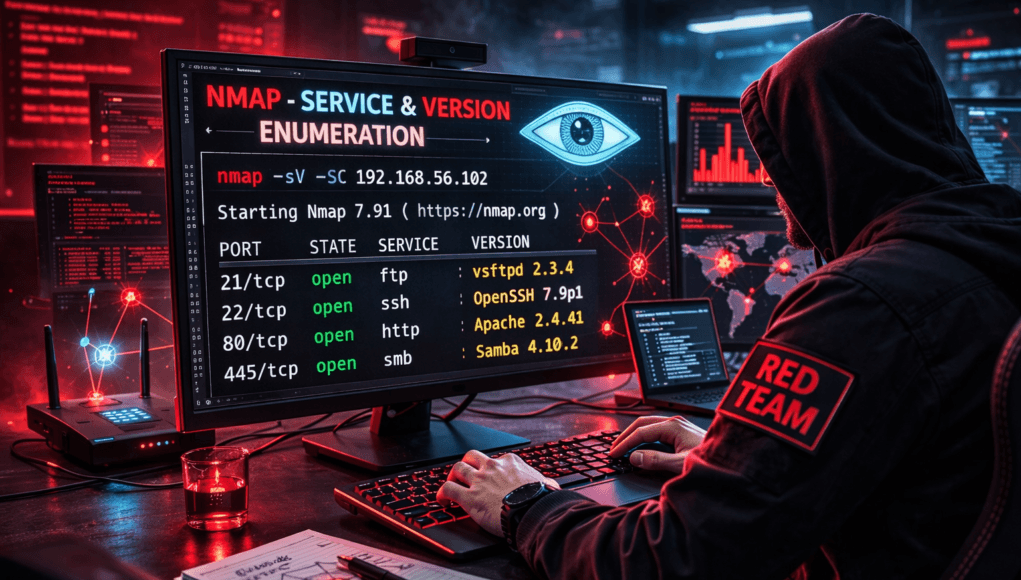
Network Scanning Tutorial Using Nmap — Day 4
Service & Version Enumeration Like Real Attackers
Excellent! Now we enter the stage where real penetration testers separate from tool users.
Up to now:
✅ Day 1 → Understanding scanning
✅ Day 2 → Finding live hosts
✅ Day 3 → Discovering open ports
Today we answer the question professionals actually care about:
What exactly is running behind those open ports?
Because attackers don’t exploit ports.
They exploit services and versions.
Let me share something from real incident.
A company once asked:
“How did attackers know exactly which vulnerability to exploit?”
The answer shocked management.
Attackers didn’t guess.
They enumerated services.
Within minutes, attackers identified:
- Apache version
- OpenSSH build
- outdated SMB service
Then matched them with known vulnerabilities.
Compromise followed.
No magic.
Just intelligence.
Today you learn one of the most powerful cybersecurity skills:
✅ Service Enumeration
This is where reconnaissance becomes targeted attack planning.
Note —
Open port = Door
Service enumeration = Understanding who lives behind the door.
Without enumeration, exploitation becomes blind guessing.
Why Service Enumeration Matters
From Day 3 you discovered:
22/tcp open ssh
80/tcp open http
But this information alone is incomplete.
Important questions remain:
- Which SSH version?
- Which web server?
- Is it outdated?
- Known vulnerabilities?
Attackers require software intelligence.
Real Pentest Observation
During enterprise testing:
Port 443 open everywhere.
Normal.
But version detection revealed:
OpenSSL 1.0.1
Vulnerable to Heartbleed.
Single enumeration step exposed critical risk.
Defensive Insight
Enumeration attempts often trigger:
- IDS alerts
- banner monitoring
- anomaly detection
Because defenders know:
Enumeration precedes exploitation.
What is Enumeration?
Enumeration means:
Extracting detailed system information from exposed services.
It includes:
- software name
- version number
- protocol behavior
- configuration clues
Analogy
Imagine calling customer support.
Basic scan:
Someone answered.
Enumeration:
You learned department, employee name, system used.
More intelligence → higher success.
Beginner Mistake
Students think vulnerability scanners discover everything.
Reality:
Professional hackers manually enumerate first.
Automation comes later.
Note —
Enumeration is intelligence gathering — not attacking.
Precision reduces noise.
Professional Enumeration Workflow
Real-world methodology:
Step 1 — Identify Open Ports
(Day 3 completed)
Step 2 — Detect Services
Understand application type.
Step 3 — Detect Versions
Identify software release.
Step 4 — Match Vulnerabilities
Threat intelligence phase.
Enterprise environments may:
- hide banners
- modify responses
- deploy deception systems
Enumeration must adapt.
✅ HANDS-ON PRACTICAL TUTORIAL (Live Lab)
This section mirrors real penetration testing workflow.
Lab Setup
Continue previous environment:
✅ Kali Linux
✅ Metasploitable2
✅ Same subnet
Target:
192.168.56.102
Step 1 — Service Detection Scan
Goal:
Identify running services.
Command:
nmap -sV 192.168.56.102
Flag Explanation
-sV→ Version detection
Nmap interacts with services using probes.
Technical Process
Nmap sends protocol-specific requests:
- HTTP request
- SSH handshake
- FTP query
Service responds with banner information.
Expected Output
21/tcp open ftp vsftpd 2.3.4
22/tcp open ssh OpenSSH 4.7
80/tcp open http Apache 2.2.8
Beginner View
You see software names.
Attacker View
Immediate thoughts:
- vsftpd 2.3.4 → known backdoor
- outdated Apache → exploit candidate
Attack planning begins.
Note —
Enumeration transforms scanning into vulnerability intelligence.
Step 2 — Aggressive Service Detection
Command:
nmap -sV --version-intensity 9 192.168.56.102
Meaning
Higher intensity = deeper probing.
Useful when services hide identity.
Enterprise Reality
Some systems throttle aggressive probes.
Balance accuracy vs stealth.
Step 3 — Default Script + Version Detection
Professional favorite:
nmap -sC -sV 192.168.56.102
What Happens?
Runs:
✅ default NSE scripts
✅ service detection
✅ configuration checks
Automatically gathers:
- SSL info
- HTTP titles
- login methods
Micro-Story
Bug bounty target revealed:
Apache Tomcat Manager
via default scripts.
Weak credentials → admin access.
Enumeration alone earned bounty.
Note —
Many real compromises occur BEFORE exploitation tools appear.
Step 4 — Target Specific Ports
Efficient enumeration:
nmap -sV -p 22,80,21 192.168.56.102
Professional targeting reduces detection.
Step 5 — Save Enumeration Results
Always document.
nmap -sV -oN services.txt targetIP
Pentesters rely heavily on documentation.
Troubleshooting Layer
Version Not Detected?
Increase intensity:
--version-all
Scan Too Slow?
Reduce ports scanned.
Incorrect Detection?
Firewalls or proxies may modify banners.
Manual verification required later.
Note —
Enumeration errors happen.
Professionals validate findings.
Attacker Thinking Simulation
At this stage attacker asks:
- Which service outdated?
- Public exploit available?
- Authentication required?
- Remote execution possible?
Enumeration drives exploitation decisions.
Real-World Scenario
Internal audit revealed outdated SMB version.
Admins believed patch applied.
Enumeration proved otherwise.
Led to privilege escalation simulation.
Enumeration prevented future breach.
Professional Tools
Enumeration integrates with:
- Searchsploit
- Metasploit
- Nessus
- CVE databases
- Threat intelligence feeds
Nmap becomes intelligence collector.
Beginner Mistakes 🚨
❌ Skipping version detection
❌ Trusting automated scanners blindly
❌ Not saving results
❌ Over-aggressive scanning
❌ Ignoring service banners
Pro Tips From 20 Years Experience 🔥
- Enumerate slowly.
- Verify manually.
- Compare versions with CVEs.
- Prioritize internet-facing services.
- Document everything.
Elite hackers investigate deeply.
Defensive & Ethical Perspective
Blue Teams reduce enumeration risk via:
- banner hiding
- service hardening
- rate limiting
- intrusion detection
Security posture improves when enumeration exposure minimized.
Practical Implementation Checklist
✅ Services identified
✅ Versions detected
✅ Default scripts executed
✅ Results saved
✅ Intelligence interpreted
Career Insight
Enumeration expertise enables:
- Vulnerability Analyst
- Penetration Tester
- Red Team Operator
- Security Auditor
- Threat Researcher
Most junior pentesters fail here.
Professionals excel here.
Quick Recap
Today you learned:
✅ Service detection
✅ Version enumeration
✅ Banner analysis
✅ Intelligence extraction
✅ Attack preparation logic
Tomorrow…
We fingerprint entire systems.
Operating system detection begins.
FAQs
What does -sV do?
Detects service versions running on open ports.
Is enumeration noisy?
More than discovery scans, yes.
Can services hide versions?
Yes using banner obfuscation.
Is version detection accurate?
Usually high but not perfect.
Why combine -sC and -sV?
Efficient intelligence gathering.
Does enumeration exploit systems?
No. It gathers information only.
Do defenders monitor enumeration?
Yes — strongly monitored phase.