🔐
Authorised use only. Every tool on this page is for use on systems you own or have explicit written authorisation to test. Use your
home lab,
TryHackMe, or
Hack The Box.
⚔
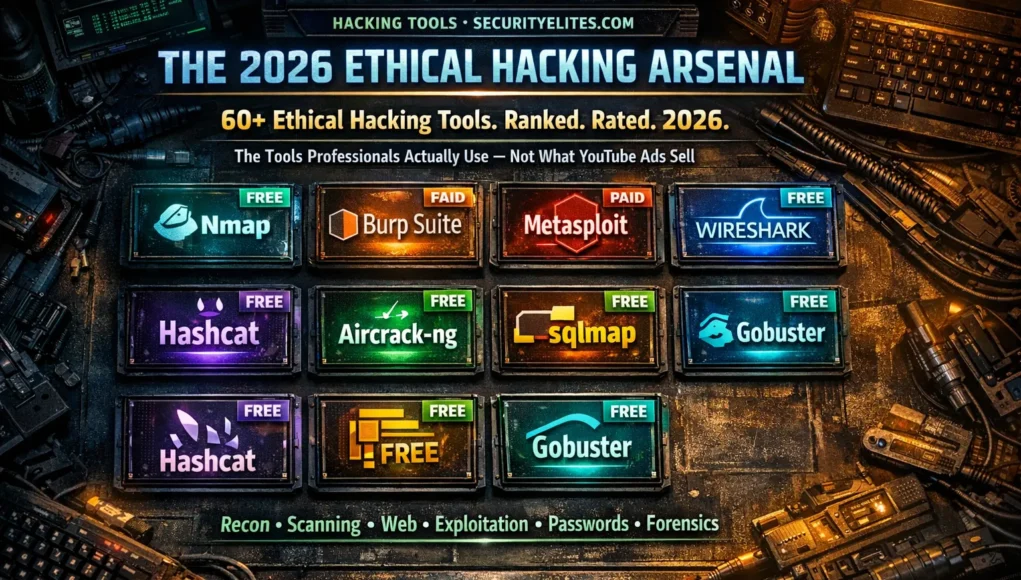
There are over 600 tools pre-installed on Kali Linux. Search “ethical hacking tools list” and you’ll find articles listing 100 of them with one-sentence descriptions and no opinion on any of them. That list is useless. What matters is which tools professionals actually open on every engagement, which ones are worth learning deeply versus skimming, and which expensive commercial tools have better free alternatives.
This is the honest version — 60+ tools across 10 categories, each rated by how often they appear in real professional work, labelled free or paid, and linked to deep-dive tutorials where SecurityElites.com has built them. No affiliate relationships. No sponsored placements. Just the tools that actually matter.
How to Read This List
S Used in nearly every engagement — master these first
A Commonly used — learn after S-tier
B Situational — valuable in specific contexts
FREE Completely free to use
FREE+ Free tier + paid upgrade available
PAID Commercial / requires licence
🔭 Reconnaissance Tools
Information gathering before any active testing. Passive recon leaves no trace on the target. Active recon involves direct interaction with the target’s systems.
📡 Scanning & Enumeration Tools
Active probing of discovered services to enumerate users, versions, paths, and vulnerabilities.
Gb
Gobuster
SFREE
Fast directory and file brute-forcing using wordlists. Discovers hidden paths, admin panels, API endpoints, backup files, and config files that are not publicly linked. Essential on every web-facing target.
gobuster dir -u https://target.com -w /usr/share/wordlists/dirb/common.txt
ff
ffuf
SFREE
Extremely fast web fuzzer. Fuzzes URLs, headers, POST bodies, or any part of an HTTP request. Supports filters for response size, word count, and status code. Preferred over Gobuster for complex fuzzing scenarios requiring header injection or POST body fuzzing.
ffuf -u https://target.com/FUZZ -w wordlist.txt -mc 200,301
Nk
Nikto
AFREE
| Pre-installed Kali
Web server scanner checking for 6,700+ potentially dangerous files, outdated server versions, and common misconfigurations. Noisy (easily detected) but provides a comprehensive quick surface scan in minutes.
e4
enum4linux
AFREE
Linux alternative to enum.exe for enumerating Windows / Samba shares, users, groups, password policies, and OS info from SMB. Essential on any target with port 139 or 445 open.
enum4linux -a 192.168.1.10
🕷️ Web Application Testing Tools
The most active area of both penetration testing and bug bounty. Web apps are the primary attack surface in most modern engagements.
securityelites.comWEB APPLICATION TESTING TOOLS — PROFESSIONAL TIER RANKING 2026
S
Burp Suite
The undisputed #1 web security testing platform. Proxy + Repeater + Intruder + Scanner. Used in 95%+ of web application penetration tests globally. Nothing else comes close for manual testing depth.
COMMUNITY FREEPRO $449/YR
A
SQLmap
SQL injection automation. Detects and exploits SQLi. Essential when manual SQLi testing is confirmed — run for extraction.
OWASP ZAP
Free Burp alternative. Great automated scanner for quick surface coverage. Less powerful than Burp Pro for manual testing.
WPScan
WordPress-specific vulnerability scanner. Enumerates plugins, themes, users. Essential if target runs WordPress.
B
Nuclei
Template-based vulnerability scanner — mass scanning with community templates.
Dalfox
Fast XSS scanner. Automates XSS payload testing across parameters.
httpx
Fast HTTP probing — pipe subdomain lists to find live services.
Web Application Testing Tools — Professional Tier Ranking 2026. Burp Suite is the undisputed S-Tier — there is no substitute for manual web testing. SQLmap, ZAP, and WPScan form the A-Tier for automation. Nuclei and Dalfox are B-Tier specialised scanners. Start with Burp Suite Community and build your workflow around it.
💡 Deep Dive: Burp Suite Day 5 — Complete Tutorial covers every Burp tool in professional depth: Proxy, Repeater, Intruder (all 4 types), Decoder, Comparer, Scanner, and PortSwigger lab walkthroughs.
⚡ Exploitation Frameworks
Used after vulnerability identification to demonstrate real impact. All for authorised penetration testing only — never on systems without explicit scope authorisation.
Msf
Metasploit Framework
SFREE+
| Kali Linux Day 3
The world’s most widely used exploitation framework. Search for exploit modules, set targets and payloads, deliver exploits, manage Meterpreter sessions, and perform post-exploitation. Required knowledge for OSCP. Metasploit Community (free) and Pro ($15,000/yr commercial) versions available.
Nc
Netcat (nc)
SFREE
| Kali Linux Day 2
The “Swiss Army knife” of networking. Sets up listeners for reverse shells, transfers files between hosts, performs banner grabbing, and creates basic network connections. Fundamental to almost every post-exploitation workflow.
nc -lvnp 4444 # Start reverse shell listener
SET
Social Engineering Toolkit (SET)
BFREE
Framework for social engineering attack vectors — phishing pages, credential harvesting, spear phishing emails. Used in authorised red team engagements testing the human element of security. Requires explicit authorisation covering social engineering tactics.
🔑 Password Attack Tools
Offline hash cracking (always legal on hashes you captured in-scope) and online brute force (requires explicit authorisation — know rate limits and account lockout policies).
Hc
Hashcat
SFREE
GPU-accelerated password hash cracker. World’s fastest. Supports every major hash format (MD5, NTLM, bcrypt, SHA-256, WPA2). Multiple attack modes: dictionary, brute force, combinator, rule-based, mask. The professional choice for offline hash cracking.
hashcat -m 1000 hashes.txt rockyou.txt # NTLM dictionary attack
JtR
John the Ripper
AFREE
CPU-based password cracker with excellent auto-detection of hash formats. Slower than Hashcat on GPU but simpler syntax for beginners. The unshadow utility combines /etc/passwd and /etc/shadow for cracking Linux credentials.
Hyd
Hydra
AFREE
Online brute force tool supporting SSH, FTP, HTTP, RDP, SMB, MySQL, and 50+ protocols. Use only on in-scope systems with explicit brute force permission — check for account lockout policies before running. Always use conservatively.
hydra -l admin -P rockyou.txt 192.168.1.10 ssh
📶 Wireless Security Tools
For testing wireless networks you own or have explicit written authorisation to assess. Requires a wireless adapter supporting monitor mode (check compatibility before purchasing).
Ac
Aircrack-ng Suite
SFREE
The complete WPA2 assessment toolkit: airmon-ng (monitor mode), airodump-ng (capture handshakes), aireplay-ng (deauth clients), aircrack-ng (crack captured handshakes). The standard for WiFi penetration testing in authorised engagements.
Ws
Wireshark
AFREE
Network protocol analyser and packet capture tool. Captures and deeply analyses network traffic in real time. Essential for understanding protocols, identifying plaintext credentials, and analysing suspicious traffic patterns on authorised network engagements.
🌐 Network Analysis Tools
Tcpd
tcpdump
AFREE
Command-line packet capture. Lightweight, fast, scriptable. Use when Wireshark GUI is unavailable (e.g. on a server). Captures to .pcap files for later analysis in Wireshark.
Resp
Responder
BFREE
LLMNR, NBT-NS and MDNS poisoner. Captures NTLMv2 hashes by responding to broadcast name resolution requests on internal networks. Used in authorised internal network assessments. A core Active Directory attack tool.
🔍 Forensics & Reverse Engineering
Gh
Ghidra
AFREE
| NSA open source
Professional software reverse engineering framework developed and open-sourced by the NSA. Disassembles, decompiles, and analyses binaries. The free alternative to IDA Pro ($3,000+). Essential for malware analysis and CTF reverse engineering challenges.
Bw
Binwalk
BFREE
Firmware analysis and extraction tool. Identifies and extracts embedded file systems, compressed data, and code from binary firmware images. Essential for IoT security assessments and embedded system testing.
Vol
Volatility
BFREE
Memory forensics framework. Analyses RAM dumps to extract running processes, network connections, encryption keys, credentials, and artefacts of malicious activity. Used by digital forensics investigators and incident responders.
🔓 Post-Exploitation Tools
Used after initial access to demonstrate full compromise potential in authorised penetration tests. These tools show what a real attacker could achieve after a foothold.
LP
LinPEAS / WinPEAS
SFREE
Privilege escalation enumeration scripts. Automatically identifies misconfigurations, SUID binaries, writable paths, cron jobs, and hundreds of other privilege escalation vectors on Linux and Windows. Replaces hours of manual enumeration.
curl -L https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh | bash
BH
BloodHound
AFREE
Active Directory attack path visualisation. Maps relationships between users, groups, computers, and domain trusts to identify paths from any user to Domain Admin. Essential for Active Directory penetration testing. Paired with SharpHound or AzureHound for data collection.
Imp
Impacket
AFREE
Python library for working with network protocols — especially Active Directory attacks. Tools like secretsdump (extract hashes), psexec (remote code execution), and GetNPUsers (AS-REP Roasting) are all Impacket-based. Core to Windows/AD penetration testing.
📄 Reporting & Documentation Tools
Obs
Obsidian
SFREE
Markdown-based personal knowledge base. The most popular note-taking tool among professional penetration testers for organising engagement notes, building methodology templates, and maintaining a personal knowledge base. Offline-first, privacy-preserving.
Pwf
Pwndoc / Ghostwriter
BFREE
Professional penetration test report generators. Structure findings into formatted reports with severity charts, executive summaries, and technical appendices. Used by security consultancies to produce client-ready reports efficiently.
The Beginner’s Priority Stack — Learn In This Order
securityelites.comBEGINNER TOOL LEARNING ORDER — SECURITYELITES.COM RECOMMENDED PATH
Nmap · Netcat · Linux Bash
Foundation tools. Everything else builds on these. Do not advance until you can run an Nmap baseline scan from memory and set up a Netcat listener without looking up the flags.
Burp Suite · Gobuster / ffuf
Web application testing core. Configure Burp + Firefox + FoxyProxy. Learn Proxy, Repeater, Intruder, Decoder. Combine with ffuf for comprehensive web recon.
Metasploit · Hashcat · John
Exploitation and credential testing. Metasploit’s msfconsole core workflow. Hashcat dictionary and rule attacks against common hash formats. Lab: Metasploitable2 full compromise.
Subfinder · Hydra · Aircrack-ng
Extended toolkit. Subdomain enumeration for bug bounty. Online brute force on authorised lab systems. Wireless assessment on your own router for WiFi security validation.
BloodHound · Impacket · LinPEAS · Ghidra
Advanced and specialised tools. Active Directory attack mapping. Post-exploitation enumeration automation. Reverse engineering for malware and firmware analysis. OSCP preparation territory.
Ethical Hacking Tool Learning Order — Five monthly phases building from network fundamentals to advanced exploitation. Each phase’s tools are prerequisites for the next. The 180-Day Kali Linux Course at SecurityElites.com follows exactly this progression — one tool per day, with all tools in this visual covered in depth.
Every Tool on This List Has a Full Tutorial
180 Tools. 180 Days. Every Command Explained.
All Free. No Registration.
The 180-Day Kali Linux Course covers one tool per day — starting with Nmap on Day 1. Every tool on this page that belongs to Kali Linux has a dedicated full tutorial. Every command verified. Every flag explained. All free.
Frequently Asked Questions — Ethical Hacking Tools List
What are the most important ethical hacking tools for beginners?
Nmap, Burp Suite Community, Netcat, Gobuster/ffuf, and John the Ripper / Hashcat. All free. All pre-installed on Kali Linux. Master these five deeply before expanding to others. The 180-Day Kali Linux Course covers each in complete depth.
Do ethical hackers use all the tools in Kali Linux?
No — professionals use a core set deeply rather than all 600+ tools superficially. The S-Tier tools (Nmap, Burp Suite, Metasploit, LinPEAS, Hashcat) appear in most engagements. Specialised tools are added based on scope.
Is Burp Suite free for ethical hacking?
Burp Suite Community Edition is completely free — Proxy, Repeater, Decoder, Comparer, limited Intruder, and basic Scanner. Burp Suite Professional ($449/year) adds the full automated scanner and unlimited Intruder. Community is sufficient for most learning and bug bounty work.
What ethical hacking tools are included in Kali Linux?
600+ tools including Nmap, Burp Suite, Metasploit, SQLmap, Nikto, Gobuster, Hashcat, John the Ripper, Hydra, Aircrack-ng, Wireshark, Ghidra, Volatility, Binwalk, theHarvester, enum4linux, Responder, and hundreds more across all security testing categories.
What is the best ethical hacking tool for web applications?
Burp Suite — the industry standard for web application penetration testing and bug bounty hunting globally. OWASP ZAP is a strong free alternative for automated scanning. The 60-Day Bug Bounty Course covers Burp Suite in complete depth.
📚 Further Reading and Resources
ME
Mr Elite
Founder, SecurityElites.com | Penetration Tester | Tool Educator
The most common mistake I see in beginners is tool-collecting — downloading everything, running each one once, and moving to the next. The professionals I know who are genuinely skilled with tools are skilled because they ran Nmap on ten thousand practice targets, not because they have ten Nmap alternatives installed. This list is not a shopping list. It is a priority order. Pick the S-Tier tools first. Go deep. Everything else becomes easier once your fundamentals are solid.