The first time most beginners hear SQL Injection, they imagine movie-style hacking — passwords flying across screens and databases collapsing instantly. Lets go through SQL Injection Tutorial Step-by-Step.
Reality?
It’s quieter… slower… and far more dangerous.
During real penetration tests, I’ve seen million-record databases exposed not because of advanced hacking, but because one developer forgot to validate a login field.
Yes — just a login box.
Now here’s something most beginners don’t realize:
👉 SQL Injection is still among the Top Web Application vulnerabilities in 2026, even after decades of awareness.
Why? Because theory is easy. Secure implementation is hard.
Today, I’ll walk you through SQL Injection the same way I teach junior pentesters during live red-team training — step by step, practical, ethical, and grounded in real-world assessments.
🧠 What Is SQL Injection (Let Me Simplify First)
Think of a website database like a locked office cabinet.
Normally, users request data politely:
Show my account details
But SQL Injection happens when an attacker secretly changes the request into:
Show ALL account details
The application trusts user input — and unknowingly executes malicious database commands.
That’s SQL Injection.
Technically speaking:
SQL Injection occurs when user input becomes part of a database query without proper validation or sanitization.
And this is where theory and real-world hacking differ.
Most vulnerabilities exist not in complex systems — but in simple forms developers overlook.
⚙️ Why SQL Injection Still Exists in 2026
During enterprise penetration testing, we repeatedly encounter SQL Injection because:
- Legacy applications still run outdated code
- Developers trust frontend validation
- Input filtering is incomplete
- ORM protections are misunderstood
- Security testing happens too late
Professionals don’t start exploitation immediately.
They follow a workflow mindset.
Let’s learn that.
🔎 Step 1 — Understanding How Databases Work
Most web apps use databases like:
- MySQL
- PostgreSQL
- MSSQL
- Oracle
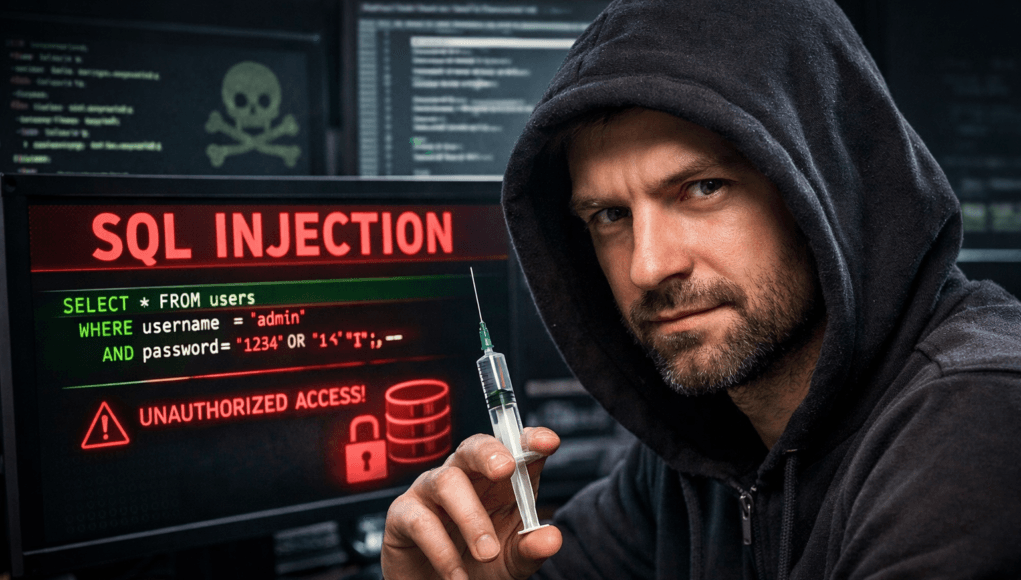
A login query usually looks like:
SELECT * FROM users
WHERE username='admin' AND password='pass123';
Now imagine user input becomes:
' OR 1=1 --
Final query becomes:
SELECT * FROM users
WHERE username='' OR 1=1 --';
1=1 is always TRUE.
Authentication bypass achieved.
Simple. Silent. Dangerous.
🚨 Beginner Mistake Alert
Many learners memorize payloads without understanding queries.
That approach fails in real penetration tests.
💡 Pro Tip from Field Experience
Always visualize how backend queries change after injection.
✅ Quick Practical Takeaway
SQL Injection = manipulating backend SQL logic through input fields.
🧪 Step 2 — Setting Up Legal Practice Environment
Never test random websites.
Professional ethical hackers practice using:
✅ DVWA (Damn Vulnerable Web App)
✅ OWASP Juice Shop
✅ WebGoat
✅ Local lab environments
Run inside Kali Linux penetration testing tools environment.
Example setup:
sudo service apache2 start
sudo service mysql start
Open:
http://localhost/dvwa
🔍 Step 3 — Detecting SQL Injection (Manual Method)
Before tools — professionals test manually.
Why?
Because automation without understanding is useless.
✅ Basic Test Payloads
Try inside login/search field:
'
If error appears:
SQL syntax error
Congratulations — potential injection point found.
Next Test
' OR '1'='1
If login bypass happens → Vulnerable.
Real Pentest Observation
During an internal company assessment, we discovered admin access simply because error messages were visible publicly.
Enumeration was skipped by developers.
One character (') exposed everything.
🚨 Beginner Mistake Alert
Running sqlmap immediately.
Manual confirmation always comes first.
🧬 Step 4 — Types of SQL Injection (Practically Explained)
1️⃣ Error-Based SQL Injection
Database errors reveal structure.
Example:
You have an error in SQL syntax...
Attackers extract table names directly.
2️⃣ Union-Based SQL Injection
Combines attacker query with original query.
Example:
UNION SELECT null, database();
Used heavily in bug bounty programs.
3️⃣ Blind SQL Injection
No errors shown.
Tester asks TRUE/FALSE questions.
Example:
AND 1=1
AND 1=2
Response difference reveals truth.
4️⃣ Time-Based SQL Injection
Server delay confirms vulnerability.
Example:
SLEEP(5)
If page delays → injection confirmed.
⚡ Step 5 — Using sqlmap (Professional Workflow)
If you’ve ever tried sqlmap, you probably noticed beginners misuse it badly.
sqlmap is powerful — but only after validation.
✅ Basic Command
sqlmap -u "http://testphp.vulnweb.com/listproducts.php?cat=1"
Database Enumeration
sqlmap -u URL --dbs
Output shows:
available databases:
users
admin
shop
Extract Tables
sqlmap -u URL -D users --tables
Dump Data
sqlmap -u URL -D users -T accounts --dump
Real-World Scenario
During a financial web assessment, automated scanning missed injection.
Manual testing confirmed blind SQLi.
sqlmap later extracted credential hashes — proving business risk instantly.
Automation supported understanding — not replaced it.
🚨 Beginner Mistake Alert
Using aggressive scan options on production systems.
You may crash servers.
💡 Pro Tip from Field Experience
Use:
--risk=1 --level=1
initially.
Stealth matters.
✅ Quick Practical Takeaway
sqlmap = exploitation assistant, not magic hacker tool.
🧭 Step 6 — Real Penetration Testing Workflow
Professional SQL Injection testing follows:
✅ Reconnaissance
Identify input points:
- Login forms
- Search bars
- Filters
- URL parameters
Tools:
- Burp Suite
- Browser DevTools
✅ Scanning
Detect anomalies and errors.
✅ Enumeration
Most critical phase.
Find:
- Database name
- Tables
- Columns
Enumeration wins engagements.
✅ Exploitation
Extract controlled data.
✅ Post Exploitation
Assess impact:
- Credential reuse
- Privilege escalation
- Data exposure
✅ Reporting
Most ignored skill.
Clients pay for risk explanation, not hacking screenshots.
🏢 SQL Injection in Professional Environments
SQL Injection testing appears in:
🔴 Red Team Operations
Simulating insider threats.
🟢 Bug Bounty Programs
High payout vulnerability.
🔵 Compliance Testing
PCI-DSS & ISO audits.
🟡 SOC Validation
Detection capability testing.
❌ Common Beginner Mistakes (Reality Check)
✔ Running tools blindly
✔ Copy-paste payload hacking
✔ Ignoring legal authorization
✔ Skipping enumeration
✔ No impact explanation
✔ Poor reporting skills
I’ve rejected pentest reports purely due to bad documentation.
🧠 Pro Tips From 20 Years Experience
✅ Tool mastery beats tool quantity
✅ Enumeration reveals 80% vulnerabilities
✅ Silent testing > noisy scanning
✅ Developers are partners, not enemies
✅ Automation ≠ expertise
And remember this:
The best hackers understand systems — not payload lists.
🛡 Defensive & Ethical Considerations
Ethical hacking exists to improve security, not exploit people.
Always follow:
- Written permission
- Responsible disclosure
- Data minimization
- Legal boundaries
Unauthorized testing = crime.
Professional testing = cybersecurity assessment.
Huge difference.
✅ Quick Recap Summary
- SQL Injection manipulates backend database queries
- Manual testing comes before automation
- sqlmap accelerates confirmed vulnerabilities
- Enumeration is critical
- Reporting proves business impact
- Ethical boundaries matter most
❓ FAQs
Which SQL Injection tutorial is best for beginners?
Hands-on lab practice using DVWA combined with manual testing and sqlmap workflow.
Is SQL Injection still relevant in 2026?
Yes. It remains a top web vulnerability worldwide.
Do professional pentesters use sqlmap?
Yes — but only after manual validation.
Can beginners learn ethical hacking using SQL Injection?
Absolutely. It teaches application logic understanding.
Is SQL Injection illegal?
Testing without permission is illegal. Authorized testing is ethical hacking.
What tools detect SQL Injection?
Burp Suite, sqlmap, OWASP ZAP, manual testing methods.
How long does it take to learn SQL Injection?
With daily lab practice — 2 to 4 weeks for fundamentals.