Information Gathering Using Kali Linux – Day 9
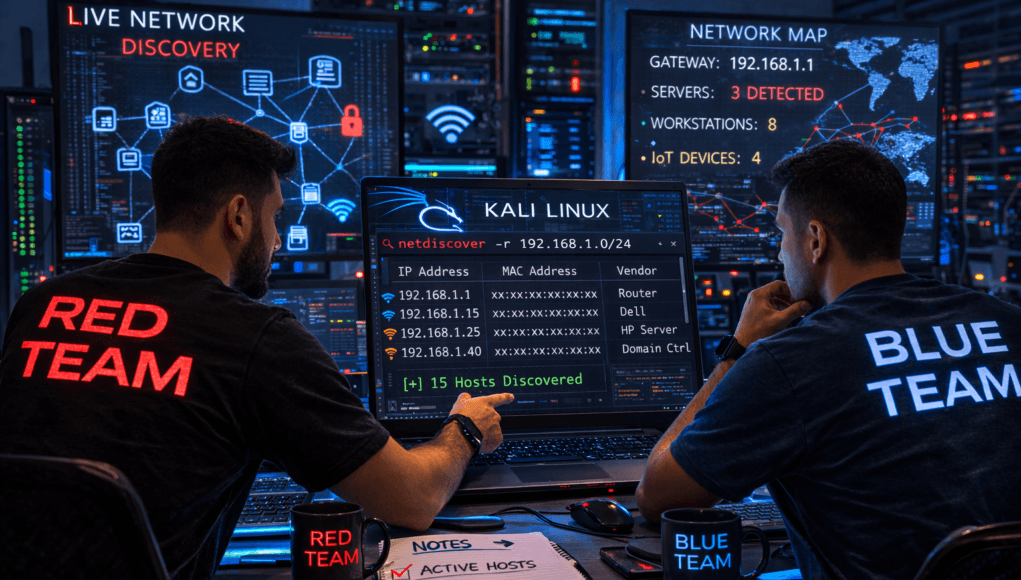
Live Network Discovery Using Netdiscover (Internal Reconnaissance)
Excellent! Now we enter a stage where reconnaissance moves inside networks.
Until now, everything you performed was mostly external reconnaissance.
You discovered:
✅ domains
✅ infrastructure
✅ subdomains
✅ technologies
✅ hidden directories
✅ organizational attack surface
But professional penetration testing does not stop at internet-facing assets.
Real engagements eventually reach this moment:
You gain network access… now what?
And the very first question becomes:
👉 Who else is on this network?
Today you learn how professionals silently discover live systems inside local environments.
Let’s walk through a realistic penetration testing scenario.
Assume you successfully connected to a corporate WiFi during an authorized engagement.
Or gained access through VPN testing scope.
You are now inside the network.
Exciting moment.
But also dangerous.
Because beginners immediately start aggressive scanning.
And instantly trigger detection systems.
From real red-team operations, internal discovery must begin quietly.
You need visibility without noise.
That’s where today’s tool becomes critical.
Instead of scanning loudly…
You listen.
You observe.
You map devices silently.
Welcome to Information Gathering using Kali Linux — Internal Network Discovery.
Tool of the day:
✅ Netdiscover
🎯 Why Internal Network Discovery Matters
External reconnaissance shows public assets.
Internal reconnaissance reveals:
- employee machines
- servers
- printers
- gateways
- domain controllers
- IoT devices
Enterprise environments often contain hundreds of systems.
Many are poorly monitored internally.
During corporate incident response investigations, lateral movement almost always begins with:
👉 device discovery.
Attackers — and ethical hackers — must identify:
- active hosts
- IP addresses
- MAC addresses
- network ranges
Without this map, movement inside networks is blind.
Here’s where beginners get confused.
They think:
“I’ll just run Nmap again.”
Bad idea early inside networks.
Why?
Because Nmap sends active probes.
SOC monitoring tools detect scans immediately.
Netdiscover works differently.
It passively observes ARP traffic.
Much stealthier.
🧠 Beginner-Friendly Concept Explanation
Let’s simplify.
Every device inside a network communicates using:
- IP address (logical identity)
- MAC address (physical identity)
ARP (Address Resolution Protocol) connects them.
Example:
192.168.1.10 → Laptop
192.168.1.1 → Router
192.168.1.25 → Server
Whenever devices communicate, ARP broadcasts occur.
Netdiscover listens to these broadcasts.
Meaning:
✅ minimal noise
✅ passive discovery
✅ stealth enumeration
Think of it like overhearing conversations rather than knocking on doors.
⚙️ Professional Recon Workflow (Continuation)
Your workflow now evolves:
External Recon
↓
Attack Surface Expansion
↓
Initial Access
↓
Internal Network Discovery ✅
↓
Lateral Movement Preparation
Every professional red-team engagement follows this logic.
Discovery always precedes movement.
🧪 Real-World Scenario
During an enterprise internal assessment, testers obtained limited workstation access.
Network appeared segmented.
Aggressive scanning blocked immediately.
Netdiscover passive monitoring revealed:
192.168.10.5 Domain Controller
Critical infrastructure quietly identified.
Later privilege escalation targeted that system.
Entire domain compromise followed.
Discovery created opportunity.
🛠 Tool of the Day — Netdiscover (Kali Linux)
Netdiscover is preinstalled in Kali Linux.
Verify:
netdiscover
✅ Step 1 — Identify Network Interface
Check interfaces:
ip a
Example:
eth0
wlan0
Choose active interface.
✅ Step 2 — Passive Discovery Mode
sudo netdiscover -i eth0 -p
Options:
-i→ interface-p→ passive mode
Netdiscover now listens silently.
Output example:
IP MAC Address Vendor
192.168.1.1 xx:xx:xx Router
192.168.1.15 xx:xx:xx Dell
192.168.1.25 xx:xx:xx HP
Network visibility achieved.
Mentor Insight 🔎
Students often overlook vendor names.
Professionals analyze them carefully.
Vendor reveals device type.
Example:
Cisco → networking device
HP → workstation/server
VMware → virtual system
✅ Step 3 — Active Range Scan (Authorized Only)
sudo netdiscover -r 192.168.1.0/24
Used when passive traffic is limited.
✅ Step 4 — Save Results
sudo netdiscover -r 192.168.1.0/24 > hosts.txt
Always document findings.
🚨 Beginner Mistake Alert
❌ Running Active Mode Immediately
Stay passive first.
❌ Ignoring MAC Vendors
Hardware intelligence matters.
❌ Forgetting Network Scope
Never scan unauthorized networks.
🔥 Pro Tips From 20 Years Experience
✅ Identify gateway first.
Usually:
.x.1
High-value system.
✅ Look for virtualization vendors.
Often hosting servers.
✅ Run Netdiscover before Nmap internally.
Reduces detection risk significantly.
Enterprise reality:
Quiet reconnaissance survives longest.
🛡 Defensive & Ethical Perspective
Blue teams detect abnormal ARP behavior.
Defenders should:
- monitor ARP anomalies
- segment networks
- enforce NAC policies
- log internal discovery attempts
Ethical rule:
Internal recon requires explicit authorization.
Always respect engagement scope.
✅ Practical Implementation Checklist
Practice today:
✔ Identify network interface
✔ Run passive Netdiscover
✔ Identify active devices
✔ Record MAC vendors
✔ Map internal IP range
✔ Save host list
You now perform internal reconnaissance professionally.
💼 Career Insight
Internal discovery skills are essential for:
- Red Team Operators
- Internal Pentesters
- SOC Analysts
- Incident Responders
- Network Security Engineers
Most enterprise breaches escalate internally — not externally.
🔁 Quick Recap Summary
Your journey so far:
| Day | Skill |
|---|---|
| Day 1 | WHOIS |
| Day 2 | DNS |
| Day 3 | Subdomains |
| Day 4 | Nmap |
| Day 5 | OSINT |
| Day 6 | Fingerprinting |
| Day 7 | Directories |
| Day 8 | Amass |
| Day 9 | Internal Discovery ✅ |
You now map networks both externally and internally.
Tomorrow…
We extract intelligence hidden inside documents themselves.
❓ FAQs
1. What is Netdiscover used for?
Discovering live devices inside local networks.
2. Is Netdiscover passive?
Yes, primarily using ARP monitoring.
3. Why not use Nmap internally first?
It creates detectable scanning noise.
4. Can Netdiscover detect all devices?
Only active communicating devices.
5. Do professionals use Netdiscover?
Yes — especially during internal penetration testing.