A DDoS attack is one of the most common and dangerous cyber threats in today’s digital world. Whether you run a small blog, an eCommerce website, or a large platform, understanding DDoS attacks is essential to protect your online presence. Today we will learn what is DDOS attack and how hackers use it.
In simple terms, a DDoS attack can shut down your website, block your users, and cause serious financial and reputational damage. This guide explains what a DDoS attack is, how it works, types of DDoS attacks, real-world examples, and how to prevent DDoS attacks effectively.
If you want to protect your website and scale securely, this is a must-read guide.
Table of Contents
What Is DDoS Attack?
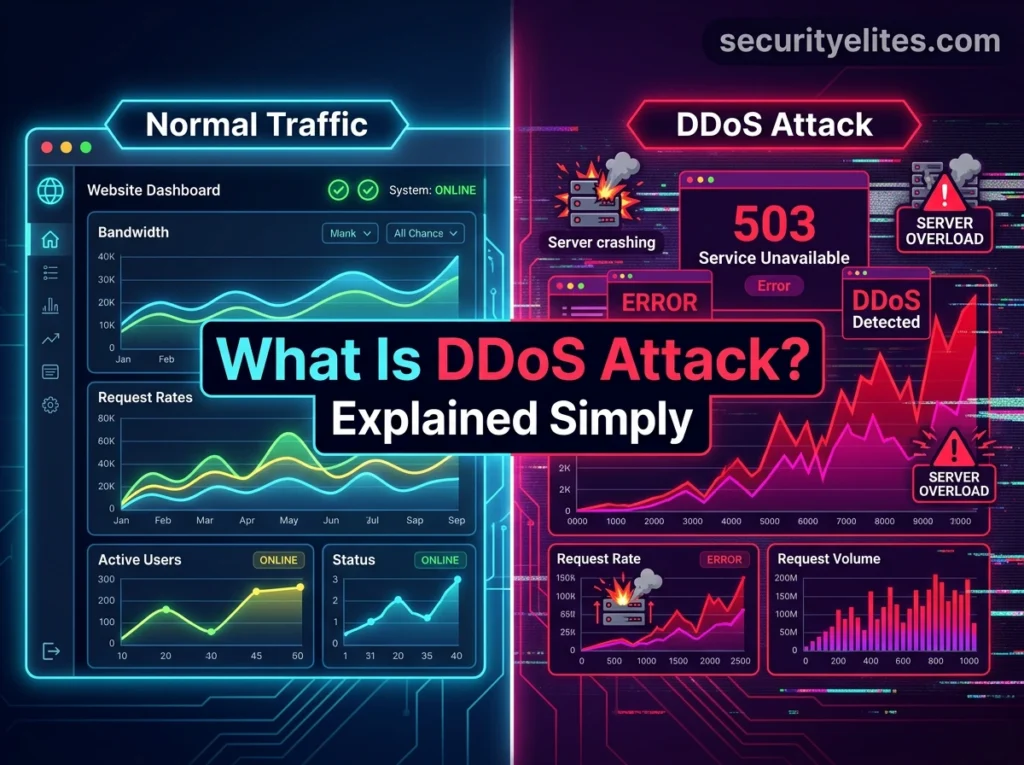
A DDoS attack (Distributed Denial-of-Service attack) is a type of cyberattack where multiple systems flood a target server, website, or network with massive traffic. The goal is to overwhelm the system so that it becomes slow or completely unavailable to real users.
Unlike a normal Denial-of-Service (DoS) attack, which comes from a single source, a DDoS attack uses multiple devices, making it much more powerful and difficult to stop.
In simple words, a DDoS attack is when thousands or millions of fake users try to access a website at the same time, causing it to crash.
To understand official cybersecurity definitions, refer to the Cloudflare DDoS guide, which explains how distributed attacks impact modern web infrastructure.
How Does a DDoS Attack Work?
To understand how a DDoS attack works, you need to understand the concept of botnets and coordinated traffic flooding.
Step 1: Creation of Botnet
Attackers first infect devices such as computers, smartphones, routers, and IoT devices with malware. These infected devices become part of a botnet, which is a network of compromised systems controlled by the attacker.
Step 2: Command and Control
The attacker uses a command-and-control server to send instructions to all devices in the botnet. These instructions tell the devices when and where to send traffic.
Step 3: Traffic Flooding
All infected devices simultaneously send a large number of requests to the target server or website. This traffic is not legitimate but is designed to overload the system.
Step 4: Resource Exhaustion
The server tries to handle all incoming requests but eventually runs out of resources such as bandwidth, CPU, or memory.
Step 5: Service Disruption
The website or application becomes slow or completely unavailable to real users. This is the final goal of a DDoS attack.
Types of DDoS Attacks
Understanding the types of DDoS attacks helps in identifying and preventing them effectively. There are three main categories.
1. Volumetric Attacks
Volumetric attacks aim to consume the entire bandwidth of the target system.
Common examples include UDP floods and ICMP floods. These attacks generate massive amounts of traffic to overwhelm the network capacity.
Impact: The network becomes congested, and legitimate traffic cannot reach the server.
2. Protocol Attacks
Protocol attacks target weaknesses in network protocols and server resources.
Examples include SYN floods and Ping of Death attacks. These attacks exploit how servers handle connections and can exhaust server resources.
Impact: The server becomes unable to process new requests.
3. Application Layer Attacks
Application layer attacks target specific applications or services such as web servers.
Examples include HTTP floods and login attacks. These attacks mimic real user behavior, making them harder to detect.
Impact: The application becomes slow or crashes while appearing to receive normal traffic.
Real-World Examples of DDoS Attacks
DDoS attacks have affected some of the largest platforms in the world.
Dyn DNS Attack (2016)
This attack disrupted major services including Twitter, Netflix, and GitHub. It used the Mirai botnet, which exploited vulnerable IoT devices.
GitHub Attack (2018)
GitHub experienced a massive 1.35 Tbps attack, making it one of the largest DDoS attacks at that time.
AWS Attack (2020)
Amazon Web Services faced a 2.3 Tbps attack, showing that even the most advanced infrastructures are not immune.
Why Do Attackers Launch DDoS Attacks?
Understanding the motivations behind DDoS attacks helps in anticipating threats. Below are few reasons why do hackers launch DDOS attacks.
- Financial Gain
- Competitive Advantage
- Political or Ideological Reasons
- Revenge or Personal Motives
- Testing Capabilities
Signs of a DDoS Attack
Recognizing early signs of a DDoS attack can help minimize damage.
- Sudden spike in traffic
- Slow website performance
- Frequent server crashes
- High CPU or memory usage
- Unusual traffic patterns from specific regions
- Multiple requests from the same IP ranges
Impact of DDoS Attacks on Businesses
DDoS attacks can have serious consequences for businesses.
- Every minute of downtime can result in lost sales and missed opportunities.
- Damage to Reputation
- Users may lose trust in your platform if it becomes unreliable.
- Search engines may lower rankings if your website experiences frequent downtime.
- Business operations may be interrupted, affecting productivity and customer experience.
How to Prevent DDoS Attacks ?
Preventing DDoS attacks requires a multi-layered approach.
Use a Content Delivery Network (CDN)
A CDN distributes traffic across multiple servers, reducing the impact of large traffic spikes.
Implement a Web Application Firewall (WAF)
A WAF filters malicious traffic and blocks suspicious requests.
Enable Rate Limiting
Rate limiting restricts the number of requests a user can make in a given time period.
Use Load Balancing
Load balancing distributes traffic across multiple servers to prevent overload.
Monitor Traffic in Real-Time
Continuous monitoring helps detect unusual traffic patterns early.
Use Security Tools
Tools such as IP lookup, WHOIS analysis, and malware detection can help identify potential threats before they escalate.
Best Practices for Website Owners
To protect your website and ensure scalability, follow these best practices.
- Use cloud-based protection services
- Keep systems and software updated
- Maintain regular backups
- Implement strong access controls
- Monitor server performance continuously
- Plan for scalability during traffic spikes
Conclusion
A DDoS attack is a serious cybersecurity threat that can disrupt websites, damage reputation, and cause financial losses. Understanding how DDoS attacks work, their types, and prevention strategies is essential for anyone managing an online platform.
By implementing strong security measures, monitoring traffic, and using reliable tools, you can protect your website and ensure uninterrupted service.
Staying proactive is the key to defending against DDoS attacks in an increasingly connected world.
Frequently Asked Questions
What is a DDoS attack in simple words?
A DDoS attack is when multiple computers send a large amount of fake traffic to a website or server, making it slow or completely unavailable for real users.
How does a DDoS attack work?
A DDoS attack works by using a network of infected devices, called a botnet, to send massive traffic to a target server. This overloads the server’s resources and causes downtime.
What is the main purpose of a DDoS attack?
The main purpose of a DDoS attack is to disrupt a website or service. Attackers may do this for financial gain, competition, political reasons, or to damage reputation.
What are the types of DDoS attacks?
The main types of DDoS attacks are volumetric attacks, protocol attacks, and application layer attacks. Each targets different parts of a system.
Can a small website get a DDoS attack?
Yes, small websites can be targeted by DDoS attacks. In fact, attackers often target smaller sites because they usually have weaker security.
Is a DDoS attack illegal?
Yes, DDoS attacks are illegal in most countries. Launching such attacks can lead to serious legal consequences including fines and imprisonment.
Can DDoS attacks steal data?
DDoS attacks do not directly steal data. Their main goal is to disrupt services, but they can be used as a distraction for other attacks.
How do I detect a DDoS attack early?
You can detect a DDoS attack by monitoring unusual traffic spikes, slow performance, high server load, and repeated requests from suspicious IP addresses.