Cyber Security Tools
Discover the most powerful cyber security tools and ethical hacking tools used by penetration testers and security researchers. This category features detailed tutorials, installation guides, and usage walkthroughs for reconnaissance, exploitation, OSINT, wireless testing, and password cracking tools. Explore both free and premium security tools, compare their features, and learn how to use them effectively in real penetration testing scenarios.
81 articles
15 AI Hacking Tools Every Security Researcher Uses in 2026
The 15 AI hacking tools I use on every security engagement in 2026. Garak, PyRIT, LangChain, Burp Suite and 11…
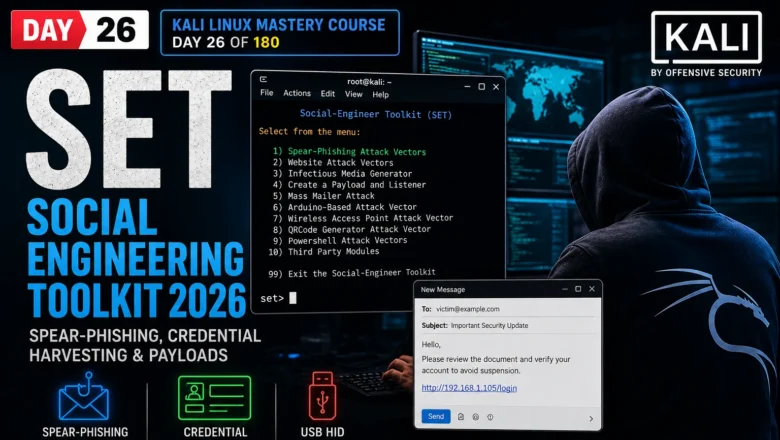
SET Social Engineering Toolkit — Spear-Phishing, Credential Harvesting & Payloads | Kali Linux Day 26
Master SET Social Engineering Toolkit in Kali Linux 2026. Spear-phishing emails, credential harvester, USB HID attacks and payload delivery. Day…
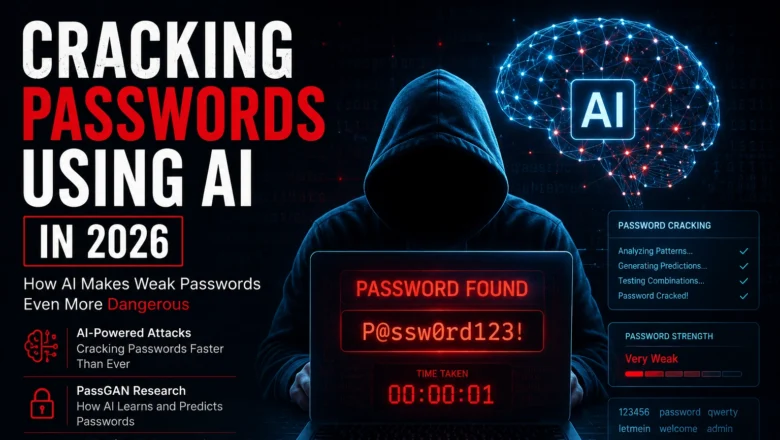
Cracking Passwords using AI – How AI Makes Weak Passwords Even More Dangerous
Cracking Passwords using AI in 2026. How AI-powered tools crack passwords faster, PassGAN research, what makes a password AI-resistant, and…
Is My Password Leaked? Check for Free 2026 — Complete Breach Check Guide
Is my password leaked? Check for free in 2026. Use breach databases to find leaked passwords, understand what hackers do…
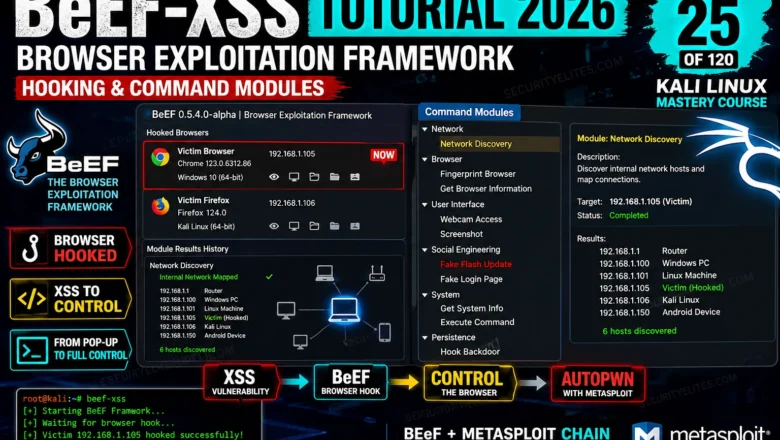
BeEF-XSS Tutorial 2026 — Browser Exploitation Framework, Hooking & Command Modules | Tools Day 25
BeEF-XSS Tutorial Kali Linux 2026. Hook browsers, run command modules, steal cookies, capture keystrokes, and understand browser exploitation in a…
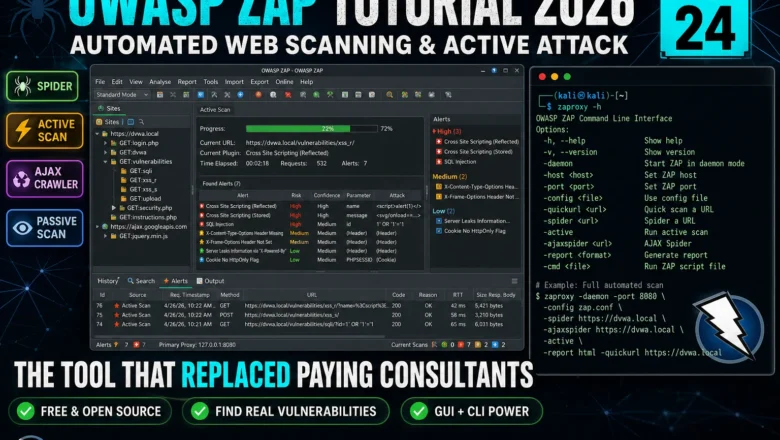
OWASP ZAP Tutorial 2026 — Automated Web Scanning, Spider & Active Attack | Kali Linux Tools Day24
Master OWASP ZAP in Kali Linux 2026. Spider, passive scan, active attack, AJAX crawl, and integrating ZAP into a professional…
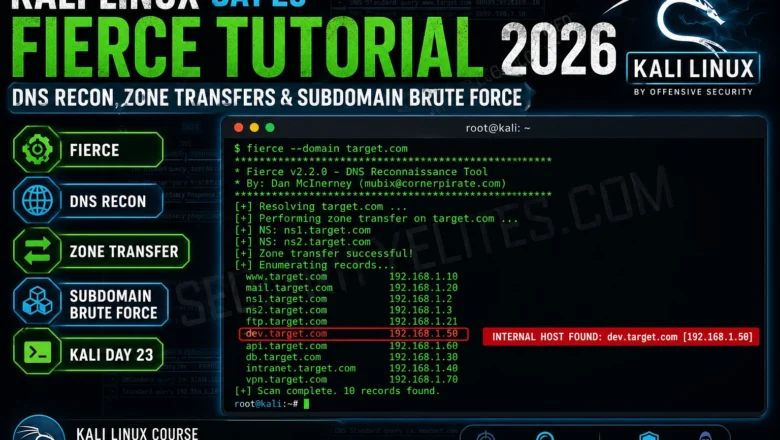
Kali Linux Day 23 — Fierce DNS Reconnaissance Tutorial 2026
Kali Linux Day 23: Fierce DNS reconnaissance tutorial — how to use Fierce for subdomain enumeration, DNS zone walking, and…
Shodan Tutorial Kali Linux 2026 — Search Engine for Hackers, Dork Queries & API Usage | Hacking Tools Day22
Shodan Tutorial in Kali Linux for 2026. Search exposed devices, run dork queries, use the API and build a recon…
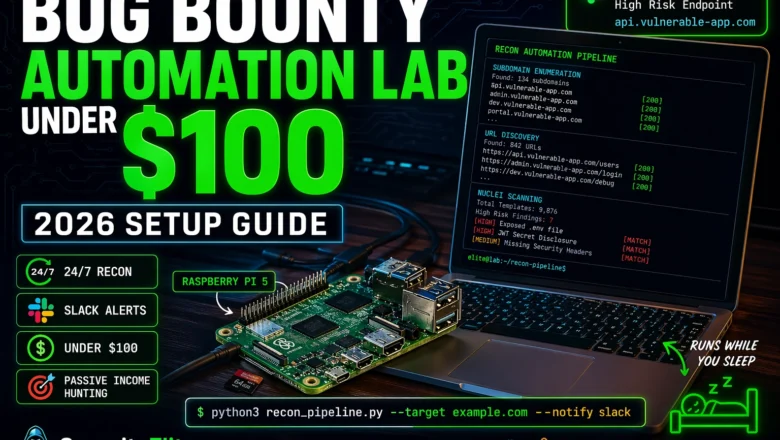
How to Build a Bug Bounty Automation Lab at Home for Under $100 (2026)
Build a complete bug bounty automation lab at home for under $100 in 2026 — hardware, tools, recon pipeline, subdomain…