Stop for a Moment — This Could Be Happening Right Now.
Your phone can be hacked in seconds. Not later. Not someday. Right now. Before you continue, take a second and look at your phone.
Ask yourself honestly:
“If someone had access to my phone at this exact moment… would I know?”
Most people wouldn’t. And that’s the real danger.
Because modern hacking doesn’t look like hacking anymore. There’s no warning screen, no loud alert, no dramatic sign. Everything looks normal — while something abnormal is already happening. You can check if your email is already compromised on our new Email Breach Check tool.
This is exactly how people lose control of their data, accounts, and even money… without realizing it until it’s too late.
Table of Contents
What Does Your Phone Can Be Hacked in Seconds Actually Mean?
Think of your phone like your personal vault.
Inside it, you have:
- Your identity
- Your private conversations
- Your photos and memories
- Your banking access
Now imagine someone gaining access to that vault. Not by breaking it… but because you unknowingly left a small gap open.
That’s how hacking works today.
Hackers don’t rely on brute force. They rely on small, everyday mistakes — clicking a link, installing an app, connecting to a network without thinking. And once that small opening appears, access happens almost instantly.
The scary part is not how they enter. The scary part is how invisible it is.
How Hackers Hack Mobile Phones ?
Let’s break this down in a way most people never think about.
It usually starts with something that feels completely normal.
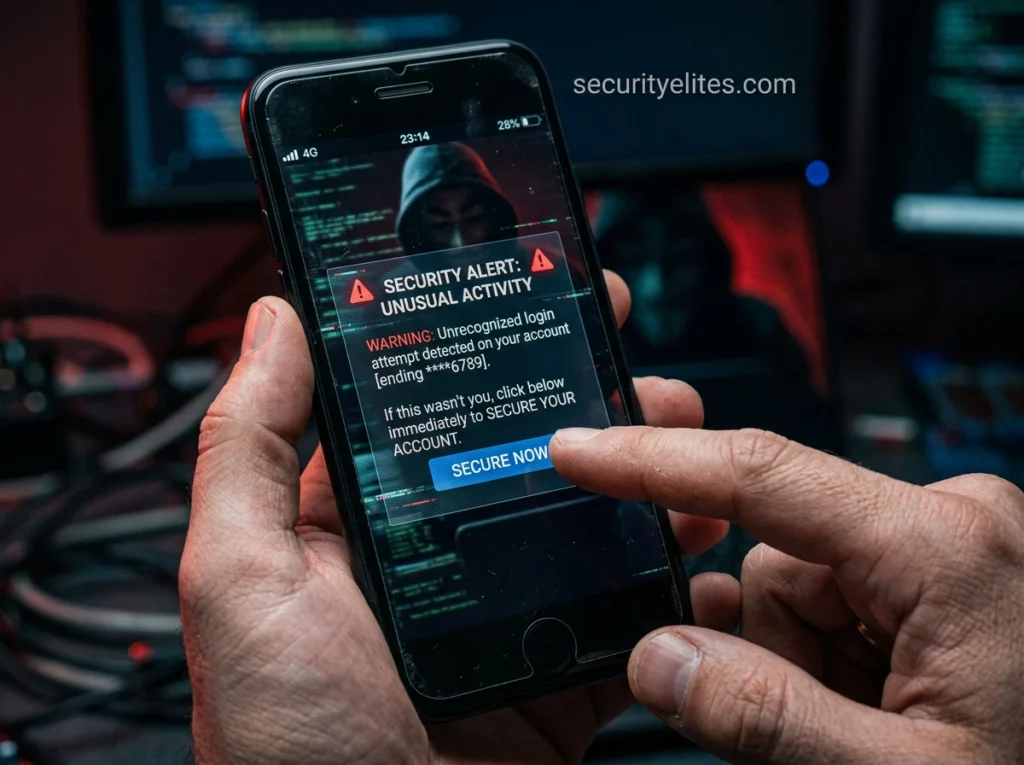
You receive a message, an email, or even a notification. It creates urgency — something needs your attention immediately.
Without thinking too much, you click. At that moment, nothing unusual appears. The page may look real. The app may behave normally. You feel everything is fine.
But behind the scenes, a chain of events may have already started. A hidden script runs. Permissions are triggered. Background processes begin collecting information.
Your phone starts sharing:
- Login credentials
- Messages
- OTPs
- Usage patterns
And you continue using your phone… unaware.
This is why these attacks are so effective. They don’t interrupt you. They blend into your normal behavior.
Reality Check –
Most people assume hacking is rare or targeted. In reality, it’s often casual and opportunistic.
- You connect to free WiFi at an airport because it’s available. It works smoothly, so you trust it. But that network could be controlled by someone monitoring traffic in real time.
- You install an app because it looks useful. It has good ratings, a clean interface, and no obvious warning signs. But hidden within it could be tracking mechanisms collecting more data than necessary.
- You receive a link from someone you know. There’s no reason to doubt it, so you open it instantly. That single action can be enough to expose your device.
These situations feel normal.
And that’s exactly why they work.
Common Android Phone Hacking Methods Used Today
To understand how to protect yourself, you need to understand how attacks actually happen.
- Phishing remains one of the most powerful methods. Attackers create pages that look identical to trusted platforms. Once you enter your details, they are captured immediately.
- Spyware takes a quieter approach. It installs itself as a normal app or hidden process and continuously monitors your activity. It doesn’t need to act fast — it just needs to stay unnoticed.
- Public network interception allows attackers to observe data as it moves between your device and the internet. This is especially effective on unsecured networks.
- More advanced methods, such as zero-click exploits, don’t require any interaction. These target system vulnerabilities directly and can execute without user action.
Most people are only aware of basic threats.
The real risks often go unnoticed.
How to Check If Your Phone Is Already Compromised

This is where awareness becomes important. Start by paying attention to behavior, not just obvious signs.
- If your phone heats up without heavy usage, it may indicate background activity. If your battery drains faster than usual, something could be running continuously.
- Unexpected data usage is another strong indicator. If you are not actively using data but consumption increases, something may be transmitting information.
- Look at your installed apps carefully. If you find anything unfamiliar or something you don’t remember installing, don’t ignore it.
- Also notice performance changes. Slower response, random popups, or unusual glitches can be signals.
None of these signs alone confirm hacking.
But together, they should raise concern.
How to Secure Your Smartphone Fast (Step-by-Step Action Plan)

Now let’s move from awareness to action.
- Start with a full review of your apps. Open your settings and go through each one. Remove anything you don’t fully recognize or no longer use. Reducing unnecessary apps reduces risk immediately.
- Next, audit permissions. Check which apps have access to sensitive features like camera, microphone, storage, and location. If an app doesn’t truly need it, revoke access.
- Change your interaction habits. Before clicking any link, pause and think. Where did it come from? Does it make sense? That small delay is one of the strongest defenses.
- Control your network exposure. Avoid automatic WiFi connections and be cautious when using public networks. If you must connect, limit sensitive activity.
- Keep your system updated. Updates are not just for features — they patch security vulnerabilities that attackers actively exploit. Security updates are critical because companies like Google Android Security continuously patch vulnerabilities that hackers actively exploit.
- Finally, consider using basic security tools. Even simple protection layers can block common threats.
Security is not about doing one big thing.
It’s about doing small things consistently.
What Most People Don’t Understand About Hacking
After years in cybersecurity, one truth stands out. The weakest point is rarely the device.
It’s the user.
Hackers understand how people think. They know how urgency creates pressure, how fear overrides logic, and how curiosity leads to quick decisions. That’s why attacks are designed to feel urgent, important, or familiar.
The moment you react without thinking, control shifts.
But when you slow down and question what you see, you break that pattern.
And that’s where real security begins.
Common Mistakes That Increase Risk –
Most vulnerabilities are not created by advanced attacks. They are created by repeated small habits.
Clicking links without verifying them, using the same password across multiple platforms, ignoring updates, installing unofficial apps, and trusting public WiFi blindly all contribute to risk.
Individually, these actions seem harmless. Over time, they create multiple entry points. And attackers only need one.
FAQs (Quick Answers You Should Not Ignore)
Can your phone really be hacked in seconds?
Yes, and this is not an exaggeration. Many modern attacks, especially phishing links and automated exploits, can compromise a phone within seconds after you click or interact. In some advanced cases, even opening a message is enough.
How do hackers hack mobile phones without touching them?
Hackers use remote methods like malicious links, fake apps, unsecured WiFi networks, and software vulnerabilities. You don’t need to hand over your phone — your interaction alone is enough to give access.
What are the first signs that your phone is hacked?
The earliest signs are usually subtle. You may notice faster battery drain, unusual heating, unknown apps, increased data usage, or small performance issues. Most people ignore these signs until it becomes serious.
Can spyware stay hidden on a phone?
Yes. Spyware is designed to stay invisible. It runs quietly in the background, collects data, and avoids detection. That’s why many users don’t realize they are being monitored.
Is Android more vulnerable to hacking?
Android is not inherently unsafe, but because of its open ecosystem, users have more control — and more responsibility. Installing apps from unknown sources or ignoring permissions increases risk significantly.
Does factory reset remove all hacking threats?
In most cases, a factory reset removes common malware and spyware. However, highly advanced threats may survive or return if the same unsafe behavior continues after resetting.
Is public WiFi safe for everyday use?
Public WiFi should always be treated as risky. While not every network is malicious, attackers often exploit open networks to intercept data. Avoid sensitive activities like banking when connected. According to CISA (Cybersecurity & Infrastructure Security Agency), unsecured networks remain one of the most common entry points for attackers.
Can someone hack my phone just by knowing my number?
Not directly in most cases. However, your number can be used for phishing, SIM swap attacks, or targeted scams that may eventually lead to a compromise.
How often should I check my phone for security issues?
At least once every few weeks. A quick review of apps, permissions, and unusual behavior can help you detect problems early before they become serious.
Final Thoughts — This Decision Matters
Before you leave, do something simple. Pick up your phone.
Go through it slowly. Check your apps. Review your settings. Pay attention to what feels different.
Because now you understand something most people ignore.
You understand how quickly access can happen. You understand how silently it works.
And most importantly — you know how to reduce your risk. Most people will read this and forget it.
Some will take action. Don’t forget to check if your password is breached, check right now using Password Breach Checker tool by Securityelites.
That difference may not feel big right now.
But in situations like this… it changes everything.