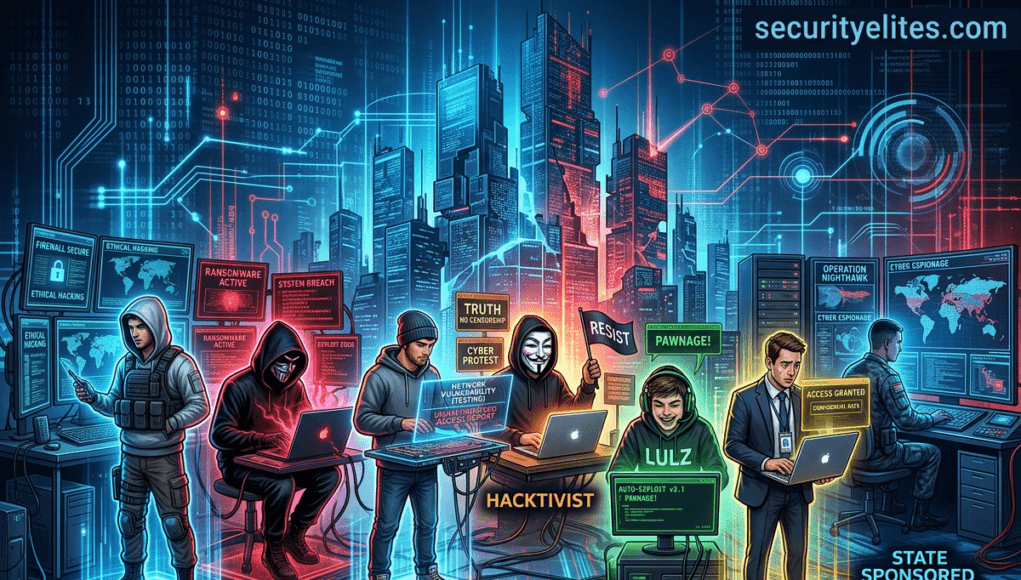
In cybersecurity, hackers are commonly classified as white hat hackers, black hat hackers, grey hat hackers, script kiddies, hacktivists, state-sponsored hackers, and insider hackers. Types of hackers refer to the different categories of individuals who interact with computer systems, networks, and applications in different ways depending on their intent, skills, and authorization.
Some hackers use their knowledge to protect organizations and improve security, while others exploit weaknesses for financial gain, espionage, activism, or sabotage.
Understanding the types of hackers helps cybersecurity professionals predict attacker behavior, strengthen defenses, and design better security systems.
In simple terms, a hacker is someone who knows how computer systems work deeply enough to manipulate them. The difference between the types of hackers lies in their purpose and ethics.
Table of Contents
What is Hacker actually means?
When people hear the word hacker, they often imagine someone wearing a hoodie typing mysterious code in a dark room.
In reality, the concept is more complex.
The term hacker originally referred to someone who understands technology deeply and enjoys experimenting with systems. Over time, cybersecurity professionals began classifying hackers into different groups based on their actions and intentions.
These classifications are known as the types of hackers in cybersecurity.
Understanding the types of hackers is important because organizations face many different threats. Each group behaves differently, uses different tools, and targets different systems.
For example:
- Some hackers try to protect systems
- Some hackers try to steal information
- Others hack for political or ideological reasons
Because motivations differ, cybersecurity teams study types of hackers to anticipate threats and prepare defensive strategies.
Why Do Different Types of Hackers Exist?
There are three main factors that create different hacker categories.
1. Motivation
Different hackers have different motivations such as:
- financial profit
- curiosity
- political activism
- national security
- revenge or sabotage
For example, a criminal hacker may steal banking data, while an ethical hacker might attempt the same attack to identify weaknesses and help fix them.
Another major difference between the types of hackers is permission.
Some hackers operate legally with permission, while others attack systems without authorization.
This difference separates ethical cybersecurity professionals from cybercriminals.
3. Skill Level
Not every hacker has the same level of expertise.
Some hackers build their own tools and discover vulnerabilities. Others simply download scripts created by experts.
This skill gap also creates distinct types of hackers.
Note —
Imagine a computer system is like a locked house.
Hackers are people who try to open the door.
Some hackers open the door to repair the lock.
Some hackers open it to steal valuables.
This difference explains the types of hackers.
Major Types of Hackers in Cybersecurity
Understanding the major types of hackers is a foundational lesson in ethical hacking training.
Below are the most widely recognized hacker categories.
1. White Hat Hackers (Ethical Hackers)
White hat hackers are cybersecurity professionals who legally test computer systems to identify vulnerabilities. Many ethical hackers follow security guidelines published by the OWASP to identify and prevent common web application vulnerabilities.
These professionals are also known as:
- ethical hackers
- penetration testers
- security researchers
Organizations hire white hat hackers to simulate cyberattacks and discover weaknesses before malicious attackers exploit them.
Typical responsibilities include:
- vulnerability assessments
- penetration testing
- security audits
- bug bounty research
- red team operations
A white hat hacker follows strict legal and ethical guidelines while testing systems.
Their goal is improving security, not causing damage.
2. Black Hat Hackers

Black hat hackers are individuals who break into computer systems illegally.
Their activities typically involve cybercrime such as:
- stealing sensitive data
- installing malware
- launching ransomware attacks
- conducting financial fraud
Black hat hackers often exploit security weaknesses in web applications, networks, or user devices.
Their primary motivation is usually financial profit, although some attacks may involve revenge or sabotage.
Among the types of hackers, black hat hackers represent the most serious threat to organizations because they actively seek vulnerabilities for exploitation.
3. Grey Hat Hackers
Grey hat hackers operate somewhere between ethical and malicious hackers.
They may access systems without permission but do not necessarily intend to cause harm.
In some cases, grey hat hackers discover vulnerabilities and later report them to organizations.
However, accessing systems without authorization can still be illegal, even if the intention is not malicious.
Among the types of hackers, grey hat hackers represent a controversial group because their actions exist in a legal and ethical gray area.
4. Script Kiddies
Script kiddies are beginners who use pre-built hacking tools without fully understanding how they work.
Instead of creating their own exploits, they rely on:
- downloadable hacking tools
- automated attack scripts
- publicly available exploit kits
Although their skill level is low, script kiddies can still cause damage because powerful tools are widely available online.
Within the types of hackers, script kiddies are usually inexperienced but unpredictable attackers.
5. Hacktivists

Hacktivists use hacking techniques to promote political or social causes.
Their attacks are often motivated by ideology rather than financial gain.
Typical hacktivist actions include:
- website defacement
- information leaks
- distributed denial of service attacks
- exposing sensitive data
Hacktivists often target governments, corporations, or institutions that they believe represent political injustice.
Among the types of hackers, hacktivists combine cybersecurity skills with activism.
6. State-Sponsored Hackers
State-sponsored hackers work for governments or intelligence agencies.
Their activities are part of cyber warfare or espionage operations.
These hackers target critical infrastructure such as:
- defense systems
- energy grids
- financial institutions
- telecommunications networks
State-sponsored hackers are typically highly skilled and well-funded.
Among all types of hackers, they are considered some of the most sophisticated attackers in the cybersecurity landscape.
7. Insider Hackers
An insider hacker is someone who already has authorized access to an organization’s systems but abuses that access.
Insiders may include:
- employees
- contractors
- administrators
- business partners
Because insiders already understand internal systems, they can bypass many security controls.
Among the types of hackers, insider threats are particularly dangerous because they originate from within the organization.
How Attackers Think: Hacker Mindset Explained
To truly understand the types of hackers, we must examine the attacker mindset.
Hackers generally follow a structured process when targeting systems.
Step 1 — Identify a Target
Attackers begin by selecting an organization or system that appears valuable or vulnerable.
Targets may include:
- financial institutions
- e-commerce platforms
- government agencies
- corporate networks
Step 2 — Gather Information
Attackers collect as much information as possible about the target.
This phase is known as reconnaissance.
Information collected may include:
- domain names
- server technologies
- exposed services
- employee email addresses
Step 3 — Identify Weaknesses
Once information is gathered, hackers analyze the system for vulnerabilities.
Examples include:
- weak passwords
- outdated software
- misconfigured servers
Different types of hackers focus on different weaknesses depending on their skills.
Step 4 — Attempt Exploitation
After identifying a vulnerability, attackers attempt to exploit it.
This could involve:
- bypassing authentication
- executing malicious code
- gaining unauthorized access
Step 5 — Maintain Access
Once attackers gain entry, they attempt to maintain long-term access to the system.
This may involve installing backdoors or creating hidden accounts.
Step 6 — Cover Tracks
Finally, attackers attempt to hide evidence of their intrusion.
This helps them remain undetected.
Understanding this mindset helps cybersecurity professionals anticipate attacks from different types of hackers.
How Organizations Protect Systems from Hackers?
Organizations implement multiple defensive layers to protect against various types of hackers.
Security Monitoring
Security teams monitor systems for suspicious activity using tools such as:
- intrusion detection systems
- security monitoring platforms
- endpoint detection solutions
These tools help detect unusual behavior that may indicate an attack.
Access Control
Strong authentication mechanisms reduce the risk of unauthorized access.
Examples include:
- multi-factor authentication
- role-based access control
- least privilege policies
These strategies help limit the damage that attackers can cause.
Patch Management
Many attacks exploit known vulnerabilities in outdated software.
Regular updates and security patches help prevent these attacks.
Employee Awareness
Human error often contributes to cybersecurity breaches.
Training employees to recognize threats such as phishing can significantly reduce risk.
Frequently Asked Questions About Types of Hackers
What are the main types of hackers?
The most recognized types of hackers include white hat hackers, black hat hackers, grey hat hackers, script kiddies, hacktivists, state-sponsored hackers, and insider hackers. These classifications are based on intent, skill level, and authorization when interacting with computer systems.
Are all hackers criminals?
No. Some hackers are ethical professionals who help organizations improve security. White hat hackers legally test systems to identify vulnerabilities and strengthen defenses before malicious attackers exploit them.
Why is it important to understand types of hackers?
Understanding the types of hackers helps cybersecurity professionals anticipate threats, identify attack patterns, and implement better defensive strategies to protect digital infrastructure.
Can beginners learn ethical hacking safely?
Yes. Beginners can learn cybersecurity through structured training, legal penetration testing labs, and cybersecurity courses that teach responsible security testing techniques.
Which type of hacker is the most dangerous?
State-sponsored hackers and organized cybercriminal groups are often considered the most dangerous because they possess advanced resources, funding, and technical expertise.
Do ethical hackers use the same techniques as attackers?
Yes. Ethical hackers use many of the same tools and techniques as malicious hackers. The key difference is that ethical hackers operate with permission and report vulnerabilities responsibly.
Conclusion and Key Takeaways
Learning about the types of hackers is one of the most important foundations in cybersecurity education.
Different hackers operate with different motivations, skill levels, and goals. Some hackers work to improve security, while others attempt to exploit weaknesses for financial or political gain.
The most common types of hackers include:
- white hat hackers
- black hat hackers
- grey hat hackers
- script kiddies
- hacktivists
- state-sponsored hackers
- insider hackers
For aspiring cybersecurity professionals, understanding these hacker categories helps develop the ability to think like an attacker while defending systems responsibly.
Cybersecurity training should always focus on ethical practices and legal security testing.
The best ethical hackers understand both how attacks work and how to stop them.
By studying hacker behavior and continuously improving security knowledge, cybersecurity professionals can help build safer digital systems for organizations and users worldwide.