Among the most dangerous and unpredictable threats in the digital world is the Zero-Day Vulnerability.
A Zero-Day Vulnerability refers to a hidden security flaw in software, hardware, or operating systems that is unknown to the vendor or developers. Because the flaw is unknown, there are zero days available to fix it before attackers begin exploiting it. This makes zero-day vulnerabilities extremely dangerous. Hackers can exploit these flaws before developers even realize they exist.
In today’s connected world, zero-day attacks can target anyone, including individuals, businesses, governments, banks, and critical infrastructure.
Understanding what a zero-day vulnerability is, how zero-day exploits work, and how to protect yourself from zero-day attacks is essential for anyone using the internet. Many zero-day attacks eventually install malicious software. Learn more in our guide on What Is Malware and How It Works.
In this comprehensive guide, we will explain everything you need to know about zero-day vulnerabilities, including real-world examples, detection techniques, prevention strategies, and cybersecurity best practices.
Table of Contents
What Does “Zero-Day” Mean?
The term zero-day refers to the fact that developers have had zero days to fix the vulnerability.
The timeline usually looks like this:
- A vulnerability exists in software.
- Hackers discover the flaw before developers do.
- Hackers create an exploit.
- Attackers launch an attack.
- Developers discover the vulnerability.
- A patch is created.
During the time between step 2 and step 5, systems are extremely vulnerable.
This is the zero-day window.
Because security teams are unaware of the vulnerability, traditional security tools may not detect the attack. Security researchers often track newly discovered vulnerabilities using the global CVE database maintained by MITRE. You can explore publicly disclosed vulnerabilities through the CVE List.
Simple Example of a Zero-Day Vulnerability
Imagine a bank vault that has a secret hidden door. The bank staff does not know the door exists. But somehow a thief discovers this hidden door of banks vault.
Since the bank staff doesn’t know about the door, they cannot lock it. But the thief can enter the vault anytime because he knows about it.
A zero-day vulnerability works exactly the same way.
Software developers do not know about the hidden flaw, but hackers exploit it before anyone can fix it. Some zero-day exploits are used to deploy ransomware attacks that encrypt user files and demand payment.
How Zero-Day Attacks Work ?
A zero-day attack happens when hackers exploit a zero-day vulnerability before developers discover the flaw or release a security patch. Because no protection exists yet, attackers can secretly compromise systems and steal data.
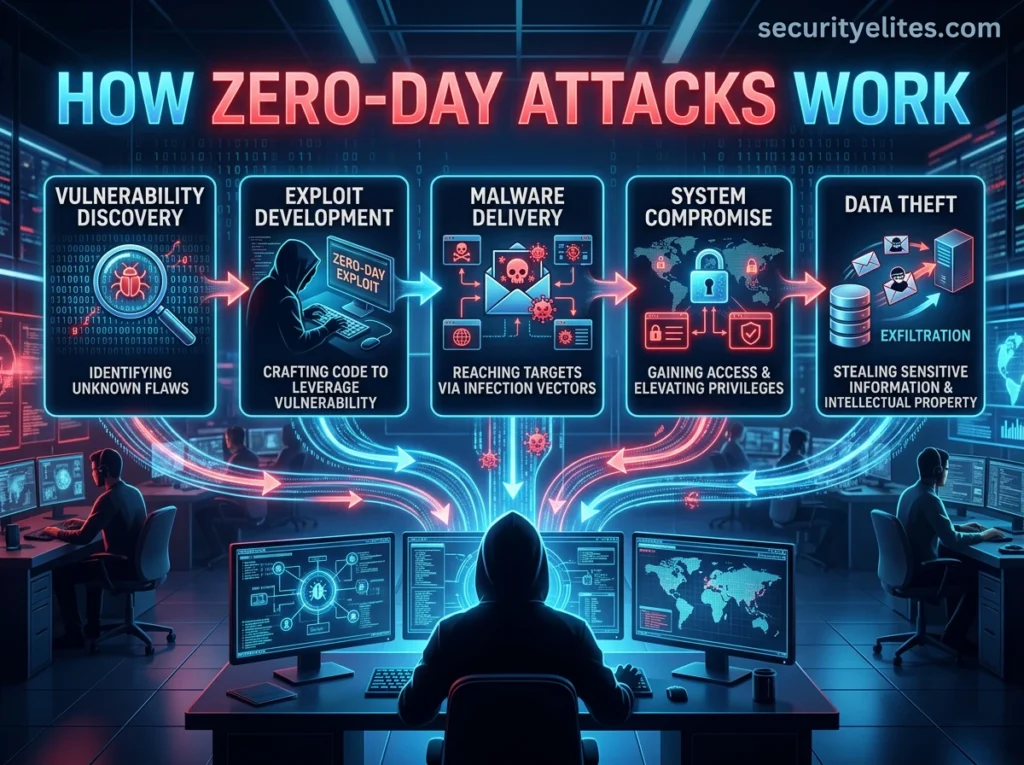
Here is a simple 5-step breakdown of how zero-day attacks work.
1. Hackers Discover a Hidden Vulnerability
The first step in a zero-day attack is finding a hidden flaw in software.
Hackers search for vulnerabilities in:
- operating systems
- web browsers
- mobile apps
- enterprise software
- cloud platforms
They use techniques like code analysis, fuzz testing, and reverse engineering to identify weaknesses in software programs.
Once they confirm the flaw works, it becomes a zero-day vulnerability.
2. Attackers Create a Zero-Day Exploit
After discovering the vulnerability, hackers develop a zero-day exploit.
An exploit is malicious code designed to take advantage of the vulnerability and manipulate the software.
The exploit can allow attackers to:
- run malicious programs
- bypass security controls
- access restricted files
- gain administrator privileges
At this stage, the exploit becomes a powerful tool that can compromise vulnerable systems.
3. Hackers Deliver the Exploit to Victims
Once the exploit is ready, attackers must deliver it to targets.
Common delivery methods include:
- phishing emails with malicious attachments
- infected websites
- fake software downloads
- compromised applications
- malicious advertisements
When the victim interacts with the infected file or website, the exploit activates automatically.
4. The Vulnerability Is Exploited

When the exploit runs on the victim’s system, it triggers the zero-day vulnerability.
This allows attackers to gain unauthorized access and perform actions such as:
- executing malware
- stealing sensitive data
- controlling the system remotely
- installing backdoors
Most zero-day exploits run silently in the background, so victims often do not notice the attack.
5. Hackers Maintain Access and Steal Data
After gaining access, attackers usually install malware to maintain control over the system. They usually use malwares like spyware, ransomware, keyloggers or backdoors(trojans) etc.
Hackers can then monitor the system, steal confidential information, or launch additional cyberattacks.
In many cases, attackers remain hidden inside the network for weeks or even months before being discovered.
Why Zero-Day Vulnerabilities Are Extremely Dangerous
Zero-day vulnerabilities are considered one of the most serious cybersecurity threats in the digital world. Unlike common security flaws that already have patches or known defenses, zero-day vulnerabilities exist without any warning or protection.
Because developers do not yet know the vulnerability exists, attackers can exploit the weakness freely until a patch is released. During this window, systems remain completely exposed.

Below are the key reasons why zero-day vulnerabilities are extremely dangerous:
1. No Patch or Security Fix Available
The biggest danger of a zero-day vulnerability is that there is no available patch or fix when the vulnerability is discovered by attackers.
In most cybersecurity situations, once a vulnerability becomes public, developers quickly release security updates to fix the issue. However, with a zero-day vulnerability, the software vendor has zero days to prepare a defense.
This means attackers can exploit the vulnerability while users remain unaware that their systems are at risk.
During this time, organizations cannot apply any official fixes, leaving systems vulnerable to compromise.
2. Security Tools Often Fail to Detect Zero-Day Attacks
Most traditional cybersecurity systems such as antivirus software rely on signature-based detection.
Signature-based security tools identify threats by comparing files with known malware patterns stored in their databases. Since zero-day exploits are completely new, they do not yet have recognizable signatures.
As a result, these attacks can bypass many traditional security defenses.
Attackers can therefore remain undetected for long periods, giving them enough time to steal data, install malware, or spread deeper into a network.
3. Attackers Gain an Early Advantage
Zero-day vulnerabilities give hackers a massive advantage over defenders.
Because attackers discover the vulnerability first, they can create and deploy exploits before security teams even know a problem exists.
This advantage allows attackers to launch stealthy attacks that can remain active for weeks or months before being discovered.
By the time developers release a patch, attackers may already have compromised thousands of systems.
4. Massive Data Breaches Can Occur
Zero-day vulnerabilities can lead to some of the largest data breaches in history.
If a vulnerability exists in widely used software, attackers can exploit it across thousands or even millions of systems simultaneously. Cybercriminals often combine phishing emails with zero-day exploits to infect victims.
This allows hackers to gain access to sensitive information such as:
- login credentials
- financial records
- personal data
- intellectual property
- confidential business documents
Because zero-day attacks often go unnoticed for extended periods, attackers may extract large volumes of sensitive information before detection.
5. Used in Advanced Cyber Warfare
Zero-day vulnerabilities are frequently used in state-sponsored cyber operations.
Governments and intelligence agencies sometimes develop sophisticated cyber weapons based on undisclosed vulnerabilities. These exploits are used for espionage, surveillance, or sabotage.
One famous example is the Stuxnet cyber weapon, which used multiple zero-day vulnerabilities to target nuclear facilities.
This demonstrates how zero-day vulnerabilities can be weaponized to attack critical infrastructure systems, including energy grids, defense networks, and communication systems.
6. Extremely Valuable on the Dark Web
Zero-day vulnerabilities are highly valuable in underground hacker marketplaces.
Because they are rare and powerful, working zero-day exploits can sell for hundreds of thousands or even millions of dollars.
Prices depend on the target platform:
- iPhone zero-day exploits can sell for over $2 million
- Android exploits can sell for $500,000 or more
- Browser exploits often sell for six-figure prices
These high prices create a strong financial incentive for hackers to discover and weaponize vulnerabilities rather than report them.
7. Zero-Day Attacks Spread Rapidly
Once attackers develop an exploit, zero-day attacks can spread extremely quickly.
Hackers often integrate exploits into automated attack tools, malware kits, or botnets. This allows them to scan the internet and identify vulnerable systems within minutes.
If the targeted software is widely used, the exploit can spread rapidly across networks, organizations, and even entire industries.
This speed makes containment extremely difficult once an attack begins.
8. Hard to Investigate and Analyze
Zero-day attacks are difficult for cybersecurity teams to analyze.
Because the vulnerability is unknown, security researchers must first reverse engineer the attack to understand how it works.
This process can take days or weeks.
During that time, attackers may continue exploiting the vulnerability in other systems.
Additionally, attackers often use advanced techniques such as obfuscation and encryption to hide their exploits, making investigation even more challenging.
9. Can Target Any Device or Software
Zero-day vulnerabilities are not limited to traditional computers.
They can affect almost any digital system, including:
- operating systems
- web browsers
- smartphones
- cloud infrastructure
- IoT devices
- industrial control systems
As the number of connected devices grows, the potential attack surface for zero-day vulnerabilities increases dramatically.
This makes cybersecurity defense increasingly complex.
10. Zero-Day Exploits Enable Other Cyber Attacks
Zero-day vulnerabilities often serve as the entry point for larger cyberattacks.
Once attackers gain initial access through a zero-day exploit, they can deploy additional malicious activities such as:
- ransomware infections
- spyware installation
- credential theft
- lateral movement within networks
- long-term surveillance
In many major cyber incidents, a zero-day vulnerability is the first step in a much larger attack chain.
11. Detection May Take Months or Years
One of the most alarming aspects of zero-day vulnerabilities is that they can remain undiscovered for long periods.
In some cases, vulnerabilities have existed in software for years before being discovered.
During that time, attackers may quietly exploit the vulnerability without raising suspicion.
Some advanced cyber espionage campaigns have used zero-day exploits that remained undetected for months, allowing attackers to maintain persistent access to sensitive systems.
Frequently Asked Questions About Zero-Day Vulnerabilities
What is a zero-day vulnerability?
A zero-day vulnerability is a security flaw in software, hardware, or operating systems that developers are unaware of. Because the vulnerability is unknown, there are zero days available to fix it before hackers begin exploiting it, making it extremely dangerous for users and organizations.
What is a zero-day exploit?
A zero-day exploit is the code or technique used by hackers to take advantage of a zero-day vulnerability. The exploit allows attackers to manipulate vulnerable software and perform unauthorized actions such as running malicious programs, stealing data, or gaining system access.
What is a zero-day attack?
A zero-day attack occurs when cybercriminals use a zero-day exploit to compromise systems before the vulnerability is discovered and patched. Because security teams are unaware of the flaw, zero-day attacks can bypass traditional security defenses and remain undetected.
Why are zero-day vulnerabilities dangerous?
Zero-day vulnerabilities are dangerous because there is no security patch available when the vulnerability is first exploited. Hackers can use the flaw to launch attacks while developers are still unaware of the issue, allowing attackers to steal data, install malware, or gain control of systems.
How do hackers find zero-day vulnerability?
Hackers discover zero-day vulnerabilities using several methods such as code analysis, fuzz testing, reverse engineering, automated vulnerability scanners, and artificial intelligence tools. Some attackers also purchase zero-day exploits from underground cybercrime markets.
How are zero-day vulnerability is detected?
Zero-day vulnerabilities are usually discovered by security researchers, ethical hackers, and cybersecurity companies. Detection methods include behavioral monitoring, advanced threat detection systems, anomaly analysis, and bug bounty programs.
How are zero-day vulnerabilities fixed?
Once a zero-day vulnerability is discovered, developers create a security patch or software update to fix the flaw. Users must install these updates quickly to protect their systems from potential exploitation.
Can antivirus software detect zero-day attacks?
Traditional antivirus software may struggle to detect zero-day attacks because they rely on known malware signatures. However, modern security tools use behavior-based detection, machine learning, and threat intelligence to identify suspicious activity associated with zero-day exploits.
Are zero-day vulnerabilities common?
Yes. Thousands of vulnerabilities are discovered in software every year, and some remain undiscovered for long periods. While not all vulnerabilities become zero-day exploits, many attackers actively search for these hidden flaws to launch cyberattacks.
What are examples of zero-day attacks?
Some well-known zero-day attacks include the Stuxnet cyber weapon, Microsoft Exchange zero-day attacks, and browser-based zero-day exploits targeting Chrome and Safari. These attacks demonstrated how dangerous zero-day vulnerabilities can be when exploited by hackers.
How can organizations protect against zero-day vulnerabilities?
Organizations can reduce the risk of zero-day attacks by implementing strong cybersecurity practices such as:
- regularly updating software
- using advanced endpoint protection
- monitoring network activity
- applying zero trust security models
- conducting regular security audits
These measures help detect suspicious behavior even when the vulnerability itself is unknown.
Key Takeaways
Zero-day vulnerabilities are extremely dangerous because they exploit the gap between vulnerability discovery and patch development.
During this window, attackers have a significant advantage, allowing them to bypass defenses, steal sensitive data, and compromise systems without detection.
As software systems grow more complex and interconnected, the number of potential vulnerabilities continues to increase.
This makes proactive cybersecurity strategies, threat intelligence, and continuous monitoring essential for defending against zero-day attacks.