Let me start this the way I usually start recon training sessions.
Most beginners think hacking begins with exploits.
It doesn’t.
It begins with reconnaissance — specifically understanding the difference between Passive vs Active Reconnaissance.
And trust me… this single distinction separates noisy amateurs from disciplined operators.
I’ve seen junior testers burn entire engagements in the first hour — simply because they skipped passive recon and jumped straight into scanning.
So let’s slow this down and break it properly.
What is Passive vs Active Reconnaissance?
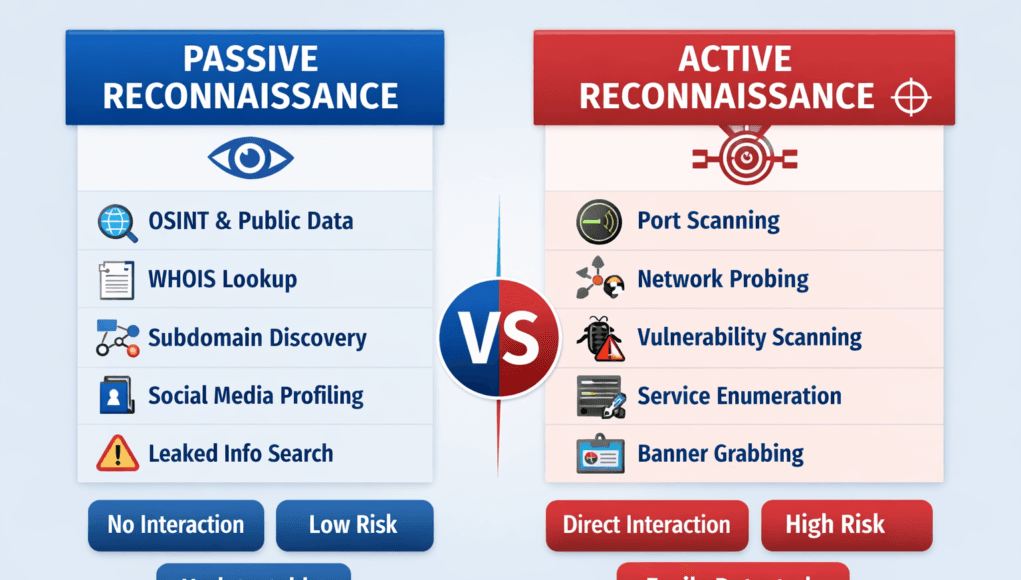
Passive vs Active Reconnaissance refers to two different intelligence-gathering approaches used in ethical hacking and penetration testing.
- Passive Reconnaissance → Collecting data without interacting with the target
- Active Reconnaissance → Directly probing target systems
Simple definition for snippet ranking:
Passive reconnaissance gathers publicly available intelligence without touching the target, while active reconnaissance directly interacts with systems to identify vulnerabilities.
This distinction impacts:
- Detection risk
- Legal exposure
- Data accuracy
- Engagement strategy
Why Reconnaissance Matters More Than Exploitation
Now here’s where most beginners get confused…
They think recon is just “information gathering.”
In reality, recon is attack surface engineering.
You’re building a blueprint of the target.
In real assessments, what we usually see is:
- 70% time spent on recon
- 20% exploitation
- 10% privilege escalation
Because the better your reconnaissance, the easier exploitation becomes.
Passive Reconnaissance Explained
Passive reconnaissance is silent.
No packets sent.
No firewall logs triggered.
You’re harvesting digital exhaust — the data organizations leak unintentionally.
Passive Reconnaissance Methods
1. Domain Intelligence Collection
We start with WHOIS and registrar data.
Key findings:
- Domain ownership
- Registration history
- Name servers
- Associated domains
This helps map infrastructure relationships.
2. Subdomain Enumeration (Passive)
Using certificate logs and public datasets, we uncover:
- Dev environments
- Staging servers
- Forgotten portals
- Legacy apps
These often lack proper security controls.
3. Employee OSINT Intelligence
Let me break this down in simple terms…
Employees leak infrastructure details daily.
Sources include:
- LinkedIn job roles
- Tech stack mentions
- Conference talks
- Resumes
If an engineer lists “Managing AWS EC2 & Kubernetes clusters,” you already know part of the backend.
4. Public Document Metadata
PDFs, DOCX files, presentations…
They often expose:
- Internal usernames
- Software versions
- File paths
- Email formats
I once extracted an internal server name from a marketing brochure.
Recon goldmine.
Passive Reconnaissance Tools Used by Professionals
- Maltego → Relationship mapping
- Shodan → Internet-facing assets
- theHarvester → Emails & hosts
- Amass (passive mode) → Subdomains
- Recon-ng → OSINT automation
Beginner Mistake Alert 🚨
Using brute-force tools during passive recon.
If your tool sends packets to the target — it’s active.
And yes, defenders will see it.
Active Reconnaissance Explained
Active reconnaissance is where interaction begins.
You’re no longer observing.
You’re testing.
This includes direct engagement with:
- Servers
- Networks
- Applications
- Services
Detection risk increases significantly here.
Active Reconnaissance Methods
1. Network Discovery
We identify live hosts using:
- ICMP requests
- TCP pings
- ARP scans
This defines reachable infrastructure.
2. Port Scanning
One of the most critical phases.
We analyze:
- Open ports
- Closed ports
- Filtered responses
Each state reveals firewall posture.
3. Service Enumeration
After identifying open ports, we fingerprint services:
- Web servers
- Databases
- SSH daemons
- Mail servers
Version detection leads to vulnerability mapping.
4. Banner Grabbing
Servers often disclose software details in banners.
Example:
OpenSSH 7.2p2 Ubuntu
That version alone may link to known CVEs.
Active Reconnaissance Tools
- Nmap → Port scanning
- Wireshark → Packet capture
- Nikto → Web scanning
- OpenVAS → Vulnerability scanning
- Metasploit scanners → Service probing
Passive vs Active Reconnaissance – Key Differences
| Factor | Passive Reconnaissance | Active Reconnaissance |
|---|---|---|
| Interaction | None | Direct |
| Detection Risk | Very Low | High |
| Data Accuracy | Inferred | Confirmed |
| Legal Risk | Low | Requires approval |
| Noise Level | Silent | Detectable |
Real-World Reconnaissance Scenario
Mini story from a fintech red-team engagement.
Passive recon revealed:
- Exposed subdomain
- GitHub API key leak
- Employee discussing Jenkins
Active recon confirmed:
- Jenkins dashboard open
- Default credentials active
- Remote build execution possible
Full internal compromise… without a single exploit.
Recon did all the work.
Reconnaissance Workflow Used in Professional Engagements
Phase 1 – Passive
- Domain mapping
- Subdomain discovery
- OSINT collection
- Breach analysis
- Tech stack profiling
Phase 2 – Light Active
- Host discovery
- Basic port scans
- Surface enumeration
Phase 3 – Deep Active
- Service fingerprinting
- Vulnerability mapping
- Web path discovery
Sequence matters more than tools.
Pro Tip from Field Experience
Never start with vulnerability scanners.
Why?
Because they:
- Generate noise
- Trigger SOC alerts
- Burn stealth advantage
Silent mapping always comes first.
Defensive Perspective – How Blue Teams Detect Recon
Understanding Passive vs Active Reconnaissance helps defenders build detection layers.
Detecting Passive Recon
Harder but possible via:
- Dark web monitoring
- Credential leak tracking
- Brand/domain monitoring
- GitHub surveillance
Detecting Active Recon
Much easier.
Detection sources:
- IDS/IPS alerts
- Firewall logs
- Scan signatures
- Traffic anomalies
Honeypots are especially effective here.
How Organizations Can Defend Against Reconnaissance
Reduce Passive Exposure
- Mask WHOIS data
- Remove document metadata
- Monitor public repos
- Train employees on OSINT risks
Harden Active Attack Surface
- Close unused ports
- Deploy WAFs
- Use EDR/XDR
- Implement rate limiting
Security begins with visibility reduction.
Quick Recap Summary
- Passive recon = Silent intelligence gathering
- Active recon = Direct probing
- Passive reduces detection risk
- Active validates exposure
- Both are essential in ethical hacking
Recon depth determines exploit success.
FAQs
What is Passive Reconnaissance in Ethical Hacking?
Passive reconnaissance is the process of gathering target intelligence from public sources without direct interaction.
What is Active Reconnaissance?
Active reconnaissance involves directly scanning and probing target systems to identify open ports, services, and vulnerabilities.
Is Passive Reconnaissance Legal?
Generally yes, since it uses public data — but always follow engagement scope and legal guidelines.
Which Tools Are Used in Passive Recon?
Common tools include Maltego, Shodan, Amass, and Recon-ng.
Why is Active Recon Riskier?
Because it generates detectable traffic that can trigger security alerts.





[…] work by using specialized search operators that allow security researchers to perform passive reconnaissance and attack surface enumeration without directly attacking a […]
[…] than randomly hacking systems, professional attackers follow a predictable lifecycle involving reconnaissance, attack surface mapping, enumeration, misconfiguration discovery, payload execution, and privilege […]