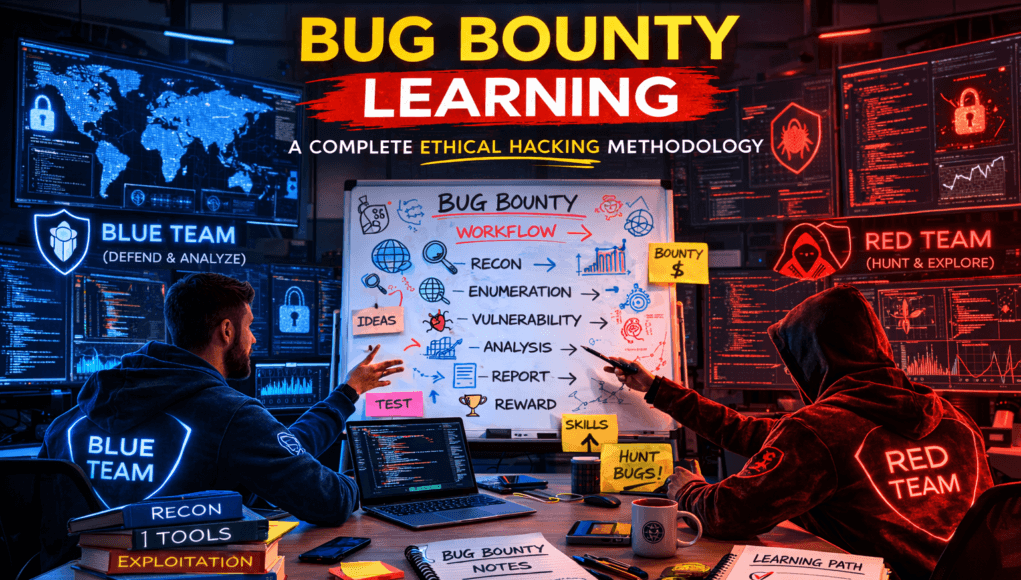
Bug Bounty Hunting Methodology: Complete Beginner to Professional Ethical Hacker Workflow Guide
Introduction to Bug Bounty Hunting Methodology (Real Hacker Perspective)
The Bug Bounty Hunting Methodology is the foundation behind every successful ethical hacker, penetration tester, and professional security researcher.
After more than two decades working in enterprise penetration testing, incident response investigations, and mentoring beginners entering cybersecurity, I have noticed one repeating pattern:
Beginners fail in bug bounty programs not because hacking is difficult — but because they lack a structured methodology.
Most new learners install Kali Linux, run automated scanners, and expect vulnerabilities instantly. When results don’t appear, motivation drops quickly.
However, professional bug bounty hunters operate differently.
They follow a systematic process involving:
- Attack surface mapping
- Reconnaissance
- Vulnerability assessment
- Exploitation workflow validation
- Responsible disclosure
Modern organizations operate thousands of exposed digital assets including APIs, staging servers, cloud platforms, and mobile backends. Each system increases organizational security posture risk if improperly configured.
The purpose of this guide is to teach the real-world Bug Bounty Hunting Methodology used during live penetration tests and red team operations.
You are not learning tools today.
You are learning attacker thinking.
✅ Mentor Note — Pause Here
Tools find data.
Methodology finds vulnerabilities.
Table of Contents
- Why Bug Bounty Hunting Matters
- Beginner Concepts Explained
- Professional Bug Bounty Workflow
- Practical Bug Bounty Recon Tutorial
- Real-World Bug Discovery Scenario
- Professional Tools Explained
- Beginner Mistakes
- Pro Tips From 20 Years Experience
- Defensive & Ethical Perspective
- Implementation Checklist
- Career Insight
- Quick Recap
- FAQs
Why Bug Bounty Hunting Methodology Matters in Cybersecurity
Cyber attacks rarely begin with exploitation.
They begin with visibility.
During a financial-sector incident response engagement, attackers gained internal access simply by discovering an exposed development server through reconnaissance — no malware involved.
This perfectly represents modern cyber attacks.
Organizations continuously expand their attack surface, often faster than security teams can monitor. Bug bounty programs allow ethical hackers to perform ongoing external vulnerability assessment activities.
Bug bounty hunters simulate real attackers by identifying:
- Forgotten assets
- Misconfigured services
- Weak authentication logic
- Data exposure risks
Unlike certification labs, bug bounty hunting exposes researchers to unpredictable environments.
This develops real skills such as:
- Threat intelligence analysis
- Application logic testing
- Defensive security understanding
Companies reward researchers who demonstrate structured methodology rather than automated findings.
Note — Pause Here
Attackers succeed because they observe systems longer than defenders expect.
Beginner Concepts Behind Bug Bounty Hunting Methodology
Before execution, beginners must understand core terminology used throughout ethical hacking workflows.
Reconnaissance
Reconnaissance means gathering publicly accessible information about a target.
Example discoveries:
api.company.com
dev.company.com
backup.company.com
Development environments frequently contain weaker protections.
Enumeration
Enumeration extracts technical intelligence after discovery.
Analogy:
Recon finds a building.
Enumeration checks doors and security locks.
Digitally this reveals:
- Open ports
- Running services
- Technologies used
Vulnerability Assessment
A vulnerability assessment identifies weaknesses impacting confidentiality, integrity, or availability.
Examples include:
- Cross-Site Scripting (XSS)
- IDOR vulnerabilities
- Security misconfigurations
- Information disclosure
Exploitation Workflow
Professionals validate impact logically rather than launching random payloads.
Mentor Note — Pause Here
Beginners attack systems.
Experts understand systems first.
Professional Bug Bounty Hunting Methodology Workflow
A mature bug bounty workflow follows structured investigation phases:
Target Selection
↓
Scope Verification
↓
Reconnaissance
↓
Attack Surface Mapping
↓
Service Enumeration
↓
Technology Fingerprinting
↓
Vulnerability Testing
↓
Impact Validation
↓
Responsible Disclosure
During enterprise penetration testing engagements, nearly 70% of effort focuses on reconnaissance.
Why?
Because vulnerabilities hide in forgotten infrastructure.
Real world scenario — Enterprise Pentest Finding
During a corporate audit, automated scanners showed zero issues.
Manual recon revealed:
legacy-admin.company.com
Outdated authentication allowed privilege escalation.
Automation failed.
Methodology succeeded.
✅ Hands-On Practical : Bug Bounty Recon Methodology Lab
⚠️ Practice only on authorized targets such as programs listed on
the OWASP Top 10 vulnerability awareness platform.
Lab Environment Setup
Install:
- Kali Linux VM
- Minimum 8GB RAM
- NAT Network Adapter
NAT prevents accidental exposure of internal devices.
Tools Installation
Update system:
sudo apt update && sudo apt upgrade
Install tools:
subfinder
httpx
amass
nmap
Step 1 — Scope Analysis
Goal:
Understand allowed testing assets.
Example:
*.example.com
Testing outside scope may result in permanent program bans.
Mentor Note — Pause Here
Professional ethical hackers respect scope stricter than attackers.
Step 2 — Subdomain Enumeration
Command:
subfinder -d example.com -o subs.txt
Flags:
-ddomain-ooutput file
Technically, the tool queries certificate transparency logs and OSINT databases.
Expected output:
dev.example.com
api.example.com
Attacker Thinking:
Development systems often lack monitoring.
Step 3 — Live Host Discovery
Command:
httpx -l subs.txt -o live.txt
Filters inactive hosts.
Output example:
https://dev.example.com
Attackers reduce noise before testing.
Step 4 — Port Enumeration
Command:
nmap -sC -sV dev.example.com
Flags explanation:
-sCdefault scripts-sVversion detection
Expected result:
8080/tcp open http-proxy
Non-standard ports frequently expose admin dashboards.
Step 5 — Manual Investigation
Visit:
http://dev.example.com:8080
Possible discoveries:
- Admin panels
- Debug consoles
- Test dashboards
Enterprise Reality Insight
Cloud migrations frequently expose internal staging environments publicly.
SOC teams usually detect exploitation attempts — not discovery phases.
Bug bounty hunters operate earlier.
Troubleshooting
| Issue | Fix |
|---|---|
| No domains found | Use Amass |
| Scan slow | Add -T4 |
| Host blocked | Rotate IP |
Note — Pause Here
Real bugs start from curiosity — not aggression.
Real-World Bug Bounty Discovery Scenario
A researcher discovered an exposed beta API revealing user identifiers.
No injection required.
Impact:
Account takeover possibility.
Reward:
$10,000 bounty.
Lesson:
Application logic flaws outperform complex exploitation.
Professional Bug Bounty Tools Explained
Subfinder
Passive reconnaissance minimizing detection.
Amass
Deep attack surface intelligence mapping.
HTTPX
Filters live web assets efficiently.
Nmap
Industry-standard service enumeration tool used worldwide.
Professionals chain tools strategically instead of relying on automation alone.
Beginner Mistakes in Bug Bounty Hunting 🚨
Common failures observed during mentorship:
- Blind scanner usage
- Ignoring attack surface mapping
- Submitting low-impact findings
- Missing proof-of-concept
- Copy-paste payload testing
Bug bounty programs reward demonstrated risk impact.
Pro Tips From 20 Years of Bug Bounty & Pentesting Experience 🔥
- Hunt logic flaws instead of injections initially
- Study disclosed HackerOne reports daily
- Focus on one vulnerability weekly
- Explore application workflows manually
- Investigate developer assumptions
Attackers exploit human mistakes.
Defensive & Ethical Security Perspective
Bug bounty hunting strengthens defensive cybersecurity by identifying unknown exposures before attackers exploit them.
Responsible disclosure improves:
- Detection engineering
- Incident response readiness
- Organizational security posture
Ethics defines professional credibility.
Practical Bug Bounty Hunting Implementation Checklist
✅ Verify scope
✅ Perform reconnaissance
✅ Map attack surface
✅ Enumerate services
✅ Analyze application logic
✅ Validate vulnerability impact
✅ Submit professional report
Consistency produces results.
Career Insight — Turning Bug Bounty Skills Into Cybersecurity Jobs
Bug bounty methodology directly prepares professionals for:
- Penetration Testing
- SOC Operations
- Threat Hunting
- Red Team Engagements
Hiring managers increasingly value demonstrated vulnerability research experience.
Quick Recap — Bug Bounty Hunting Methodology
Successful workflow:
Recon → Enumeration → Analysis → Vulnerability Testing → Impact Validation → Responsible Disclosure.
Tools assist execution.
Thinking discovers vulnerabilities.
Frequently Asked Questions (Bug Bounty Hunting Methodology)
1. What is Bug Bounty Hunting Methodology?
Bug Bounty Hunting Methodology refers to the structured process ethical hackers follow to discover vulnerabilities safely through reconnaissance, enumeration, and exploitation validation.
2. How do beginners start bug bounty hunting?
Beginners should focus on reconnaissance and attack surface mapping before attempting exploitation.
3. Which vulnerability types are beginner friendly?
IDOR, information disclosure, and misconfiguration vulnerabilities provide higher success rates.
4. Is automation enough?
Automation helps discovery but manual logic testing finds valuable vulnerabilities.
5. How long before earning first bounty?
Most consistent learners achieve first reward within 3–6 months.
6. Is bug bounty hunting legal?
Yes, when testing authorized program scopes responsibly.
7. Can bug bounty become a career?
Yes. Many penetration testers begin as bug bounty researchers.