Malware is malicious software created by hackers to steal data, spy on victims, destroy systems, or take control of devices. From ransomware attacks targeting hospitals to spyware stealing passwords, malware comes in many different forms.
Understanding the types of malware used in real attacks is essential for anyone interested in cybersecurity, ethical hacking, or online safety.
In this complete guide by SecurityElites, you will learn:
- The 25 most dangerous types of malware
- How each malware type works
- Which malware types hackers use most often
By the end of this guide, you will understand how modern cyber attacks operate and how to protect your systems from malware threats.
Table of Contents
25 Most Dangerous types of Malware Hackers Use
Cybercriminals use many different types of malware depending on the goal of their attack. Some malware is designed to steal sensitive information, while others are created to destroy data, spy on victims, or gain full control over systems.
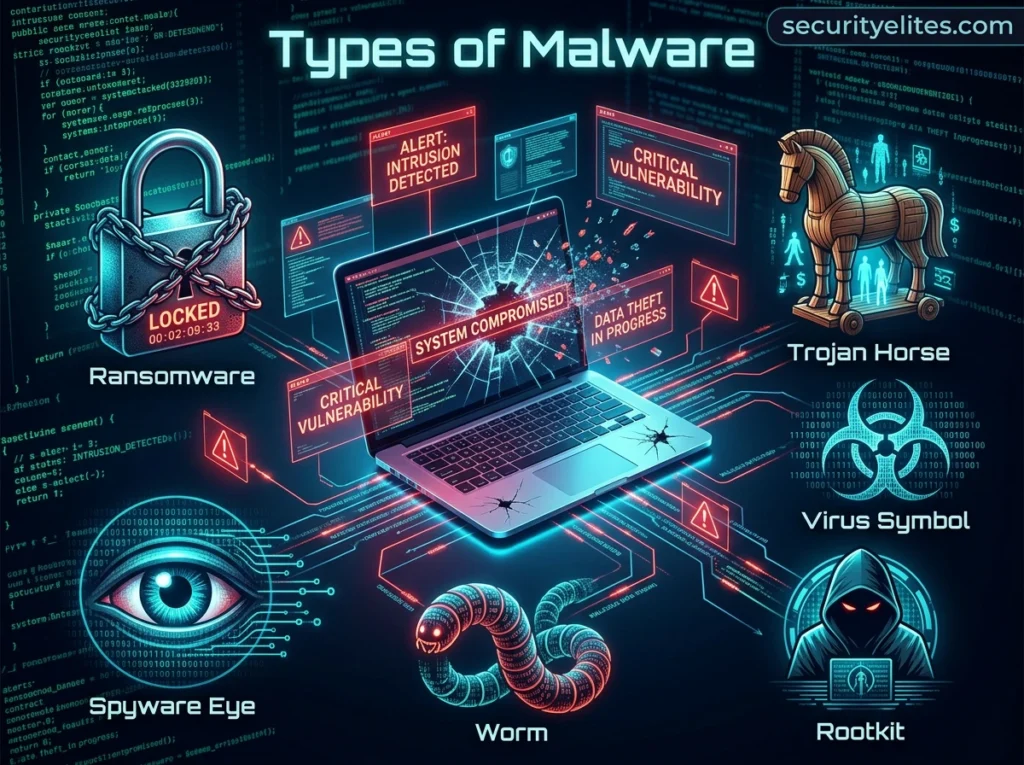
Understanding the different types of malware used in real attacks helps cybersecurity professionals detect threats early and protect networks from compromise. Below are 25 of the most common malware types hackers use in modern cyber attacks.
1. Virus
A computer virus is one of the earliest and most well-known types of malware used in cyber attacks. A virus attaches itself to legitimate files or programs and spreads when the infected file is opened or executed. Once activated, the virus can replicate itself and infect other files on the same system. In many cases, viruses also attempt to spread to other computers through shared drives, email attachments, or removable storage devices. Some viruses simply slow down system performance, while others can corrupt data, delete files, or damage operating systems. Viruses are commonly spread through malicious downloads, infected software installers, or phishing email attachments.
2. Worm
A worm is a type of malware that spreads automatically across networks without requiring any action from the user. Unlike viruses, worms do not need to attach themselves to a file or program. Instead, they exploit security vulnerabilities in operating systems, network protocols, or software applications to infect other systems. Once a worm enters a network, it can scan for other vulnerable devices and infect them rapidly. This ability to self-replicate allows worms to spread very quickly across organizations and even across the internet. Worm outbreaks can overload networks, slow down systems, and cause widespread service disruptions.
3. Trojan Horse
A Trojan horse, often called a Trojan, is malware disguised as legitimate software or files. Users may unknowingly install Trojans when downloading applications, opening attachments, or installing fake software updates. Once the Trojan is installed, it performs hidden malicious activities in the background. In many cases, Trojans create a backdoor that allows attackers to access the infected system remotely. This remote access can be used to steal files, monitor activity, or install additional malware. Trojans are widely used by cybercriminals because they rely on social engineering rather than technical vulnerabilities to gain access to systems.
4. Ransomware
Ransomware is one of the most damaging types of malware used in modern cyber attacks. It works by encrypting files on an infected system and preventing the victim from accessing them. After encryption is complete, the malware displays a message demanding payment in exchange for the decryption key needed to unlock the files. Ransomware attacks have targeted hospitals, government agencies, corporations, and individual users. In many cases, victims are asked to pay the ransom using cryptocurrency. Even after payment, attackers may not provide the decryption key, making ransomware a highly destructive cyber threat.
5. Spyware
Spyware is malware designed to secretly monitor user activity and collect sensitive information. Once installed on a device, spyware can track browsing history, capture login credentials, record keystrokes, and monitor online activity. The collected information is transmitted to attackers without the user’s knowledge. Cybercriminals often use spyware to steal financial data, personal information, and corporate secrets. Spyware infections usually occur through malicious downloads, infected websites, or bundled software installers. Because spyware operates silently in the background, victims often remain unaware that their information is being collected.
6. Adware
Adware is a type of malware that displays unwanted advertisements on a user’s device. It is often bundled with free software downloads or installed through malicious websites. Once installed, adware may display pop-up advertisements, redirect users to advertising pages, or track browsing activity. Although adware may appear less harmful than other malware types, it can still compromise privacy and reduce system performance. Some forms of adware also redirect users to malicious websites or install additional malware. Because of these risks, adware is considered a significant cybersecurity concern.
7. Rootkits
A rootkit is a sophisticated type of malware designed to hide deep within a computer’s operating system. The primary purpose of a rootkit is to allow attackers to maintain long-term access to a system without being detected. Rootkits often modify system processes and hide malicious files from security tools. Because they operate at a low system level, rootkits are extremely difficult to detect and remove. Attackers use rootkits to control systems, steal information, and install additional malware. Removing rootkits often requires specialized security tools or complete system reinstallation.
8. Keylogger
A keylogger is malware that records every keystroke typed on a device. This allows attackers to capture sensitive information such as usernames, passwords, credit card numbers, and personal messages. Keyloggers may be installed through Trojans, malicious downloads, or infected websites. Some keyloggers also record clipboard activity and screenshots. Once the information is collected, it is transmitted to the attacker’s server. Keyloggers are widely used in financial fraud and identity theft attacks. Because they operate silently, victims may not realize their data has been compromised.
9. Botnet Malware
Botnet malware infects computers and connects them to a network of compromised devices controlled by attackers. Each infected device becomes a bot, which can receive commands from a central command-and-control server. Botnets can contain thousands or even millions of infected devices. Attackers use botnets to launch distributed denial-of-service attacks, send spam emails, spread malware, and perform automated hacking attempts. Because the attacks come from many devices simultaneously, botnets can overwhelm targeted systems and make it difficult to identify the original attacker.
10. Fileless Malware
Fileless malware is an advanced type of malware that operates directly in system memory instead of installing files on the hard drive. It often uses legitimate system tools such as PowerShell or Windows Management Instrumentation to execute malicious commands. Because it does not rely on traditional files, fileless malware leaves fewer traces on the system. This makes it much harder for antivirus software to detect. Attackers often use fileless malware in targeted cyber attacks where stealth and persistence are important.
11. Backdoor Malware
Backdoor malware is designed to create a hidden method of bypassing normal authentication or security mechanisms in a system. Once installed, it allows attackers to access the computer or network remotely without needing the user’s password or permission. Hackers often use backdoors to maintain persistent access after compromising a system. For example, a Trojan may install a backdoor so the attacker can reconnect later and continue exploiting the device. Backdoor malware is commonly used in targeted cyber attacks because it provides long-term control over infected systems and allows attackers to install additional malware or steal sensitive data.
12. Logic Bomb
A logic bomb is malware programmed to activate only when a specific condition is met. These conditions might include a particular date, a specific system event, or the deletion of a file. Until the trigger condition occurs, the malware remains hidden and inactive within the system. Once activated, a logic bomb can perform destructive actions such as deleting files, corrupting data, or disabling systems. Logic bombs are sometimes planted by malicious insiders who have access to company systems. Because they remain dormant for long periods, logic bombs can be difficult to detect before they cause damage.
13. Wiper Malware
Wiper malware is designed to permanently destroy data on infected systems. Unlike ransomware, which encrypts files and demands payment for recovery, wiper malware deletes files or overwrites them so they cannot be restored. This type of malware is often used in destructive cyber attacks against organizations or government systems. Wiper attacks can cause massive operational disruptions by erasing critical data and disabling computers. Because recovery is often impossible without backups, wiper malware can result in significant financial losses and long system downtime.
14. Banking Trojan
A banking Trojan specifically targets online banking systems and financial applications. It is designed to steal banking credentials, credit card details, and authentication codes used during financial transactions. Banking Trojans often inject malicious code into legitimate banking websites or create fake login pages that capture user credentials. Once attackers obtain these credentials, they can access the victim’s bank accounts and perform fraudulent transactions. Banking Trojans are commonly distributed through phishing emails and malicious downloads, making them one of the most dangerous malware types used in financial cybercrime.
15. Password Stealer
Password stealer malware focuses on collecting login credentials stored on an infected system. Many users store passwords in web browsers or password managers for convenience. Password stealers scan these storage locations and extract saved credentials. The malware then sends the stolen passwords to attackers through remote servers. These credentials can be used to access personal accounts, corporate systems, or online services. Password stealers are frequently used as the first stage of a cyber attack, allowing attackers to gain access to multiple systems using stolen login information.
16. Infostealer
Infostealer malware is designed to collect a wide range of sensitive information from infected devices. This may include login credentials, browser cookies, saved passwords, personal documents, system information, and even screenshots. Infostealers are widely used in cybercrime operations because they allow attackers to gather valuable data before launching additional attacks. The stolen information may be sold on underground marketplaces or used for identity theft, fraud, or espionage. Because infostealers often run silently in the background, victims may not realize their data is being collected.
17. Cryptomining Malware
Cryptomining malware secretly uses the computing power of an infected device to mine cryptocurrency for attackers. Cryptocurrency mining requires significant processing power, and attackers exploit victim systems to generate digital currency without paying for hardware or electricity. When cryptomining malware infects a device, it may cause high CPU usage, overheating, and reduced system performance. Victims often notice their computers running slower than usual. Because cryptomining malware focuses on using system resources rather than stealing data, it can remain undetected for long periods.
18. Bootkit
A bootkit is a highly advanced form of malware that infects the system’s boot process. The boot process starts before the operating system loads, meaning bootkits can run before most security software is activated. This gives attackers deep control over the system and allows them to hide other malware components. Bootkits are particularly dangerous because they operate at a very low level within the system architecture. Removing bootkits often requires specialized security tools or a complete system reinstallation.
19. DDoS Malware
DDoS malware is used to launch distributed denial-of-service attacks against websites, servers, or online services. After infecting many devices, attackers control them as part of a botnet. These devices are then instructed to send massive amounts of traffic to a targeted server simultaneously. The large volume of traffic overwhelms the server, causing it to slow down or become unavailable to legitimate users. DDoS attacks are commonly used to disrupt services, damage reputations, or extort money from organizations.
20. Mobile Malware
Mobile malware targets smartphones and tablets rather than traditional computers. As mobile devices store large amounts of personal and financial information, they have become attractive targets for cybercriminals. Mobile malware may steal contacts, messages, location data, login credentials, and files stored on the device. Some mobile malware also installs additional malicious applications or tracks user activity. These infections often occur through malicious apps downloaded from unofficial app stores or through phishing links.
21. SMS Malware
SMS malware is designed to send unauthorized text messages from infected smartphones. In some cases, the malware sends messages to premium-rate phone numbers that charge the victim for each message. In other cases, it spreads malicious links to contacts in the victim’s phonebook, helping the malware spread to additional devices. SMS malware is particularly dangerous because users may not notice the unauthorized activity until they receive unexpectedly high phone bills.
22. Mobile Banking Trojan
Mobile banking Trojans specifically target financial applications on smartphones. These malware programs can intercept login credentials, authentication codes, and financial transaction details. Some mobile banking Trojans create fake login screens that look identical to legitimate banking apps. When users enter their credentials, the information is sent directly to attackers. Because many banks use mobile apps for transactions, mobile banking Trojans have become a growing cybersecurity threat.
23. Polymorphic Malware
Polymorphic malware is designed to change its code structure every time it spreads to a new system. Although the malware performs the same malicious activities, the constantly changing code makes it difficult for antivirus software to recognize it using traditional signature detection. This technique allows attackers to bypass many security systems. Polymorphic malware is often used in advanced cyber attacks where attackers want to remain undetected for as long as possible.
24. Metamorphic Malware
Metamorphic malware takes code modification even further than polymorphic malware. Instead of simply altering small parts of its code, metamorphic malware rewrites its entire code structure each time it spreads. Despite these changes, the malware continues performing the same malicious functions. Because each version of the malware looks different, detecting it using signature-based security tools becomes extremely difficult. Metamorphic malware is considered one of the most advanced forms of malicious software.
25. AI-Powered Malware
AI-powered malware represents the next generation of cyber threats. This type of malware uses artificial intelligence and machine learning techniques to adapt its behavior based on the environment it infects. AI-powered malware can analyze security defenses, avoid detection systems, and automatically modify attack strategies. In the future, attackers may use AI to automate cyber attacks and identify vulnerabilities more efficiently. As cybersecurity technologies evolve, defending against AI-powered malware will become an increasingly important challenge.
Which Malware Types Hackers Use Most Often

Although there are many different types of malware used in cyber attacks, some are far more common than others. Cybercriminals usually choose malware based on their goals, the target they want to attack, and how easily the malware can spread or remain undetected.
In most real-world attacks, hackers prefer malware that can steal valuable data, generate financial profit, or provide long-term access to systems. These malware types are widely used because they are effective, relatively easy to distribute, and can be combined with other attack techniques such as phishing or social engineering.
Below are some of the malware types most frequently used by attackers.
Ransomware
Ransomware has become one of the most widely used malware types in modern cybercrime. It allows attackers to generate direct financial profit by locking victims out of their own systems.
When ransomware infects a device, it encrypts important files and displays a message demanding payment for a decryption key. Organizations often feel pressured to pay because their operations depend on recovering the encrypted data. Hospitals, businesses, schools, and government agencies have all been targets of ransomware attacks.
Because ransomware can generate large payments in a short time, it has become a favorite tool among cybercriminal groups.
Trojan Malware
Trojans are extremely popular among attackers because they rely on deception rather than technical vulnerabilities. Instead of exploiting software flaws, Trojans trick users into installing them voluntarily.
Once installed, Trojans can perform many malicious tasks such as opening backdoors, installing spyware, or giving attackers remote control of the infected system. Many advanced cyber attacks begin with a Trojan infection because it provides attackers with an entry point into a network.
Trojans are commonly distributed through phishing emails, malicious downloads, or fake software updates.
Spyware and Infostealers
Spyware and infostealers are widely used because they allow attackers to collect valuable information from infected devices. These malware types focus on gathering data rather than immediately damaging the system.
Information commonly stolen includes login credentials, browser cookies, financial information, personal documents, and system details. This data can then be used for identity theft, financial fraud, or additional cyber attacks.
Infostealer malware is particularly popular in cybercrime operations because it can quietly collect large amounts of sensitive information before the victim even realizes their system is compromised.
Botnet Malware
Botnet malware is frequently used in large-scale cyber attacks. After infecting a device, the malware connects it to a command-and-control server operated by attackers.
This allows hackers to control thousands or even millions of infected devices simultaneously. These botnets can then be used to launch distributed denial-of-service attacks, send spam emails, or distribute additional malware.
Botnets are especially powerful because they use legitimate devices belonging to unsuspecting users, making the attacks difficult to trace.
Banking Trojans
Banking Trojans are specifically designed to steal financial data. They target online banking systems, payment platforms, and financial applications used by individuals and businesses.
Once installed, banking Trojans may intercept login credentials, capture authentication codes, or modify online transactions. In many cases, victims do not realize their accounts have been compromised until unauthorized transactions occur.
Because financial theft provides immediate monetary gain, banking Trojans remain a common tool for cybercriminals.
Fileless Malware
Fileless malware has become increasingly popular among advanced attackers because it is much harder to detect than traditional malware.
Instead of installing files on the system, fileless malware runs directly in system memory and uses legitimate tools already present on the operating system. This allows it to perform malicious actions while leaving very few traces behind.
Because traditional antivirus software often focuses on scanning files, fileless malware can remain hidden for long periods.
Why Hackers Prefer These Malware Types
The malware types listed above are commonly used because they offer several advantages to attackers. They can generate financial profit, remain hidden for long periods, or allow attackers to maintain control over compromised systems.
Modern cyber attacks often involve multiple malware types working together. For example, a phishing email may deliver a Trojan that installs spyware, which then steals credentials that allow attackers to launch ransomware attacks.
Understanding which malware types are most commonly used helps cybersecurity professionals focus their defenses on the most significant threats.
FAQs – Types of Malware
Which type of malware is considered the most dangerous?
Ransomware is often considered the most dangerous malware because it can lock entire systems and demand payment to restore access. Large ransomware attacks have disrupted hospitals, governments, and major companies worldwide.
How do hackers spread malware?
Hackers typically spread malware through phishing emails, malicious downloads, infected websites, fake software updates, and compromised mobile apps. Social engineering is often used to trick users into installing malware unknowingly.
Can smartphones be infected with malware?
Yes, smartphones can also be infected with malware, especially through malicious apps, phishing links, and unofficial app stores. Mobile malware can steal contacts, messages, login credentials, and financial information.
How can I protect my device from malware attacks?
You can reduce the risk of malware infections by using antivirus software, updating systems regularly, avoiding suspicious downloads, enabling firewalls, and practicing safe browsing habits.
What is the difference between malware and a virus?
Malware is a broad term that refers to all types of malicious software. A virus is just one type of malware that spreads by attaching itself to files or programs and infecting other systems.
Key Takeaways
Understanding how these malware types work is essential for learners, cybersecurity professionals, and anyone who uses the internet. By staying informed about malware threats and following strong security practices—such as updating software, using trusted security tools, and avoiding suspicious downloads—individuals and organizations can significantly reduce the risk of infection and protect their systems from modern cyber attacks.
Security frameworks such as those developed by the National Institute of Standards and Technology help organizations detect and respond to malware threats.







