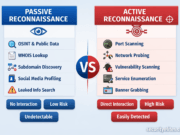
Passive vs Active Reconnaissance – Real Hacker Methods Explained
Master Passive vs Active Reconnaissance in ethical hacking. Learn real hacker methods, tools, workflows, detection risks, and pro field tips.
Kali Linux Installation Guide (2026) – Step-by-Step
Learn how to install Kali Linux in 2026 with this step-by-step expert guide. Covers VM setup, dual boot basics, tools, mistakes, and pro security tips.
Enumeration in Ethical Hacking – Full Practical Guide
Learn Enumeration in Ethical Hacking with this in-depth practical guide. Step-by-step techniques, real-world examples, tools, beginner mistakes, and pro tips from 20+ years of cybersecurity experience.
Footprinting and Reconnaissance Tutorial (2026) – Complete Step-by-Step Guide
Learn footprinting and reconnaissance in ethical hacking with this 2026 step-by-step guide. Covers OSINT, DNS recon, subdomain enumeration, tools, pro tips, and real-world examples.
Beginner’s Guide for Cyber Security and Ethical Hacking (Step-by-Step 2026)
A complete beginner’s guide to Cyber Security and Ethical Hacking written by a 20-year industry expert. Learn tools, roadmap, mistakes, pro tips, and real-world insights.