Information Gathering Using Kali Linux – Day 5
OSINT Intelligence Gathering Using theHarvester (Email & Intelligence Discovery)
Now we reach a major turning point in professional reconnaissance.
Until now we learned:
✅ Day 1 — WHOIS → Ownership
✅ Day 2 — DNSRecon → Infrastructure
✅ Day 3 — Sublist3r → Subdomains
✅ Day 4 — Nmap → Live Hosts & Services
We now understand systems.
But real attackers — and elite defenders — go one step further.
They target people and public intelligence.
Today we enter:
🔎 OSINT Reconnaissance.
Let me share something from a real incident response case.
A company invested millions in firewalls.
Network segmentation.
Endpoint protection.
24/7 SOC monitoring.
Technically strong.
Yet attackers gained access without exploiting a single vulnerability.
How?
They discovered employee email addresses publicly available online.
Then launched targeted phishing.
One login.
One employee.
Full compromise.
Pause here for a second.
Most beginners think hacking targets machines.
Professionals know:
👉 Humans are part of the attack surface.
And today’s tool specializes in discovering exactly that.
Welcome to Day 5 of Information Gathering using Kali Linux.
Tool of the day:
✅ theHarvester
🎯 Why OSINT Intelligence Matters in Cybersecurity
OSINT means:
Open Source Intelligence
Information publicly available on the internet.
No intrusion.
No exploitation.
Just intelligence collection.
During enterprise penetration testing, OSINT reveals:
- employee emails
- usernames
- exposed hosts
- company infrastructure
- third-party services
- leaked credentials indicators
Something important happens here.
Technical defenses protect servers.
But organizations constantly expose information through:
- search engines
- social media
- job portals
- public documents
- GitHub repositories
Attack surface expands beyond networks.
It becomes human-centric.
You might wonder:
“Is collecting emails really hacking?”
Not directly.
But intelligence enables attacks.
Recon drives exploitation workflow.
Without intelligence, attacks are blind.
Core Concept
Think of OSINT like investigative journalism.
You gather clues without entering restricted areas.
Example:
A company domain:
example.com
theHarvester searches public sources to find:
john@example.com
admin@example.com
vpn.example.com
Each discovery becomes potential entry intelligence.
Emails → phishing vectors
Hosts → scan targets
Names → password patterns
Beginners often ignore this stage.
Professionals never do.
⚙️ Professional Recon Workflow (Continuation)
Let’s connect our growing methodology.
Previous Days Produced:
✔ domains
✔ subdomains
✔ live hosts
Now we enrich intelligence.
Workflow:
- Passive Recon ✅
- DNS Mapping ✅
- Host Discovery ✅
- Human Intelligence Collection ✅ (Today)
- Attack Path Modeling (Coming)
Enterprise recon always combines technical + human data.
🧪 Real-World Scenario
During a red-team engagement, perimeter security was flawless.
No exposed vulnerabilities.
But theHarvester revealed:
it-support@company.com
vpn-admin@company.com
LinkedIn confirmed employees.
Password spraying attack launched.
VPN access obtained.
No exploit used.
Only intelligence.
This is why OSINT is powerful.
🛠 Tool of the Day — theHarvester (Kali Linux)
theHarvester gathers intelligence from:
- Bing
- GitHub
- Shodan
- DNS sources
Completely passive reconnaissance.
✅ Step 1 — Verify Installation
theHarvester -h
If help menu appears → ready.
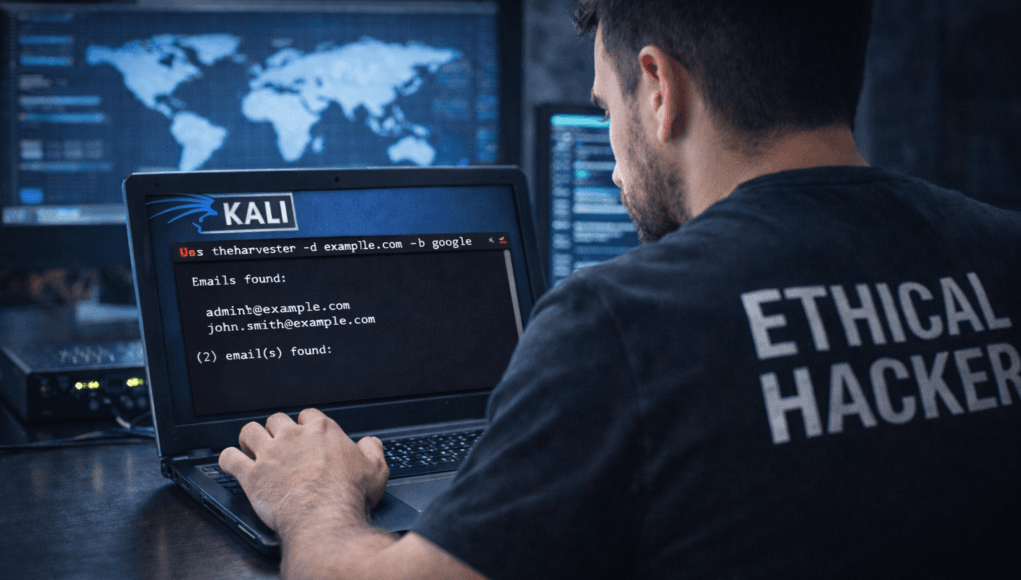
✅ Step 2 — Basic Email Enumeration
theHarvester -d example.com -b google
Meaning:
-d→ domain-b→ data source
Output:
Emails found:
admin@example.com
support@example.com
Mentor Insight 🔎
Students focus only on quantity.
Professionals analyze roles.
Admin accounts matter more than generic emails.
✅ Step 3 — Use Multiple Intelligence Sources
theHarvester -d example.com -b bing
Different engines reveal different data.
Always cross-check.
✅ Step 4 — Discover Hosts
theHarvester -d example.com -b dns
Finds additional infrastructure.
✅ Step 5 — Save Output
theHarvester -d example.com -b all -f harvest.html
Creates professional report.
Documentation habit starts here.
🚨 Beginner Mistake Alert
❌ Using Single Data Source
OSINT requires aggregation.
❌ Ignoring Employee Names
Names help predict usernames.
❌ Jumping to Attacks
Recon ≠ exploitation.
Stay methodological.
🔥 Pro Tips From 20 Years Experience
✅ Look for patterns:
firstname.lastname@
f.lastname@
admin@
Predict authentication formats.
✅ Combine with LinkedIn searches.
Role intelligence matters.
✅ Developers often expose emails via Git commits.
Huge intelligence leak source.
Enterprise observation:
Human intelligence frequently bypasses technical defenses.
Defensive & Ethical Perspective
Blue teams should monitor:
- exposed employee data
- leaked emails
- public repositories
- phishing exposure risks
Modern defense includes:
✅ OSINT monitoring
✅ brand protection
✅ employee awareness training
Ethical reminder:
Never misuse collected personal data.
Professional cybersecurity protects privacy.
✅ Practical Implementation Checklist
Today practice:
✔ Run theHarvester on test domains
✔ Collect emails
✔ Identify naming patterns
✔ Discover hosts
✔ Export HTML report
✔ Document findings
Your recon dataset now includes humans.
💼 Career Insight
OSINT skills are critical for:
- Threat Intelligence Analysts
- Red Team Operators
- SOC Analysts
- Cyber Investigators
- Bug Bounty Hunters
Many advanced roles focus more on intelligence than exploitation.
Recon specialists are rare — and valuable.
🔁 Quick Recap Summary
Your progression:
| Day | Skill |
|---|---|
| Day 1 | WHOIS |
| Day 2 | DNSRecon |
| Day 3 | Sublist3r |
| Day 4 | Nmap |
| Day 5 | OSINT Intelligence ✅ |
You now understand:
✔ infrastructure
✔ live systems
✔ exposed human intelligence
Tomorrow…
We fingerprint technologies powering discovered websites.
And this unlocks vulnerability targeting.
❓ FAQs
1. What is theHarvester used for?
It collects emails, hosts, and OSINT intelligence related to domains.
2. Is OSINT legal?
Yes, when using publicly available information responsibly.
3. Why collect emails during recon?
They help identify users and attack vectors.
4. Is theHarvester passive?
Mostly yes — it queries public data sources.
5. Do professionals use OSINT?
Absolutely. It’s essential in modern cybersecurity.