The internet is much bigger than most people think. When you open Google, watch YouTube videos, or visit websites, you are only seeing a small part of the internet. There is a hidden side of the internet that most people never see. This Dark Web Guide will help you understand that hidden world in simple terms.
Many people hear the phrase dark web and imagine hackers sitting in dark rooms typing code on glowing computer screens. Movies and TV shows often show the dark web as a mysterious place where criminals buy illegal things.
But the reality is much more interesting.
In this Dark Web Guide, we will explain the hidden internet step by step so even beginners can understand how it works. By the end of this Dark Web Explained tutorial, you will learn:
- what the dark web actually is
- how the tor network hides user identity
- why hackers sometimes use the dark web
- how cybersecurity experts investigate dark web activity
The dark web itself is simply a hidden network that allows anonymous communication. It was created to protect privacy and allow people to communicate without revealing their location.
Because of this privacy feature, the dark web ecosystem is used by many different groups:
- journalists protecting sources
- activists avoiding censorship
- cybersecurity researchers studying cybercrime
- hackers trading stolen data
This Dark Web Guide will explain everything step by step so even someone who has never heard about the dark web can understand it.
Table of Contents
What Is the Dark Web?
The Dark Web is a hidden part of the internet that cannot be accessed using standard web browsers like Chrome or Safari. Instead, users must connect through privacy-focused networks such as the Tor Network. These networks hide a user’s identity by routing internet traffic through encrypted servers, allowing anonymous communication and access to websites with the .onion domain.
Understanding the Layers of the Internet
Before learning about the dark web, it is important to understand how the internet is structured.
Cybersecurity experts often explain the internet using something called the internet iceberg model.
Imagine a huge iceberg floating in the ocean.
Only the top part of the iceberg is visible above the water. Most of the iceberg is hidden below the surface.
The internet works in a similar way.
In this Dark Web Guide, we will explain the three layers of the internet:
- Surface Web
- Deep Web
- Dark Web
The dark web is actually the smallest part of the internet. However, it receives a lot of attention because it focuses on anonymous communication and hidden networks.
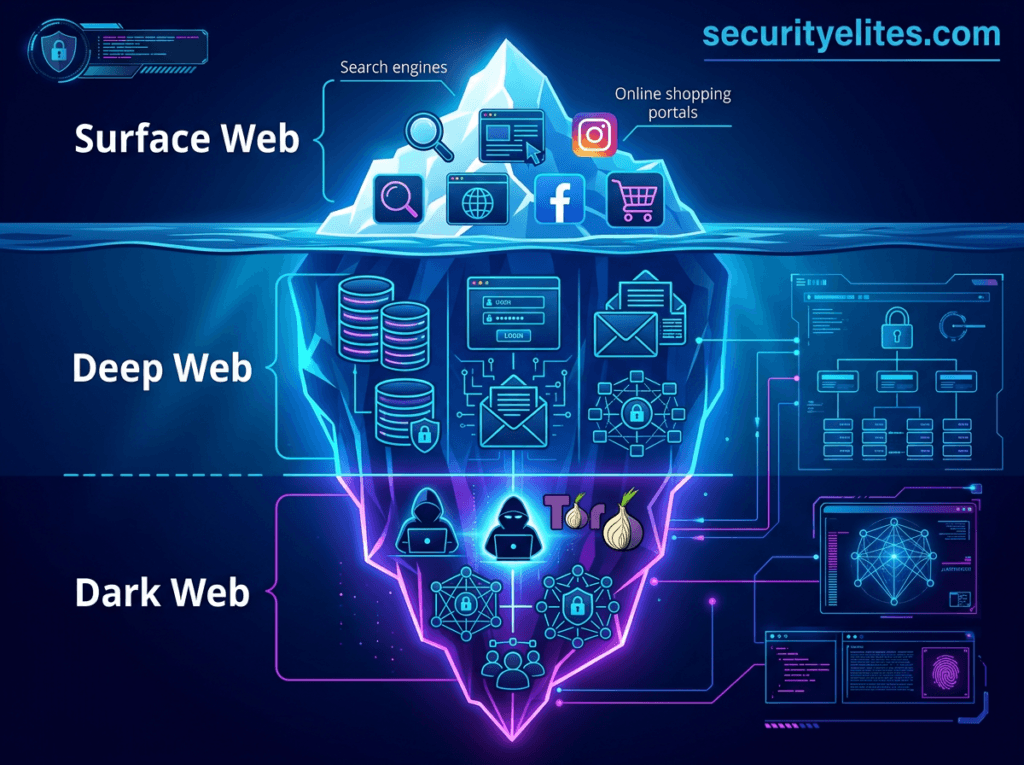
Understanding these layers is the first step in understanding the Dark Web Explained concept.
Surface Web – The Internet Everyone Uses
The surface web is the part of the internet that most people use every day.
These are websites that search engines like Google can find and index.
Examples include:
- blogs
- online stores
- news websites
- Wikipedia
- YouTube
- social media platforms
If you can search for a website using Google, it belongs to the surface web.
For example:
- amazon.com
- wikipedia.org
- cnn.com
All of these websites belong to the surface web.
However, the surface web represents only a very small part of the internet.
Experts estimate that the surface web contains only about 5% of the entire internet.
The remaining content exists in the deep web and dark web.
This is why this Dark Web Guide starts by explaining how the internet layers work.
Deep Web – The Hidden Internet
The deep web contains all internet content that search engines cannot access.
This does not mean the deep web is dangerous or illegal.
Most of the deep web contains completely normal information.
Examples of the deep web include:
- email inboxes
- online banking portals
- company internal networks
- academic databases
- medical record systems
Whenever you log into a website using a username and password, you are entering the deep web.
For example:
When you log into Gmail, your emails are not visible in Google search results. That content is part of the deep web.
In this Dark Web Guide, it is important to understand that the deep web and dark web are not the same thing.
Note —
Think of the internet like a large building.
The surface web is the lobby where everyone can walk in.
The deep web is the private office area where only employees can enter.
You need a password or key to access those rooms.
Dark Web – The Anonymous Internet
Now we reach the most mysterious part of the internet: the dark web.
The dark web is a small section of the deep web designed specifically for anonymous communication. Unlike the surface web, the dark web requires special software to access.
The most common tool used to access the dark web is the Tor Browser.
The tor network hides the identity of users by routing internet traffic through multiple encrypted servers around the world. This makes it extremely difficult to trace where the connection originally came from.
Because of this privacy feature, the dark web network allows anonymous communication.
Some people use the dark web for legitimate reasons such as protecting privacy or avoiding censorship.
However, hackers sometimes misuse the dark web ecosystem for illegal activities.
This Dark Web Guide explains how these hidden networks work.
Deep Web vs Dark Web vs Surface Web
Many beginners confuse the deep web and dark web.
In this Dark Web Guide, here is a simple comparison.
| Internet Layer | Description | Examples | Accessibility |
|---|---|---|---|
| Surface Web | Public websites indexed by search engines | Blogs, news sites | Open access |
| Deep Web | Private content not indexed by search engines | Email accounts | Login required |
| Dark Web | Anonymous networks accessed through Tor | .onion websites | Special software |
Understanding this difference is essential for the Dark Web Explained concept.
How the Dark Web Works
The dark web network works differently from the normal internet.
On the normal internet, when you visit a website, your computer connects directly to that website server.
Example:
User → Website Server
But on the dark web, your internet traffic travels through several encrypted servers before reaching the final website.
Example:
User → Tor Node → Relay Node → Exit Node → Website
Each node in the network only knows the previous and next step in the connection path.
This prevents anyone from easily identifying the original user.
This system is explained in detail throughout this Dark Web Guide.
Understanding the Tor Network
The tor network is the main technology used to access the dark web.
Tor stands for:
The Onion Router
The tor network protects privacy by routing internet traffic through multiple encrypted servers around the world.
Each server removes one layer of encryption before forwarding the data.
Because of this process, tracking the original user becomes extremely difficult.
This technology is the backbone of the dark web ecosystem.
Understanding Onion Routing
Onion routing is the system that protects privacy on the dark web.
Data is encrypted multiple times before being sent through the network.
Each relay server removes one layer of encryption before passing the data to the next relay.
This layered encryption is similar to the layers of an onion.
Simple Example
Imagine sending a secret message through three different friends.
Each friend only knows who gave them the message and who they must send it to next.
None of them know the original sender.
This is how onion routing protects anonymity on the dark web network.
Hidden Services (.onion Websites)
Websites on the dark web use special domain names.
Instead of ending with:
.com
.org
.net
Dark web websites end with:
.onion
These websites are called hidden services.
They can only be accessed through the Tor Browser.
Because search engines cannot index these websites, they remain hidden from the public internet.
This is why the dark web remains difficult to explore without special tools.
How People Access the Dark Web
In this Dark Web Guide, one important question beginners ask is:
“How do people actually access the dark web?”
The dark web cannot be accessed using normal browsers like Chrome, Firefox, or Edge. These browsers only work on the surface web.
To access the dark web network, users need special software that connects them to privacy-focused networks.
The most common tool used to access the dark web is the Tor Browser.
The Tor Browser is designed to connect users to the Tor Network, which hides their identity by routing internet traffic through multiple encrypted servers.
Basic Steps to Access the Dark Web
People usually follow these steps to access the dark web:
- Download the Tor Browser
- Install the browser on their computer
- Connect to the Tor Network
- Visit websites with .onion domain names
These .onion websites exist inside the dark web ecosystem.
Note —
Think of the dark web like a secret underground library.
Normal browsers are like regular doors that open normal rooms.
But the dark web requires a special key to enter.
The Tor Browser is that key.
Why Cybersecurity Researchers Access the Dark Web
Many cybersecurity professionals explore the dark web for research purposes.
They monitor hacker discussions, investigate data leaks, and collect information about cybercrime groups.
This process is often called dark web threat intelligence.
Researchers search the dark web to discover:
- leaked passwords
- stolen company databases
- new malware tools
- hacker discussions about vulnerabilities
This is why understanding the hidden internet is important in this Dark Web Guide.
Why Hackers Use the Dark Web
One of the most important questions in this Dark Web Guide is:
Why do hackers use the dark web?
Hackers prefer the dark web because it provides anonymity and privacy.
When someone connects to the dark web through the Tor Network, their real identity becomes difficult to trace.
This makes the dark web attractive for cybercriminal activity.
Some common reasons hackers use the dark web include:
- anonymous communication
- selling stolen data
- buying malware tools
- sharing hacking techniques
- coordinating cybercrime activities
The dark web has become a major part of the modern cybercrime economy.
What Hackers Really Do on the Dark Web
Many people think hackers spend all their time launching cyberattacks on the dark web.
But the reality is different.
Most hacker activity on the dark web involves buying and selling digital tools or information.
Hackers use dark web marketplaces to trade items such as:
- stolen passwords
- malware software
- hacked server access
- phishing tools
This underground market is part of what cybersecurity researchers call the dark web economy.
Selling Stolen Data
One of the most common activities on the dark web is the sale of stolen data.
When hackers break into company systems or websites, they may steal sensitive information.
This information can include:
- credit card numbers
- login credentials
- email databases
- personal identity information
Instead of using the data themselves, hackers often sell it on dark web marketplaces.
Other criminals may buy the data and use it for fraud or identity theft.
Imagine a hacker breaks into a website that stores thousands of user accounts.
The hacker steals a database containing usernames and passwords.
Instead of using the data personally, the hacker lists the database for sale on the dark web marketplace.
Buyers can then purchase the data.
This type of activity is frequently discussed in cybersecurity investigations.
Malware Marketplaces
Another common activity on the dark web involves selling malware.
Malware is software designed to damage computers or steal information.
Examples of malware sold on the dark web include:
- ransomware
- spyware
- trojan viruses
- keyloggers
Some hackers develop malware and sell it to others.
This allows criminals who do not know how to code to still launch cyberattacks.
Malware-as-a-Service
Many dark web marketplaces now offer Malware-as-a-Service (MaaS).
This business model works like a subscription service.
Instead of building malware themselves, criminals can rent malware tools from developers.
This makes cybercrime easier for beginners.
This concept is an important part of the Dark Web Explained concept.
Phishing Kits
Phishing kits are another popular product sold on the dark web.
A phishing kit is a ready-made toolkit that allows attackers to create fake login websites.
These websites look identical to real websites.
Examples include fake login pages for:
- PayPal
- Gmail
- online banking portals
When victims enter their username and password, the attacker steals the information.
Phishing kits make cybercrime easier for beginners because they require very little technical knowledge.
Botnet Rentals
A botnet is a network of infected computers controlled by hackers.
When malware infects a computer, the attacker may secretly control the device.
Thousands of infected computers can form a botnet.
Botnets are often used for:
- launching DDoS attacks
- sending spam emails
- spreading malware
Some criminals rent botnets through dark web marketplaces.
This allows attackers to perform large cyberattacks without owning the botnet themselves.
Access Brokers
Access brokers play a major role in the dark web cybercrime economy.
An access broker is a hacker who breaks into company networks and sells that access to other criminals.
For example:
A hacker discovers a vulnerability in a company’s server.
The hacker gains access to the network.
Instead of launching an attack directly, the hacker sells the access on the dark web.
Another criminal group may then buy the access and deploy ransomware.
This system has become common in modern cybercrime.
Cryptocurrency Laundering
Most dark web marketplaces use cryptocurrency payments.
Cryptocurrency allows people to send money without using traditional banks.
Common cryptocurrencies used on the dark web include:
- Bitcoin
- Monero
- Ethereum
However, blockchain transactions can sometimes be traced.
To hide the origin of funds, criminals sometimes use services called cryptocurrency mixers.
Mixers combine many transactions together to make it harder to track where the money came from.
Dark Web Marketplaces Explained
Dark web marketplaces operate similarly to online shopping websites like Amazon or eBay.
However, instead of selling physical products, these marketplaces sell digital cybercrime tools.
Examples of products sold on dark web marketplaces include:
- stolen data
- malware software
- hacking tools
- phishing kits
These marketplaces include features designed to build trust between anonymous users.
Vendor Reputation Systems
Just like e-commerce websites, dark web marketplaces use reputation systems.
Sellers receive ratings based on customer feedback.
If a vendor sells high-quality products, buyers leave positive reviews.
Over time, trusted vendors build strong reputations.
This system helps buyers choose reliable sellers.
Escrow Payments
Dark web marketplaces often use escrow payment systems.
When a buyer purchases something, the payment is held by the marketplace until the transaction is completed.
Once the buyer confirms delivery, the seller receives the payment.
This protects both buyers and sellers from scams.
Cryptocurrency Transactions
Cryptocurrency is widely used in dark web marketplaces because it allows payments without banks.
Some cryptocurrencies provide stronger privacy features than others.
For example, Monero is often preferred because it hides transaction details better than Bitcoin.
Understanding cryptocurrency transactions is an important part of this Dark Web Guide.
Real Examples of Dark Web Cybercrime
In this Dark Web Guide, we have learned that the dark web is not only used for privacy and anonymous communication. Some criminals also misuse the dark web to run illegal operations.
Over the years, many major cybercrime marketplaces have existed on the dark web. These marketplaces allowed criminals to buy and sell illegal goods and digital tools.
Some of these platforms became extremely large and operated like real online businesses.
For example, certain dark web marketplaces allowed criminals to trade:
- stolen credit card data
- hacked user accounts
- malware software
- fake identity documents
Law enforcement agencies eventually shut down many of these marketplaces through international investigations.
These cases demonstrate an important point explained in this Dark Web Explained guide:
Even though the dark web provides anonymity, it is not impossible for authorities to investigate crimes.
Is the Dark Web Illegal?
Many beginners reading this Dark Web Guide wonder whether the dark web itself is illegal.
The answer is simple.
The dark web itself is not illegal.
Accessing the dark web using tools like the Tor Browser is legal in most countries.
The technology behind the dark web was originally designed to protect privacy and allow people to communicate securely.
However, illegal activities performed on the dark web are crimes.
Examples of illegal activities include:
- selling stolen financial data
- distributing malware
- running illegal marketplaces
- purchasing illegal goods
So the dark web itself is simply a technology. What matters is how people use it.
Note —
Think of the dark web like a road.
Driving on the road is legal.
But if someone uses the road to commit a crime, that activity becomes illegal.
The same idea applies to the dark web.
How Law Enforcement Tracks Dark Web Criminals
Many people believe that criminals operating on the dark web cannot be tracked.
This is a common myth.
In reality, law enforcement agencies have successfully arrested many criminals who used dark web marketplaces.
In this Dark Web Guide, it is important to understand how investigators track cybercriminals.
Authorities use several investigative techniques.
Undercover Investigations
Law enforcement agents sometimes create undercover accounts on dark web forums or marketplaces.
They may pretend to be buyers or sellers.
Over time, investigators gather valuable information about criminal networks.
These operations help authorities identify key members of cybercrime groups.
Blockchain Analysis
Many transactions on dark web marketplaces use cryptocurrency.
Although cryptocurrencies provide some privacy, many transactions are recorded on public blockchains.
Investigators use specialized tools to analyze blockchain transactions.
This allows them to trace money flows connected to cybercrime.
Server Seizures
Sometimes authorities manage to locate the servers hosting dark web marketplaces.
When investigators seize these servers, they may obtain valuable evidence such as:
- transaction records
- user accounts
- private messages
This information can help identify criminals.
How Cybersecurity Experts Monitor the Dark Web
Cybersecurity professionals regularly monitor the dark web to detect cyber threats.
This process is known as dark web threat intelligence.
Security teams search dark web forums and marketplaces to find information about potential attacks.
They look for signs such as:
- leaked passwords
- stolen company databases
- discussions about software vulnerabilities
- ransomware group announcements
Monitoring the dark web helps organizations detect cyber threats before they cause damage.
This is why studying the dark web is important in modern cybersecurity.
Dark Web Safety Tips
Anyone researching the dark web should follow strict safety guidelines.
This Dark Web Guide recommends the following precautions.
Never Download Unknown Files
Files found on dark web websites may contain malware.
Downloading unknown files can infect your computer.
Avoid Illegal Marketplaces
Participating in illegal activities on the dark web can lead to serious legal consequences.
Always avoid illegal marketplaces.
Protect Personal Information
Never reveal personal identity details when exploring the dark web.
Anonymous networks provide privacy, but mistakes can expose users.
Use Isolated Research Environments
Cybersecurity researchers often use virtual machines when studying the dark web.
If malware infects the system, the damage remains contained.
Common Myths About the Dark Web
There are many myths surrounding the dark web.
This Dark Web Guide will clarify some common misunderstandings.
Myth 1: The Dark Web Is Only for Criminals
Reality:
While criminals use the dark web, it is also used by journalists, researchers, and privacy advocates.
Myth 2: Everything on the Dark Web Is Illegal
Reality:
Many dark web websites exist purely for anonymous communication.
Myth 3: The Dark Web Cannot Be Tracked
Reality:
Law enforcement agencies have successfully arrested many criminals who operated on dark web marketplaces.
Frequently Asked Questions
Is the Dark Web illegal?
The Dark Web itself is not illegal. Accessing the Dark Web using tools like the Tor Browser is legal in most countries. However, illegal activities performed on the Dark Web, such as selling stolen data or malware, are crimes.
Why do hackers use the Dark Web?
Hackers use the Dark Web because it provides anonymity. The Tor Network hides user identities by routing internet traffic through encrypted servers. This allows cybercriminals to communicate, trade hacking tools, and share stolen data with reduced risk of being identified.
How do people access the Dark Web?
To access the Dark Web, users typically install the Tor Browser, connect to the Tor Network, and visit websites that use the .onion domain. This process allows users to browse anonymous networks that are not indexed by search engines.
What are Dark Web marketplaces?
Dark Web marketplaces are online platforms that operate inside anonymous networks like Tor. These marketplaces allow users to buy and sell digital goods such as stolen data, malware tools, and hacking services.
Can law enforcement track Dark Web criminals?
Yes. Law enforcement agencies can track Dark Web criminals using methods such as blockchain analysis, undercover investigations, and server seizures. Although the Dark Web provides anonymity, criminals often make mistakes that allow investigators to identify them.
Is it safe to explore the Dark Web?
Exploring the Dark Web can be risky because some websites contain malware or illegal content. Cybersecurity researchers often use secure environments such as virtual machines when studying the Dark Web to reduce potential risks.
Why do cybersecurity experts study the Dark Web?
Cybersecurity professionals monitor the Dark Web to detect cyber threats early. They search for leaked passwords, stolen databases, and hacker discussions about vulnerabilities. This process is known as Dark Web threat intelligence.
What is the Tor Network in the Dark Web?
The Tor Network is a privacy system that routes internet traffic through multiple encrypted servers. This process hides the user’s location and identity. The Tor Network is the main technology used to access websites on the Dark Web.
Key Takeaways for SecurityElites Learners
This Dark Web Guide has explained the hidden internet in simple terms.
The dark web is often misunderstood as a mysterious underground world used only by criminals.
In reality, the dark web is a privacy-focused network designed to protect anonymous communication.
While criminals sometimes misuse the dark web for illegal activities, cybersecurity professionals study the dark web ecosystem to understand attacker behavior and defend against cyber threats.
For beginners learning cybersecurity, understanding the Dark Web Explained concept provides valuable insight into how modern cybercrime works.
The more we understand the hidden parts of the internet, the better we can protect the digital world.




