?
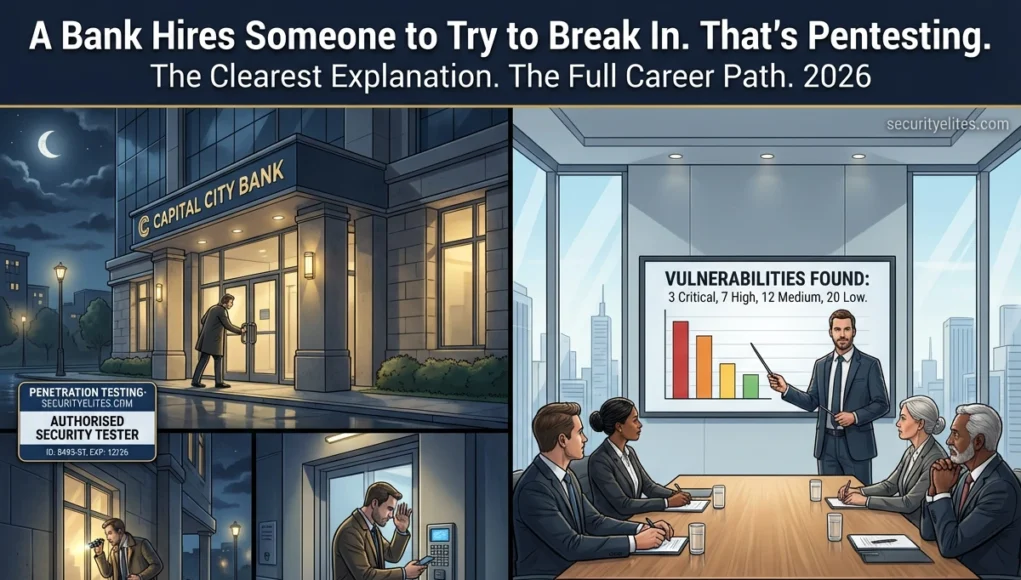
A bank hires a security firm to try to break in before criminals do. Not to steal money — to find every weakness in the physical security before someone with worse intentions finds it first. The security firm attempts to pick locks, tailgate through secure doors, bypass cameras, and access the vault using every technique a real criminal would use. They succeed in some ways. They document everything. They present a report. The bank fixes the weaknesses. Everybody wins. Let’s understand in detail what is penetration testing.
That is penetration testing. Exactly that — but for computer systems instead of physical buildings. A company hires a penetration tester with written authorisation to attack their digital infrastructure using the same techniques a real attacker would use. The goal is to find vulnerabilities before criminals do, document them with evidence, and deliver a report that allows the company to fix them.
If you have ever wondered what a penetration tester actually does, why companies pay for this service, and how to build a career in this field — this is the explanation you have been looking for.
What Is Penetration Testing — The Complete Definition
Penetration testing (also called a pentest, pen test, or ethical hacking engagement) is a structured, authorised security assessment in which a security professional simulates a real cyberattack against an organisation’s systems, applications, or network to identify exploitable vulnerabilities before malicious actors can find and exploit them.
Every Legitimate Penetration Test Has These Three Elements:
1
Explicit Written Authorisation
A signed contract or statement of work from the system owner explicitly authorising the security testing. Without this, the same activities constitute criminal hacking regardless of intent.
2
Defined Scope
A clear definition of what systems, IP ranges, applications, and methods are included and excluded. Testing anything outside the defined scope — even accidentally — violates the engagement terms and potentially the law.
3
Professional Report
A detailed written report documenting every vulnerability found, its severity rating, evidence of exploitation, and specific remediation recommendations. The report is the primary deliverable — what the client is actually paying for.
Penetration Testing vs Ethical Hacking vs Bug Bounty
These three terms are often used interchangeably but describe different engagement models. Understanding the distinction matters for your career path:
| Model | Authorisation | Structure | Payment | Deliverable |
|---|
| Penetration Testing | Signed contract | Defined scope + timeline | Fixed fee (upfront) | Full professional report |
| Bug Bounty | Programme policy | Open-ended, programme scope | Per valid finding | Individual finding reports |
| Ethical Hacking (broad) | Any written permission | Variable | Variable | Variable |
The 5 Phases Every Professional Penetration Test Follows
securityelites.comTHE 5 PHASES OF PROFESSIONAL PENETRATION TESTING
Gather intelligence about the target without triggering alerts. Passive recon: WHOIS, LinkedIn, Google dorking, Shodan, DNS records, SSL certificate transparency. Active recon: Nmap scans, subdomain enumeration, service fingerprinting. Goal: build a complete picture of the attack surface before touching anything sensitive.
Tools: nmap · subfinder · amass · shodan · theHarvester · OSINT framework
Scanning & Enumeration — Map the Vulnerabilities
Actively probe discovered services for vulnerabilities and gather detailed information about configurations. Service version detection, OS fingerprinting, vulnerability scanning, directory enumeration, user enumeration. This phase identifies specific exploitable weaknesses rather than just open ports.
Tools: nmap –script · nikto · gobuster · enum4linux · smtp-user-enum
Exploitation — Demonstrate Real Impact
Attempt to exploit identified vulnerabilities to gain unauthorised access — demonstrating that vulnerabilities are real and impactful, not theoretical. This is the phase that requires the most skill and is what most people imagine when they think of “hacking.” Every exploit attempt is documented with screenshots and logs.
Tools: metasploit · sqlmap · burp suite · custom scripts · manual exploitation
Post-Exploitation — Assess the True Blast Radius
After gaining initial access, determine what a real attacker could achieve: privilege escalation (from user to administrator), lateral movement (accessing other systems), persistence (maintaining access after the session ends), and data access (what sensitive data is reachable). This phase answers the client’s real question: “If we were breached, how bad could it get?”
Tools: meterpreter · bloodhound · mimikatz (in authorised lab) · linpeas/winpeas
Reporting — The Deliverable the Client Pays For
Document everything: executive summary for non-technical stakeholders, technical findings with severity ratings (CVSS), detailed reproduction steps, screenshots as evidence, and specific remediation recommendations for each finding. The report is the primary product. A pentester who cannot write a clear, actionable report is only half a professional.
Format: Executive Summary + Technical Findings + Remediation + Appendices
The 5 Phases of Penetration Testing — Every professional engagement follows this sequence. Reconnaissance gathers intelligence. Scanning maps vulnerabilities. Exploitation demonstrates impact. Post-exploitation assesses blast radius. Reporting converts all findings into actionable recommendations. The report is the deliverable the client actually receives.
3 Types of Penetration Testing: Black Box, Grey Box, White Box
⬛
Black Box
Tester has zero prior knowledge of the target. No credentials, no architecture diagrams, no inside information. Simulates a real external attacker. Most challenging for the tester but most realistic threat simulation.
Best for: Testing external attacker perspective
🔲
Grey Box MOST COMMON
Tester has partial knowledge — typically user-level credentials and some system documentation. Simulates a compromised account or insider threat. Most common engagement type because it balances realism with testing efficiency.
Best for: Most real-world engagements
⬜
White Box
Tester has full knowledge — source code, architecture diagrams, admin credentials, and complete system documentation. Most thorough coverage. Finds the deepest vulnerabilities but does not simulate realistic external attacker perspective.
Best for: Code security audits, maximum coverage
A Day in the Life of a Penetration Tester
securityelites.comA DAY IN THE LIFE — PENETRATION TESTER SCHEDULE
8:30 AM
Kickoff call with client — Review scope, rules of engagement, emergency contacts if something breaks. Confirm start time of testing window.
9:00 AM
Reconnaissance phase begins — Subdomain enumeration, DNS queries, OSINT gathering, Shodan lookups. Document everything in notes. No exploitation yet.
11:00 AM
Nmap and service scanning — Run comprehensive scans against in-scope IP ranges. Service version detection. Pipe results into notes. Begin identifying priority targets.
1:00 PM
Web application testing — Burp Suite open. Browse target web app with intercept off. Review HTTP history. Test IDOR vectors on API endpoints. Find candidate for further investigation.
2:30 PM
FINDING: SQL injection confirmed — UNION-based SQLi on search parameter. Extracting database names. Screenshot capture. Severity: High. Stop exploitation at data confirmed. Document.
4:00 PM
Report writing begins — Document the SQLi finding: description, steps to reproduce, evidence screenshots, CVSS score, remediation recommendation. Notes become the draft report.
5:30 PM
End of day debrief — Internal team review of day’s findings. Plan tomorrow’s testing focus. Check in with client if critical finding was made. Confirm testing window for tomorrow.
A Day in the Life — Penetration testing is methodical, not dramatic. Most of the day involves reconnaissance, scanning, and documentation. The “hacking” phase (exploitation) is a relatively small part of the total engagement time. Report writing begins from day one, not after testing concludes.
Penetration Tester Salaries 2026
$55K–$75K
Junior (0–2 years)
eJPT level · First job
$80K–$110K
Mid-Level (2–5 yrs)
OSCP certified
$120K–$180K
Senior (5+ years)
Specialist / Lead
$150–$250/hr
Independent Consultant
Self-employed · Variable
How to Start a Penetration Testing Career From Zero
The penetration testing career path is well-documented at SecurityElites.com — our free courses and guides cover every step from no experience to employed professional:
1
Build foundations (3 months)
2
Practice in legal environments (months 3–6)
4
Build portfolio and apply (months 10–12)
CTF write-ups on GitHub, bug bounty findings, HTB profile. Apply for junior penetration tester roles. See the full
12-month roadmap.
Frequently Asked Questions
What is penetration testing in simple terms?
A company hires a security professional to attack their systems with permission — using the same techniques a real criminal would use — to find vulnerabilities before actual attackers do. The tester documents everything found and delivers a report with recommendations to fix each issue.
What are the 5 phases of penetration testing?
Reconnaissance (intelligence gathering), Scanning and Enumeration (vulnerability mapping), Exploitation (demonstrating impact), Post-Exploitation (assessing blast radius), and Reporting (the professional deliverable). Every professional engagement follows this sequence regardless of scope or target type.
What is the difference between black box, grey box, and white box?
Black box: no prior knowledge (simulates external attacker). Grey box: partial knowledge like user credentials (most common, simulates insider threat). White box: full knowledge including source code (most thorough, used for code audits).
How much does a penetration tester earn?
US market 2026: Junior (0–2 years) $55K–$75K/year. Mid-level (2–5 years, OSCP) $80K–$110K/year. Senior (5+ years) $120K–$180K/year. Independent consultants $150–$250/hour. These are among the highest-paying entry-level technology roles available.
What is the difference between penetration testing and ethical hacking?
Ethical hacking is the broad concept — any authorised security testing with the goal of improving security. Penetration testing is a specific, structured service with defined scope, timeline, and a professional report deliverable. All penetration testing is ethical hacking, but not all ethical hacking is formal penetration testing.
ME
Mr Elite
Founder, SecurityElites.com | Penetration Tester | Educator
The bank analogy in the opening is the one I use when non-technical people ask what I do for a living. It works every time because it communicates the core truth: this profession exists because organisations need to know their weaknesses before adversaries exploit them. The job is finding those weaknesses first, in a controlled way, and communicating them clearly enough that they get fixed.