Information Gathering Using Kali Linux – Day 11
Full Recon Automation Using Recon-ng (Professional Recon Framework)
We’ve reached the final stage of the professional journey.
Up to now, we didn’t just learn tools.
You learned how real penetration testers think.
Let’s pause and look at what you’ve built:
✅ Ownership Intelligence
✅ DNS Mapping
✅ Subdomain Discovery
✅ Network Enumeration
✅ OSINT Intelligence
✅ Technology Fingerprinting
✅ Directory Discovery
✅ Attack Surface Expansion
✅ Internal Network Discovery
✅ Metadata Intelligence
Now comes the question every professional eventually asks:
Can all reconnaissance be unified into one intelligent framework?
Yes.
And this is exactly how enterprise red teams operate.
Welcome to the Master Level.
Early in my career, reconnaissance meant running tools manually.
WHOIS → save results
DNS → copy output
Subdomains → separate files
Emails → another report
Messy.
Slow.
Error-prone.
During a large enterprise assessment involving thousands of assets, manual recon became impossible.
That’s when frameworks changed everything.
Instead of running tools individually…
Professionals use intelligence platforms that:
✔ collect
✔ correlate
✔ store
✔ automate
✔ analyze
all reconnaissance data together.
Today you learn the same framework used by advanced ethical hackers:
✅ Recon-ng
🎯 Why Recon Automation Matters in Real Cybersecurity
Modern organizations generate massive data footprints.
Manual reconnaissance fails because:
- assets change constantly
- intelligence sources multiply
- correlations get missed
Recon-ng solves this by acting like:
Metasploit — but for reconnaissance
It creates a structured database storing:
- domains
- hosts
- emails
- contacts
- companies
- vulnerabilities indicators
From enterprise red-team experience:
Automation doesn’t replace skill.
It amplifies it.
Beginners often think:
More tools = better hacking.
Professionals think differently:
Better workflow = better intelligence.
Recon-ng builds workflow discipline.
🧠 Beginner-Friendly Concept Explanation
Think of Recon-ng as a command center.
Instead of scattered notes:
emails.txt
hosts.txt
subdomains.txt
Everything lives inside one intelligence database.
Recon modules automatically gather information and connect relationships.
Example:
Domain → Email → Employee → Host → Infrastructure
Patterns emerge automatically.
That’s professional reconnaissance.
⚙️ Professional Recon Workflow (Final Evolution)
Your completed workflow:
WHOIS
↓
DNS
↓
Subdomains
↓
Hosts
↓
OSINT
↓
Technology Detection
↓
Directories
↓
Attack Surface Mapping
↓
Internal Discovery
↓
Metadata Intelligence
↓
Recon Automation ✅
You are now operating at professional recon level.
🧪 Real-World Scenario
During a multinational red-team engagement, scope included multiple subsidiaries.
Manual tracking became impossible.
Recon-ng correlated:
- employee emails
- cloud infrastructure
- leaked credentials
- forgotten domains
Framework automatically linked assets belonging to the same organization.
One abandoned Azure deployment exposed admin access.
Critical finding discovered.
Automation revealed what humans missed.
🛠 Tool of the Day — Recon-ng (Kali Linux)
Recon-ng is preinstalled in Kali Linux.
Launch:
recon-ng
You’ll enter workspace environment:
[recon-ng][default] >
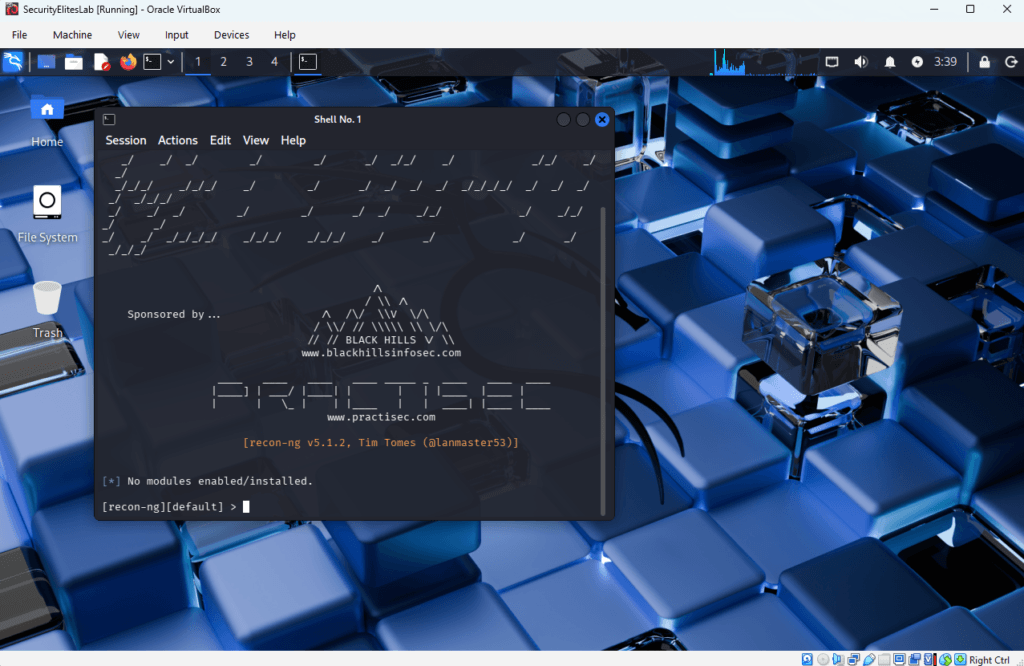
✅ Step 1 — Create Workspace
workspaces create securityelites_recon
Workspace = engagement project.
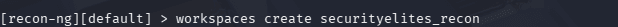
Professional habit.
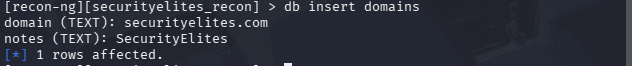
✅ Step 2 — Add Target Domain
db insert domains
Enter:
example.com ( we will use securityelites.com)
Target stored in database.
Mentor Insight 🔎
Students skip workspace organization.
Enterprise testers never do.
Documentation defines professionalism.
✅ Step 3 — View Available Modules
modules search
Modules include:
- WHOIS lookup
- DNS enumeration
- email discovery
- host discovery
Everything centralized.
✅ Step 4 — Load Module
Example WHOIS module:
modules load recon/domains-contacts/whois_pocs
You might get an error that module not found. You have to update it from marketplace using below command:
First refresh the marketplace:
marketplace refresh
Then search for modules in marketplace:
marketplace search whois
Now install the module using below command:
marketplace install recon/domains-contacts/whois_pocs
Now again run the actual command to load whois module:
modules load recon/domains-contactss/whois_pocs
Similarly you can install other modules for recon-ng, some of might require API Key, for that you need to get API keys from bing or shodan.
✅ Step 5 — Configure Options
options show
Set source:
options set SOURCE example.com (note: we will use google.com for example)
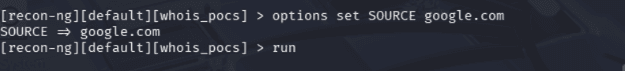
✅ Step 6 — Run Module
run
Results automatically saved.
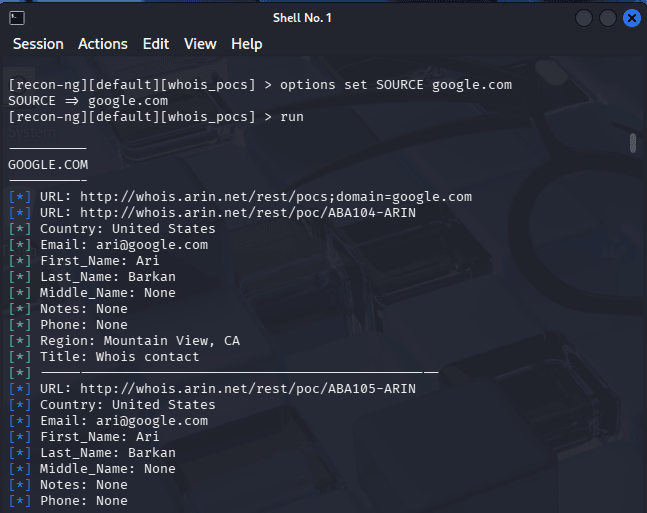
No manual copying required.
✅ Step 7 — View Collected Data
show contacts
Intelligence correlation achieved.
🚨 Beginner Mistake Alert
❌ Running Random Modules
Follow workflow sequence.
❌ Ignoring Database Power
Recon-ng strength = correlation.
❌ Skipping Documentation
Reports depend on stored intelligence.
🔥 Pro Tips From 20 Years Experience
✅ Always create new workspace per target.
✅ Run passive modules first.
Stay stealthy.
✅ Export results regularly:
reporting html
Enterprise truth:
Automation enables large-scale reconnaissance.
🛡 Defensive & Ethical Perspective
Blue teams use similar frameworks for:
- threat intelligence
- asset monitoring
- exposure tracking
Modern defense mirrors attacker methodology.
Ethical reminder:
Recon frameworks must only be used under authorization.
Professional ethics sustain cybersecurity careers.
✅ Practical Implementation Checklist
Final practice:
✔ Launch Recon-ng
✔ Create workspace
✔ Insert domain
✔ Load modules
✔ Run reconnaissance
✔ View stored intelligence
✔ Export report
You now operate reconnaissance professionally.
💼 Career Insight
Recon automation skills are essential for:
- Red Team Operators
- Threat Intelligence Analysts
- Advanced Pentesters
- SOC Engineers
- Cybersecurity Consultants
Senior cybersecurity roles depend heavily on intelligence platforms.
You’ve crossed beginner territory.
Frequently Asked Questions (FAQs) — Recon-ng
What is Recon-ng in Kali Linux?
Recon-ng is an open-source reconnaissance framework used for automated information gathering using Kali Linux. It allows ethical hackers and penetration testers to collect intelligence such as domains, hosts, emails, and infrastructure details through modular reconnaissance modules. Recon-ng stores gathered data inside a built-in database, making it easier to correlate information during cybersecurity investigations and penetration testing engagements.
Why do ethical hackers use Recon-ng for information gathering?
Ethical hackers use Recon-ng because it automates the reconnaissance phase of penetration testing. Instead of running multiple tools separately, Recon-ng integrates various intelligence modules into a single framework. This helps security professionals quickly collect OSINT data like subdomains, employee contacts, and host information while maintaining organized intelligence records during information gathering using Kali Linux.
Is Recon-ng passive or active reconnaissance?
Recon-ng mainly performs passive reconnaissance, meaning it gathers publicly available information from external intelligence sources without directly interacting with target systems. However, some modules may perform limited active queries depending on configuration. Ethical hackers typically begin with passive modules to avoid detection during the early stages of information gathering using Kali Linux.
What type of data can Recon-ng collect?
Recon-ng can collect a wide range of intelligence data during reconnaissance, including:
- Domain names
- Subdomains
- Email addresses
- Employee contacts
- IP addresses
- Host infrastructure
- Company information
This collected data is stored inside the Recon-ng workspace database, allowing penetration testers to analyze relationships between discovered assets during professional information gathering using Kali Linux.
Is Recon-ng similar to Metasploit?
Yes, Recon-ng is often described as the Metasploit framework for reconnaissance. While Metasploit focuses on exploitation and vulnerability testing, Recon-ng focuses on intelligence gathering and OSINT reconnaissance. Both frameworks use modular architectures that allow security professionals to load modules, configure options, and automate cybersecurity workflows.
Do professional penetration testers still use Recon-ng?
Yes, many penetration testers and red team operators still use Recon-ng for reconnaissance automation. Although modern recon workflows may combine additional tools such as Amass, Subfinder, and custom scripts, Recon-ng remains valuable because it provides a structured framework for organizing reconnaissance data during information gathering using Kali Linux.
Is Recon-ng legal to use?
Recon-ng is legal when used for authorized cybersecurity activities such as penetration testing, bug bounty programs, or security research. Ethical hackers must always obtain permission before collecting intelligence on any organization or network. Unauthorized reconnaissance activities can violate cybersecurity laws and ethical hacking guidelines.
🔁 Quick Recap Summary (Full Course)
| Day | Skill Mastered |
|---|---|
| 1 | WHOIS |
| 2 | DNSRecon |
| 3 | Sublist3r |
| 4 | Nmap |
| 5 | theHarvester |
| 6 | WhatWeb |
| 7 | Dirsearch |
| 8 | Amass |
| 9 | Netdiscover |
| 10 | Metagoofil |
| 11 | Recon-ng ✅ |
You now understand complete Information Gathering using Kali Linux.
From beginner → professional workflow.