Password Cracking
20 articles
Social Engineering Scripts for Pentesters 2026 — Phishing, Vishing & Pretexting Playbooks
Real social engineering scripts for pentesters in 2026. Phishing lures, vishing call scripts, pretexting playbooks and SET automation used on…
How Ethical Hackers Break Into Smart Locks — Real Techniques Explained (2026)
How hackers break smart locks in 2026 — BLE replay attacks, Flipper Zero cloning, firmware extraction, rolling code bypass and…
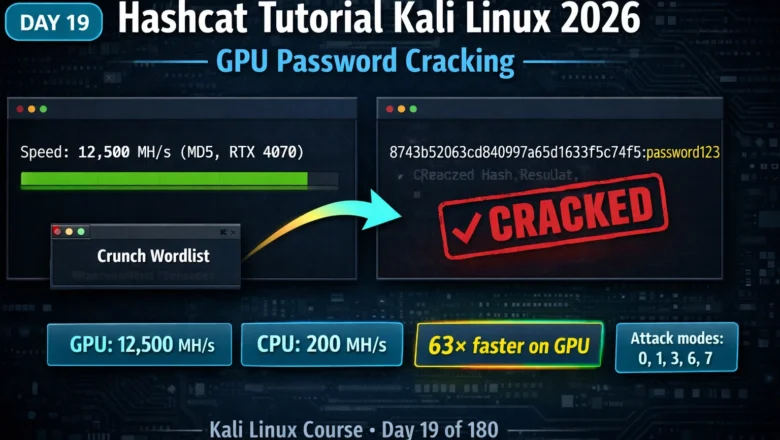
Kali Linux Day19: Hashcat Tutorial Kali Linux 2026 — GPU Password Cracking, Attack Modes & Benchmarking
Hashcat tutorial Kali Linux 2026 — master GPU password cracking with dictionary, mask, rule-based and combinator attack modes. Crack MD5,…
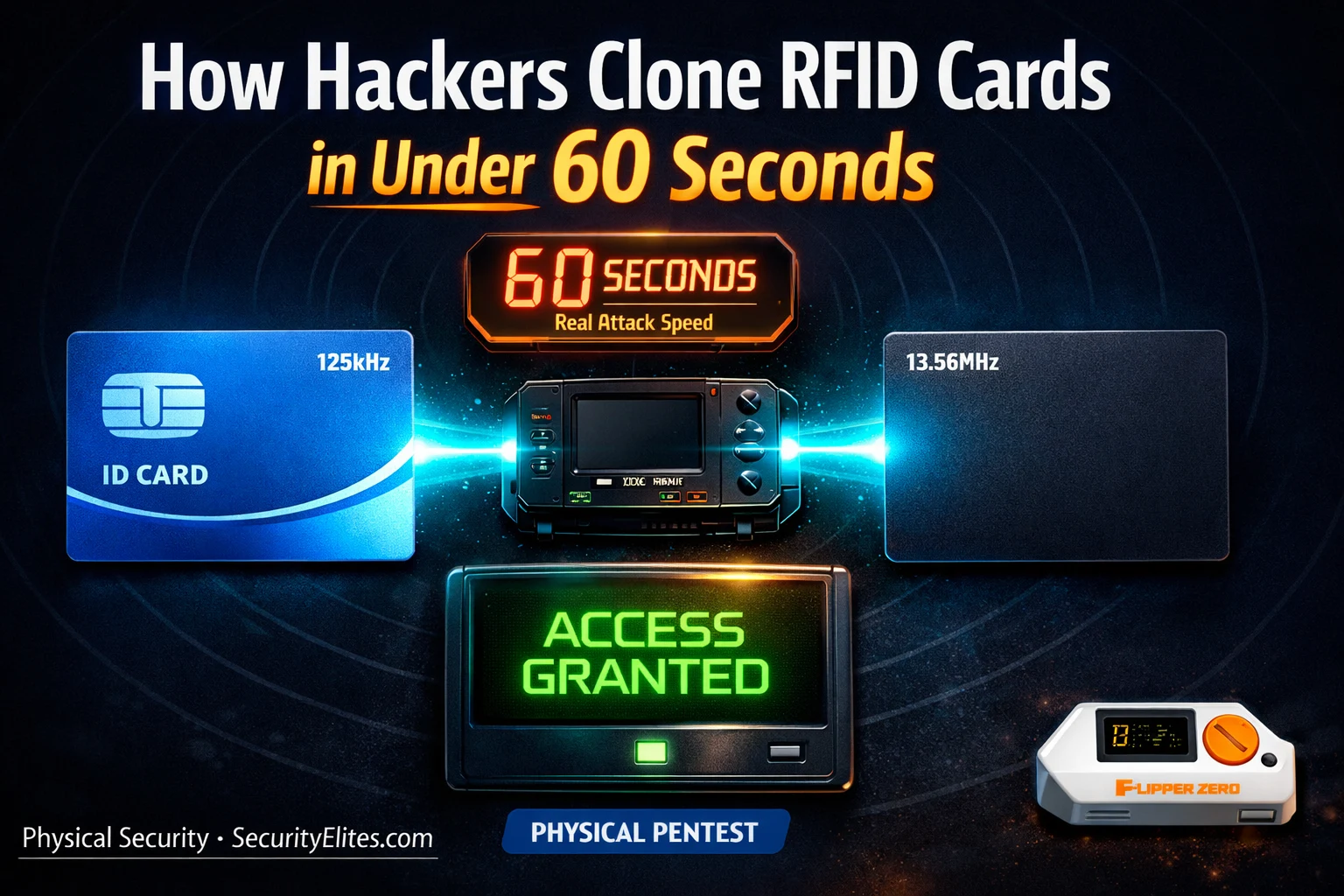
How Hackers Clone RFID Cards in Under 60 Seconds — The Hardware They Use
How hackers clone rfid cards 2026 — the real hardware and software used to copy access cards, hotel key cards…
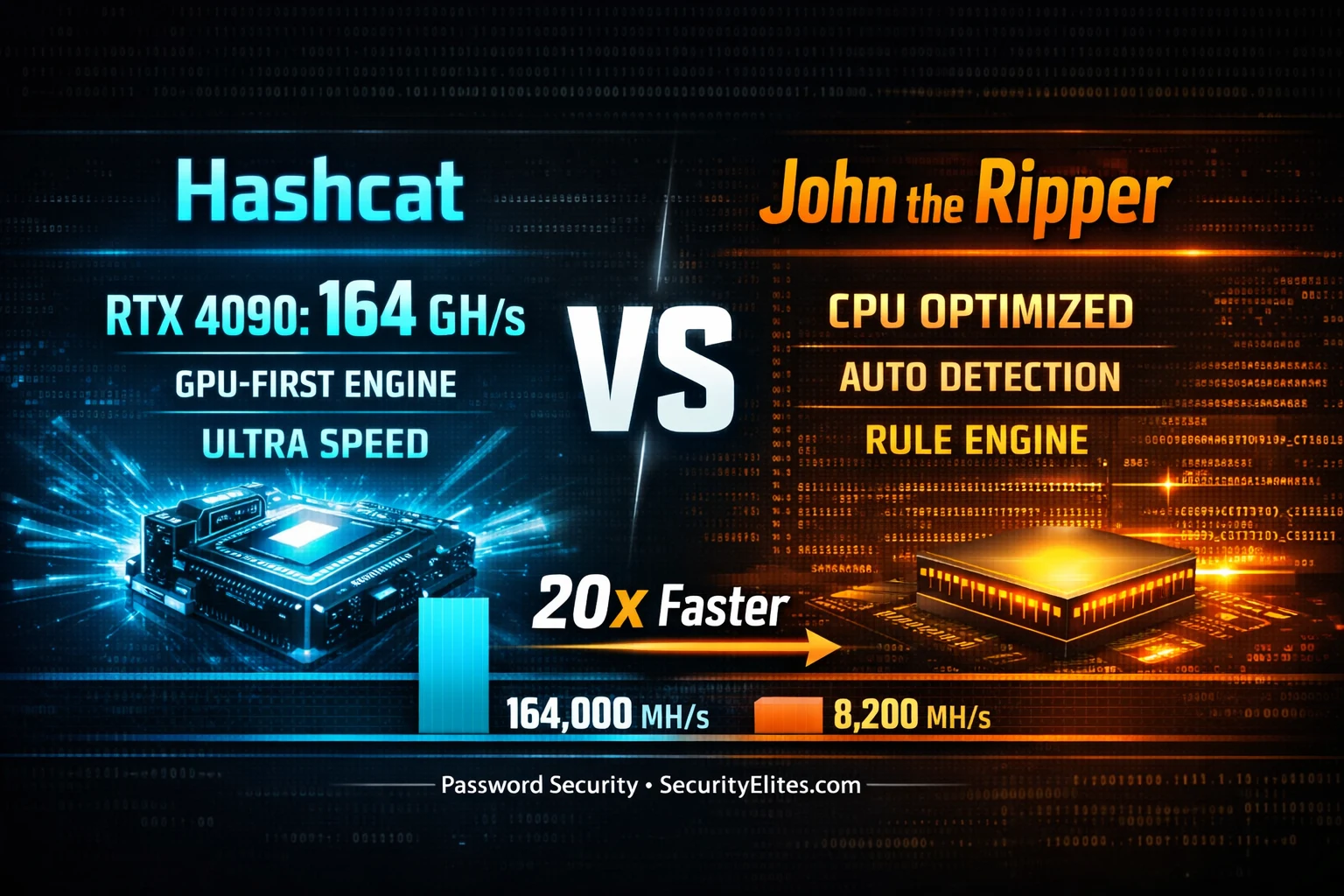
Hashcat vs John the Ripper 2026 — The 20x Speed Gap No One Talks About
Hashcat vs John the Ripper 2026 — real benchmark comparison on GPU vs CPU for MD5, NTLM, bcrypt and SHA256.…
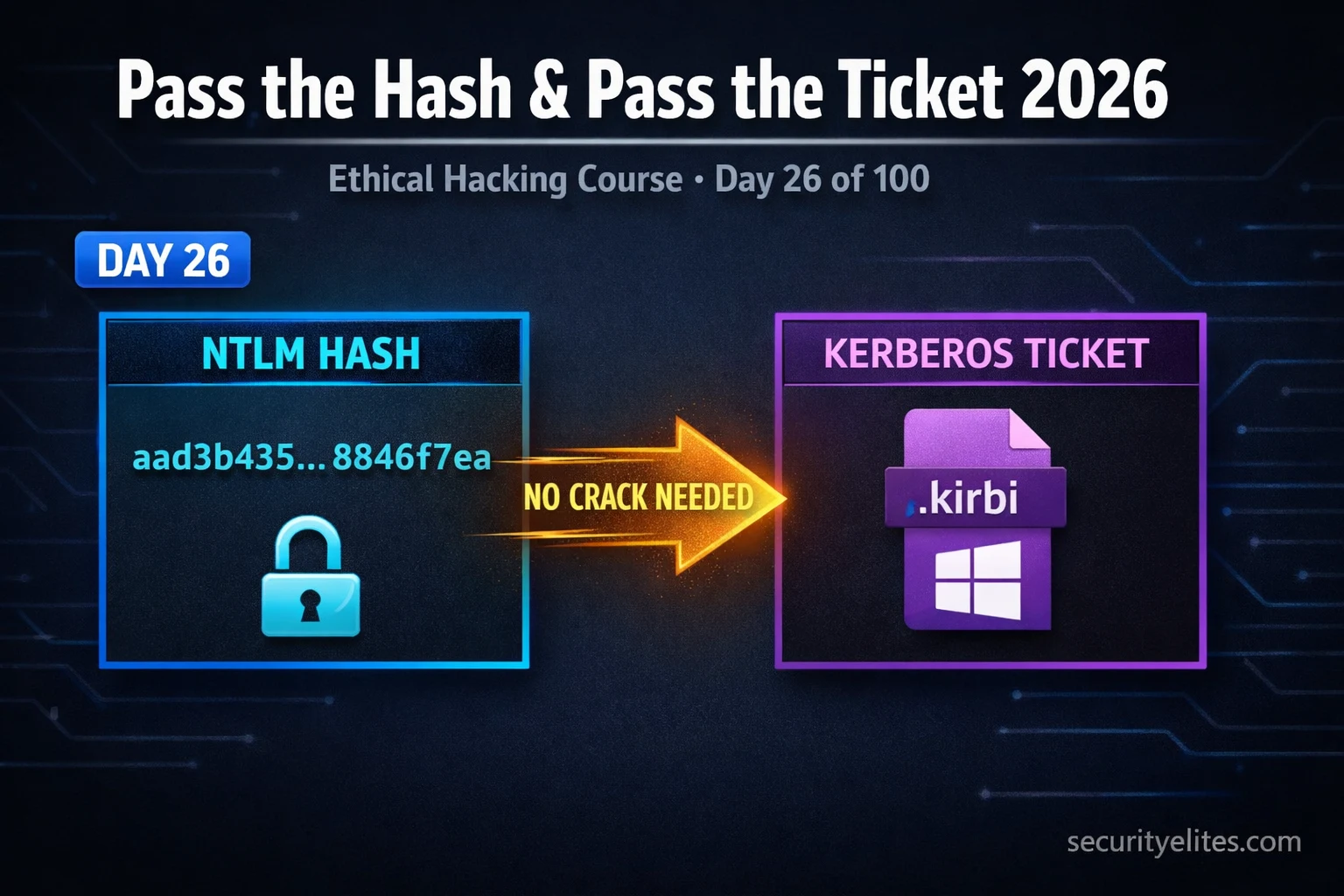
Day 26: Pass the Hash & Pass the Ticket 2026 — Lateral Movement With NTLM & Kerberos
Pass the hash & pass the ticket 2026 — exploit NTLM hashes and Kerberos tickets for lateral movement in Active…
Day 25: Kerberoasting 2026 — Attack & Defend Service Account Passwords in Active Directory
Master Kerberoasting in 2026 — request Kerberos service tickets, extract TGS hashes, crack offline with Hashcat, and detect attacks as…
Kali Linux Day 11: Aircrack-ng Tutorial 2026 — Crack WiFi Passwords & Audit WPA2 Security
Aircrack-ng tutorial in Kali Linux 2026 — capture WPA2 handshakes, run dictionary attacks, audit wireless security. Day 11 complete guide…
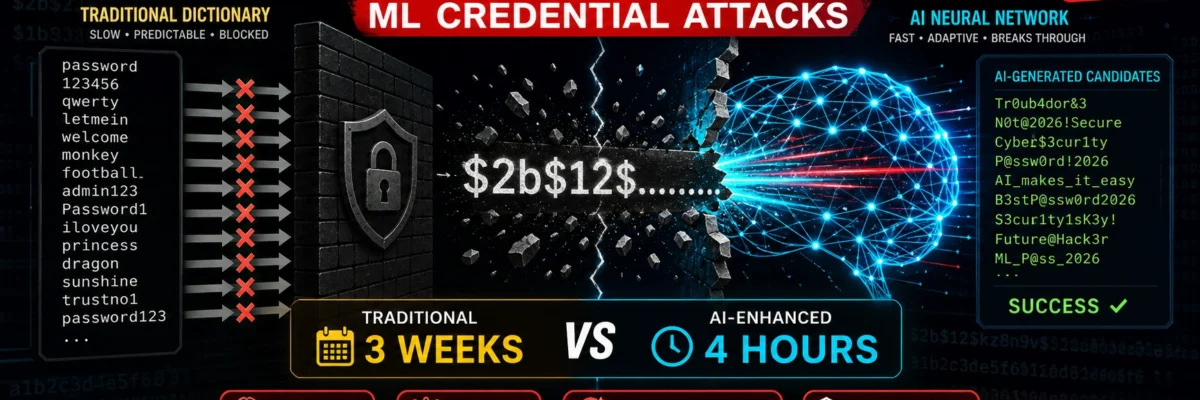
Identity Based Attacks 2026 — Credential Abuse, MFA Bypass & Account Takeover (Complete Guide)
Identity based attacks are the #1 breach vector in 2026. Learn credential stuffing, password spraying, MFA fatigue, pass-the-cookie, SIM swapping,…