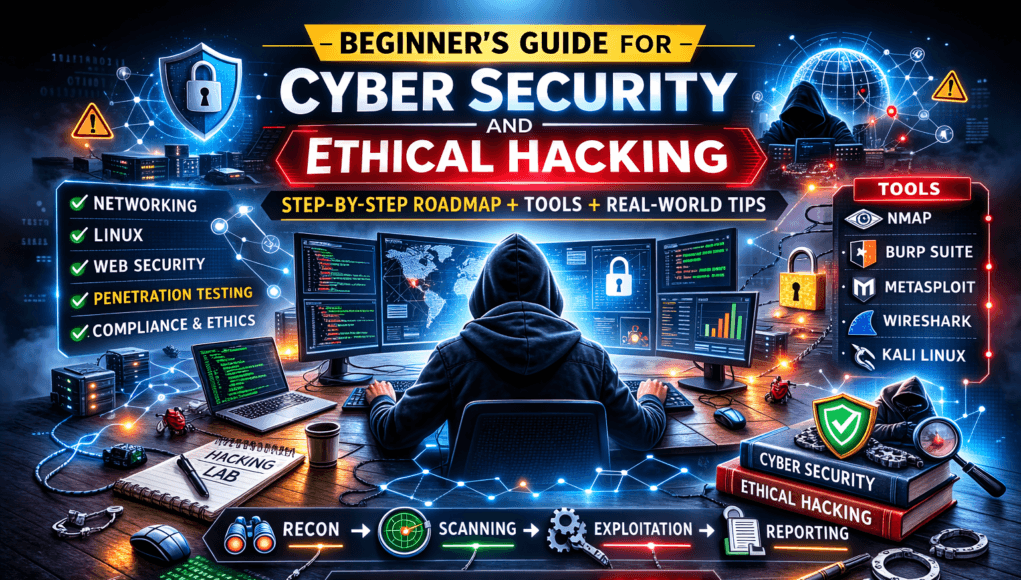
Let me say this straight. Welcome to the Beginner’s Guide for Cyber Security and Ethical Hacking.
If you’re stepping into Cyber Security and Ethical Hacking because it looks “cool” on YouTube — slow down.
If you’re stepping in because you genuinely want to understand how attacks happen, how systems break, and how to defend real people and real businesses — welcome. You’re in the right place.
I’ve spent over 20 years in penetration testing labs, corporate boardrooms, breach investigations at 3 AM, and training junior analysts who were overwhelmed in their first week. And here’s the truth:
Cyber security is not about hacking tools.
It’s about thinking differently.
Beginner’s Guide for Cyber Security and Ethical Hacking Overview
Let’s break this down properly.
What Is Cyber Security and Ethical Hacking (In Simple Terms)?
At its core:
- Cyber Security = Protecting systems, networks, and data.
- Ethical Hacking = Legally breaking into systems to find weaknesses before criminals do.
Think of it like this:
If cyber security is building a fortress, ethical hacking is hiring someone to test whether the walls actually hold.
Now here’s where most beginners get confused…
They think ethical hacking means:
- Running flashy tools
- Typing green text in terminals
- Breaking WiFi passwords
That’s maybe 5% of the real job.
The real job is:
- Understanding systems deeply
- Thinking like an attacker
- Documenting everything
- Communicating risks clearly
And yes — sometimes writing more reports than running tools.
Social Media Footprinting Techniques Hackers Use (Complete Ethical Hacker Guide)
The Mindset Behind Cyber Security and Ethical Hacking
Before tools.
Before certifications.
Before labs.
You need the mindset.
In real assessments, what we usually see is this:
Two analysts run the same tool.
One finds nothing.
The other finds a critical vulnerability.
Why?
Curiosity.
A good ethical hacker asks:
- What happens if I change this parameter?
- What if input validation fails?
- What if this API wasn’t meant to be public?
- Why is this port open at all?
Security is detective work mixed with engineering logic.
Core Foundations Every Beginner Must Learn
Let me break this down in simple terms.
In this Beginner’s Guide for Cyber Security and Ethical Hacking, we will explore essential concepts and practical skills you need to succeed.
You cannot secure what you don’t understand.
1. Networking (Non-Negotiable)
Learn:
- TCP/IP
- DNS
- HTTP/HTTPS
- Ports and protocols
- Firewalls
- NAT
- Subnetting
If someone says “port 443 is open” — you must instantly know what that implies.
Beginner Mistake Alert 🚨
Jumping into hacking tools without understanding networking is like trying to hack a building without knowing how doors work.
Passive vs Active Reconnaissance – Real Hacker Methods Explained
2. Operating Systems
Focus on:
- Linux fundamentals
- Windows internals basics
- File permissions
- Process management
- Logs
Most breaches I’ve investigated came down to poor configuration, not sophisticated malware.
3. Web Application Basics
You must understand:
- How websites work
- Client vs server
- Cookies
- Sessions
- Authentication
Because today, 70% of attacks target web apps.
Beginner’s Guide for Cyber Security and Ethical Hacking: Essential Skills
Step-by-Step Path Into Cyber Security and Ethical Hacking
Here’s a realistic roadmap I give to my trainees.
Step 1: Build Strong IT Foundations (3–6 Months)
Checklist:
- Learn networking basics
- Install Linux (Ubuntu or Kali in VM)
- Understand command line
- Study how websites work
- Basic scripting (Python)
Don’t rush.
Step 2: Learn How Attacks Actually Work
Focus on:
- SQL Injection
- XSS (Cross-Site Scripting)
- CSRF
- Broken authentication
- Misconfigurations
- Weak passwords
- Privilege escalation
But don’t just memorize definitions.
Break them in a lab environment.
Step 3: Practice in Controlled Labs
Platforms to use:
- Hack The Box
- TryHackMe
- PortSwigger (for Web Security Academy)
These simulate real-world environments.
In real assessments, what we usually see is misconfigured services — not movie-style hacks.
Step 4: Learn Documentation
No one talks about this.
But if you can’t explain a vulnerability clearly, your work has no impact.
Learn to write:
- Executive summary
- Technical details
- Risk severity
- Proof of concept
- Remediation steps
That’s what makes you employable.
Real-World Example: A Simple Misconfiguration
Let me share a story.
A mid-sized company hired us for a security audit.
Nothing fancy. Standard penetration test.
Within two hours, we found:
- An exposed admin panel
- Default credentials still active
- No rate limiting
No zero-days.
No advanced exploitation.
Just negligence.
The breach risk? Severe.
And this is common.
Cyber security is often about catching simple mistakes before attackers do.
Tools Used in Professional Ethical Hacking
Tools are secondary — but yes, you need them.
Here are industry standards:
Network Scanning
- Nmap
Web Testing
- Burp Suite
- OWASP ZAP
Exploitation Framework
- Metasploit
Password Testing
- John the Ripper
- Hydra
But listen carefully.
Running tools without understanding output is dangerous.
Top 20 Kali Tools Explained Practically — Real Ethical Hacker Workflow Guide
I’ve seen juniors report “critical vulnerabilities” that were false positives because they didn’t verify manually.
Common Beginner Mistakes I See All the Time
Let’s be honest.
Here’s what usually goes wrong:
🚨 Beginner Mistake Alert
- Skipping networking fundamentals
- Chasing certifications without skills
- Using tools blindly
- Trying illegal hacking
- Ignoring documentation
- Focusing only on offense, not defense
And the worst one?
Comparing yourself to someone with 10 years of experience.
This field takes time.
Pro Tip from Field Experience
Security is about reducing risk, not achieving perfection.
You will never make a system 100% secure.
Your job is to:
- Reduce attack surface
- Increase detection capability
- Improve response time
Perfection is marketing.
Risk reduction is reality.
Defensive Side of Cyber Security (Often Ignored)
Ethical hacking is exciting.
But defense is where long-term careers grow.
Learn:
- SIEM tools
- Log analysis
- Incident response
- Threat modeling
- Secure coding
- Patch management
During breach investigations, what matters most is:
- How quickly you detect
- How clearly you communicate
- How effectively you contain
Not how cool your terminal looks.
Mini Scenario: Incident Response at 2 AM
A finance company detects unusual outbound traffic.
We investigate.
Findings:
- Compromised user credentials
- Phishing email
- Lateral movement
- Data staging
The attacker wasn’t brilliant.
But the company lacked:
- MFA
- Network segmentation
- Monitoring alerts
Security failure is usually layered negligence.
Certifications (Do They Matter?)
Short answer: Yes — but not first.
Start with:
- Networking knowledge
- Linux basics
- Practical labs
Then consider:
- CEH
- OSCP
- Security+
But remember.
Certifications open doors.
Skills keep you inside.
Ethical and Legal Boundaries (Non-Negotiable)
Let me be crystal clear.
Ethical hacking without permission is illegal hacking.
Always:
- Get written authorization
- Define scope
- Respect data privacy
- Avoid destructive testing unless approved
Reputation in this industry is everything.
Lose integrity once — and you’re done.
Quick Action Plan for Beginners
If you’re serious, do this:
Week 1–4:
- Learn networking basics
- Install Linux in VM
Week 5–8:
- Practice command line daily
- Start TryHackMe labs
Week 9–12:
- Learn web vulnerabilities
- Practice on PortSwigger Academy
Month 4 onward:
- Build home lab
- Write reports
- Document findings publicly (without sensitive info)
Consistency beats intensity.
Quick Recap
Cyber Security and Ethical Hacking is:
- About mindset first
- Foundations second
- Tools third
- Documentation always
- Ethics non-negotiable
It is not:
- Movie hacking
- Instant money
- A shortcut career
It is discipline.
It is patience.
It is structured curiosity.
Frequently Asked Questions (Real Questions I Get From Students)
1. Can I start without a technical background?
Yes. But expect a slower start. Focus heavily on networking and Linux.
2. How long before I get a job?
Realistically?
6–18 months of consistent learning and lab work.
Anyone promising 3 months is overselling.
3. Is ethical hacking high-paying?
It can be.
But pay increases with:
- Experience
- Communication skills
- Specialization
4. Do I need expensive tools?
No.
Most powerful tools are open-source.
Skill matters more.
5. Is this career stressful?
Yes — during incidents.
But deeply rewarding when you prevent a breach.
Final Words from Experience
After 20 years in this field, here’s what I’ve learned:
The best security professionals are not the loudest.
They are:
- Curious
- Ethical
- Patient
- Relentless learners
If you commit long-term, Cyber Security and Ethical Hacking can become more than a career.
It becomes how you think.
And once you start thinking like an attacker…
You never really stop.