Passwords are still the most widely used authentication mechanism on the internet. Whether you are logging into your email account, accessing an online banking portal, or connecting to a corporate network, passwords serve as the first line of defense against unauthorized access.
However, passwords are also one of the weakest security controls when poorly implemented or chosen. Attackers constantly develop new ways to break authentication systems and gain access to protected data. One of the most common techniques used in cyber attacks is known as password cracking.
Password cracking refers to the process of recovering passwords from stored data or encrypted password hashes using different attack techniques. These techniques range from simple guessing methods to highly advanced attacks using powerful GPUs and distributed computing systems.
Although password cracking is often associated with hackers and cybercriminals, it also plays an important role in ethical hacking and cybersecurity testing. Security professionals use password cracking tools to identify weak passwords and improve system security.
Understanding password cracking is essential for anyone interested in:
- Cybersecurity
- Ethical hacking
- Penetration testing
- Network security
- Online privacy
Organizations also need to understand how password attacks work in order to protect their systems and sensitive information from modern cyber threats.
In this comprehensive guide, we will explore everything you need to know about password cracking, including the techniques attackers use, the tools used by ethical hackers, real-world breach examples, and proven methods to prevent password attacks.
By the end of this article, you will clearly understand how password cracking works and how to defend against it.
Table of Contents
What is Password Cracking?
Password cracking is the process of discovering or recovering a password from its stored or encrypted form.
Most modern applications do not store passwords in plain text. Instead, they store hashed passwords, which are encrypted representations of the original password.
When a user creates an account, the password is converted into a hash using a mathematical function called a hashing algorithm.
For example:
Password:
security123
Hash:
482c811da5d5b4bc6d497ffa98491e38
The system stores only the hash value. When the user logs in, the entered password is hashed again and compared to the stored hash.
If both hashes match, the user is authenticated.
Password cracking occurs when attackers attempt to recover the original password from its hash.
Hackers achieve this by testing large numbers of possible passwords until they find one that produces the same hash.
Password cracking attacks may target:
- Online login systems
- Password databases
- WiFi networks
- Encrypted files
- Network authentication protocols
These attacks can be performed manually, but most modern password cracking attempts rely on automated tools and high-performance computing systems.
Why Password Cracking Matters in Cybersecurity
Password-based authentication remains one of the most common security mechanisms used by websites, applications, and organizations worldwide. Unfortunately, weak passwords continue to be a major vulnerability.
Studies have shown that a significant percentage of users still choose extremely predictable passwords such as:
123456
password
qwerty
admin
letmein
Attackers take advantage of these weak password habits to gain unauthorized access to systems.
According to cybersecurity research reports, more than 80% of data breaches involve compromised passwords.
Password cracking plays a central role in many cyber attacks, including:
- Corporate network intrusions
- Account takeovers
- Data breaches
- Ransomware attacks
- Identity theft
In many cases, a single compromised password can allow attackers to access entire networks.
For example, if an employee uses a weak password and attackers successfully crack it, they may gain access to internal systems, confidential documents, and sensitive business data.
Understanding password cracking techniques helps organizations design stronger authentication systems and enforce better password policies.
How Fast Can Hackers Crack Your Password?
Many people underestimate how quickly modern computers can break weak passwords.
With the help of GPU acceleration, password cracking tools can test billions of password combinations per second.
Consider the following examples.
Weak password:
password123
Estimated cracking time: Less than one second
Moderately strong password:
Cyber2025
Estimated cracking time: A few minutes
Strong password:
T8$kL!92@xPq
Estimated cracking time: Millions of years
This example demonstrates why password complexity is extremely important in modern cybersecurity.
How Passwords Are Stored in Modern Systems
To understand password cracking, it is important to first understand how passwords are stored.
Modern systems rely on hashing algorithms to protect passwords.
A hashing algorithm converts input data into a fixed-length output known as a hash value.
Example:
Password:
cybersecure
Hash:
f3abb86bd34cf4d52698f14c0da1dc60
Hash functions have several important properties:
- They are one-way functions
- The same input always produces the same output
- Small input changes produce completely different outputs
- It is extremely difficult to reverse the hash
Because of these properties, hashing is widely used to store passwords securely.
However, attackers attempt to reverse or guess passwords through password cracking techniques.
What is Password Hashing?
Password hashing is the process of transforming a password into a hashed value using a cryptographic algorithm.
For example:
Password: hacking123
After hashing with MD5:
2d3536a9d5b3b47e9c1d0dce274164a5
Instead of storing the password itself, the system stores the hash.
When a user logs in, the entered password is hashed again and compared to the stored hash.
If both hashes match, authentication succeeds.
Common Password Hashing Algorithms
Several hashing algorithms have been used over the years.
Some are now considered insecure because modern hardware can crack them quickly.
1. MD5
MD5 was once widely used for password hashing.
However, MD5 is now considered broken because attackers can crack MD5 hashes extremely quickly using modern hardware.
A powerful GPU can compute billions of MD5 hashes per second.
For this reason, MD5 should never be used to store passwords.
2. SHA-1
SHA-1 is another older hashing algorithm that was once widely used.
Although SHA-1 is stronger than MD5, it is no longer considered secure for password storage.
Major companies and security organizations have deprecated SHA-1.
3. bcrypt
bcrypt was designed specifically for password hashing.
It includes features that slow down hashing operations, making brute-force attacks significantly more difficult.
bcrypt also supports adaptive cost factors, which allow developers to increase hashing difficulty as hardware becomes more powerful.
4. Argon2
Argon2 is considered one of the most secure password hashing algorithms available today.
It was the winner of the Password Hashing Competition and is designed to resist GPU-based cracking attacks.
Argon2 provides strong protection against modern password cracking techniques.
The Role of Salting in Password Security
Another important security concept is password salting.
A salt is a random value added to the password before hashing.
Example:
Password:
password123
Salt:
x9@7!
Combined value:
password123x9@7!
The resulting hash becomes unique even if two users choose the same password.
Salting prevents attackers from using precomputed hash databases known as rainbow tables.
Without salting, attackers could quickly crack large numbers of passwords.
Offline vs Online Password Cracking
Password cracking attacks are generally divided into two categories.
Online Password Cracking
Online attacks target login systems directly.
Examples include:
- SSH login attacks
- Web login brute-force attacks
- FTP authentication attacks
These attacks attempt to guess passwords by repeatedly sending login requests.
Security systems often detect and block these attacks using rate limiting and account lockouts.
Offline Password Cracking
Offline attacks occur when attackers obtain password hashes from a compromised database.
Because the attacker already has the hashes, they can attempt millions or billions of password guesses without interacting with the target system.
Offline password cracking is significantly faster and more dangerous than online attacks.
12 Most Powerful Password Cracking Techniques Used by Hackers
Understanding the most common password cracking techniques is essential for cybersecurity professionals and developers. These techniques are used both by malicious attackers and by ethical hackers performing security testing.
Each technique has different levels of complexity, speed, and effectiveness. Some methods rely on guessing common passwords, while others use advanced computing power to test billions of password combinations per second.
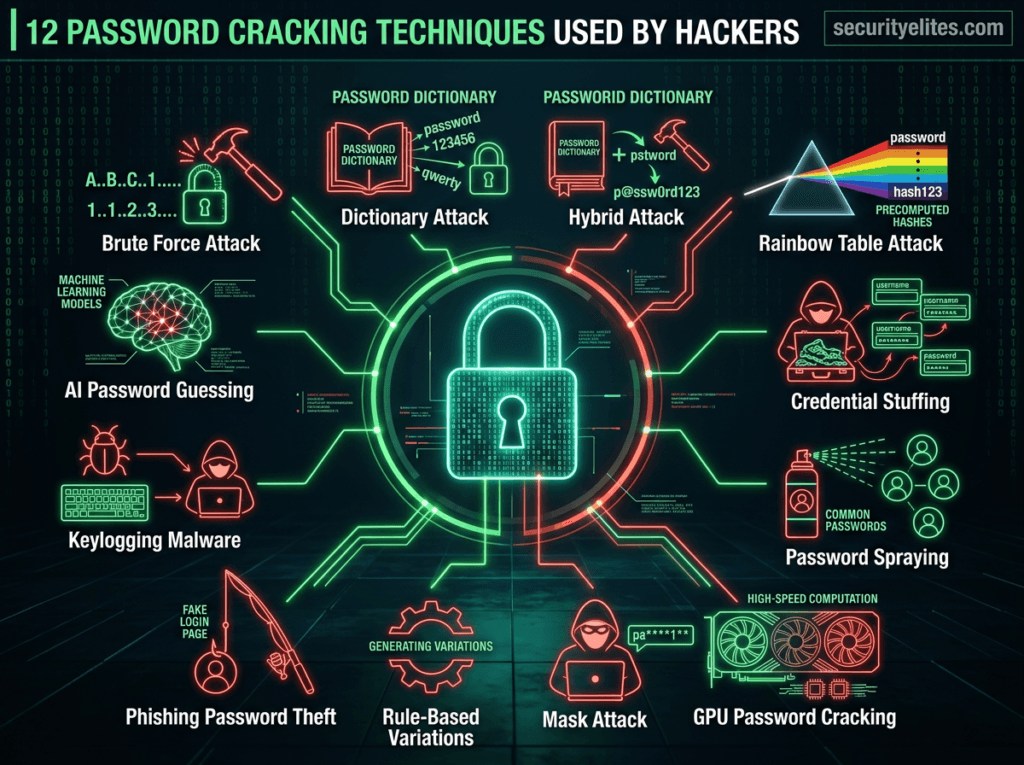
Below are the most widely used password cracking techniques in modern cybersecurity attacks.
1. Brute Force Password Cracking
Brute force password cracking is one of the oldest and simplest password attack techniques.
In a brute force attack, the attacker attempts every possible combination of characters until the correct password is discovered.
For example, if a password contains only lowercase letters, the attacker may attempt combinations like:
a
aa
aaa
abc
abcd
abcde
Eventually, the correct password will be found.
Advantages of Brute Force Attacks
- Guaranteed success if enough time is available
- Does not require prior knowledge of the password
- Works against any password
Disadvantages
- Extremely slow for long passwords
- Easily detected by modern security systems
- Inefficient for strong passwords
Example Scenario
Suppose an attacker targets an SSH server and attempts to guess the password for the user admin.
A brute force attack tool will automatically try thousands of password combinations until the correct one is discovered.
Modern security defenses like account lockouts and rate limiting can reduce the effectiveness of brute force attacks.
2. Dictionary Password Cracking
Dictionary attacks are one of the most efficient password cracking techniques.
Instead of trying every possible character combination, attackers use a predefined list of commonly used passwords.
These lists are known as wordlists.
Example passwords in a dictionary attack:
password
123456
admin
qwerty
letmein
football
iloveyou
Because millions of people choose weak passwords, dictionary attacks often succeed quickly.
Popular Wordlists Used by Hackers
One of the most famous password lists is:
rockyou.txt
This wordlist contains over 14 million real passwords leaked from a previous data breach.
Cybersecurity professionals frequently use rockyou.txt during penetration testing to simulate real attacks.
3. Hybrid Password Cracking
Hybrid attacks combine the power of dictionary attacks and brute force attacks.
In this technique, attackers start with a dictionary word and then modify it using different patterns.
Examples:
password1
password123
admin2025
welcome123
Many users create passwords using predictable patterns such as:
- word + numbers
- name + birth year
- company name + year
Hybrid attacks are extremely effective because they mimic common human password behaviors.
4. Rainbow Table Attack
Rainbow table attacks target password hashes stored in databases.
A rainbow table is a precomputed database containing millions of password hashes.
Instead of calculating hashes during an attack, the attacker simply looks up the hash in the table.
Example rainbow table entry:
| Password | Hash |
|---|---|
| 123456 | e10adc3949ba59abbe56e057f20f883e |
| admin | 21232f297a57a5a743894a0e4a801fc3 |
If the attacker finds a matching hash in the rainbow table, the original password is revealed instantly.
Why Salting Prevents Rainbow Table Attacks
When passwords are salted before hashing, rainbow tables become useless because each password hash becomes unique.
5. Credential Stuffing
Credential stuffing is a modern password attack that exploits password reuse.
Attackers obtain stolen username-password combinations from previous data breaches.
They then attempt to use those credentials on other websites.
Example stolen credentials:
email: user@gmail.com
password: password123
If the victim reused the same password on multiple websites, attackers can gain access to multiple accounts.
Credential stuffing attacks are responsible for millions of account takeovers every year.
6. Password Spraying
Password spraying is a variation of brute force attacks.
Instead of targeting one account with many passwords, attackers attempt one common password across many accounts.
Example attack:
admin → password123
john → password123
sarah → password123
alex → password123
This technique helps attackers avoid account lockout mechanisms.
7. GPU Password Cracking
Modern password cracking tools use Graphics Processing Units (GPUs) to dramatically increase cracking speed.
A powerful GPU can attempt billions of password guesses per second.
Large password cracking setups may include:
- multiple GPUs
- dedicated cracking rigs
- cloud computing clusters
These systems are capable of cracking weak passwords extremely quickly.
8. Mask Attack
Mask attacks are used when attackers know partial information about a password.
Example password pattern:
CompanyName2025
The attacker knows the password format and only needs to guess certain characters.
Example mask pattern:
????2025
Mask attacks significantly reduce the number of password combinations required.
9. Rule-Based Password Cracking
Rule-based attacks modify dictionary words using predefined transformation rules.
Examples:
password → Password
password → P@ssword
password → password123
These transformations mimic common password variations used by real users.
Password cracking tools like Hashcat include powerful rule engines that automate these modifications.
10. Phishing-Based Password Harvesting
Not all password attacks involve complex algorithms.
Sometimes attackers simply trick users into revealing their passwords.
Phishing attacks use fake login pages that look identical to legitimate websites.
When users enter their credentials, attackers capture the passwords.
Phishing remains one of the most successful password theft methods.
11. Keylogging Attacks
Keyloggers are malicious programs that record keystrokes on a victim’s computer.
If a user types their password, the keylogger captures it and sends it to the attacker.
Keylogging malware is often delivered through:
- malicious downloads
- phishing emails
- infected software
12. AI-Based Password Guessing
Artificial intelligence is now being used in password cracking research.
AI models analyze leaked password databases and learn common password patterns.
Examples:
Name + Birthyear
PetName + 123
CityName + 2024
AI can predict these patterns and generate highly effective password guesses.
This dramatically increases the success rate of password cracking attacks.
Most Powerful Password Cracking Tools Used by Ethical Hackers
Cybersecurity professionals rely on specialized password cracking tools to test password strength and identify vulnerabilities in authentication systems.
These tools are commonly used during penetration testing, red team exercises, and cybersecurity audits.
Below are the most widely used password cracking tools in the cybersecurity industry.
Hashcat
Hashcat is widely considered the fastest password cracking tool in the world.
It is capable of performing billions of password guesses per second using GPU acceleration.
Hashcat supports more than 300 different hashing algorithms, including:
- MD5
- SHA1
- SHA256
- bcrypt
- NTLM
- WPA/WPA2
Key Features
• GPU acceleration
• Advanced rule-based attacks
• Hybrid attack support
• Mask attack support
• Distributed cracking capability
Example Hashcat Command
hashcat -m 0 -a 0 hashes.txt rockyou.txt
Explanation:
- -m 0 specifies the hash type (MD5)
- -a 0 specifies dictionary attack mode
- hashes.txt contains password hashes
- rockyou.txt is the wordlist
Hashcat is widely used by:
- penetration testers
- ethical hackers
- digital forensics investigators
John the Ripper
John the Ripper is another powerful password cracking tool used by cybersecurity professionals.
It supports many different password hash formats and provides automatic password cracking techniques.
Key Features
• Automatic password rule generation
• Multiple cracking modes
• Supports hundreds of hash types
• Open-source software
Example Command
john --wordlist=rockyou.txt hashes.txt
John the Ripper attempts to match password hashes using the provided wordlist.
Hydra
Hydra is designed for online password attacks.
Instead of cracking hashes, Hydra attempts to log into real services using different username and password combinations.
Hydra supports many protocols including:
- SSH
- FTP
- HTTP
- RDP
- Telnet
- MySQL
Example Hydra Command
hydra -l admin -P passwords.txt ssh://192.168.1.10
Explanation:
- -l admin specifies the username
- -P passwords.txt contains password list
- ssh://192.168.1.10 is the target system
Hydra is widely used during penetration testing of authentication systems.
Aircrack-ng
Aircrack-ng is a suite of tools used for WiFi password cracking.
It works by capturing wireless packets and analyzing them to recover network passwords.
Aircrack-ng supports attacks against:
- WEP networks
- WPA/WPA2 networks
Typical Workflow
- Capture wireless packets
- Extract handshake data
- Run dictionary attack
Aircrack-ng is commonly used for wireless security testing.
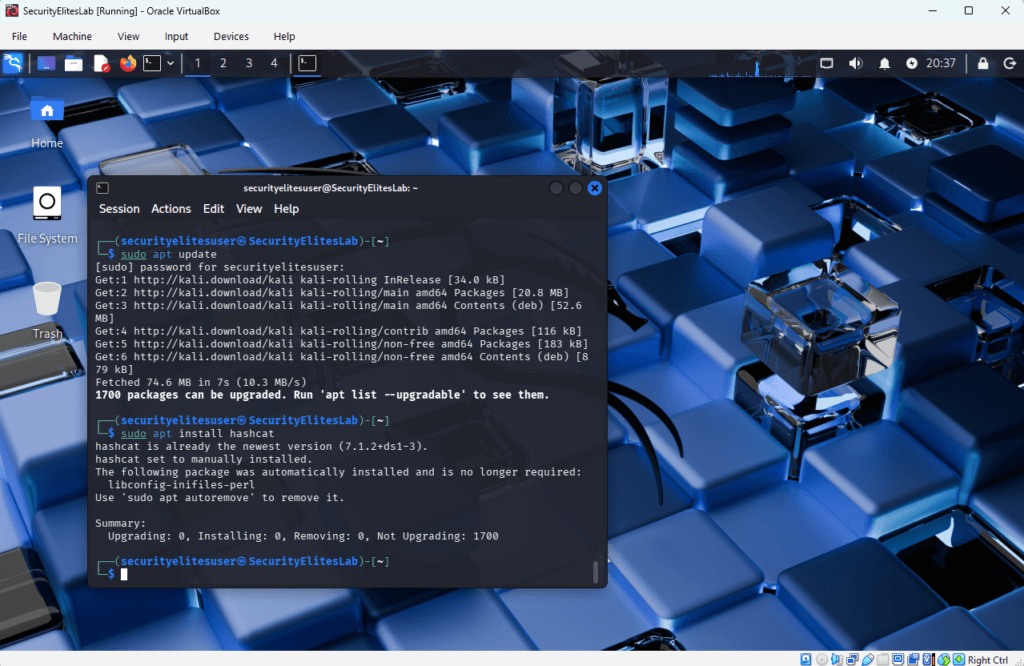
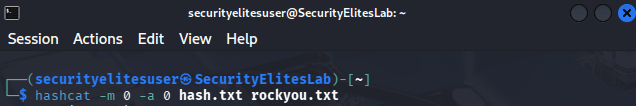
SecurityElites Hands on Tutorial : Password Cracking Lab (Kali Linux Tutorial)
This simple lab demonstrates how password cracking works using Hashcat in Kali Linux.
This section is designed so even beginners can understand the process.
Step 1: Install Hashcat
In Kali Linux, Hashcat is usually pre-installed.
If not, install it using:
sudo apt update
sudo apt install hashcat
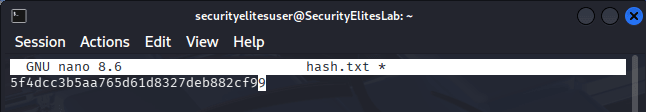
Step 2: Create a Password Hash
Create a sample MD5 hash file.
Example password:
password
MD5 hash:
5f4dcc3b5aa765d61d8327deb882cf99
Create and Save it in a file:
nano hash.txt
Paste the hash.
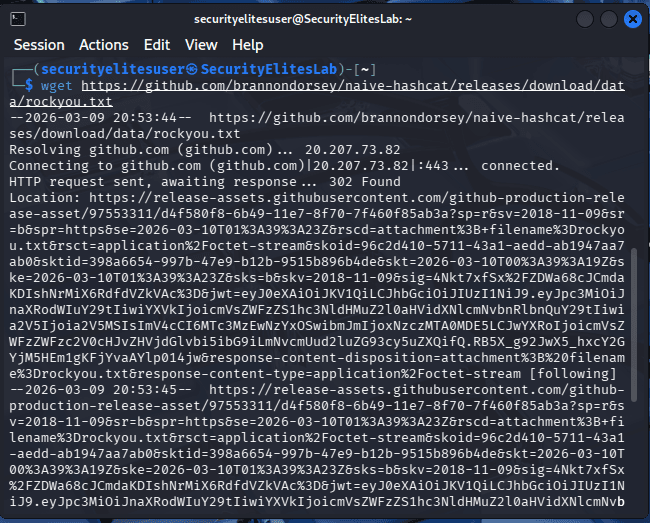
Step 3: Download Wordlist
Most password cracking labs use the rockyou.txt wordlist.
Unzip the file in Kali Linux:
sudo gzip -d /usr/share/wordlists/rockyou.txt.gz
If you get an error like file or directory not found just run below command.
wget https://github.com/brannondorsey/naive-hashcat/releases/download/data/rockyou.txt
Step 4: Run Hashcat Attack
Now run Hashcat using the wordlist.
hashcat -m 0 -a 0 hash.txt rockyou.txt
Hashcat will begin testing passwords from the wordlist.
Step 5: View Cracked Password
After the attack completes view the password.
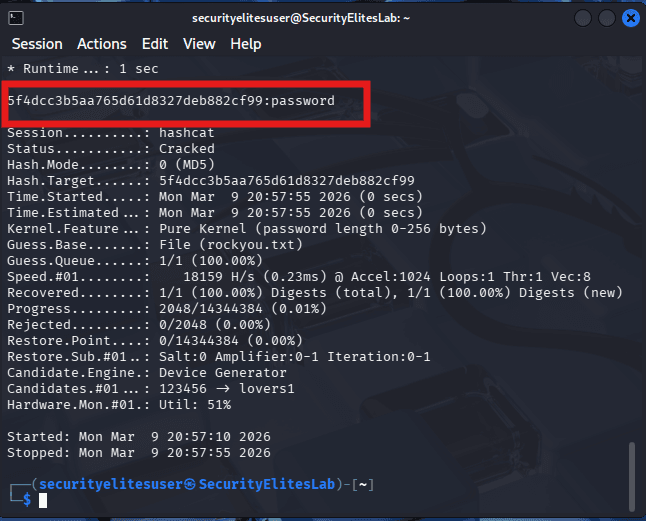
This simple lab demonstrates how quickly weak passwords can be cracked.
Why Weak Passwords Are Dangerous
Weak passwords create several security risks.
These include:
- account takeover
- financial fraud
- identity theft
- corporate espionage
- ransomware attacks
Even large organizations can suffer severe damage if attackers crack employee passwords.
How to Prevent Password Cracking Attacks
Preventing password cracking requires a combination of strong password policies, secure authentication systems, and user education.
According to the OWASP Password Security Guidelines, organizations should enforce strong password policies and multi-factor authentication to prevent password cracking attacks.
Below are the most effective prevention methods.
1. Use Strong Passwords
Strong passwords should contain:
- uppercase letters
- lowercase letters
- numbers
- special characters
Example strong password:
T9$kL!92@xPq
Avoid predictable passwords such as:
password123
admin
qwerty
2. Enable Multi-Factor Authentication (MFA)
Multi-factor authentication adds an additional security layer.
Even if attackers crack the password, they still cannot access the account without the second verification factor.
Examples of MFA:
- OTP codes
- authenticator apps
- hardware security keys
3. Use Password Managers
Password managers generate and store complex passwords securely.
Popular password managers include:
- Bitwarden
- 1Password
- Dashlane
4. Implement Account Lockouts
Systems should automatically lock accounts after several failed login attempts.
Example:
5 failed attempts → account locked for 30 minutes
This significantly reduces brute force attacks.
5. Use Secure Password Hashing
Developers should use modern hashing algorithms such as:
- bcrypt
- Argon2
- scrypt
Avoid outdated algorithms like:
- MD5
- SHA1
6. Monitor Suspicious Login Activity
Security teams should monitor login patterns and detect unusual activity such as:
- multiple failed login attempts
- login attempts from unusual locations
- rapid login requests from automated scripts
The Future of Password Security
Passwords are slowly being replaced by passwordless authentication technologies.
These technologies include:
- biometrics
- hardware security keys
- passkeys
- mobile authentication
Major companies like Google, Apple, and Microsoft are already implementing passwordless login systems.
Frequently Asked Questions (SEO FAQ Schema)
What is password cracking?
Password cracking is the process of recovering passwords from encrypted hashes using techniques such as brute force attacks, dictionary attacks, and hybrid attacks.
What is the fastest password cracking tool?
Hashcat is widely considered the fastest password cracking tool because it supports GPU acceleration.
Is password cracking illegal?
Password cracking is illegal if performed without permission. However, it is legal when conducted as part of ethical hacking or penetration testing.
How long does it take to crack a password?
Weak passwords can be cracked in seconds, while strong passwords may take millions of years using brute force techniques.
Key Takeaways
Password cracking remains one of the most common techniques used in cyber attacks. Hackers constantly develop new methods to break weak authentication systems and gain unauthorized access to accounts.
Understanding how password cracking works allows individuals and organizations to build stronger defenses against cyber threats.
Key takeaways from this guide include:
- Weak passwords are a major security vulnerability
- Modern password cracking tools can test billions of passwords per second
- Multi-factor authentication significantly improves security
- Secure password hashing algorithms protect stored credentials
As cybersecurity threats continue to evolve, organizations must adopt stronger authentication practices and educate users about password security.
By implementing strong passwords, enabling multi-factor authentication, and using modern hashing algorithms, individuals and businesses can significantly reduce the risk of password cracking attacks.




