If reconnaissance is about finding doors, enumeration in ethical hacking is about checking which doors are unlocked, what’s behind them, and who forgot to close the windows.
And here’s where most beginners get confused…
They think enumeration is just “running a tool.”
It’s not.
Enumeration is structured curiosity. It’s controlled digging. It’s the phase where a good penetration tester starts separating themselves from script-kiddie noise.
I’ve seen countless junior analysts rush through enumeration because they were excited to exploit something. And almost every time, they missed critical attack paths sitting right in front of them.
Let me break this down properly.
What is Enumeration in Ethical Hacking?
In simple terms:
Enumeration is the active process of extracting detailed information from a target system.
Not just discovering services — but pulling structured, actionable data from them.
Think of it like this:
Recon tells you:
“This building has a reception desk.”
Enumeration tells you:
“Receptionist name is Priya. She works 9–5. The visitor log is exposed. The admin office is behind Door 3.”
Big difference.
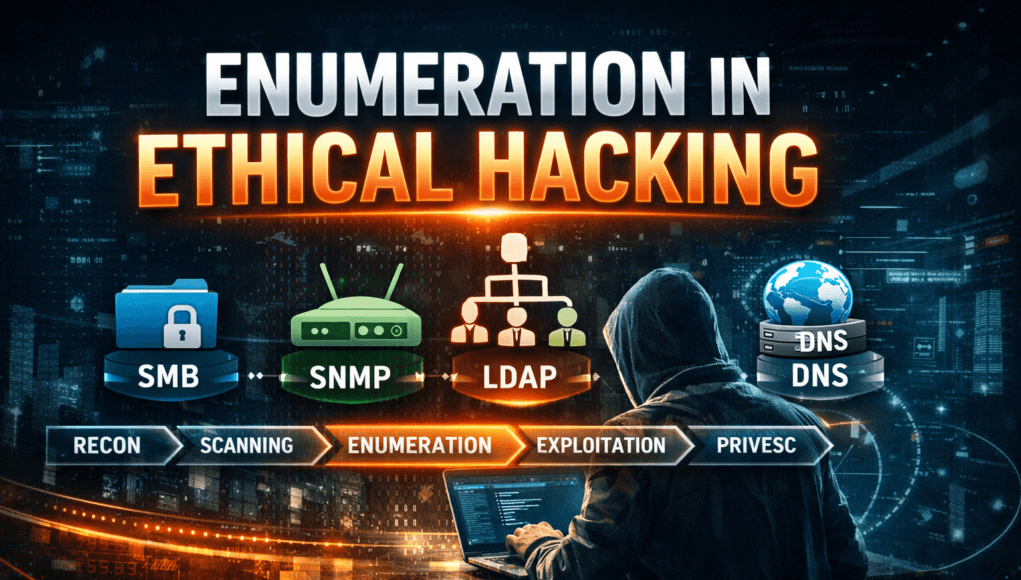
Technically speaking, enumeration happens after scanning (usually after identifying open ports using tools like Nmap). It involves interacting with services such as:
- SMB
- FTP
- SNMP
- LDAP
- DNS
- SMTP
- Web applications
- Active Directory
And extracting:
- Usernames
- Shares
- Domain info
- Service versions
- Policies
- Misconfigurations
Now here’s the key:
Enumeration is active interaction.
Which means it is detectable. That matters.
Why Enumeration is the Real Goldmine
In real assessments, what we usually see is this:
- Firewalls properly configured
- IDS/IPS monitoring traffic
- Patching somewhat decent
But…
- Weak SMB shares exposed
- LDAP leaking domain usernames
- SNMP using default community strings
- Anonymous FTP enabled
And guess what?
90% of internal breaches begin with weak enumeration findings.
Not zero-days.
Not Hollywood hacking.
Just poor configuration visibility.
Where Enumeration Fits in the Hacking Methodology
Let’s structure this properly:
- Reconnaissance (Passive)
- Scanning
- Enumeration
- Exploitation
- Privilege Escalation
- Lateral Movement
- Persistence
Enumeration is the bridge between “I see something” and “I can abuse something.”
Miss this step — and your exploitation attempts become blind guesses.
Step-by-Step Enumeration Process (Practical Walkthrough)
Let’s walk through this like we would in a lab or real engagement.
Step 1: Service Identification (Foundation Phase)
Before enumeration, we confirm services:
nmap -sV -sC target_ip
This identifies:
- Open ports
- Running services
- Version details
But here’s where most beginners stop.
Beginner Mistake Alert ⚠️
Running default scripts and assuming you’ve enumerated everything.
You haven’t.
You’ve barely scratched the surface.
Step 2: SMB Enumeration (Common Goldmine)
Why SMB?
Because misconfigured SMB is everywhere in internal networks.
We use:
- enum4linux
- smbclient
- Nmap SMB scripts
- CrackMapExec
Example:
enum4linux -a target_ip
We’re looking for:
- Usernames
- Shares
- Password policy
- Null session access
In real assessments, null session exposure is still shockingly common.
Mini Real Scenario
A financial firm once believed their network was hardened.
SMB allowed anonymous enumeration.
Within 15 minutes:
- Extracted 200+ domain usernames
- Identified naming convention
- Launched password spray
- Compromised 3 accounts
No exploit needed.
Just enumeration.
Step 3: SNMP Enumeration (The Silent Leak)
SNMP is often ignored. Big mistake.
Default community strings like:
- public
- private
Using:
snmpwalk -v2c -c public target_ip
You can extract:
- Running processes
- Network interfaces
- Installed software
- System uptime
Let me tell you — I’ve seen entire internal topologies mapped via SNMP leakage.
Step 4: LDAP & Active Directory Enumeration
In enterprise environments, Active Directory is king.
Tools:
- ldapsearch
- BloodHound
- PowerView
- CrackMapExec
BloodHound (by SpecterOps) changed how we see AD attacks.
It visualizes:
- Trust relationships
- Privilege paths
- Group memberships
And here’s the reality:
Most AD breaches happen because enumeration exposed a misconfigured privilege chain.
Not because of sophisticated malware.
Step 5: DNS Enumeration
DNS reveals:
- Subdomains
- Internal naming
- Mail servers
- Zone transfers
Try:
dig axfr @target_ip domain.com
If zone transfer works — you’ve hit jackpot.
Step 6: Web Application Enumeration
This is where creativity kicks in.
Tools:
- dirsearch
- gobuster
- ffuf
- Burp Suite (Burp Suite)
We look for:
- Hidden directories
- Backup files
- Admin panels
- API endpoints
- Debug parameters
Now here’s where beginners get overwhelmed.
They brute force 50,000 directories.
Instead, think logically.
Developers reuse naming conventions.
Look at:
- robots.txt
- sitemap.xml
- JS files
Enumeration is intelligence gathering — not blind brute forcing.
Tools Used in Professional Environments
Let me list tools I’ve personally used across red team engagements:
Network Enumeration
- Nmap
- enum4linux
- CrackMapExec
- rpcclient
Web Enumeration
- Burp Suite
- ffuf
- dirsearch
- WhatWeb
Active Directory
- BloodHound
- PowerView
- Impacket
SNMP
- snmpwalk
- onesixtyone
SMTP
- smtp-user-enum
Beginner Mistakes I’ve Seen Repeated for 20 Years
Let’s talk honestly.
1. Running One Tool and Stopping
Enumeration is layered.
One tool ≠ complete visibility.
2. Ignoring Error Messages
Error messages are information leaks.
Developers reveal internal paths accidentally.
3. Not Saving Output
You will forget findings.
Always document.
4. Skipping Low-Severity Findings
“Anonymous read-only share” looks harmless.
Until it contains credentials in Excel sheets.
Pro Tip from Field Experience 💡
Always enumerate with context.
Ask:
- What type of organization is this?
- What naming conventions might they use?
- What business apps might be running?
Enumeration without thinking is noise.
Enumeration with reasoning is strategy.
Real-World Example – Internal Network Enumeration
During an internal red team for a manufacturing company:
- SMB revealed naming format: firstname.lastname
- Password policy allowed 5 attempts
- VPN portal used same AD authentication
- Password spray succeeded
- VPN access gained externally
All from enumeration.
No exploit framework used.
Defensive & Ethical Considerations
Let’s be clear.
Enumeration is intrusive.
In real engagements:
- Always have written authorization
- Follow scope strictly
- Avoid Denial-of-Service risks
- Respect production systems
Ethical hacking is not about “how far can I go.”
It’s about “how responsibly can I demonstrate risk.”
Checklist: Enumeration Workflow
Use this every time:
☐ Identify services
☐ Run version detection
☐ Enumerate SMB
☐ Test SNMP
☐ Check DNS zone transfer
☐ Enumerate SMTP users
☐ Analyze web directories
☐ Investigate SSL/TLS configuration
☐ Map AD trust relationships
☐ Document everything
Quick Recap (If You Remember Nothing Else)
- Enumeration is active information extraction.
- It turns open ports into actionable intelligence.
- Most real-world compromises start here.
- It requires patience, logic, and documentation.
- Tools help — thinking wins.
FAQs (Answered Like I Would to a Student)
Is enumeration illegal?
Without authorization? Yes.
With written permission in a scoped engagement? It’s professional security testing.
Is Nmap enough for enumeration?
No. Nmap identifies services. Enumeration requires deeper interaction.
What is the most commonly exploited service?
In internal networks? SMB and Active Directory.
Externally? Web applications.
How do I get better at enumeration?
Practice in labs:
- Build Active Directory environments.
- Break them.
- Fix them.
- Repeat.
Is enumeration noisy?
Yes. It can trigger logs and alerts.
That’s why stealth matters.
Final Thought from 20 Years in the Field
Tools evolve.
Attack frameworks change.
But enumeration fundamentals? They haven’t changed much in two decades.
If you master enumeration:
You stop “trying exploits.”
You start engineering compromises.
And that’s when you transition from beginner to professional.




[…] Enumeration […]