Every day, thousands of people search Google asking the same question:
“How do I become an ethical hacker?”
But most beginners face a frustrating problem. The internet is filled with random tutorials, confusing hacking tools, and scattered cybersecurity advice. Instead of learning properly, many beginners end up jumping between tools without understanding the real ethical hacking roadmap.
The truth is that becoming an ethical hacker is not about learning random hacking tricks. It is about following a structured ethical hacking roadmap that gradually builds the skills required to understand how real cyber attacks work.
In 2026, ethical hackers are among the most valuable cybersecurity professionals in the world. Organizations across industries are hiring ethical hackers to protect their systems from increasingly sophisticated cyber threats.
But the biggest challenge for beginners is knowing where to start and what to learn next.
Should you learn programming first?
Should you start with Kali Linux?
Do you need to learn networking before hacking?
This guide answers all those questions.
This ethical hacking roadmap will show you exactly how to become ethical hacker professionals step by step, even if you are starting with zero cybersecurity knowledge.
Inside this guide, you will learn:
• the complete ethical hacking roadmap from beginner to expert
• the exact skills required to become an ethical hacker
• the tools used by professional penetration testers
• real-world cybersecurity labs for practice
• bug bounty and red team career paths
Unlike most articles online, this guide explains the ethical hacking roadmap the same way cybersecurity professionals learn it in training academies.
Every concept is explained clearly so that even a beginner who knows nothing about hacking can understand it. By the end of this guide, you will have a clear roadmap for how to become ethical hacker professionals and build a career in cybersecurity.
If you are serious about learning ethical hacking, start with the roadmap below and follow it step by step.
Because the difference between a beginner and a professional ethical hacker is simple:
Professionals follow a roadmap. Beginners guess.
And this guide gives you the complete ethical hacking roadmap 2026 used by cybersecurity professionals.
Table of Contents
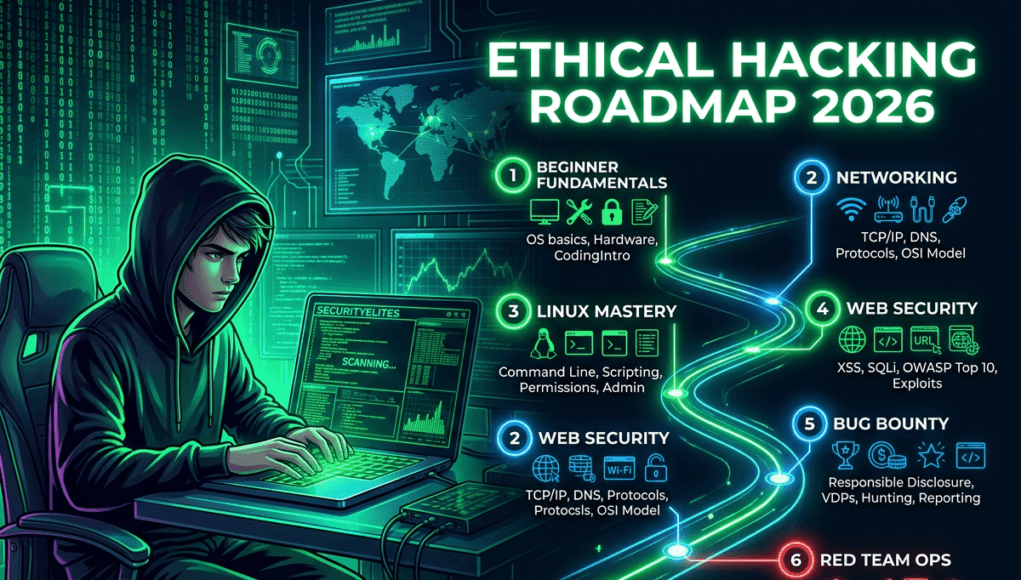
SecurityElites Ethical Hacking Roadmap 2026 — Step-by-Step Learning Path
Think of Ethical Hacking Roadmap like a map for learning cybersecurity skills.
Just like someone learning to become a doctor must first study biology before performing surgery, a cybersecurity learner must first understand how computers and networks work before learning how to hack them.
The ethical hacking roadmap generally follows these stages:
- Stage 1 — Learn Computer Fundamentals
- Stage 2 — Learn Networking Fundamentals
- Stage 3 — Learn Linux Operating System
- Stage 4 — Learn Programming Basics
- Stage 5 — Learn Cybersecurity Fundamentals
- Stage 6 — Learn Web Application Security
- Stage 7 — Learn Ethical Hacking and Penetration Testing Tools
- Stage 8 — Practice Ethical Hacking in Real Security Labs
- Stage 9 — Learn bug bounty hunting
- Stage 10 — Become a professional penetration tester
Each stage builds knowledge required for the next stage.
Skipping fundamentals is the biggest mistake beginners make.
Stage 1 — Learn Computer Fundamentals
The very first step in the ethical hacking roadmap is learning how computers work.
If someone wants to understand how to become ethical hacker professionals, they must first understand the basic structure of computers.
Every cyber attack happens on a computer system. If you do not understand how a computer works, it is impossible to understand how hackers attack it.
Important topics to learn in this stage of the ethical hacking roadmap include:
• Operating systems
• Files and folders
• Computer memory
• Processes and programs
• Hardware components
For example:
When you open a file on your computer, several things happen internally:
- The operating system locates the file
- The CPU processes instructions
- The memory stores temporary data
- The program executes
Ethical hackers study these processes because vulnerabilities often occur when software handles data incorrectly.
Understanding these basics is the foundation of the ethical hacking roadmap.
Note —
Imagine your computer is like a school building.
The CPU is the principal, the memory is the classroom, and files are books.
If you want to learn how to become ethical hacker professionals, you must first understand how the school operates.
Only then can you find the broken doors.
That is why computer fundamentals are the first step in the ethical hacking roadmap.
Stage 2 — Learn Networking Fundamentals
The second stage in the ethical hacking roadmap focuses on networking.
Almost every cyber attack happens over the internet.
Websites, servers, and computers communicate through networks.
If someone wants to understand how to become ethical hacker professionals, they must learn how computers talk to each other.
Important networking concepts in the ethical hacking roadmap include:
• IP addresses
• DNS systems
• TCP/IP protocol
• Ports and services
• Packets and routing
For example:
When you open a website like:
example.com
Your computer performs several networking operations.
First, the DNS server converts the domain name into an IP address.
Then your computer sends packets to the web server.
The server responds with data that loads the website.
Ethical hackers analyze this communication process to identify security weaknesses.
Networking knowledge is therefore one of the most important parts of the ethical hacking roadmap.
Note —
Imagine sending a letter to a friend.
You need:
• an address
• a delivery system
• a mailbox
The internet works the same way.
The IP address is the house address.
Packets are like letters traveling through the internet.
Understanding this Networking Fundamentals is critical in the ethical hacking roadmap.
Stage 3 — Learn Linux Operating System
Linux is the operating system used by most cybersecurity professionals.
Therefore learning Linux is a crucial step in the ethical hacking roadmap 2026. We have shared an article for absolute beginners to use Kali Linux, you can go through that in detail.
Most ethical hacking tools run on Linux distributions such as:
• Kali Linux
• Parrot OS
• Ubuntu
Anyone learning how to become ethical hacker professionals must understand basic Linux commands.
Common commands include:
ls
cd
pwd
cat
mkdir
chmod
grep
These commands allow ethical hackers to:
• navigate files
• analyze system logs
• manage permissions
• execute programs
Linux knowledge allows ethical hackers to interact directly with operating systems during penetration testing.
Without Linux skills, progressing in the ethical hacking roadmap becomes extremely difficult.
Note —
Linux is like the control panel of a computer system.
Instead of clicking buttons, you type commands.
Ethical hackers prefer Linux because it gives full control over the system.
This is why Linux is a core stage in the ethical hacking roadmap.
Stage 4 — Learn Programming Basics (Important Stage in the Ethical Hacking Roadmap)
A very important stage in the ethical hacking roadmap is learning basic programming.
Many beginners searching how to become ethical hacker professionals believe programming is optional. In reality, programming helps ethical hackers understand how software behaves internally.
Applications, websites, and mobile apps are all built using programming languages. Vulnerabilities often occur when programmers write insecure code.
Learning programming allows ethical hackers to:
• understand application logic
• analyze how input is processed
• automate security testing
• build custom hacking scripts
This is why programming is an essential stage in the ethical hacking roadmap 2026.
Programming Languages Ethical Hackers Should Learn
The ethical hacking roadmap typically includes these programming languages.
Python
Python is one of the most important languages in the ethical hacking roadmap.
Python helps ethical hackers:
• automate reconnaissance
• build vulnerability scanners
• write security scripts
• analyze network traffic
Example Python usage:
import requests
response = requests.get("https://example.com")
print(response.status_code)
This simple script sends a request to a website and prints the response.
JavaScript
JavaScript is extremely important for web application security testing.
Anyone learning how to become ethical hacker professionals must understand how JavaScript works inside browsers.
Many vulnerabilities such as Cross-Site Scripting (XSS) involve JavaScript execution.
Understanding JavaScript helps ethical hackers identify client-side vulnerabilities.
Bash Scripting
Bash scripting allows ethical hackers to automate Linux commands.
Example Bash script:
for i in {1..10}
do
ping -c 1 192.168.1.$i
doneThis script checks multiple hosts in a network.
Automation is extremely useful in the ethical hacking roadmap.
Note —
Programming is like giving instructions to a computer.
If you want to learn how to become ethical hacker professionals, you must understand how these instructions work.
When hackers exploit vulnerabilities, they are often manipulating program instructions.
That is why programming is an important step in the ethical hacking roadmap.
Step 5 — Learn Cybersecurity Fundamentals
The next stage in the ethical hacking roadmap is understanding cybersecurity fundamentals.
Before learning hacking techniques, students must understand how security systems are designed.
Cybersecurity is built around three core principles called the CIA Triad.
These include:
• Confidentiality
• Integrity
• Availability
These three principles form the foundation of the ethical hacking roadmap 2026.
Confidentiality
Confidentiality ensures that sensitive information is accessible only to authorized users.
Example:
Bank account data should only be visible to the account owner.
If attackers steal this information, confidentiality is broken.
Integrity
Integrity ensures that data cannot be modified without authorization.
Example:
A hacker changing bank balances would violate data integrity.
Availability
Availability ensures that systems remain accessible.
Example:
A website should remain online for users. DDoS attacks attempt to break availability.
Understanding these principles helps learners understand why vulnerabilities are dangerous.
Cybersecurity fundamentals are therefore a key stage in the ethical hacking roadmap.
Stage 6 — Learn Web Application Security
Web applications are one of the most common attack targets on the internet.
This is why web security is one of the most important stages in the ethical hacking roadmap.
Most bug bounty programs focus on web vulnerabilities.
Anyone researching how to become ethical hacker professionals must master web application security.
Common Web Vulnerabilities
The ethical hacking roadmap includes learning common vulnerabilities such as:
SQL Injection
SQL Injection occurs when attackers manipulate database queries.
Example vulnerable input:
' OR 1=1 --
This input may bypass authentication systems.
Cross-Site Scripting (XSS)
Cross-Site Scripting allows attackers to execute JavaScript inside a victim’s browser.
Example payload:
<script>alert("XSS")</script>XSS can steal cookies and session tokens.
Broken Authentication
Authentication flaws allow attackers to bypass login systems.
Example:
Weak password reset mechanisms.
File Upload Vulnerabilities
Improper file validation may allow attackers to upload malicious scripts.
These vulnerabilities are frequently discovered in bug bounty programs.
Learning web application security is a major milestone in the ethical hacking roadmap.
Stage 7 — Learn Ethical Hacking and Penetration Testing Tools
After learning fundamentals, students begin using professional tools.
Tools help ethical hackers and penetration testers perform tasks faster.
However, tools are not the starting point of the ethical hacking roadmap.
Tools should only be used after understanding the concepts behind them.
Important Tools in the Ethical Hacking Roadmap
Nmap
Nmap is used for network scanning and discovery. We have shared complete day wise course on NMAP usage, you should use it to learn it.
Example command:
nmap -sV 192.168.1.10
This command identifies open ports and running services.
Burp Suite
Burp Suite is used for web application security testing.
Ethical hackers intercept HTTP requests and modify parameters to test vulnerabilities.
FFUF
FFUF is used for directory fuzzing.
It helps discover hidden directories on websites.
Amass
Amass performs subdomain enumeration.
Subdomains expand the attack surface.
Gobuster
Gobuster discovers hidden resources on web servers.
There are more than 300 Ethical Hacking Tools which we should learn in our journey to become an professional hacker. These tools help ethical hackers perform reconnaissance in the ethical hacking roadmap.
Stage 8 — Practice Ethical Hacking in Real Security Labs
At this stage of the ethical hacking roadmap, learners already understand computers, networking, Linux, programming, and web security basics.
Now comes the most important stage of learning how to become ethical hacker professionals — practice.
Ethical hacking is a practical skill. Reading theory alone cannot make someone an ethical hacker.
Real learning begins when you start testing vulnerable systems in controlled environments.
This stage in the ethical hacking roadmap 2026 focuses on practicing attacks safely in cybersecurity labs.
These labs simulate real vulnerable systems used in cybersecurity training.
Practicing in labs allows learners to understand:
• how vulnerabilities appear in real applications
• how attackers exploit security weaknesses
• how penetration testing works in real scenarios
• how to analyze system responses
Hands-on practice transforms theoretical knowledge into real ethical hacking skills.
Best Platforms to Practice Ethical Hacking
Several platforms help beginners practice the ethical hacking roadmap safely.
These platforms provide intentionally vulnerable machines for training.
TryHackMe
TryHackMe is one of the most beginner-friendly platforms for learning how to become ethical hacker professionals.
It provides guided cybersecurity rooms where learners can practice:
• Linux basics
• networking attacks
• web application testing
• privilege escalation
TryHackMe explains concepts step-by-step, making it ideal for beginners following the ethical hacking roadmap.
Hack The Box
Hack The Box provides realistic vulnerable machines.
Learners must discover vulnerabilities and exploit them.
This platform helps ethical hackers develop:
• reconnaissance skills
• vulnerability discovery techniques
• exploitation strategies
Hack The Box is a critical stage in the ethical hacking roadmap 2026.
PortSwigger Web Security Academy
This platform focuses on web application vulnerabilities.
Learners practice discovering vulnerabilities such as:
• SQL Injection
• Cross-Site Scripting
• authentication bypass
• CSRF attacks
Web security practice is extremely important for anyone learning how to become ethical hacker professionals.
Stage 9 — Learn Bug Bounty Hunting
After gaining experience in security labs, the next stage in the ethical hacking roadmap is bug bounty hunting.
Bug bounty programs allow ethical hackers to test real systems legally.
Companies invite security researchers to discover vulnerabilities in their platforms.
If a valid vulnerability is discovered, the ethical hacker receives a reward.
This stage in the ethical hacking roadmap allows learners to apply their skills in real-world environments.
How Bug Bounty Programs Work
Bug bounty programs usually follow this process:
- A company publishes a bug bounty program.
- Ethical hackers test the system for vulnerabilities.
- If a vulnerability is discovered, it is reported responsibly.
- The company verifies the vulnerability.
- The ethical hacker receives a reward.
Bug bounty rewards can range from $100 to over $100,000 depending on severity.
Skills Required for Bug Bounty Hunting
Anyone learning how to become ethical hacker professionals should develop the following skills before attempting bug bounty hunting.
Important skills include:
• reconnaissance
• subdomain enumeration
• web application testing
• API security analysis
• authentication testing
Bug bounty hunting heavily depends on web application security knowledge.
Most successful bug bounty hunters follow the ethical hacking roadmap carefully before starting bug bounty programs. We have also shared Real Bug Bounty Case Study for students, you must go through it.
Stage 10 — Become a Professional Penetration Tester (Final Stage of the Ethical Hacking Roadmap)
The final stage of the ethical hacking roadmap is becoming a professional penetration tester.
At this stage in the ethical hacking roadmap, learners have already developed strong technical skills such as:
• networking fundamentals
• Linux system knowledge
• programming basics
• web application security testing
• vulnerability discovery
• exploitation techniques
• cybersecurity lab experience
These skills prepare learners for the ultimate goal of the ethical hacking roadmap — working as a professional ethical hacker who helps organizations identify security weaknesses.
For anyone researching how to become ethical hacker professionals, becoming a penetration tester is one of the most common and respected career paths.
Penetration testers are cybersecurity experts who simulate cyber attacks against systems in order to find vulnerabilities before malicious hackers exploit them.
Their job is to think like an attacker but act responsibly to protect organizations from cyber threats.
What Does a Penetration Tester Do?
A penetration tester performs authorized security testing on computer systems, networks, and applications.
This process is often called penetration testing or ethical hacking.
Penetration testers follow structured testing phases that align closely with the ethical hacking roadmap.
Typical penetration testing activities include:
• reconnaissance and information gathering
• vulnerability scanning
• web application security testing
• exploiting vulnerabilities in controlled environments
• documenting discovered security weaknesses
• recommending security improvements
These activities help organizations understand where their systems are vulnerable.
Career Opportunities After Completing the Ethical Hacking Roadmap
After completing the ethical hacking roadmap, several cybersecurity career paths become available.
Common professional roles are:
• Penetration Tester
• Ethical Hacker
• Red Team Operator
• Security Researcher
• Cybersecurity Consultant
The demand for ethical hackers continues increasing worldwide as organizations face more cyber attacks.
Companies need professionals who understand how attackers think and how systems can be protected.
Frequently Asked Questions — Ethical Hacking Roadmap
What is the best ethical hacking roadmap for beginners?
The best ethical hacking roadmap begins with learning computer fundamentals, networking basics, and Linux operating systems before moving into cybersecurity and penetration testing. Beginners searching how to become ethical hacker professionals should focus on understanding how systems work rather than jumping directly into hacking tools. A proper ethical hacking roadmap 2026 gradually introduces web application security, vulnerability discovery, and practical labs so learners build strong cybersecurity foundations step by step.
How long does it take to follow the ethical hacking roadmap?
The time required to complete the ethical hacking roadmap depends on how consistently someone studies and practices. Most beginners following the ethical hacking roadmap can learn core cybersecurity skills within 12–18 months. However, becoming a highly skilled professional penetration tester may take several years of hands-on practice. Anyone serious about learning how to become ethical hacker professionals should practice regularly in cybersecurity labs while studying networking, Linux, and web security concepts.
Can beginners learn ethical hacking from scratch?
Yes. Anyone can start learning using a structured ethical hacking roadmap even without prior cybersecurity experience. Beginners who want to know how to become ethical hacker professionals should start with basic computer knowledge and networking concepts. After learning these foundations, they can move toward Linux, cybersecurity principles, and web application security. Following the ethical hacking roadmap step by step allows beginners to gradually develop the skills required for penetration testing and ethical hacking careers.
Do you need programming to become an ethical hacker?
Programming is not required at the very beginning of the ethical hacking roadmap, but it becomes very useful later. Ethical hackers often analyze application logic and automate tasks using programming languages such as Python, JavaScript, and Bash. Anyone researching how to become ethical hacker professionals should eventually learn programming because it helps understand vulnerabilities and develop custom security tools. Programming knowledge strengthens several stages of the roadmap.
What tools are used in the ethical hacking roadmap?
The ethical hacking roadmap includes many cybersecurity tools used by penetration testers. Common tools include Nmap for network scanning, Burp Suite for web application testing, FFUF for directory fuzzing, Amass for subdomain discovery, and Metasploit for exploitation testing. However, tools are only effective when learners understand the underlying concepts. Anyone learning how to become ethical hacker professionals should focus on cybersecurity fundamentals before relying heavily on hacking tools.
Is ethical hacking a good career in 2026?
Yes. Ethical hacking continues to be one of the fastest growing cybersecurity careers worldwide. Organizations need skilled professionals who understand the ethical hacking roadmap and can identify vulnerabilities before attackers exploit them. Professionals who follow the roadmap can pursue careers as penetration testers, security researchers, red team operators, or cybersecurity consultants. The increasing number of cyber attacks ensures strong demand for ethical hackers across industries.
What are the Best Certifications for Ethical Hackers?
Certifications help validate skills learned during the ethical hacking roadmap.
Popular certifications for Ethical Hackers are:
• CompTIA Security+
• CEH (Certified Ethical Hacker)
• OSCP (Offensive Security Certified Professional)
• PNPT (Practical Network Penetration Tester)
These certifications demonstrate that professionals understand how to become ethical hacker professionals and perform penetration testing effectively.
Key Takeaways
Anyone serious about learning cybersecurity should follow a structured ethical hacking roadmap instead of randomly learning hacking tools.
The ethical hacking roadmap provides a clear learning path that helps beginners gradually develop the skills required to become professional ethical hackers and SecurityElites will help you to acheive it.
By learning fundamentals, practicing in labs, and gaining real-world experience, anyone dedicated to cybersecurity can eventually achieve their goal of becoming an ethical hacker.