UPDATED MARCH 2026
PART OF OUR 60-DAY COURSE
💰
Instagram has over 2 billion monthly active users. Its parent company Meta runs one of the most generous and well-respected bug bounty programmes in the world — having paid out over $16 million in bounties to security researchers since 2011. Every legitimate security vulnerability found in Instagram and reported through the official programme is reviewed, acknowledged, and rewarded. No grey areas. No legal risk. Just research, report, and get paid.
This guide explains exactly how Meta’s Instagram bug bounty programme works — what is in scope, what types of vulnerabilities are found and rewarded, how to set up a legal testing environment, and how real researchers have earned thousands of dollars finding security issues that Meta wanted found. This is ethical hacking in its most professional form.
Meta’s Bug Bounty Programme launched in 2011 — one of the earliest large-scale bug bounty programmes in the tech industry. It covers all Meta products including Facebook, Instagram, WhatsApp, Messenger, Oculus, and more. The Instagram bug bounty programme specifically invites security researchers worldwide to test Instagram’s web application, mobile apps, and APIs for security vulnerabilities.
What makes Meta’s programme stand out is its scale, its transparency, and its minimum bounty policy. Meta has guaranteed minimum bounty amounts per vulnerability severity, publishes detailed statistics about their programme, and has a dedicated security engineering team that triages reports quickly and professionally.
securityelites.comMETA BUG BOUNTY PROGRAMME — KEY FACTS
$16M+
Total paid to researchers since 2011
$500
Minimum payout for valid reports
2011
One of the first big tech programmes
Global
Open to researchers worldwide
PROGRAMME HIGHLIGHTS
✓ No minimum experience requirement
✓ Guaranteed $500 minimum for valid reports
✓ Safe harbour — legal protection for researchers
✓ Meta engineers provide feedback on reports
✓ Hall of fame recognition for top researchers
✓ No geographic restrictions on participation
Meta Bug Bounty Programme Overview — $16M+ paid out since 2011, $500 minimum guaranteed payout, open globally. The programme covers all Meta products including Instagram, Facebook, WhatsApp, and Messenger.
Instagram Bug Bounty Payout Ranges — What Different Vulnerability Types Actually Pay
Meta’s bug bounty payouts are based on the severity and impact of the vulnerability. They follow a tiered structure, though exact amounts vary depending on the specific finding, its novelty, and the quality of the report. Here is the realistic payout landscape for Instagram-specific findings:
Account takeover, remote code execution, significant auth bypass
Examples: Ability to take over any Instagram account without user interaction, bypass of Instagram’s login mechanism, RCE on Instagram’s servers, access to private content across all users. These are rare but happen — and pay very well.
Significant access control flaws, high-impact IDOR, sensitive data exposure
Examples: Ability to view or modify another user’s private content or settings, access to private messages without authorisation, reading private Instagram posts. These require more skill but appear in the mid-range of experience.
Limited IDOR, stored XSS, CSRF on significant actions, auth weaknesses
Examples: Stored XSS that affects other users’ Instagram experience, CSRF on account settings changes, limited access to another user’s data. These are the most commonly found medium-skill findings in the Instagram programme.
Information disclosure, missing security headers, non-critical CSRF
Examples: Server version disclosure, sensitive information exposed in API responses, missing HTTPS enforcement on non-critical pages. The $500 minimum applies here. These are beginner-accessible and build the reputation needed for private invites.
What Is In Scope — Instagram Assets You Can Legally Test
The Instagram bug bounty programme scope defines exactly what you can test. Staying within scope is not optional — it is the legal and ethical boundary of the programme. Always read Meta’s current scope documentation before testing, as it is updated periodically.
securityelites.comfacebook.com/whitehat — Programme Scope (Representative)
Meta Bug Bounty — Instagram Scope
✓ instagram.com (web)
✓ Instagram iOS app
✓ Instagram Android app
✓ Instagram Graph API
✓ Instagram Basic Display API
✓ instagram.com/developer
Testing must use your own test accounts only.
OUT OF SCOPE — DO NOT TEST
✗ Third-party Instagram tools
✗ Social engineering Meta employees
✗ DoS / DDoS attacks
✗ Physical security testing
✗ Testing on real user accounts
✗ Exfiltrating real user data
✗ Automated scanning at scale
Safe Harbour: Meta will not pursue legal action against researchers who act in good faith within the defined scope and follow programme rules. Always read the current scope at facebook.com/whitehat before testing.
Instagram Bug Bounty Scope (Representative) — The scope document defines what you can and cannot test. Never test against real user accounts or data. Always read the current official scope at facebook.com/whitehat — it is updated periodically.
Vulnerability Types That Meta Rewards — What Researchers Actually Find in Instagram
Understanding what types of vulnerabilities have been found and rewarded in the Instagram programme helps you focus your testing time on the most productive areas. Here are the vulnerability classes that appear repeatedly in Meta’s disclosed reports and researcher writeups:
IDORInsecure Direct Object Reference — The Most Common Instagram Finding
Instagram handles billions of resources — posts, stories, reels, user data, messages — all accessed via IDs. When an API endpoint does not verify that the requesting user owns or is authorised to access a resource, IDOR exists. Example: researcher discovered they could view any user’s archived stories (private content) by modifying the story ID in an API request. Paid $3,000–$8,000 typically.
AUTHAuthentication and Authorisation Flaws
Bypassing authentication steps, token reuse vulnerabilities, session management weaknesses. A researcher once found that Instagram’s password reset flow had a rate-limiting weakness that allowed brute-forcing 6-digit reset codes — a critical finding that paid $30,000. Another found that OAuth tokens could be extracted from the Instagram app via a specific URL scheme exploitation.
APIInstagram API Security Issues
Instagram’s private API (used by the mobile app) exposes many endpoints not available in the public API. Researchers who intercept and analyse this API traffic frequently find undocumented endpoints with insufficient authorisation checks, mass assignment vulnerabilities in user data updates, or information disclosure via overly verbose error responses.
XSSCross-Site Scripting in Instagram Web
While Instagram’s web frontend is heavily hardened against XSS, researchers still find stored XSS in less-tested areas such as business account features, Shops, advertising dashboards, and creator tools. These pay $1,000–$5,000 depending on impact. Reflected XSS in URL parameters has also been found historically.
Legal Testing Environment Setup — How to Research Instagram Safely and Ethically
Setting up a proper testing environment is not just a technicality — it is the boundary between legitimate security research and illegal unauthorised access. Everything in this section ensures your research is authorised, ethical, and safe for other users.
securityelites.comLEGAL INSTAGRAM RESEARCH ENVIRONMENT
TEST ACCOUNTS
✓ Create 2–3 dedicated Instagram test accounts
✓ Use email aliases (e.g. yourname+bb1@gmail.com)
✓ Note them in programme “My Accounts” on Bugcrowd
✗ Never test on real user accounts
✗ Never access real user data
TOOLS NEEDED
🔧 Burp Suite Community (free)
🔧 Firefox + FoxyProxy extension
🔧 Burp CA certificate installed
🔧 Android emulator OR physical device
🔧 Note-taking tool (Notion, Obsidian)
BEFORE YOU START
📋 Read the full Meta programme policy
📋 Verify current scope at facebook.com/whitehat
📋 Register on Bugcrowd and complete profile
📋 Document your test account usernames
📋 Set up a research notes folder structure
Non-negotiable: Create a test account and register it with the programme before any testing. If your testing accidentally triggers Meta’s fraud systems, the registered account note helps demonstrate good-faith research intent.
Legal Instagram Research Environment — Always create dedicated test accounts and register them with the programme. Never test on real user accounts. Document everything from the start — good documentation leads to good reports, which leads to bounties.
Notable Past Instagram Bug Bounty Reports — Real Examples That Paid
The best way to understand what valid findings look like is to study real reports. Meta discloses summaries of notable reports through security blog posts and researcher writeups. Here are some publicly documented examples that illustrate the types of findings the Instagram bug bounty programme rewards:
CASE STUDY #1
$30,000
Password Reset Code Brute Force
Researcher Laxman Muthiyah discovered that Instagram’s 6-digit password reset code (sent via SMS) had a rate-limiting weakness that, when exploited via distributed IPs, allowed attempting all possible codes. This was a critical account takeover vulnerability affecting any Instagram account. Meta fixed it and paid a $30,000 bounty.
Vulnerability type: Authentication bypass | Severity: Critical
CASE STUDY #2
$6,000
Private Post Access via IDOR
A researcher found that modifying a media ID parameter in a specific Instagram API endpoint allowed viewing private posts from any user without following them. The API did not verify whether the requesting user had permission to view the content. Full private feed content was accessible — a clear High severity IDOR finding.
Vulnerability type: IDOR / Access Control | Severity: High
CASE STUDY #3
$2,500
OAuth Token Exposure in URL
A researcher discovered that Instagram’s OAuth flow was including access tokens in URL parameters in a redirect flow, where they could be logged by browser history, referrer headers, or server access logs. While the immediate impact was limited, the potential for token theft made this a valid medium-severity finding worth $2,500.
Vulnerability type: Token exposure | Severity: Medium
How to Write and Submit an Instagram Bug Bounty Report
A great finding with a poor report gets triaged slowly, may be marked as insufficient evidence, and risks a lower bounty. A clear, well-structured report with strong proof of concept gets fast triage, acknowledgement, and the maximum bounty for the severity. Report quality matters.
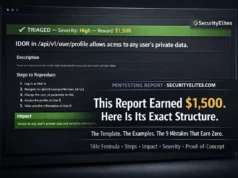
securityelites.comfacebook.com/whitehat/report — New Report
Bug Bounty Report Template — Meta / Instagram
TITLE (be specific)
IDOR in /api/v1/media/{media_id}/info/ allows viewing private posts of any user
DESCRIPTION
The endpoint /api/v1/media/{media_id}/info/ does not verify whether the authenticated user has permission to view the requested media object. By substituting the media_id of a private post belonging to a different user, an attacker can retrieve the full post metadata and media URLs regardless of the account’s privacy setting.
STEPS TO REPRODUCE
1. Log in as test account A (public account)
2. Note the media_id of a post from test account B (private account, not followed by A)
3. Send GET /api/v1/media/{private_media_id}/info/ with Account A’s authentication token
4. Observe: full post details returned — access granted incorrectly
IMPACT
Any authenticated Instagram user can view the private posts of any other Instagram account, bypassing Instagram’s privacy controls. This affects all private accounts on the platform. An attacker could harvest private content from target accounts systematically.
Bug Report Template for Meta/Instagram — The four essential sections: Title (specific), Description (technical detail), Steps to Reproduce (exact, reproducible), Impact (who is affected and how severely). Quality reports get triaged faster and paid more.
The Beginner’s Path to First Instagram Bug Bounty Submission
Most beginners make the mistake of jumping straight to Meta’s programme without the foundational knowledge to recognise vulnerabilities even when they are staring at them. Here is the realistic path that builds the skills needed before touching Instagram’s scope:
1
Learn the fundamentals first (Days 1–30 of our free course)
2
Practise on intentionally vulnerable apps
PortSwigger Web Security Academy (free), DVWA, HackTheBox Starting Point. Build the muscle memory of finding IDOR, XSS, and auth flaws in a safe practice environment before testing real applications.
3
Find your first bounty on a smaller programme first
Meta’s programme is competitive — thousands of researchers test Instagram daily. Earn your first bounty on a less competed beginner-friendly HackerOne or Bugcrowd programme first. This builds confidence, methodology, and proof of the model working before tackling a top-tier target.
4
Focus on Instagram’s mobile API — the most fertile ground
Set up an Android emulator, install Instagram, route traffic through Burp Suite. The Instagram private API handles far more functionality than the web interface and often has endpoints that received less security review. Many high-value findings come from API research.
Frequently Asked Questions — Instagram Bug Bounty
How much does Meta pay for Instagram bug bounty reports?
Meta pays $500 minimum for any valid finding, up to $50,000+ for critical vulnerabilities. Critical findings like account takeover or RCE pay $15,000–$50,000+. High severity findings pay $5,000–$15,000. Medium severity pays $1,000–$5,000. Low severity starts at the $500 minimum. Exceptional findings on novel attack vectors have received six-figure payouts.
Is testing Instagram for vulnerabilities legal?
Yes, within the official Meta Bug Bounty programme scope. The programme provides explicit written authorisation. Researchers must use their own test accounts, must not access real user data, and must stay within the defined scope. The Safe Harbour provision protects researchers acting in good faith within the programme rules.
Do I need to be an expert to find Instagram bugs?
No, but you need foundational knowledge of web security and HTTP. Many Instagram findings come from accessible vulnerability classes — IDOR, access control issues, and information disclosure. The key qualities are methodical testing, good documentation, and understanding what impact means. Our free 60-day bug bounty course builds exactly these skills.
Where do I submit Instagram bug bounty reports?
Reports are submitted through Meta’s official bug bounty portal at facebook.com/whitehat/report. The programme also has a presence on Bugcrowd. Include a clear title, description, exact steps to reproduce, and impact assessment. Meta’s security team triages reports and provides feedback on validity.
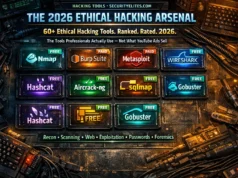
What tools do Instagram bug bounty hunters use?
The standard toolkit: Burp Suite Community Edition (free) for intercepting and analysing Instagram’s API traffic, a dedicated test Instagram account, Firefox with FoxyProxy, an Android emulator for mobile API research, and note-taking tools. The Instagram mobile API is particularly valuable because it exposes more functionality than the web interface.
ME
Mr Elite
Founder, SecurityElites.com | Bug Bounty Hunter | Educator
Meta’s bug bounty programme is one of the best entry points for new researchers because of its guaranteed minimum payout, professional triage team, and sheer breadth of functionality to test. Instagram’s scale means there are always newly launched features — and new features mean code that has received less security review than legacy features. The opportunity is real, the payment is real, and it is entirely legal when done correctly through the official programme.