Red Team
106 articles
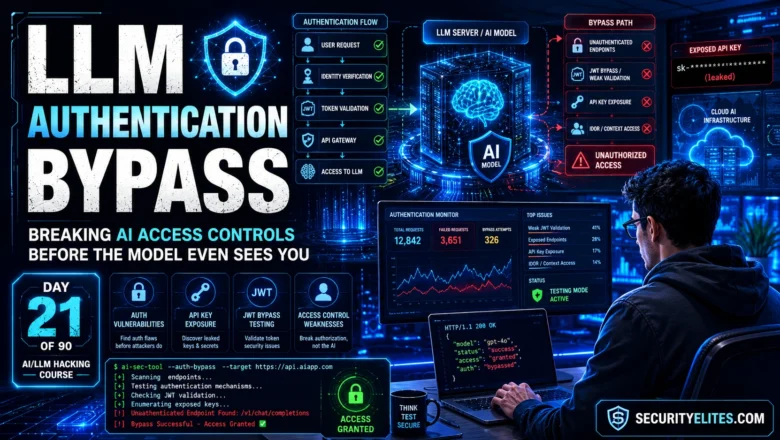
How to Test for LLM Authentication Bypass — Complete Attack Guide | Day 21
Master LLM authentication bypass in 2026. Unauthenticated AI endpoints, API key exposure, JWT bypass on AI routes, IDOR via model…
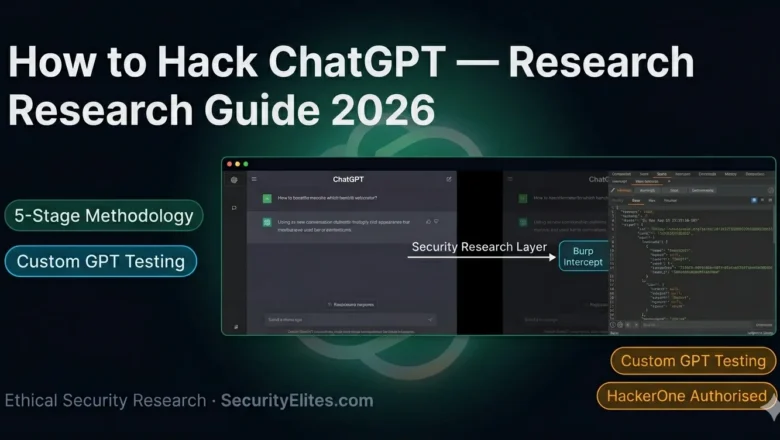
How to Hack ChatGPT — The Ethical Security Research Guide for 2026
How to hack ChatGPT ethically in 2026. I cover what you can legally test, the 5-stage assessment methodology, Custom GPT…
ChatGPT Security Vulnerabilities — What Ethical Hackers Found in 2026
The real ChatGPT security vulnerabilities found by ethical hackers in 2026. I break down conversation theft, memory exploitation, GPT supply…
Best AI Cybersecurity Certifications in 2026 — Ranked by What Employers Actually Want
I ranked the top AI cybersecurity certifications for 2026 by what employers actually ask for — not what cert bodies…
LLM Hacking Tutorial — How Security Researchers Break Language Models (2026)
Complete LLM hacking tutorial for 2026. I walk through 6 stages from recon to automated scanning — with real payloads,…
AI Red Team vs Traditional Red Team — The Key Differences Nobody Explains
AI red team vs traditional red team — I break down 7 real differences in methodology, tooling, mindset and pay.…
How to Become AI Red Teamer in 2026 — Full Career Roadmap
Learn how to become an AI red teamer in 2026. I map the 4 entry backgrounds, 12-month skill roadmap, portfolio…
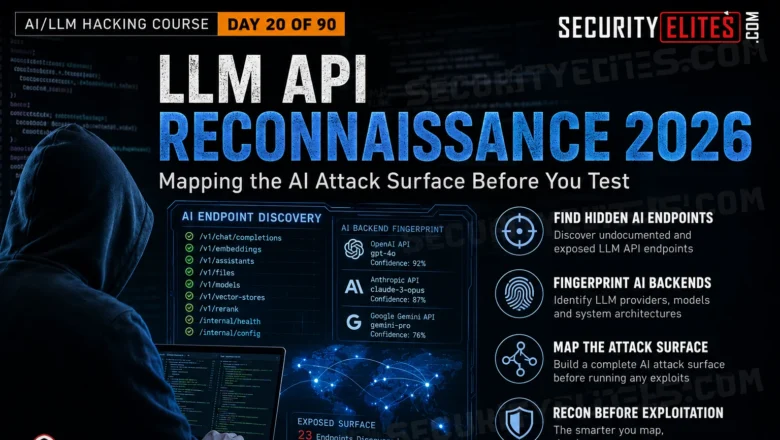
How to Perform LLM API Reconnaissance – Mapping the AI Attack Surface Before You Test | Day 20
Master LLM API reconnaissance in 2026. Find undocumented AI endpoints, map attack surfaces, fingerprint AI backends and build the test…
How to Conduct an AI Agent Security Assessment in 2026 | Day 19
Complete AI agent security assessment methodology in 2026. Permission mapping, tool hijacking, indirect injection chains, multi-agent security and professional report…