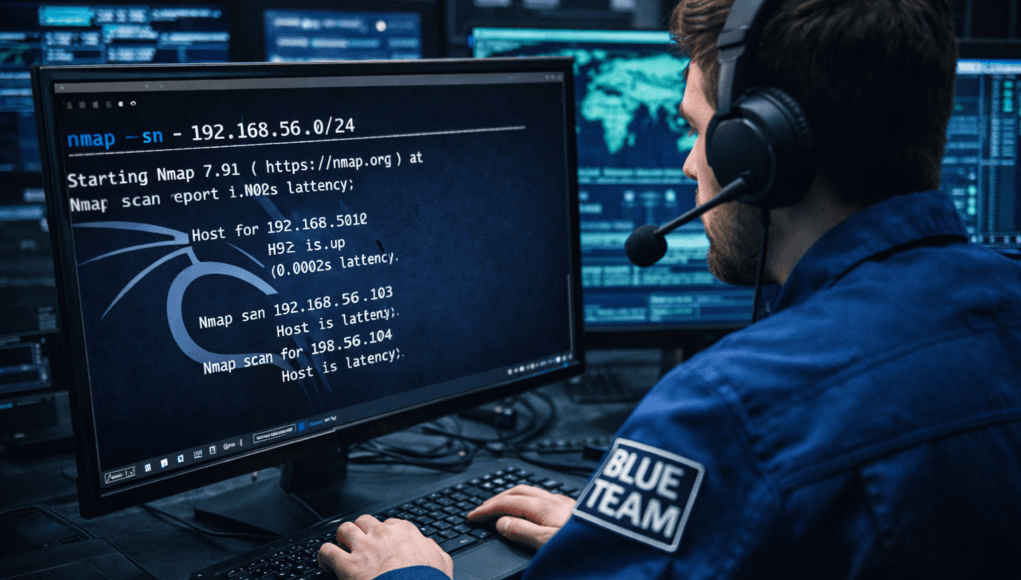
Network Scanning Tutorial Using Nmap — Day 2
Discovering Live Systems Like Real Attackers
Yesterday, you scanned one known machine.
That was controlled learning.
But real attackers never receive target IP addresses.
Nobody sends hackers an email saying:
“Here is our vulnerable server. Please scan it.”
Instead, attackers face uncertainty.
They see only:
- an organization name
- an IP range
- sometimes just a domain
Their first mission becomes:
✅ Find what actually exists.
This phase separates amateurs from professionals.
In enterprise penetration tests, I often spend hours — sometimes days — just identifying live hosts hidden inside networks.
Because here’s the uncomfortable truth:
You cannot attack what you cannot see.
Today you learn how attackers transform an unknown network into a visible battlefield using Host Discovery and Network Mapping with Nmap.
Note —
Day 1 taught how to scan.
Day 2 teaches what to scan.
Huge difference.
Why Host Discovery Matters
Imagine scanning a company network blindly:
10.10.0.0 – 10.10.255.255
That equals:
👉 65,536 possible systems
But reality?
Only 300 may be alive.
Scanning everything wastes:
- time
- bandwidth
- stealth
- operational safety
Professional attackers first identify:
✅ Live machines
✅ Active infrastructure
✅ Network layout
This reduces noise dramatically.
Real Pentest Observation
During a financial-sector assessment, the organization provided a /16 network.
Initial assumption:
Thousands of devices.
After host discovery?
Only 412 live hosts existed.
Attack surface reduced instantly.
Efficiency equals professionalism.
Defensive Insight
SOC teams monitor discovery scans heavily because:
Host discovery is often the first detectable intrusion indicator.
Blue teams label this as:
Reconnaissance Activity.
What is Host Discovery?
Host discovery answers one question:
Which systems are alive?
Nmap sends probes using different protocols:
- ICMP (Ping)
- TCP
- ARP
- UDP
Each checks system responsiveness differently.
Simple Analogy
Apartment building example:
- Ring bell → ICMP
- Knock door → TCP
- Check mailbox → ARP
Different techniques reveal occupants differently.
Firewalls may block one method but allow another.
Professional scanners adapt.
Confusion
Students think:
Ping works everywhere.
Enterprise networks frequently block ICMP.
Meaning:
System alive
But invisible to normal ping.
Nmap solves this.
Note —
Host discovery failure does not mean host absence.
It may mean defensive filtering.
This mindset shift is critical.
Professional Host Discovery Workflow
Real attacker workflow:
Step 1 — Define Target Range
CIDR notation understanding.
Example:
192.168.56.0/24
Represents 256 addresses.
Step 2 — Silent Host Identification
Avoid triggering alerts early.
Step 3 — Map Network Density
Understand infrastructure distribution.
Step 4 — Prioritize Targets
Servers > Workstations.
Enterprise Reality
Corporate environments include:
- VLAN segmentation
- NAC controls
- endpoint monitoring
- IDS correlation engines
Aggressive discovery immediately raises alarms.
Professionals start quietly.
✅ HANDS-ON PRACTICAL TUTORIAL (Live Lab)
We now simulate real reconnaissance.
Lab Preparation
Environment from Day 1 continues.
Machines Required
✅ Kali Linux (Attacker)
✅ Metasploitable2
✅ Optional Windows VM
Network Mode:
Host-Only Adapter
Step 1 — Identify Your Network Range
Command:
ip a
Example Output:
192.168.56.101
Network becomes:
192.168.56.0/24
Technical Explanation
CIDR /24 means:
First 24 bits = network
Last 8 bits = hosts
Range:
192.168.56.1 – 192.168.56.254
Note —
Beginners often scan wrong ranges.
Wrong range = zero results.
Always confirm network first.
Step 2 — Basic Ping Sweep
Goal:
Find live hosts.
Command:
nmap -sn 192.168.56.0/24
Command Breakdown
-sn→ Ping Scan (No port scan)- Faster
- Stealthier
Expected Output
Nmap scan report for 192.168.56.102
Host is up
Multiple hosts appear.
Beginner View
You see IP list.
Attacker View
Attacker now identifies:
- potential servers
- gateways
- virtual machines
- hidden infrastructure
Network visibility achieved.
Step 3 — ARP Discovery (Most Reliable Local Scan)
Command:
nmap -sn -PR 192.168.56.0/24
What Happens Technically?
ARP asks:
Who owns this IP?
Local systems MUST respond.
Firewalls rarely block ARP internally.
Enterprise Insight
Internal pentests rely heavily on ARP discovery.
It bypasses many defenses.
Step 4 — TCP SYN Host Discovery
When ICMP blocked:
nmap -sn -PS80,443 192.168.56.0/24
Meaning:
Send SYN packets to web ports.
Alive hosts respond.
Attacker Thinking Simulation
At this point attacker thinks:
Web services often allowed through firewalls.
So discovery disguises as normal traffic.
Step 5 — Skipping Host Discovery
Sometimes hosts ignore probes.
Force scan:
nmap -Pn 192.168.56.102
Treats host as alive.
Micro-Story
During a red-team engagement, ICMP was completely disabled.
Junior tester assumed network empty.
Using -Pn revealed:
Domain Controller online.
Critical lesson learned.
Troubleshooting Layer
No Hosts Found?
Check:
✅ Same network adapter
✅ VM running
✅ Firewall disabled in lab
Slow Scan?
Use:
nmap -T4 -sn network
Too Many Results?
Segment scan:
192.168.56.1-50
Professional targeting.
Note —
Discovery phase defines success later.
Never rush this step.
Real-World Scenario
Bug bounty reconnaissance once revealed:
Printer IP responding.
Ignored initially.
Printer hosted outdated web admin panel.
Led to internal credentials exposure.
Non-traditional assets matter.
Professional Tools Explained
Host discovery integrates with:
- Masscan
- Netdiscover
- Angry IP Scanner
- Asset management platforms
But Nmap remains preferred due to flexibility.
Professionals automate results into:
- vulnerability scanners
- exploitation frameworks
- threat intelligence mapping
Beginner Mistakes 🚨
Common failures:
❌ Scanning internet ranges randomly
❌ Ignoring stealth
❌ Missing subnet logic
❌ Assuming ping failure means offline
❌ Scanning entire /8 networks
Efficiency beats aggression.
Pro Tips From 20 Years Experience 🔥
- Discovery first, ports later.
- Scan smaller ranges intelligently.
- Identify infrastructure roles early.
- Gateways reveal topology.
- Repeat scans periodically.
Networks change constantly.
Defensive & Ethical Perspective
Blue Teams detect discovery through:
- ICMP bursts
- SYN sweeps
- abnormal ARP traffic
Defense actions:
- rate limiting
- segmentation
- deception hosts
Understanding discovery helps defenders reduce exposure.
Practical Implementation Checklist
✅ Network range identified
✅ Ping sweep executed
✅ ARP discovery completed
✅ TCP discovery tested
✅ Hidden hosts detected
✅ Output validated
Career Insight
Host discovery skills apply to:
- Red Team operations
- SOC investigations
- Incident response
- Threat hunting
- Asset discovery audits
Many breaches succeed because organizations don’t know their own assets.
Quick Recap
Today you learned:
✅ Network range identification
✅ Host discovery techniques
✅ ARP vs ICMP scanning
✅ Firewall bypass discovery
✅ Attacker reconnaissance thinking
Tomorrow changes everything.
We move from:
👉 Finding hosts
to
👉 Opening their doors
FAQs
Why use -sn instead of normal scan?
It avoids port scanning, making discovery faster and quieter.
Why does ping fail sometimes?
Firewalls block ICMP responses.
Is ARP scan detectable?
Yes internally, but harder to block.
Should discovery scans be aggressive?
No. Early stealth prevents detection.
What is CIDR notation?
Method defining network size using prefix bits.
Can host discovery reveal operating systems?
Not directly. That comes later.
Do companies monitor discovery scans?
Yes. SOC teams treat them as reconnaissance indicators.