What if you could see the internet the same way hackers do — spotting vulnerabilities before anyone else? In today’s rapidly evolving digital world, cyber threats are becoming more sophisticated, and organizations rely heavily on ethical hackers to identify security weaknesses before attackers exploit them.
At SecurityElites, our mission is to help aspiring cybersecurity professionals understand the tools and techniques used by real ethical hackers. One of the most important parts of penetration testing is having the best ethical hacking tools that can scan networks, analyze vulnerabilities, and simulate real-world cyberattacks.
Ethical hackers rely on powerful tools to identify vulnerabilities before attackers do. If you’re new to cybersecurity, start by understanding the ethical hacking techniques used by professionals.
In this guide, you will discover 15 of the best ethical hacking tools used by hackers in 2026, helping you understand how cybersecurity experts identify and fix vulnerabilities before attackers strike.
Table of Contents
15 Best Ethical Hacking Tools Used by Hackers
Modern cybersecurity professionals use a combination of best ethical hacking tools for different tasks such as network scanning, web application testing, password auditing, vulnerability exploitation, reconnaissance, and traffic analysis. Each tool plays a specific role in the penetration testing process, helping ethical hackers understand how attackers might target systems.
Below are 15 of the best ethical hacking tools used by hackers in 2026, widely trusted by penetration testers, bug bounty hunters, and cybersecurity experts around the world.
1. NMAP
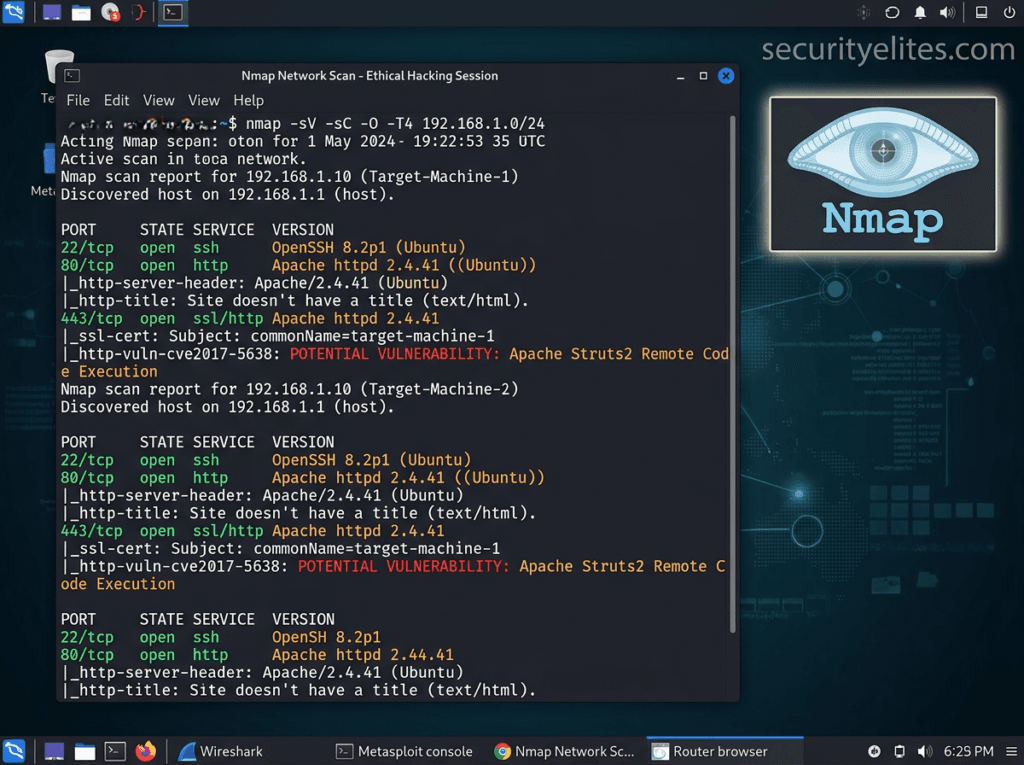
One of the most essential tools in any ethical hacker’s toolkit is Nmap, shortform for Network Mapper. This powerful open-source tool is used for network discovery and security auditing, making it one of the most widely used ethical hacking tools in the cybersecurity industry.
Security professionals use Nmap to scan networks, identify active devices, and detect open ports and services running on target systems. Understanding which services are exposed on a network is a critical step in penetration testing because attackers often exploit vulnerable services to gain unauthorized access.
Nmap works by sending specially crafted packets to target machines and analyzing the responses. This allows ethical hackers to determine which ports are open, what operating systems are running, and which services are available.
Key Features
Nmap provides a wide range of capabilities that make it indispensable for cybersecurity professionals.
- Network host discovery
- Port scanning
- Operating system detection
- Service version detection
- Network topology mapping
- Firewall evasion techniques
These features allow penetration testers to build a detailed picture of the target network before attempting any exploitation.
Why Ethical Hackers Use Nmap
Network reconnaissance is the first step in most penetration tests. Before exploiting vulnerabilities, ethical hackers must understand the network structure.
Nmap helps security professionals:
- discover hidden devices on a network
- identify vulnerable services
- analyze firewall configurations
- map network infrastructure
Because of its reliability and flexibility, Nmap is widely used by cybersecurity professionals, system administrators, and security researchers.
2. Burp Suite
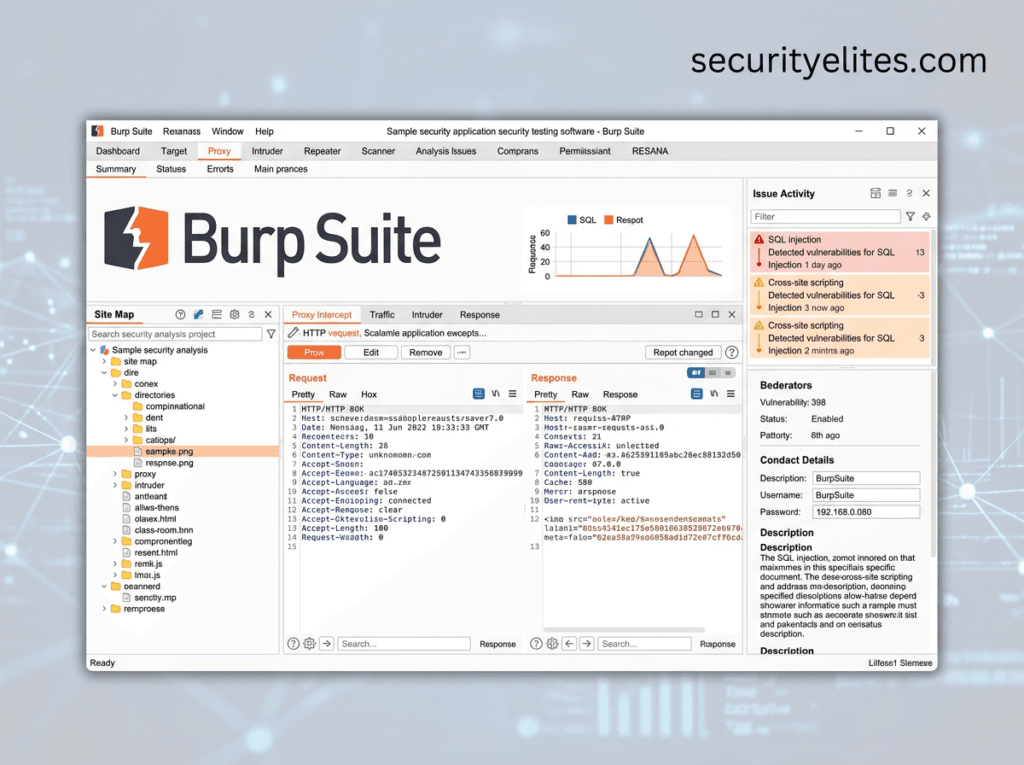
Modern applications rely heavily on web technologies. Unfortunately, web applications are also one of the most common targets for cyberattacks.
This is where Burp Suite becomes extremely valuable.
Official link: https://portswigger.net/burp
Burp Suite is a powerful platform used for web application penetration testing. Developed by PortSwigger, it allows ethical hackers to intercept, analyze, and modify web traffic between browsers and servers.
By acting as a proxy between the browser and the web server, Burp Suite allows penetration testers to inspect every request and response exchanged by the application.
Key Features
Burp Suite includes multiple tools designed for web security testing.
- Intercepting proxy
- Automated vulnerability scanning
- Intruder for automated attack testing
- Repeater for manual request manipulation
- Decoder for analyzing encoded data
- Comparer for analyzing differences in responses
These tools help ethical hackers analyze how web applications process data and identify security weaknesses.
Vulnerabilities Burp Suite Can Detect
Burp Suite is commonly used to detect serious web vulnerabilities such as:
- SQL Injection
- Cross-Site Scripting (XSS)
- Cross-Site Request Forgery (CSRF)
- authentication bypass vulnerabilities
- insecure session management
Because web applications often handle sensitive data, identifying these vulnerabilities is critical for protecting users and organizations.
Why Burp Suite Is Popular
Many professional penetration testers and bug bounty hunters consider Burp Suite their primary tool.
Its flexibility allows both automated scanning and manual testing, which is essential for discovering complex vulnerabilities.
For anyone interested in web application security, learning Burp Suite is an essential skill.
3. Metasploit
Metasploit is one of the most powerful penetration testing frameworks available today. It allows ethical hackers to test vulnerabilities by safely simulating real cyberattacks.
Developed by Rapid7, Metasploit provides a large database of exploits, payloads, and auxiliary modules that security professionals use to assess system security.
Instead of writing exploit code from scratch, penetration testers can use Metasploit to quickly test whether a vulnerability can be exploited.
Key Features
Metasploit provides a complete framework for vulnerability exploitation and security testing.
Important features include:
- exploit development tools
- payload generation
- vulnerability scanning modules
- post-exploitation capabilities
- session management
These features allow security professionals to test how attackers might gain access to systems.
Why Metasploit Is Important
Metasploit allows penetration testers to simulate real attacks in a safe environment.
For example, if a vulnerability is discovered in a system, Metasploit can test whether it can be exploited to gain remote access.
This helps organizations understand the severity of vulnerabilities and prioritize security fixes.
Because of its powerful capabilities, Metasploit remains one of the most important tools in professional ethical hacking.
4. Wireshark
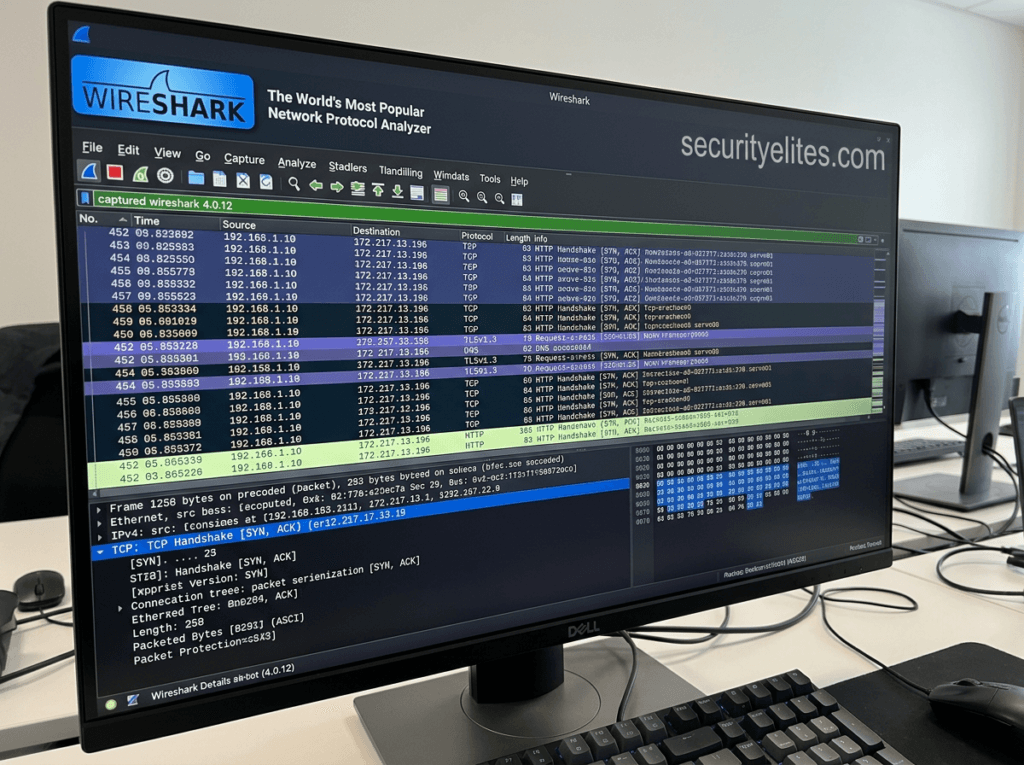
Wireshark is one of the most powerful network analysis tools used in cybersecurity. It allows ethical hackers to capture and analyze network traffic in real time.
Network traffic consists of data packets traveling between devices on a network. By analyzing these packets, security professionals can detect suspicious activity, identify vulnerabilities, and troubleshoot network issues.
Wireshark provides deep visibility into network communications.
Key Features
Wireshark offers several advanced capabilities.
- Real-time packet capture
- Deep packet inspection
- Network protocol analysis
- Traffic filtering and searching
- Security anomaly detection
These features allow security professionals to examine network behavior in detail.
Why Ethical Hackers Use Wireshark
Understanding how data travels across a network is essential for cybersecurity.
Wireshark allows ethical hackers to:
- detect malicious network traffic
- analyze suspicious activity
- identify unencrypted sensitive data
- investigate network attacks
For example, if sensitive data such as passwords is transmitted in plain text, Wireshark can reveal the vulnerability.
5. John the Ripper
Passwords remain one of the weakest points in cybersecurity. Even today, many users rely on predictable passwords such as simple words, reused credentials, or short numeric combinations. These weak passwords create opportunities for attackers to gain unauthorized access to systems.
One of the most widely used tools for testing password strength is John the Ripper. It is a powerful password auditing and recovery tool designed to identify weak credentials within systems and applications.
Security professionals often use John the Ripper during penetration testing engagements to determine whether user passwords are strong enough to resist cracking attempts. If the tool can quickly recover passwords from hashed data, it indicates that the organization needs stronger password policies.
Key Features
John the Ripper provides several advanced capabilities that make it extremely effective.
- Dictionary-based password attacks
- Brute force password cracking
- Support for hundreds of password hash formats
- Automatic hash detection
- GPU acceleration for faster cracking
The tool supports password hashes used by operating systems, databases, and web applications.
Why Ethical Hackers Use John the Ripper
During security assessments, ethical hackers often gain access to password hashes stored on systems. These hashes can then be tested using John the Ripper to determine how easily they can be cracked.
If passwords are cracked quickly, the organization may need to implement stronger password requirements such as:
- longer password lengths
- complex character combinations
- multi-factor authentication
Testing password strength is a critical part of protecting sensitive systems.
6. Aircrack-ng
Wireless networks are an essential part of modern connectivity. Businesses, universities, and public spaces rely on WiFi networks to provide internet access to users.
However, poorly secured wireless networks can create significant security risks. If attackers gain access to a wireless network, they may be able to intercept traffic, launch attacks on internal systems, or steal sensitive information.
Aircrack-ng is a suite of tools designed for testing the security of wireless networks. It is widely used by ethical hackers to evaluate WiFi security and identify weaknesses in wireless encryption.
Key Features
Aircrack-ng includes several tools for wireless security testing.
- Packet capture and analysis
- WiFi password cracking
- Wireless network monitoring
- Deauthentication attack testing
- WPA/WPA2 password auditing
These features allow ethical hackers to analyze wireless traffic and test encryption strength.
Why Wireless Security Testing Is Important
Many organizations underestimate the importance of wireless network security. Weak encryption or default router settings can allow attackers to gain unauthorized access.
Aircrack-ng helps ethical hackers determine whether wireless networks are properly secured and resistant to attacks.
7. Nikto
Web servers host websites, APIs, and online services used by millions of people every day. If these servers are misconfigured or running outdated software, they may expose vulnerabilities that attackers can exploit.
Nikto is an open-source web server scanner designed to detect dangerous files, outdated software, and security misconfigurations.
Official link: https://github.com/sullo/nikto
It is widely used during web penetration testing to identify weaknesses in server configurations.
Key Features
Nikto performs extensive security checks on web servers.
- Detection of outdated server software
- Identification of dangerous files and scripts
- Security misconfiguration detection
- SSL configuration testing
- Vulnerability scanning
The tool scans thousands of known vulnerabilities and generates detailed reports.
Why Ethical Hackers Use Nikto
Many web servers contain hidden vulnerabilities that administrators may not be aware of. Nikto helps security professionals detect these issues quickly.
For example, Nikto can identify:
- outdated server versions
- exposed backup files
- insecure default configurations
- vulnerable CGI scripts
Detecting these weaknesses early allows organizations to fix vulnerabilities before attackers discover them.
8. Hydra
Authentication systems protect access to servers, databases, and applications. However, if login systems allow unlimited attempts, attackers may attempt brute-force attacks to guess passwords.
Hydra is a fast and flexible network login cracker used to test authentication systems.
Unlike John the Ripper, which focuses on password hashes, Hydra targets online login services.
Key Features
Hydra supports many network protocols including:
- SSH
- FTP
- HTTP
- SMTP
- Telnet
- RDP
This allows ethical hackers to test password security across multiple services.
Why Ethical Hackers Use Hydra
Weak login security is a common vulnerability in many systems.
Hydra helps security professionals test whether authentication systems can withstand brute-force attacks.
If Hydra successfully guesses passwords, it indicates the system requires stronger security measures.
9. SQLmap
SQL injection remains one of the most dangerous vulnerabilities affecting web applications. It occurs when attackers manipulate database queries to access or modify sensitive information.
SQLmap is a powerful automated tool designed to detect and exploit SQL injection vulnerabilities.
Security professionals use SQLmap to test web applications and ensure databases are properly secured.
Key Features
SQLmap offers several advanced capabilities.
- Automated SQL injection detection
- Database fingerprinting
- Data extraction from databases
- Database takeover capabilities
- Password hash extraction
These features make SQLmap one of the most powerful tools for database security testing.
Why SQL Injection Is Dangerous
SQL injection attacks can allow attackers to:
- access confidential user data
- bypass login systems
- modify database records
- delete entire databases
Because of these risks, testing web applications for SQL injection vulnerabilities is essential.
10. FFUF
During penetration testing, attackers often look for hidden directories, files, and endpoints within web applications.
These hidden resources may contain sensitive functionality such as administrative panels or development environments.
FFUF (Fuzz Faster U Fool) is a high-speed web fuzzing tool used to discover hidden resources within web applications.
Key Features
FFUF provides powerful fuzzing capabilities.
- High-speed directory fuzzing
- Parameter discovery
- API endpoint discovery
- Multi-threaded scanning
- Custom wordlist support
Its speed makes it extremely popular among bug bounty hunters.
Why Ethical Hackers Use FFUF
Many web applications contain hidden endpoints that are not visible through normal browsing.
FFUF helps ethical hackers discover these hidden areas by sending large numbers of requests with different wordlists.
This process often reveals:
- hidden admin panels
- backup files
- private APIs
- development environments
When combined with other tools like SQLmap and Burp Suite, FFUF becomes a powerful component of the ethical hacker toolkit.
11. OWASP ZAP
Web applications power many modern services including banking platforms, e-commerce websites, social networks, and cloud dashboards. Because these applications process sensitive user data, they are common targets for cyberattacks.
One of the most effective tools used to test web application security is OWASP ZAP (Zed Attack Proxy). Developed by the Open Web Application Security Project, OWASP ZAP is an open-source web security scanner designed to identify vulnerabilities in web applications.
Security professionals use this tool to detect common web vulnerabilities before attackers discover them.
Key Features
OWASP ZAP includes powerful capabilities for both automated and manual security testing.
- Automated web vulnerability scanning
- Passive and active security testing
- Proxy interception of HTTP traffic
- Web application spidering and crawling
- API security testing
These features allow ethical hackers to analyze how web applications respond to user input and identify potential weaknesses.
Why Ethical Hackers Use OWASP ZAP
OWASP ZAP is particularly valuable because it is beginner-friendly while still offering powerful capabilities used by professional penetration testers.
The tool can detect vulnerabilities such as:
- Cross-Site Scripting (XSS)
- SQL injection vulnerabilities
- insecure authentication mechanisms
- sensitive data exposure
- session management flaws
Because it integrates well with development pipelines, many companies use OWASP ZAP in automated security testing processes.
OWASP ZAP is widely used for:
- web application penetration testing
- API security testing
- DevSecOps security automation
- vulnerability assessments
Testing web applications regularly helps organizations prevent serious security breaches.
12. Maltego
Before attempting to exploit vulnerabilities, ethical hackers must first gather information about their target. This process is known as reconnaissance. One of the most powerful tools used for reconnaissance is Maltego, an intelligence gathering platform designed to map relationships between digital entities.
Maltego is widely used by security researchers, penetration testers, and investigators to analyze publicly available information.
Key Features
Maltego provides advanced capabilities for intelligence gathering.
- Open-source intelligence (OSINT) collection
- relationship mapping between entities
- domain and IP investigation
- email and username discovery
- infrastructure mapping
The tool visualizes connections between entities using graphical diagrams, making it easier to analyze large datasets.
Why Ethical Hackers Use Maltego
Understanding the target environment is crucial for successful penetration testing.
Maltego helps ethical hackers identify:
- company domains and subdomains
- exposed infrastructure
- public employee email addresses
- connected servers and services
This information helps security professionals understand potential attack surfaces.
Maltego is commonly used for:
- penetration testing reconnaissance
- digital investigations
- threat intelligence research
- cybercrime investigations
Its visualization capabilities make it one of the most advanced reconnaissance tools available.
13. Kali Linux
Unlike most tools on this list, Kali Linux is not just a single tool but an entire operating system designed specifically for penetration testing.
Developed by Offensive Security, Kali Linux includes hundreds of cybersecurity tools preinstalled, making it one of the most widely used platforms for ethical hackers.
Security professionals often use Kali Linux as their primary operating system for performing security assessments. We have shared complete beginners guide for Kali Linux, go through same for learning it in detail.
Key Features
Kali Linux provides a complete penetration testing environment. The operating system includes tools for:
- network scanning
- vulnerability assessment
- password cracking
- wireless security testing
- digital forensics
- reverse engineering
Because these tools are preinstalled and preconfigured, security professionals can start testing immediately.
Why Ethical Hackers Use Kali Linux
Kali Linux simplifies the penetration testing process by providing a centralized environment containing all the necessary tools.
For example, Kali Linux includes tools such as:
- Nmap
- Burp Suite
- Metasploit
This eliminates the need to install and configure each tool individually.
Kali Linux is widely used in:
- professional penetration testing
- cybersecurity research
- security training programs
- ethical hacking certifications
Because of its versatility and extensive toolset, Kali Linux has become the standard operating system for many ethical hackers.
14. Dirb
Many web applications contain hidden directories and files that are not visible through normal browsing. These hidden locations may contain sensitive information such as administrative panels, configuration files, or backup data.
Dirb is a web content scanner used to discover hidden directories and files on web servers. It works by performing dictionary-based brute-force scans against web applications.
Key Features
Dirb offers several useful features for directory discovery.
- dictionary-based directory scanning
- hidden file discovery
- recursive scanning capabilities
- customizable wordlists
- detailed scanning reports
These features allow ethical hackers to explore web applications more thoroughly.
Why Dirb Is Important
Developers sometimes leave hidden resources exposed on web servers without realizing the security risks.
Examples include:
- backup directories
- staging environments
- hidden administration panels
- old application versions
Dirb helps identify these hidden resources before attackers discover them.
Dirb is commonly used for:
- web penetration testing
- bug bounty reconnaissance
- hidden directory discovery
- web server security audits
When combined with tools like FFUF, directory discovery becomes even more effective.
15. Hashcat
Passwords remain a major component of digital security, yet many systems still rely on weak or poorly protected credentials.
Hashcat is one of the most advanced password recovery tools used by ethical hackers to test password strength.
It is widely recognized as one of the fastest password cracking tools available.
Key Features
Hashcat offers powerful capabilities for password recovery.
- GPU-accelerated password cracking
- support for hundreds of hash algorithms
- multiple attack modes
- distributed password cracking
- custom rule-based password generation
Because it uses GPU acceleration, Hashcat can perform billions of password guesses per second.
Attack Techniques Supported
Hashcat supports several password attack techniques.
- Dictionary attacks – Uses wordlists containing common passwords.
- Brute-force attacks – Attempts every possible password combination.
- Hybrid attacks – Combines dictionary words with brute-force methods.
- Rule-based attacks – Applies transformation rules to generate new password variations.
Why Ethical Hackers Use Hashcat
During penetration tests, security professionals often obtain password hashes from compromised systems.
Hashcat helps determine how resistant those passwords are to cracking attempts.
If passwords are cracked quickly, it indicates that the organization needs stronger password policies.
Its speed and flexibility make it one of the most powerful password testing tools available today.
FAQs – Best Ethical Hacking Tools
What are ethical hacking tools?
Ethical hacking tools are specialized cybersecurity software used by professionals to identify vulnerabilities in systems, networks, and applications. Security experts use these tools to perform penetration testing, analyze security weaknesses, and strengthen defenses against cyberattacks.
Examples of widely used tools include Nmap, Burp Suite, and Metasploit.
Are ethical hacking tools legal to use?
Yes, ethical hacking tools are legal when used for authorized security testing or educational purposes. Ethical hackers use these tools with permission to identify vulnerabilities and help organizations improve cybersecurity.
Using hacking tools without permission on systems you do not own is illegal and can result in serious legal consequences.
What are best ethical hacking tools for beginners?
Beginners should start with tools that are widely used and relatively easy to learn.
Some beginner-friendly tools include:
- Nmap for network scanning
- Wireshark for analyzing network traffic
- OWASP ZAP for web application testing
Learning these tools provides a strong foundation in cybersecurity and penetration testing.
What operating system do ethical hackers use?
Most ethical hackers use Kali Linux, a specialized operating system designed for cybersecurity professionals.
Kali Linux includes hundreds of penetration testing tools that allow ethical hackers to perform vulnerability scanning, password auditing, wireless security testing, and web application security assessments.
What tools do professional penetration testers use?
Professional penetration testers typically use a combination of tools depending on the testing objective.
Common tools used by cybersecurity professionals include:
- Nmap for network discovery
- Burp Suite for web application testing
- Metasploit for vulnerability exploitation
- Hashcat for password auditing
These tools help identify and exploit vulnerabilities in controlled testing environments.
How long does it take to learn best ethical hacking tools?
The time required to learn best ethical hacking tools depends on the individual’s dedication and practice. Beginners can learn the basics within a few months, but mastering penetration testing tools and cybersecurity techniques typically requires consistent practice over several years.
Hands-on practice using hacking labs and cybersecurity training platforms significantly accelerates the learning process.
Can ethical hackers earn money using these tools?
Yes, ethical hackers can earn money using cybersecurity tools by working as penetration testers, security consultants, or bug bounty hunters.
Many organizations reward security researchers for responsibly reporting vulnerabilities discovered using ethical hacking tools.
What skills are required to use best ethical hacking tools effectively?
To use best ethical hacking tools effectively, professionals should understand several core concepts including:
- networking fundamentals
- operating systems like Linux
- web application security
- programming and scripting
- cybersecurity principles
Combining these skills with best ethical hacking tools enables professionals to perform effective penetration testing.
Do ethical hackers use automated tools?
Yes, ethical hackers often use automated tools to speed up vulnerability detection. Tools like OWASP ZAP and Nikto can automatically scan systems and web applications for common vulnerabilities.
However, manual testing is still required to identify complex security flaws.
Which ethical hacking tools are most powerful in 2026?
Some of the most powerful and best ethical hacking tools used by cybersecurity professionals in 2026 include:
- Nmap
- Metasploit
- Burp Suite
- Hashcat
- Maltego
These tools are widely used for vulnerability discovery, exploitation, and security analysis.
Key Takeaways
Learning best ethical hacking tools is essential for building strong cybersecurity skills. At SecurityElites, we share deep cybersecurity guides and penetration testing tutorials used by professionals.
The tools listed in this guide are widely used by penetration testers and security professionals worldwide. We have also published comprehensive 300 Ethical Hacking Tools List on securityelites, feel free to go through same.
By mastering these best ethical hacking tools, you can identify vulnerabilities, strengthen security systems, and build a successful cybersecurity career.