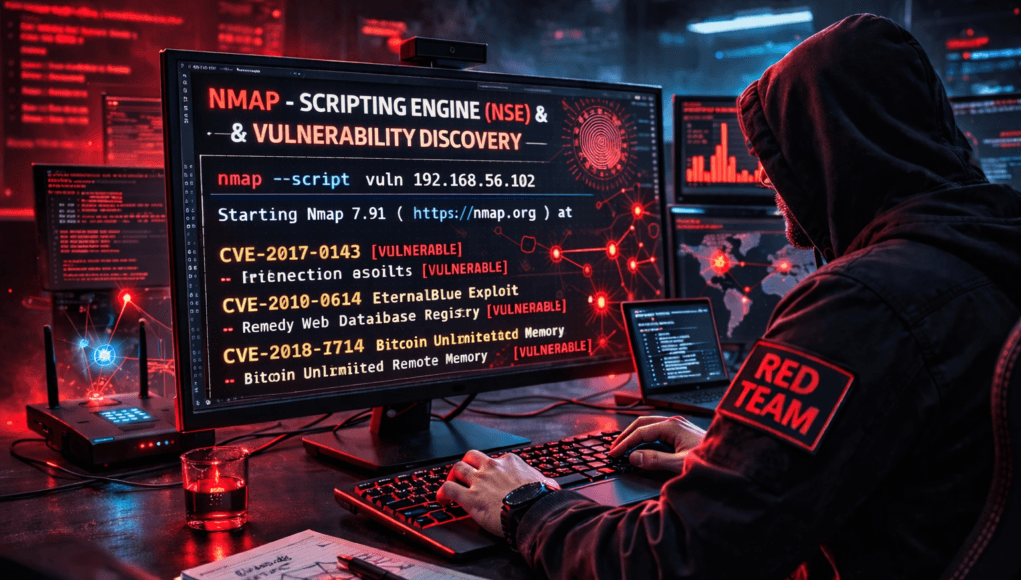
Network Scanning Tutorial Using Nmap — Day 6
Vulnerability Discovery Using Nmap Scripting Engine
Perfect! Now we reach the stage where Nmap stops being just a scanner…
…and becomes a vulnerability discovery engine.
Up to now in our professional progression we explored:
✅ Day 1 — Nmap Fundamentals
✅ Day 2 — Host Discovery
✅ Day 3 — Port Scanning
✅ Day 4 — Service Enumeration
✅ Day 5 — OS Detection & Fingerprinting
Today you unlock what most beginners never fully understand:
Nmap Scripting Engine (NSE)
This is where automation meets attacker intelligence.
Let me tell you something many cybersecurity learners discover late.
Professional attackers rarely test vulnerabilities manually first.
They automate intelligence gathering.
During a real Red Team engagement, our objective was simple:
Identify vulnerable systems inside a corporate subnet within hours.
Instead of manually checking hundreds of services…
We used NSE.
Within minutes:
- weak SMB configurations detected
- anonymous FTP access identified
- outdated SSL protocols exposed
No exploitation yet.
Just intelligent automation.
Today you learn how Nmap evolves into a mini vulnerability scanner.
Note —
Scanning finds doors.
Enumeration identifies occupants.
NSE checks whether doors are weak.
Why NSE Matters in Real Penetration Testing
Without NSE:
You manually verify:
- authentication methods
- SSL configuration
- exposed shares
- misconfigurations
With NSE:
Nmap performs structured testing automatically.
Real Enterprise Observation
SOC investigations often detect attackers running NSE scripts because:
NSE mimics vulnerability scanning behavior.
It signals escalation from reconnaissance to attack preparation.
Defensive Insight
Blue Teams classify NSE activity as:
Active Threat Enumeration
Meaning risk level increases significantly.
What is Nmap Scripting Engine?
NSE allows Nmap to run Lua-based scripts during scans.
Scripts perform:
✅ vulnerability checks
✅ authentication testing
✅ service enumeration
✅ configuration analysis
✅ brute-force testing
Nmap includes 600+ scripts.
Analogy
Think of Nmap as smartphone hardware.
NSE scripts are apps.
Each performs specialized tasks.
Note —
Important mindset:
NSE does NOT hack automatically.
It identifies weaknesses.
NSE Script Categories
Professional understanding begins here.
| Category | Purpose |
|---|---|
| safe | Non-intrusive checks |
| discovery | Information gathering |
| vuln | Vulnerability detection |
| auth | Authentication testing |
| brute | Password testing |
| exploit | Limited exploitation |
| default | Common scripts |
Professionals choose scripts carefully.
Professional NSE Workflow
Real pentest flow:
Step 1 — Port Identification
(from Day 3)
Step 2 — Service Enumeration
(from Day 4)
Step 3 — Targeted NSE Execution
Never run everything blindly.
Enterprise Reality
Running all scripts may:
- trigger IDS
- crash fragile systems
- generate alerts instantly
Precision matters.
✅ HANDS-ON PRACTICAL TUTORIAL (Live Lab)
Now we simulate real vulnerability discovery.
Lab Setup
Environment continues:
✅ Kali Linux
✅ Metasploitable2
Target:
192.168.56.102
Step 1 — Default Script Scan
Goal:
Run safe reconnaissance scripts.
Command:
nmap -sC 192.168.56.102
What Happens?
Executes default NSE scripts.
Checks include:
- FTP anonymous login
- HTTP titles
- SSL info
- SMB data
Expected Output Example
ftp-anon: Anonymous FTP login allowed
Attacker Thinking
Immediate concern:
Anonymous access may expose files.
Note —
Many breaches start with simple misconfiguration discovery.
Step 2 — Vulnerability Detection Scripts
Command:
nmap --script vuln 192.168.56.102
Technical Behavior
Scripts compare service responses against known vulnerabilities.
Example checks:
- Heartbleed
- SMB vulnerabilities
- outdated services
Real Meaning
You are now performing vulnerability assessment.
Step 3 — Target Specific Service Scripts
Professional approach:
nmap --script ftp-* -p21 192.168.56.102
Why Targeted?
Reduces noise.
Avoids detection spikes.
Improves accuracy.
Micro-Story
Bug bounty engagement revealed writable FTP directory via NSE.
Upload allowed.
Web shell deployed later.
Enumeration → Access chain completed.
Note —
Attack chains begin from small findings.
Never ignore minor results.
Step 4 — SMB Enumeration Scripts
Command:
nmap --script smb-enum-shares -p445 targetIP
Finds shared folders.
Often exposes sensitive data.
Step 5 — Safe Vulnerability Scan Combination
Professional favorite:
nmap -sV --script safe,vuln targetIP
Balanced intelligence gathering.
Step 6 — Discover Available Scripts
Command:
ls /usr/share/nmap/scripts/
Professionals explore scripts regularly.
Troubleshooting Layer
Script Not Found?
Update database:
nmap --script-updatedb
Scan Too Slow?
Limit ports.
False Positives?
Always validate manually.
Note —
Automation assists thinking.
It never replaces verification.
Attacker Thinking Simulation
At this stage attacker evaluates:
- exploitable vulnerability?
- authentication weakness?
- lateral movement opportunity?
- privilege escalation path?
NSE accelerates decision-making.
Real-World Scenario
Internal audit detected SMB signing disabled via NSE.
Admins unaware.
Condition enabled relay attacks.
Fixed before breach occurred.
Professional Tools
NSE results integrate with:
- Metasploit
- CVE databases
- Vulnerability scanners
- Threat intelligence systems
Nmap becomes reconnaissance automation platform.
Beginner Mistakes 🚨
❌ Running all scripts blindly
❌ Ignoring safe categories
❌ Trusting results blindly
❌ Scanning production aggressively
❌ Skipping documentation
Pro Tips From 20 Years Experience 🔥
- Start with safe scripts.
- Target services individually.
- Validate vulnerabilities.
- Save outputs:
-oA nse_scan
Automation must remain controlled.
Defensive & Ethical Perspective
Blue Teams defend against NSE using:
- IDS signatures
- rate limiting
- segmentation
- honeypots
Understanding NSE improves both offense and defense.
Practical Implementation Checklist
✅ Default scripts executed
✅ Vulnerability scripts tested
✅ Service-specific scripts used
✅ Results validated
✅ Outputs documented
Career Insight
NSE mastery directly applies to:
- Penetration Testing
- Vulnerability Assessment
- Red Team Operations
- SOC Analysis
- Security Auditing
Many professional pentesters rely heavily on NSE daily.
Quick Recap
Today you learned:
✅ NSE fundamentals
✅ Script categories
✅ Vulnerability detection
✅ Targeted scanning
✅ Automation workflow
Tomorrow…
You learn what professionals truly master:
👉 Stealth Scanning & Evasion Techniques
FAQs
What is NSE?
Nmap Scripting Engine enabling automated security checks.
Is NSE exploitation?
Mostly detection, not exploitation.
Are NSE scans detectable?
Yes — often monitored.
Should beginners run vuln scripts?
Only in lab environments.
Can NSE crash systems?
Rare but possible on fragile services.
How many scripts exist?
600+ built-in scripts.
Do professionals rely on NSE?
Extensively during reconnaissance.