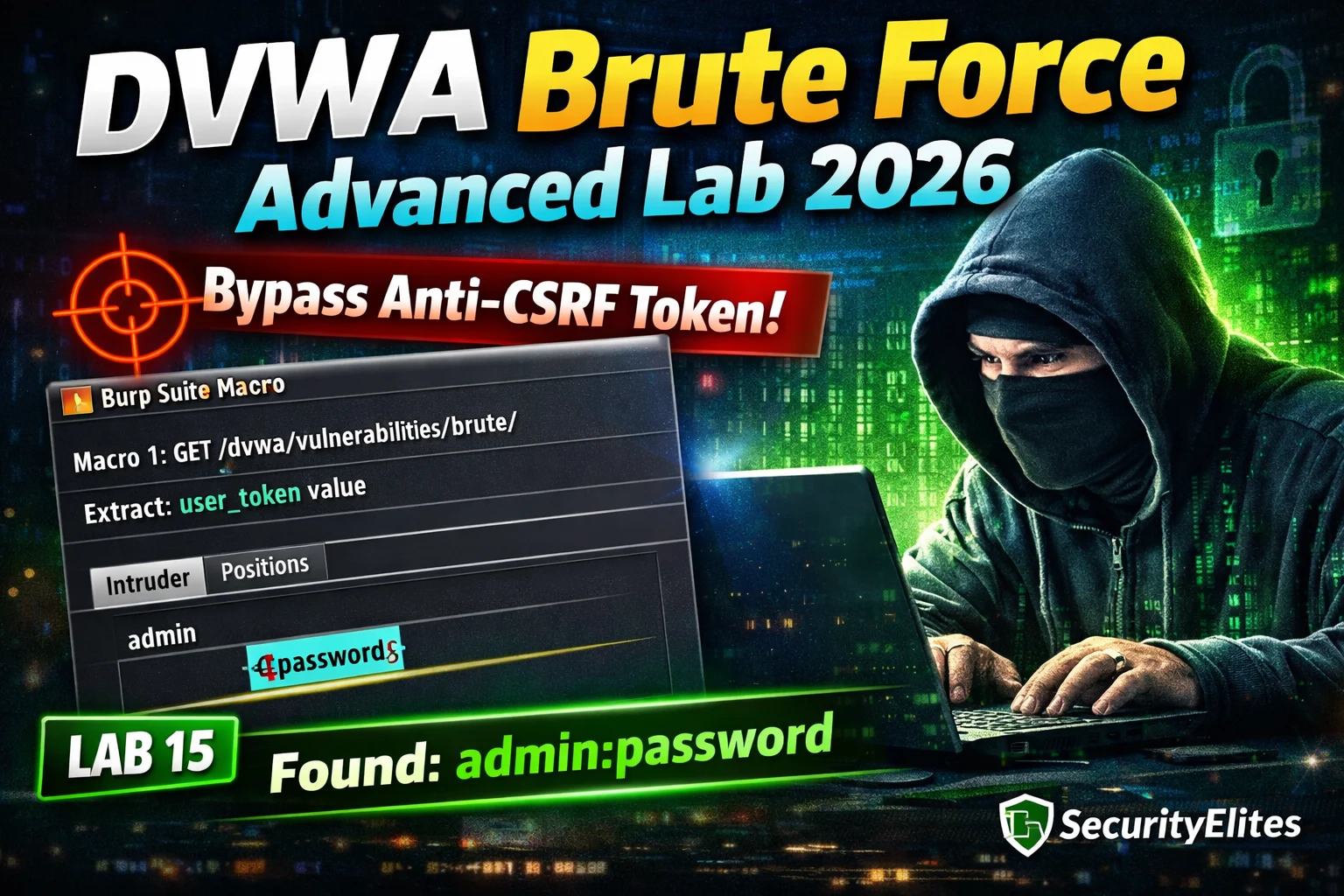
DVWA Brute Force Advanced Lab 2026 — Anti-CSRF Token Bypass Complete Walkthrough | Hacking Lab15
DVWA brute force advanced lab 2026 — bypass anti-CSRF token protection at High security using Burp Suite macros to extract…
BB Day18: OAuth 2.0 Bug Bounty 2026 — CSRF in OAuth, Token Leakage & Account Takeover Chains
OAuth bug bounty 2026 — find CSRF in OAuth flows, token leakage via referrer, account takeover chains and open redirect…
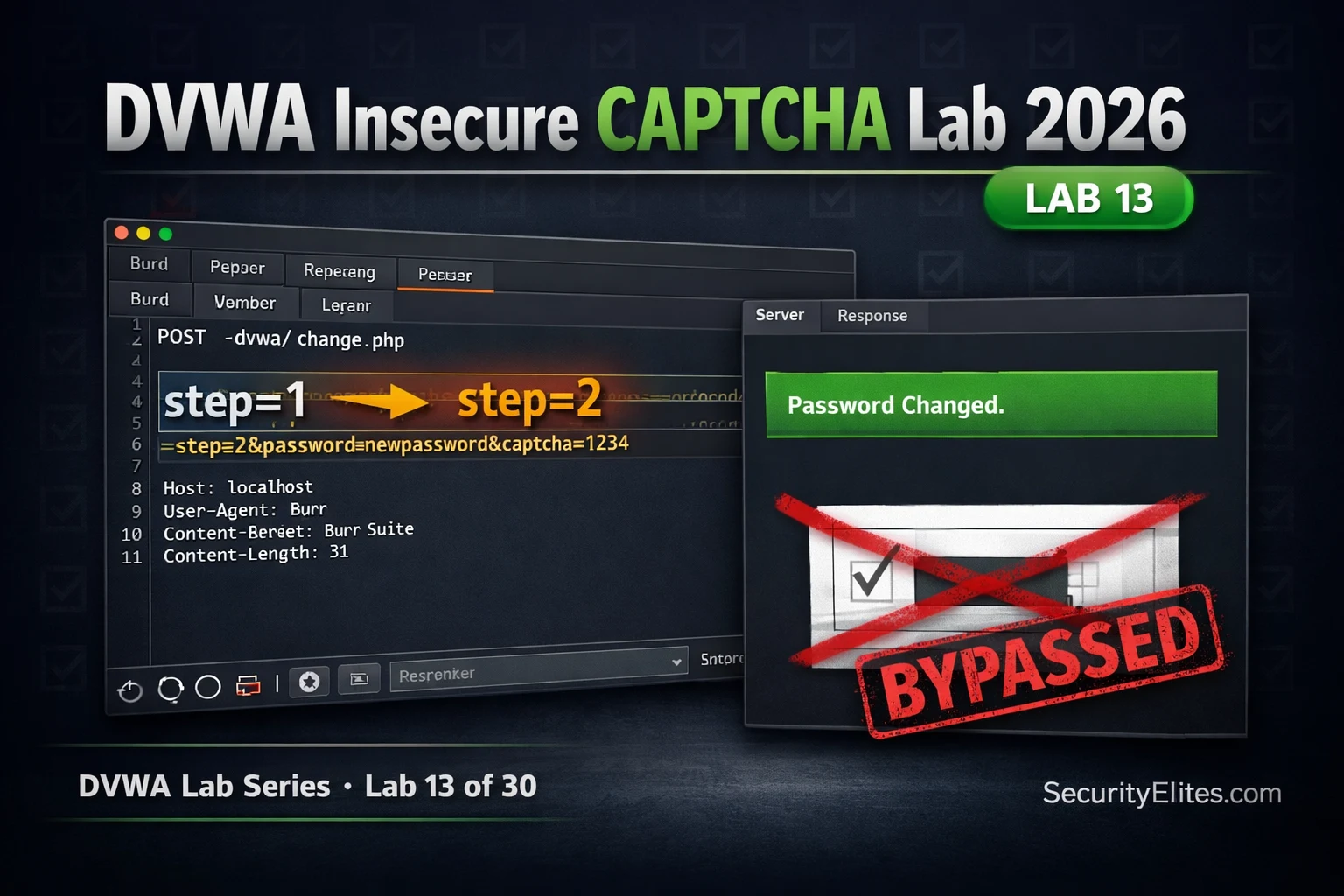
Lab13: DVWA Insecure CAPTCHA Lab 2026 — Bypass Logic & Complete Walkthrough
DVWA insecure captcha lab 2026 — bypass CAPTCHA logic flaws at all security levels using Burp Suite. Complete walkthrough with…
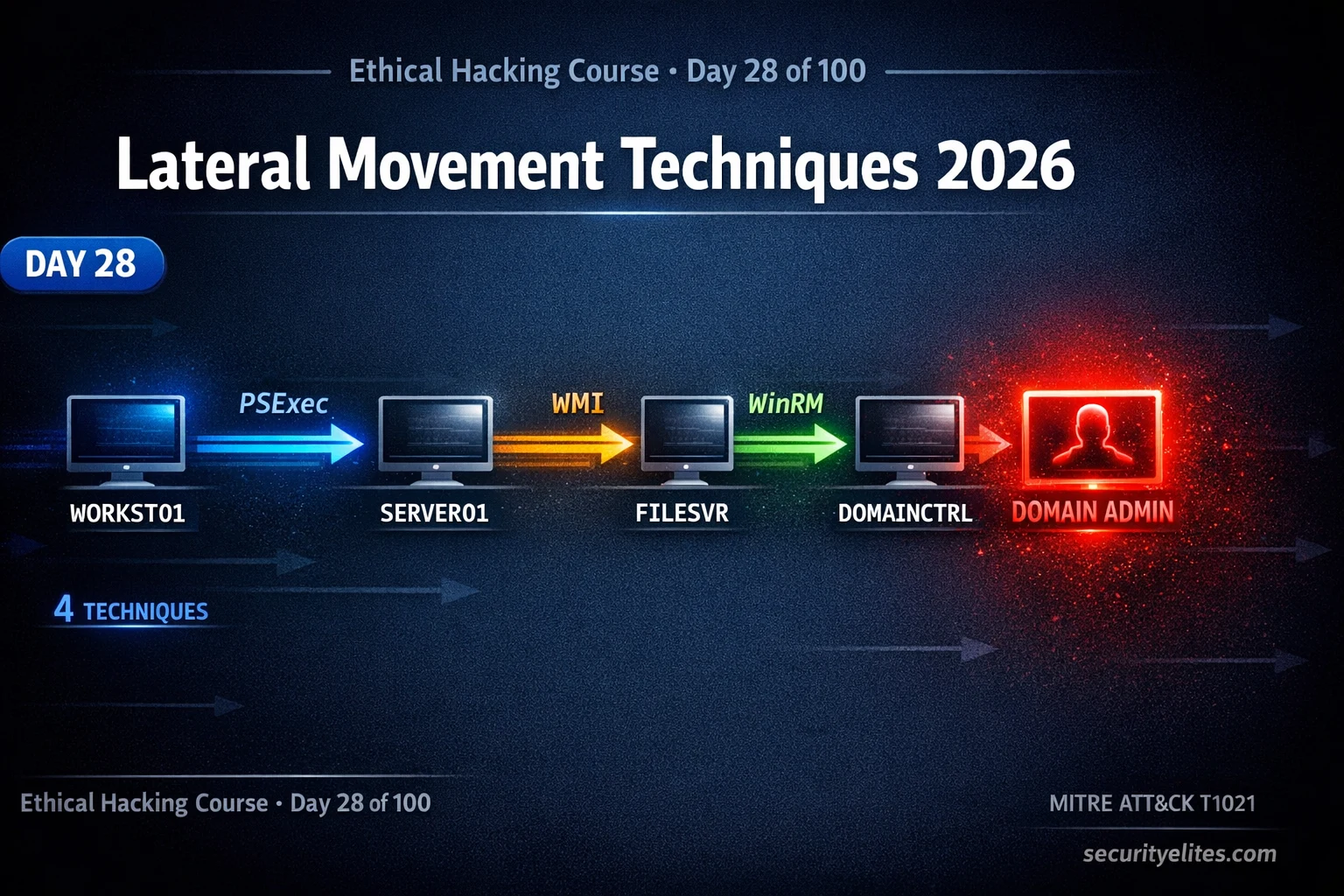
Lateral Movement Techniques 2026 — Execute Every BloodHound Attack Path in AD | Hacking Course Day 28
Lateral movement techniques 2026 — execute BloodHound attack paths using PSExec, WMI, WinRM and DCOM to move through Active Directory…
How Hackers Bypass 2FA in 2026 — 7 Methods That Still Work (Ethical Analysis)
How hackers bypass 2fa 2026 — 7 real methods used to circumvent two-factor authentication including SIM swapping, SS7 attacks, AiTM…
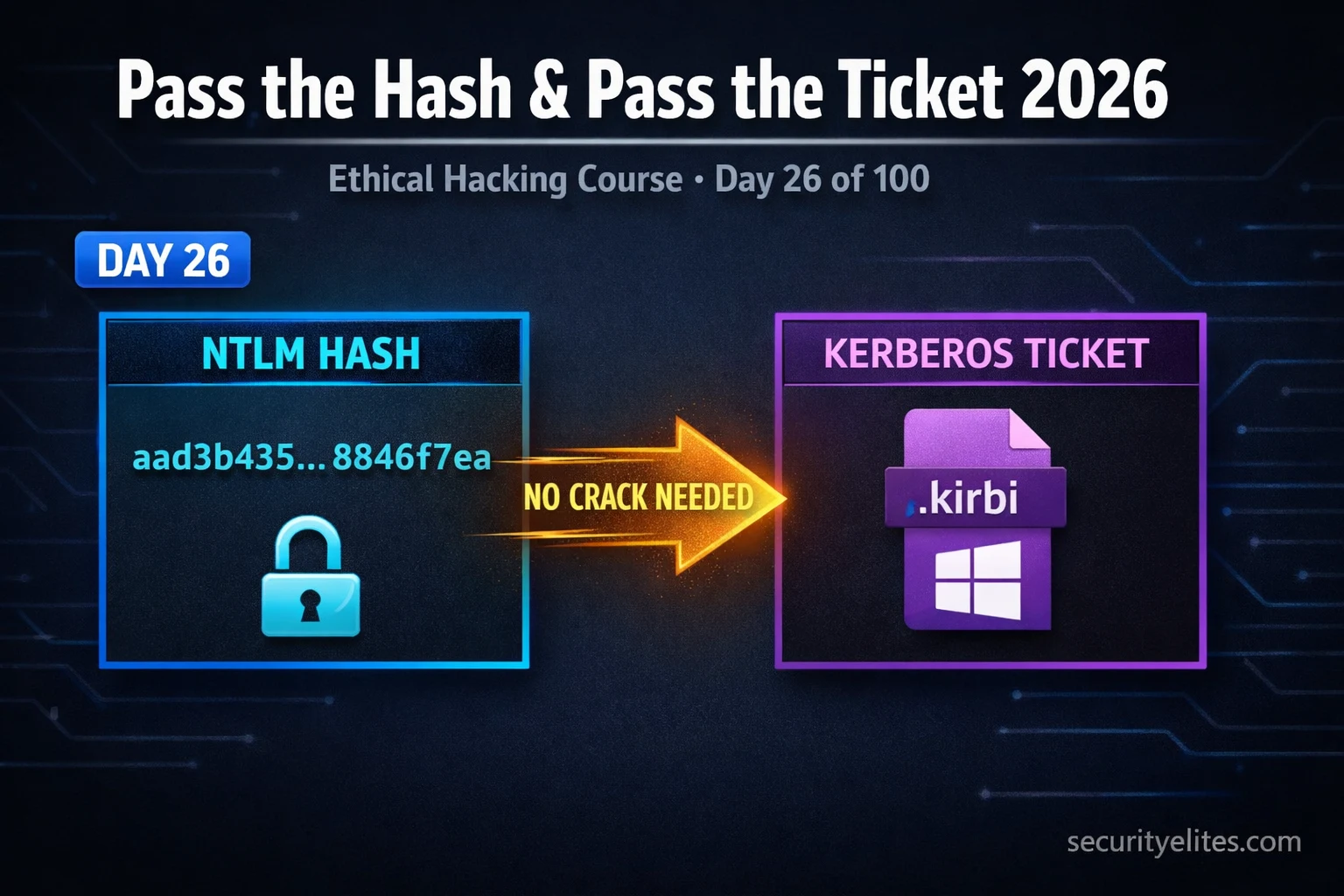
Day 26: Pass the Hash & Pass the Ticket 2026 — Lateral Movement With NTLM & Kerberos
Pass the hash & pass the ticket 2026 — exploit NTLM hashes and Kerberos tickets for lateral movement in Active…