All Articles
Cybersecurity tutorials, hacking guides, and security research.
Social Media Footprinting Techniques Hackers Use (Complete Ethical Hacker Guide)
Learn real social media footprinting techniques hackers use in ethical hacking, OSINT investigations, and penetration testing workflows.
Top 20 Kali Tools Explained Practically — Real Ethical Hacker Workflow Guide
Learn the top 20 Kali Linux tools explained practically with real-world penetration testing examples, expert tips, workflows, and beginner guidance.
Kali Linux Commands List – 200+ Ethical Hacking Commands Cheat Sheet (2026)
Complete Kali Linux commands cheat sheet with 200+ essential ethical hacking commands explained by a cybersecurity expert with real-world penetration…
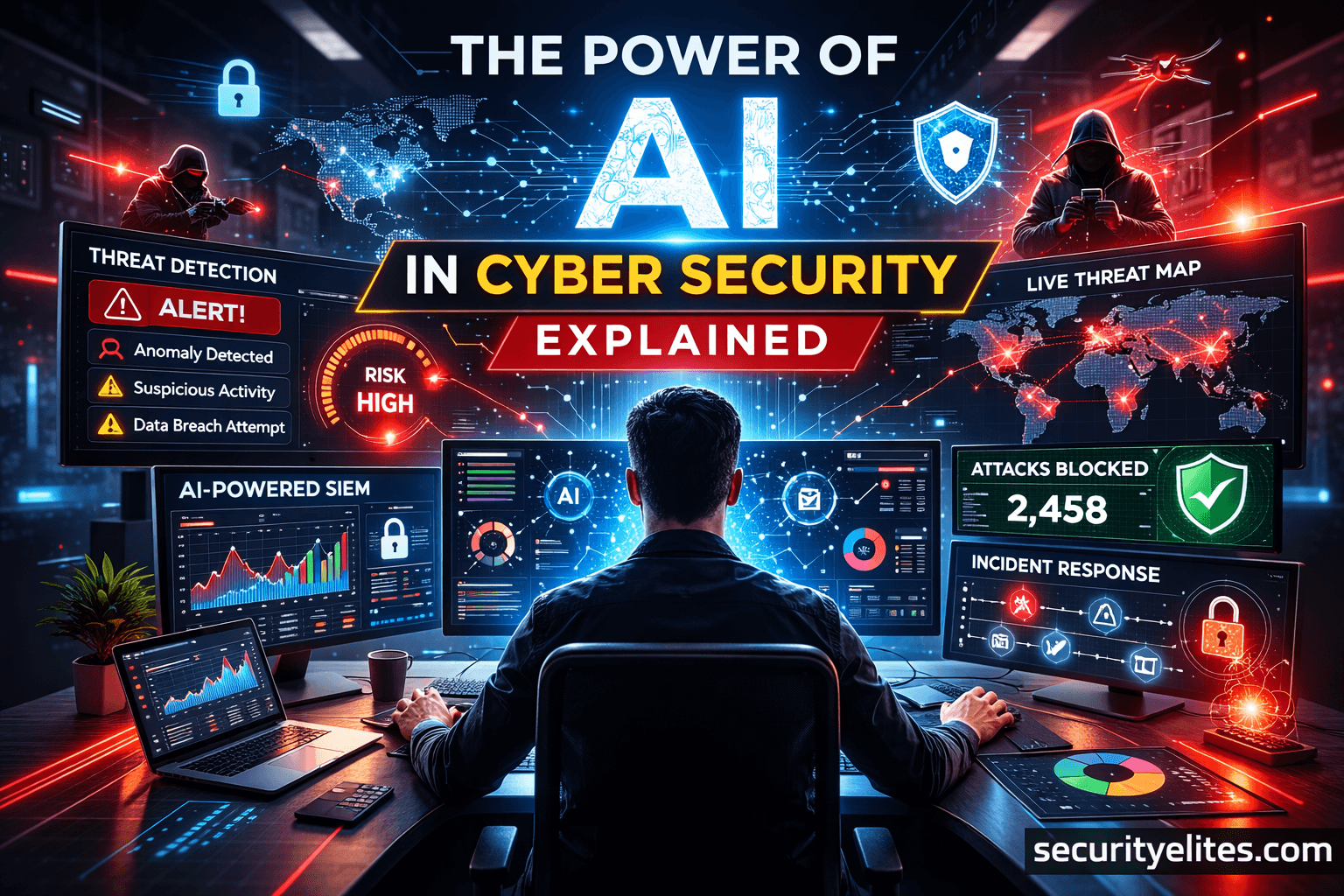
The Power of AI in Cyber Security – Beginner Friendly Guide (2026)
Learn how AI in Cyber Security works, real-world examples, tools used by professionals, and practical insights from 20 years of…
How to Start Bug Bounty With Zero Experience – Beginner to Pro Guide
Learn how to start bug bounty with zero experience using this practical, mentor-style guide. Step-by-step process, tools, mistakes, and pro…
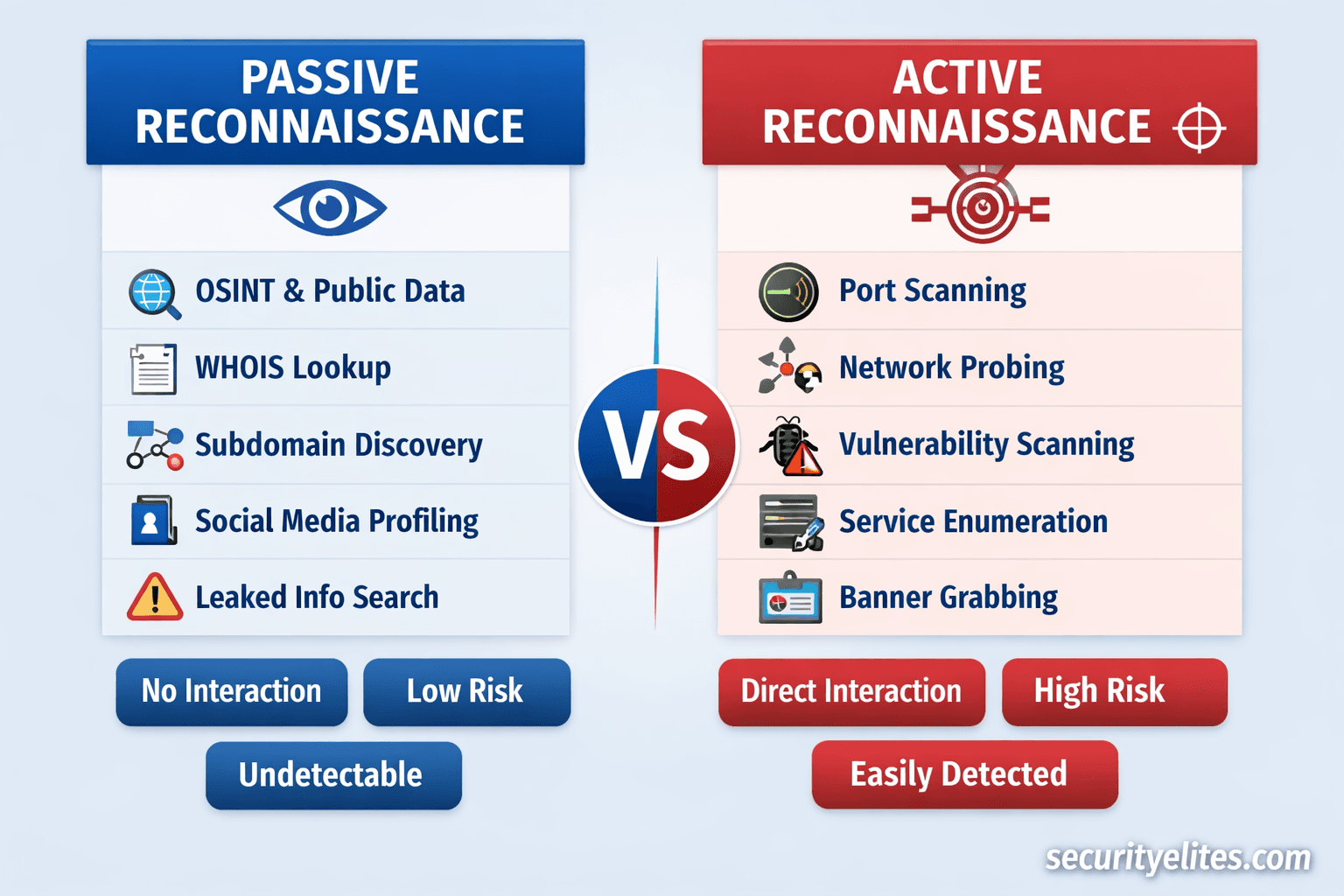
Passive vs Active Reconnaissance – Real Hacker Methods Explained
Master Passive vs Active Reconnaissance in ethical hacking. Learn real hacker methods, tools, workflows, detection risks, and pro field tips.