Mobile Hacking
11 articles
How Hackers Exploit Bluetooth Devices in 2026 — Bluejacking, Bluesnarfing & BIAS Attacks
How hackers exploit Bluetooth in 2026 — bluejacking, bluesnarfing, BIAS authentication bypass, BLE attacks, and how to protect your devices.…
How Hackers Bypass 2FA in 2026 — 7 Methods That Still Work (Ethical Analysis)
How hackers bypass 2fa 2026 — 7 real methods used to circumvent two-factor authentication including SIM swapping, SS7 attacks, AiTM…
2.3 Million Android Phones Were Infected via Google Play — How the NoVoice Rootkit Works (2026)
Operation NoVoice Android Malware hid a rootkit in 50+ Google Play apps with 2.3M downloads. Factory reset won’t remove it.…
Can Someone Hack Your Phone Just By Calling You? (2026 Reality)
Can someone hack your phone just by calling you in 2026? Here’s the honest answer—what’s real, what’s a myth, which…
AI Scam Calls 2026 — How Voice Cloning Scams Work and Exactly How to Protect Yourself and Your Family
AI scam calls are the fastest-growing fraud in 2026. Criminals clone real voices in seconds to trick families, businesses, and…
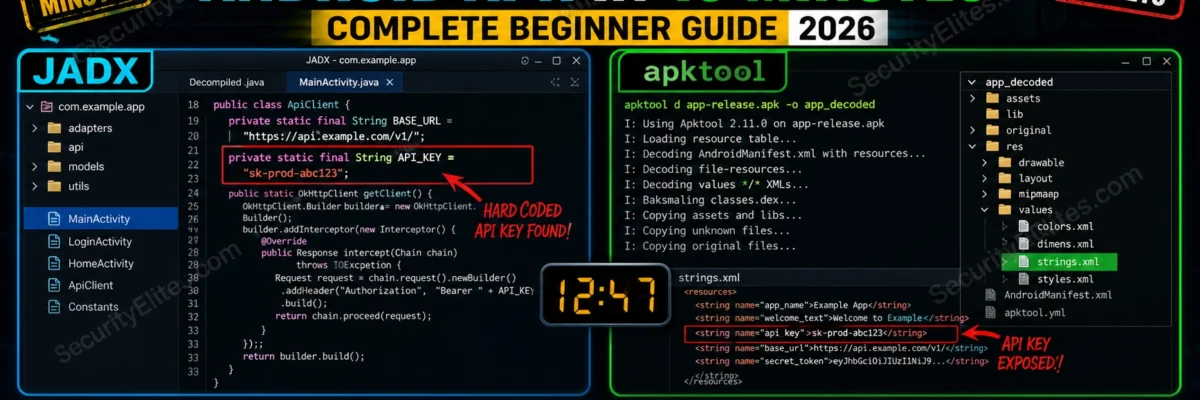
How to Hack Android Phone Ethically 2026 – ADB, Metasploit & APK Analysis Guide
Learn how to hack Android phones ethically using ADB, Metasploit & APK analysis. Complete mobile penetration testing guide for 2026.
Is Someone Spying on Your Phone? 7 Hidden Signs You Must Check NOW (2026)
Is Someone Spying on Your Phone? Discover 7 hidden signs of stalkerware and how to detect and remove spyware instantly…
10 Signs Your Phone Has Been Hacked (Fix It Immediately Before It’s Too Late)
Think your phone is hacked? Discover 10 warning signs your phone has been hacked and exactly what to do right…
Hackers Are Watching You Through Camera (2026) – How to Stop It Before It’s Too Late
Hackers are watching you through your camera right now. Learn how webcam hacking works and how to stop it before…